Automation & Orchestration
Security Automation and Orchestration
Smart SOAR makes security orchestration, automation and response easy. Connect your tools using REST API and vendor-agnostic integrations, and automate workflows without coding. Attract and retain SOC staff, maximize all of your technology investments, and innovate faster than ever.
Security Automation That Helps You Achieve More
Smart SOAR gives security teams the automation and orchestration they need to offload manual processes, spot real incidents, and trigger actions.
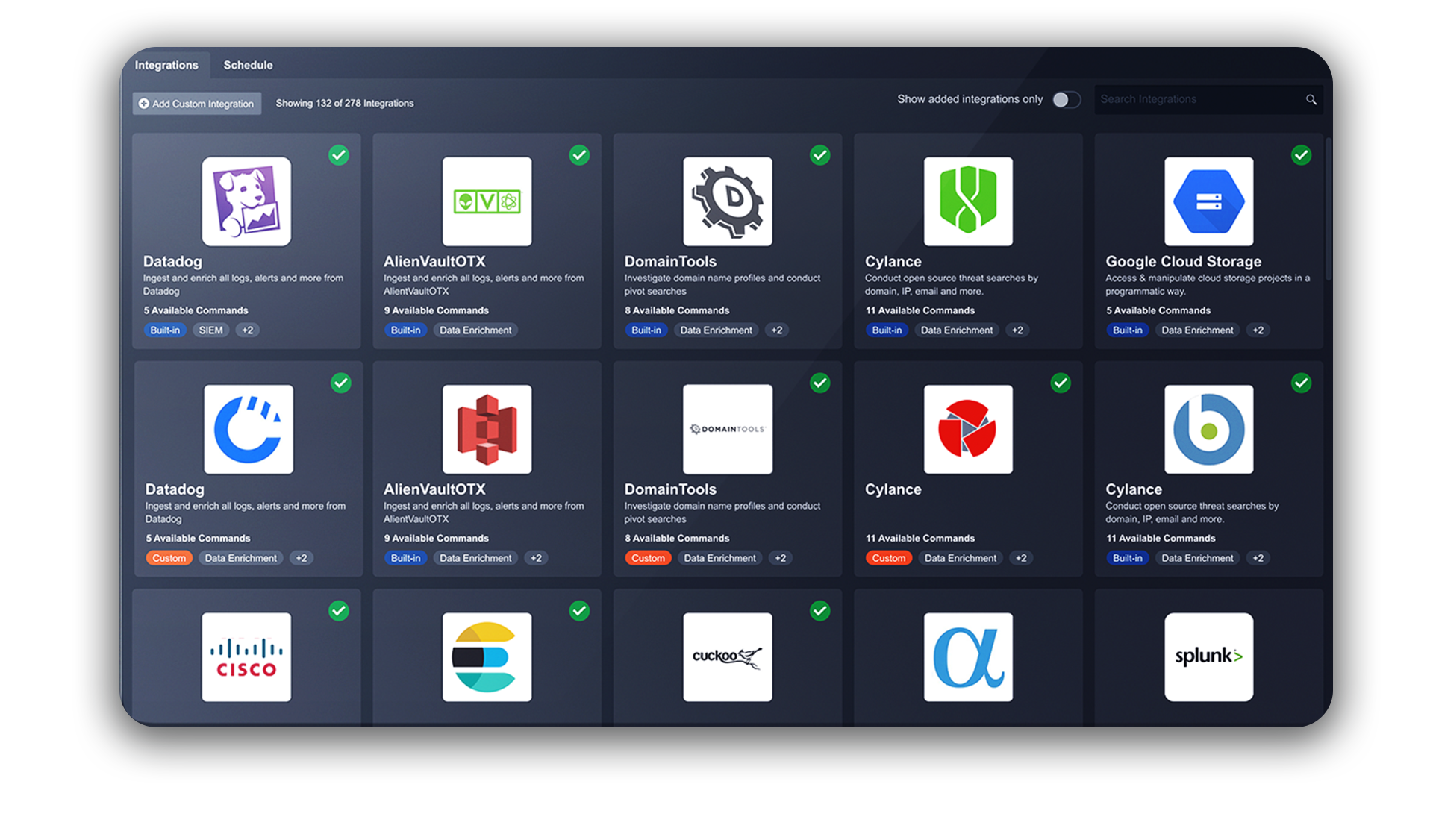
Connect To Any Rest Api Or Web App
Ingest, normalize, de-duplicate, and correlate event data from any app, stack or environment. Hundreds of fully featured, vendor-agnostic integrations give you all the data you need, with minimal effort.
