SMART CASES
Integrated Case Management and Security Automation
Give Serious Threats the Attention They Deserve
Smart SOAR’s case management system help cross-functional teams collaborate and conduct incident investigations in a carefully orchestrated, consistent, and timely manner.
Incident Response and Security Case Management
Our cyber security case management features are built into the incident workspace interface so that you can conduct an end-to-end investigation from a single pane of glass.
Automated Reporting
Automatically export incident reports to keep stakeholders engaged and informed, without taking any time away from security tasks.
Efficient Investigations
Group together related events, preventing redundant work and enabling more effective investigations.
The Smart Soar Approach
End-to-End Cyber Security Investigation and Case Management
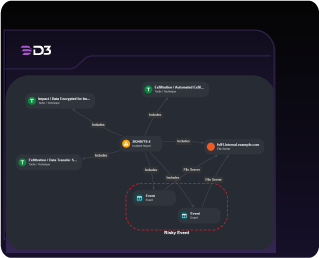
Link Analysis
Visualize cyber-attacks as they unfold in an auto-generated mind map.
Investigation Timelines
Follow incidents from initial detection through to privilege escalation and exfiltration.
More than Just SOAR
Unlike other SOAR vendors, we have been helping enterprises manage cases end to end for more than 10 years.
Get all the Clues
Smart SOAR captures and correlates data from all your tools.
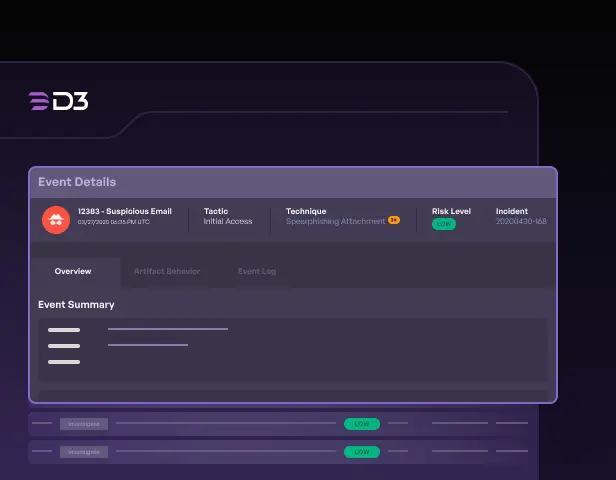
Digital Forensics
Track the chain of custody for evidence. Smart SOAR provides the flexibility to accommodate any artifact.
Role-Based Access Controls
Stay secure and compliant while enabling collaboration between investigators.
How it Works
Scalable Security Case Management Software
Investigate cases of every type in their entirety, within the SOC and beyond. Log relevant details and evidence around a case. Build a team of investigators, store digital artifacts, assign tasks by priority, and more. Enable cross-functional teams to work together on a case. Granular role-based access controls and a full audit trail of actions make it easy to maintain and demonstrate compliance.
Learn More About Smart Case Management
Check out these resources to answer your questions about our integrated incident response and cyber security case management software.
-
A Comprehensive Guide to Smart SOAR
Learn how Smart SOAR outperforms conventional SOAR tools in every aspect of threat detection, analysis, and incident response.
-
The MSSP Client Portal: Differentiate Your Services with Streamlined Client Collaboration
The MSSP Client Portal addresses challenges in providing efficient communication, accurate reporting, and scaling security services.
-
How High Wire Networks Eliminated 99% of Alert Noise and Increased Capacity 3x Without Adding Headcount
Serving 25k+ customers through a global network of channel partners, Master MSSP High Wire Networks used Smart SOAR to cut alert noise by 99% and 3x client capacity without adding headcount.
Get Started with D3
One platform to stop alert overwhelm. Transform how your security team works, by focusing its resources on real threats.