investigate & Hunt
Threat Hunting and Investigations
Smart SOAR makes it easy to locate threats in your environment, wherever they’re hiding. Using signature and behavior-based methods, D3’s threat hunting playbooks enable you to uncover connections, identify dangers, and proactively search for ongoing incidents.
Automate Threat Hunting
Security teams don’t have the time for slow, manual threat hunting, which allows dangerous threats to go undetected. The solution is automation-powered threat hunting.
Integrate Your Tools
With unlimited integrations, Smart SOAR can connect to all your tools to orchestrate threat hunting that covers your entire environment from one interface.
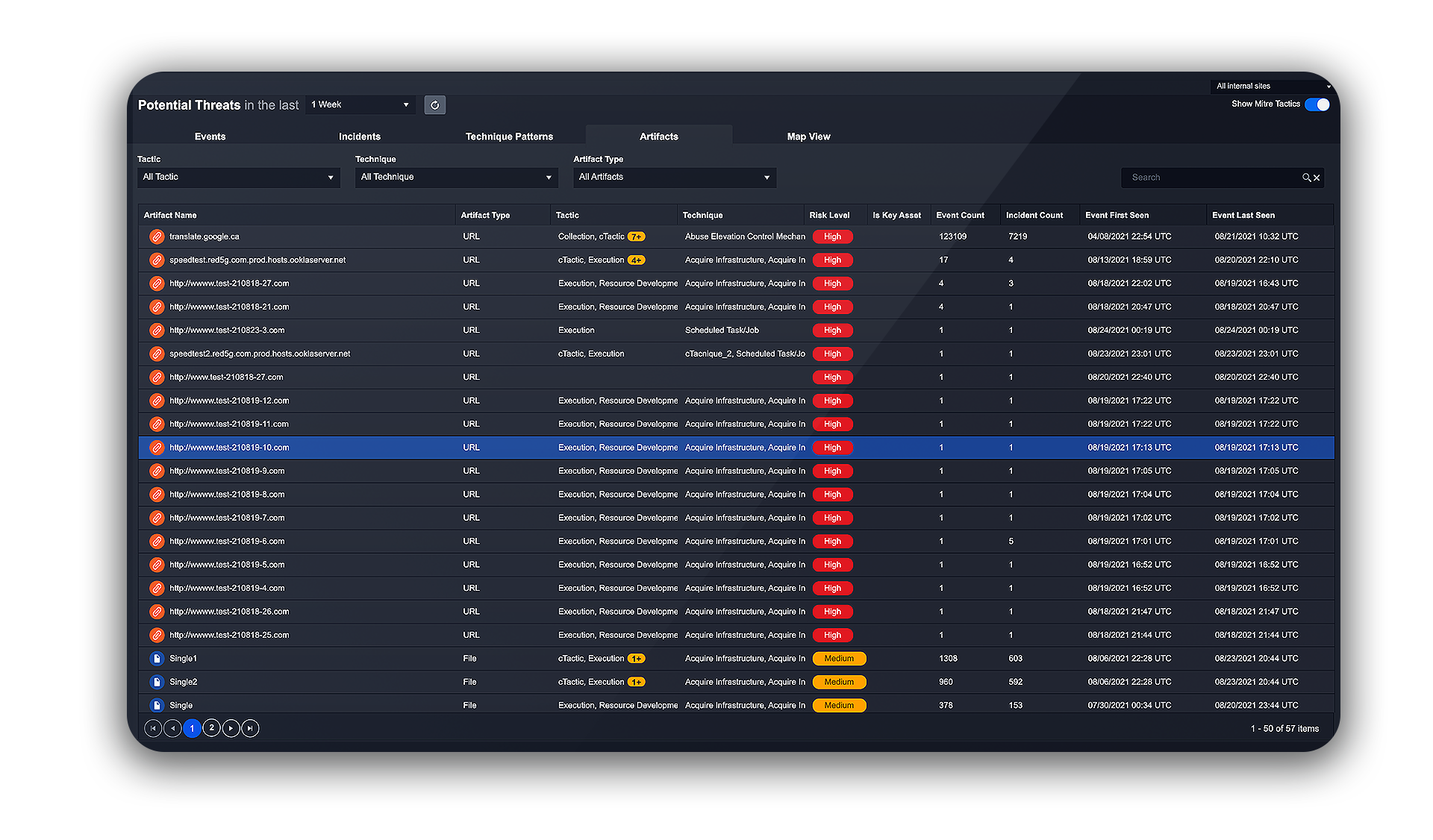
Indicators of Compromise (IOC) Search
D3 extracts indicators of compromise (IOCs) from incoming incidents and uses them to run searches across your entire environment. Automatically find IOCs across other events, logs, and endpoints, while expanding your understanding of the incident by incorporating linked IOCs into the search.
