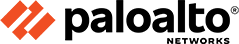
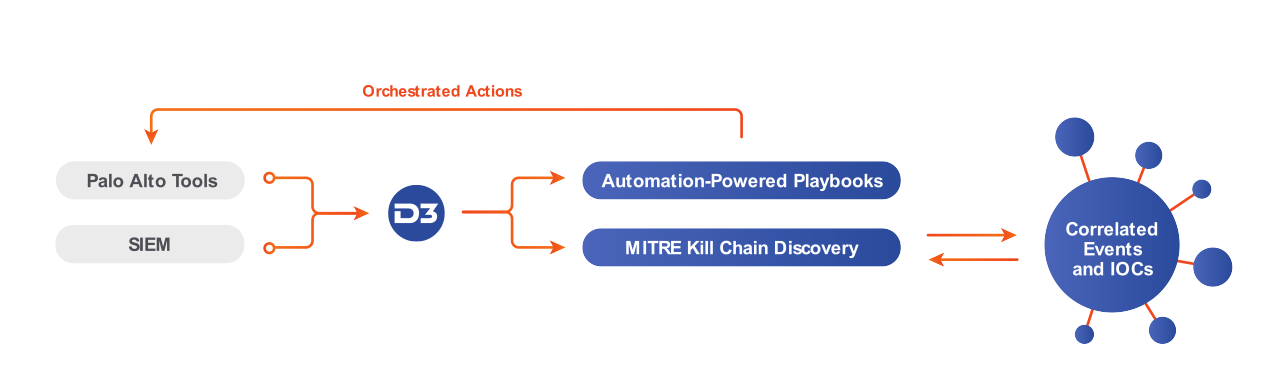
D3 integrates with the Palo Alto Networks Application Framework so that you can orchestrate response workflows that include threat intelligence enrichment, malware analysis, firewall blacklists, and MITRE kill chain correlation—all from a single dashboard. D3 users can automate dozens of distinct actions across Palo Alto tools on the fly, using D3’s codeless playbook editor.
| Integration | Capabilities |
|---|---|
| Palo Alto Networks Firewall | Orchestrate 20+ firewall actions to quickly respond to threats and block attackers. |
| Palo Alto Networks Autofocus | Enrich incidents by searching across Autofocus threat intelligence. |
| Palo Alto Networks WildFire | Automate reputation checks and file detonation, and ingest the reports into the incident workflow. |
Integrating D3 SOAR with your Palo Alto tools enables you to enrich alerts with valuable contextual data, including Autofocus threat intelligence and MITRE ATT&CK matrix correlations, to inform decisions and determine the next steps. D3 can then trigger a response playbook that orchestrates tasks across your security infrastructure, such as blocking malicious IPs, URLs, and applications across your network and firewall. With D3’s automated workflows and full-lifecycle playbooks for incident response, analysts no longer have to manually coordinate dozens of triage and response tasks. Response occurs in seconds, not hours.
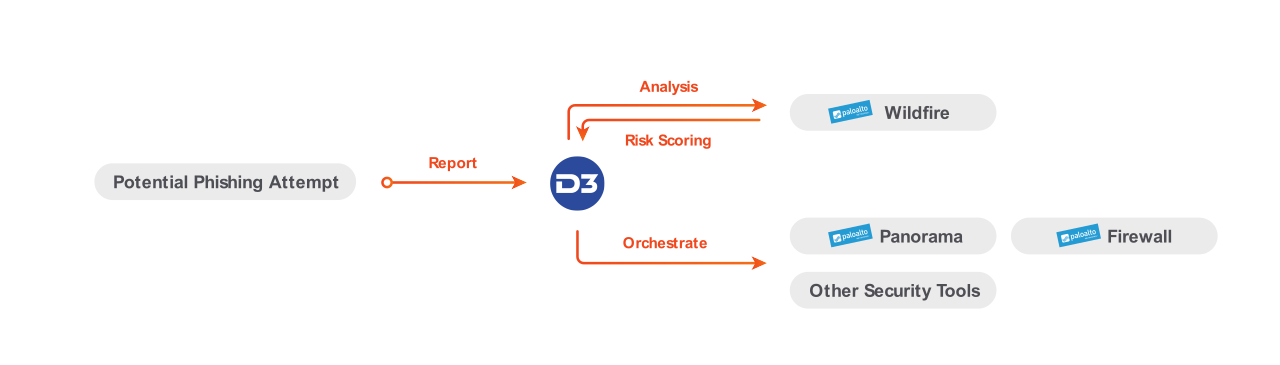
With D3’s integration with Palo Alto, when a phishing attempt is reported to the SOC, an analyst can trigger an automated phishing playbook in D3 that parses out the elements of the email, including the potentially malicious attached file. The file is then uploaded to Wildfire for analysis and risk scoring. If it is confirmed as a genuine incident, D3 can then orchestrate the appropriate actions in other Palo Alto tools. Using D3 to orchestrate the analysis also allows you to automatically update network and firewall rules based on the result of the investigation.
Our Connected SOAR Security Alliance brings hundreds of vendors together, allowing customers to benefit from our deep industry relationships and fully vendor-agnostic, independent SOAR platform.