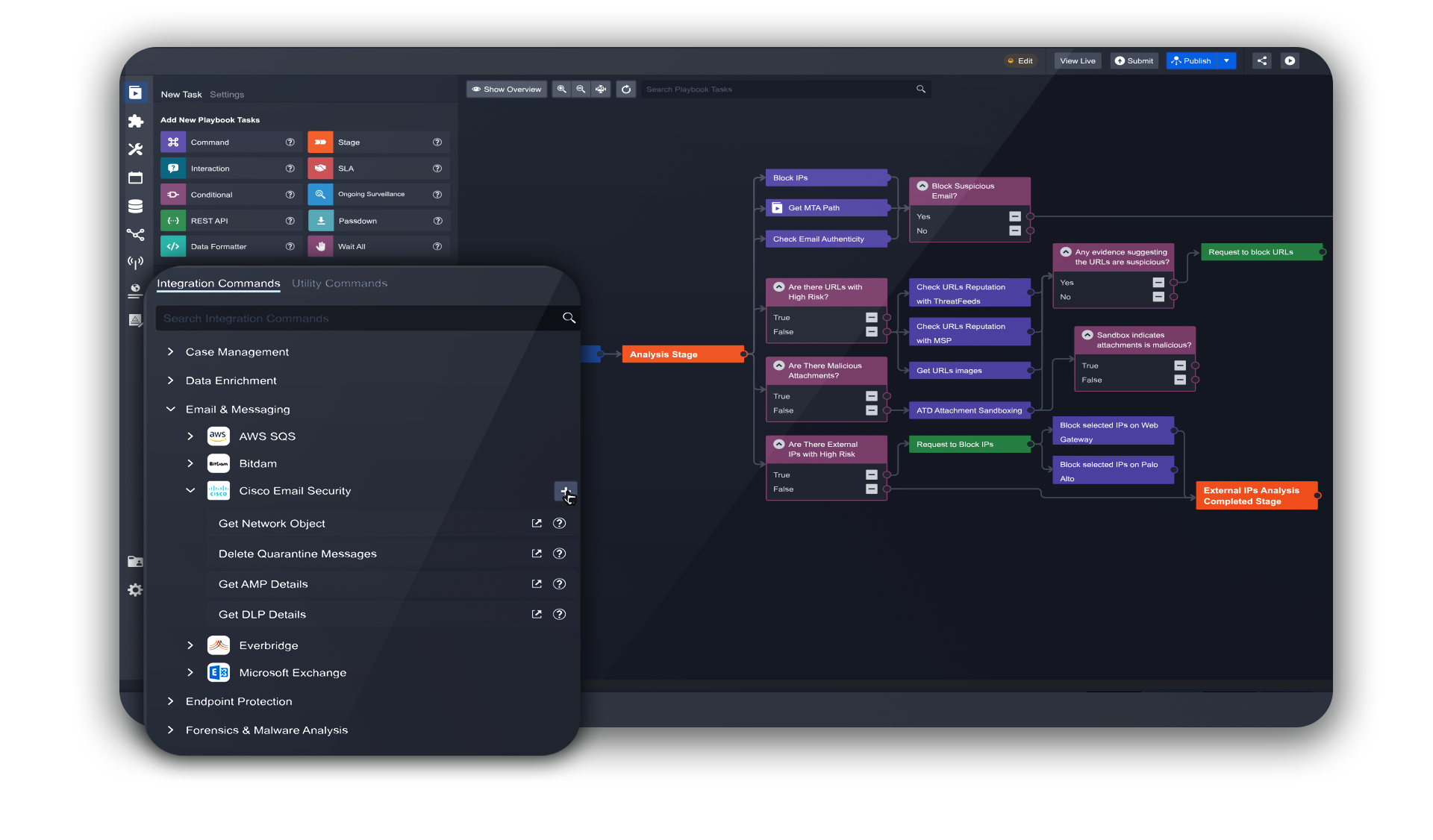
Integration and Playbook Fusion
Smart SOAR enables you to configure and test integrations and playbooks from a single screen; no jumping back and forth between the integration marketplace and playbook environment. As you bring on more integrations and playbooks, our seamless SOAR setup process saves considerable time and effort, helping you and your team to accomplish more.
Universal REST API
Smart SOAR’s Universal REST API eliminates all of the pain points usually associated with security tool integration. Connect with ease to any REST API or web application, no matter the product, version, vendor, or if its in-house or custom-built. Plus, you can leverage the full functionality of your tech stack for automated workflows.