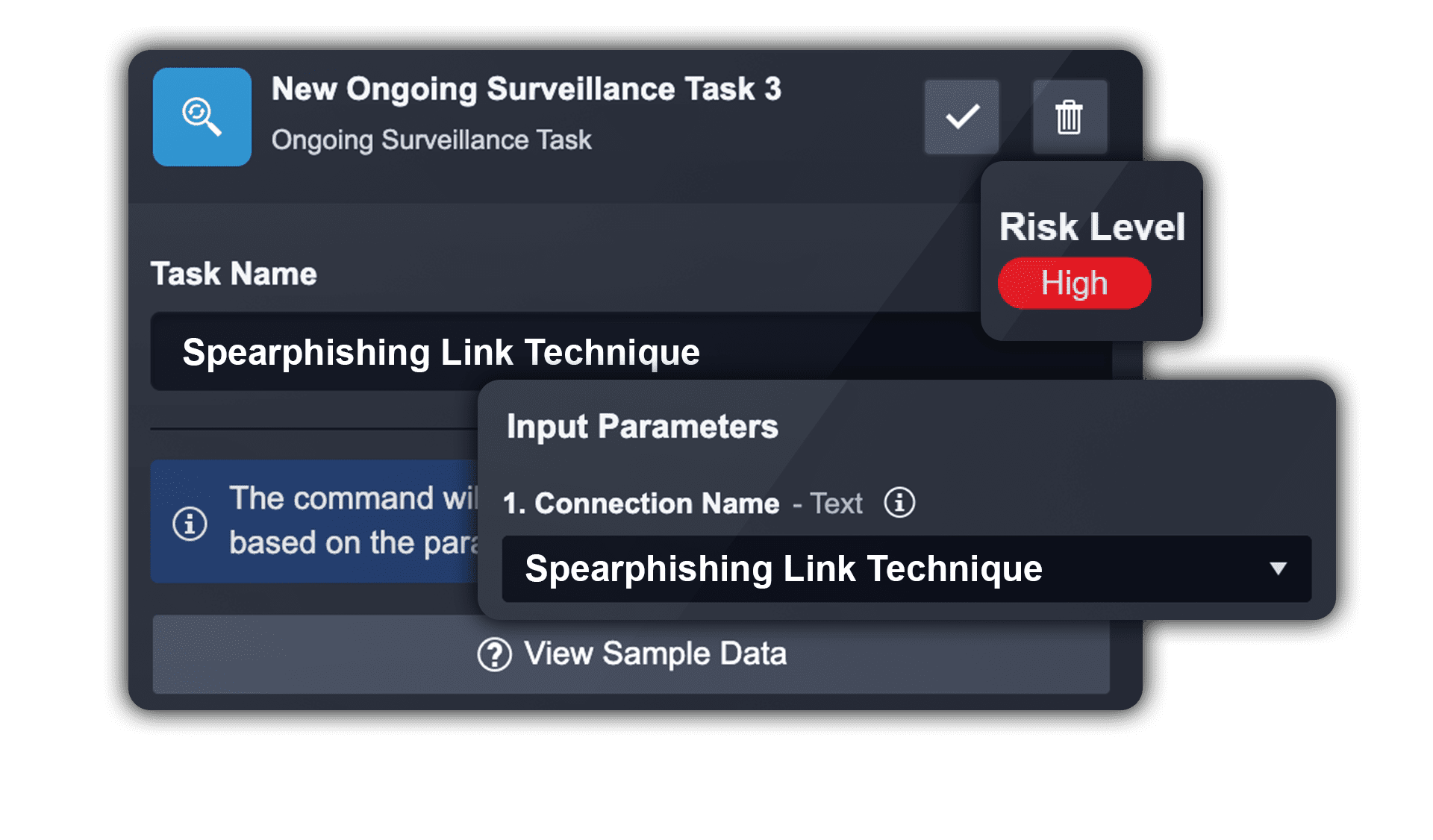
Surveillance
Place important IOCs and TTPs under surveillance, with playbooks that automatically track them. When a sign of a potential attack is detected, you can monitor the behaviors that would represent further links in that kill chain. Surveillance allows you to keep a constant eye on the most pressing threats, knowing that you’ll be alerted immediately when they’re involved in an incident.
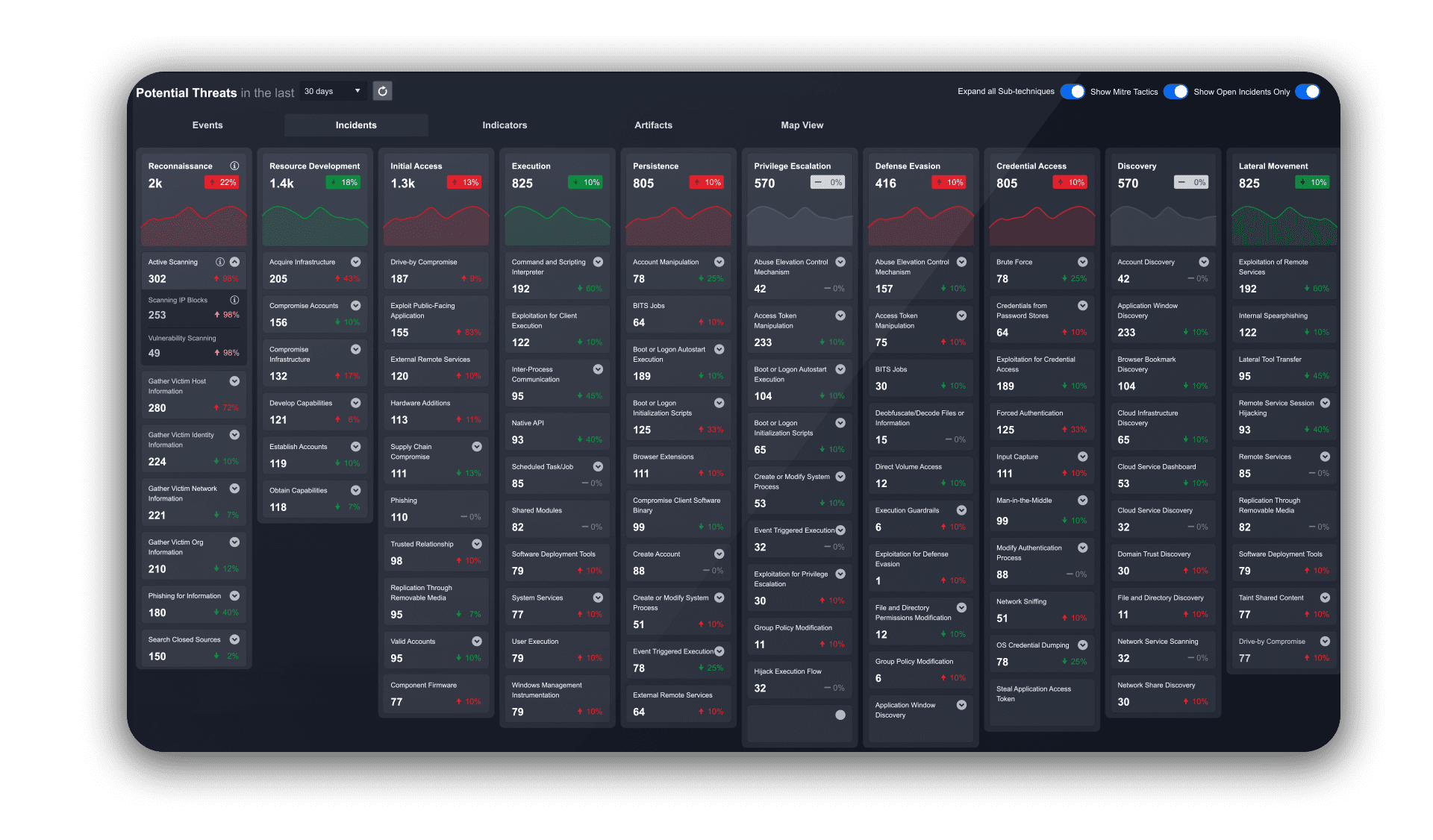
MITRE ATT&CK Monitor
Track and visualize the occurrence of each ATT&CK technique in your environment with D3’s MITRE ATT&CK Monitor dashboard. You’ll know at a glance what techniques your adversaries are using against you and where to focus your resources.
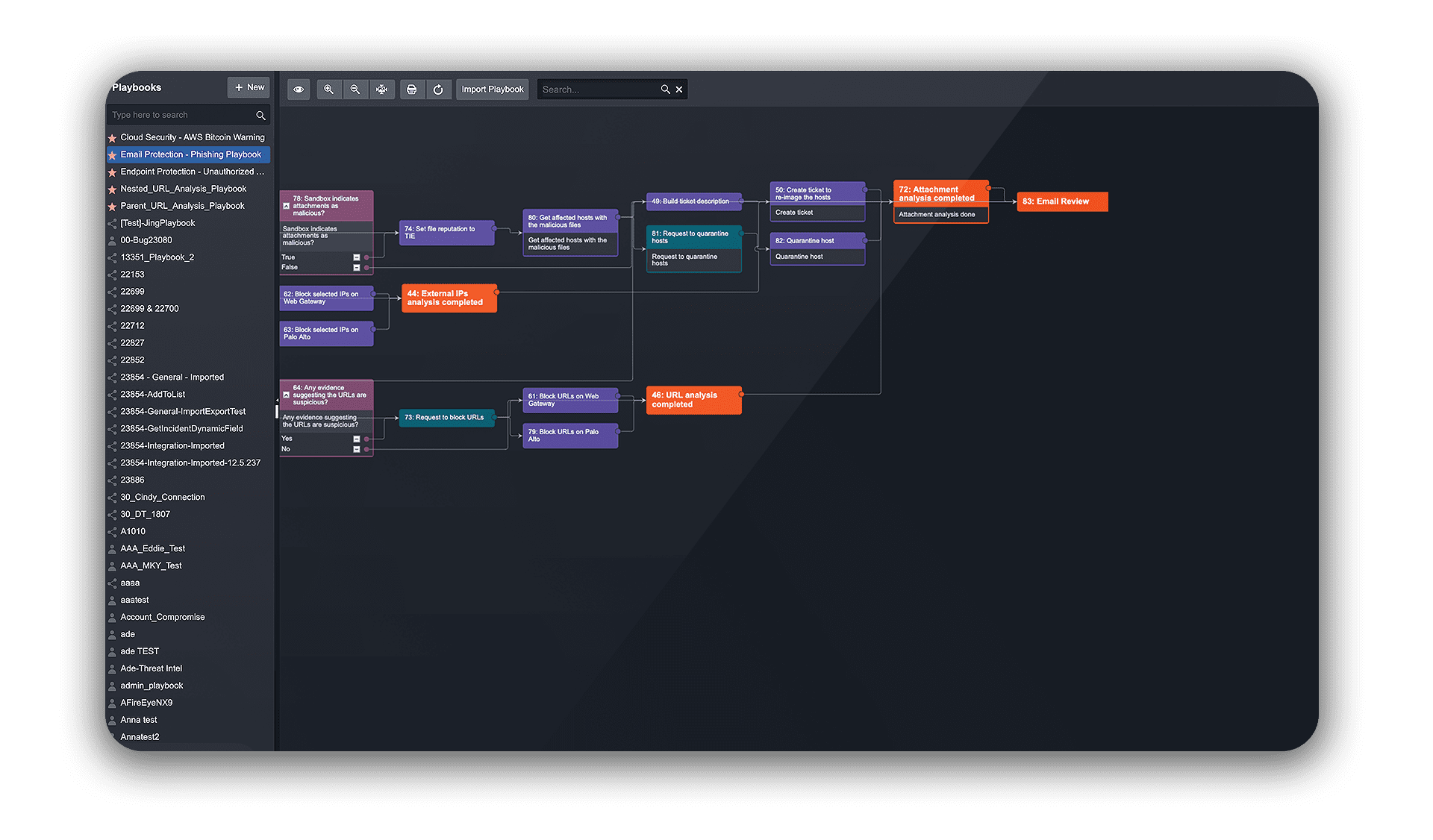
Cyber Threat Hunting Playbooks
Orchestrate threat hunting workflows with D3’s automation-powered Tier 3 playbooks. Contextualize security events using integrations with email, identity, endpoint, and network tools. Identify connections between events, uncover the user account that is responsible for a malicious process, and widen the scope to find related IOCs across your organization.
Get Started with D3 Security
One platform to stop alert overwhelm. Transform how your security team works, by focusing its resources on real threats.