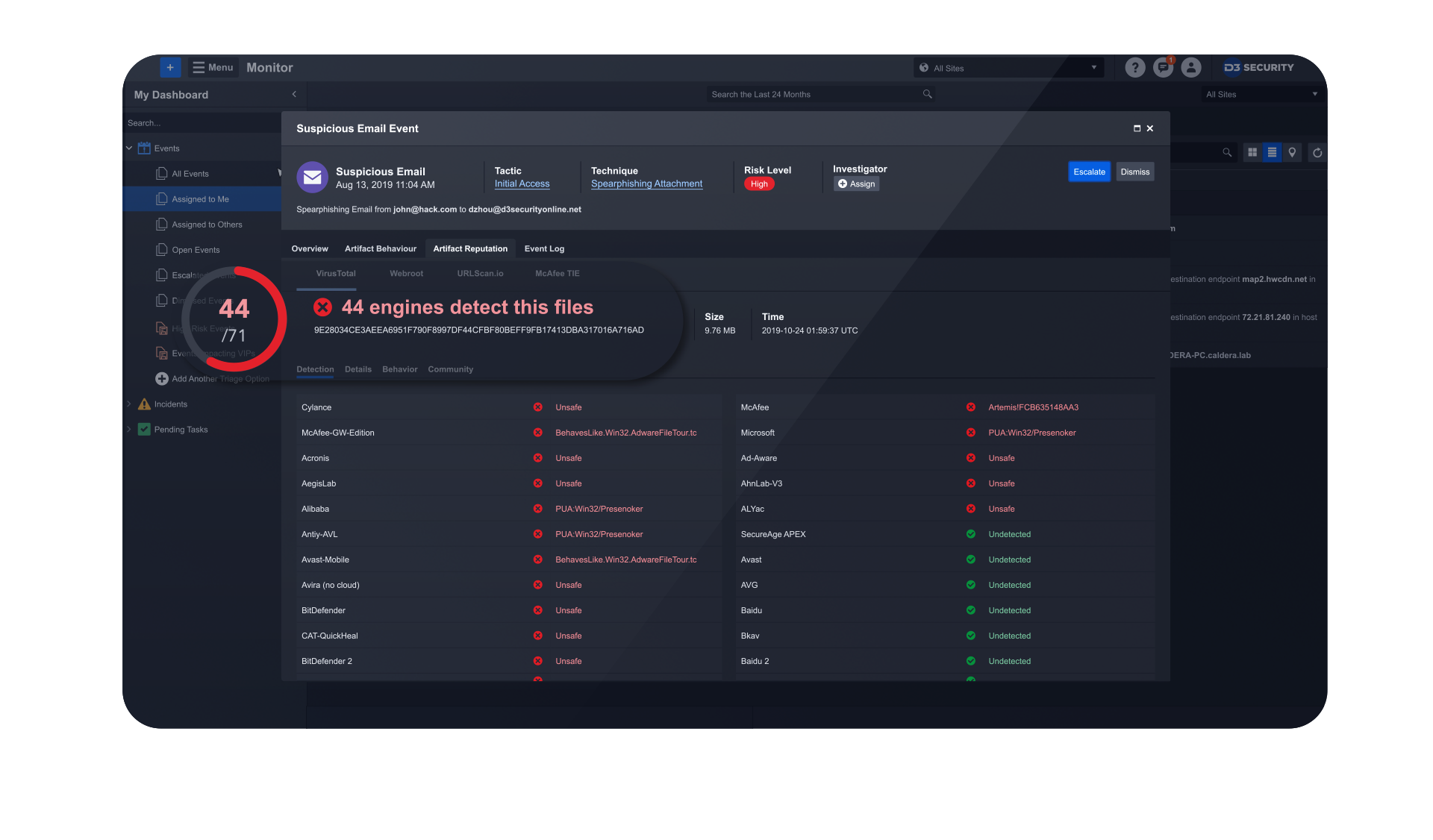
Context-Driven Triage and Prioritization
Smart SOAR provides security analysts and response playbooks with all of the context needed to drive highly intelligent, rapid and scalable threat investigation and incident response. Opening an alert for the first time, analysts are presented with incident type(s) and playbook(s), linked events, IOCs, logs, and data from threat intelligence, incident knowledge and MITRE ATT&CK TTPs. The level of context available is so high that many Smart SOAR customers have fully automated their tier-1 security workflows.
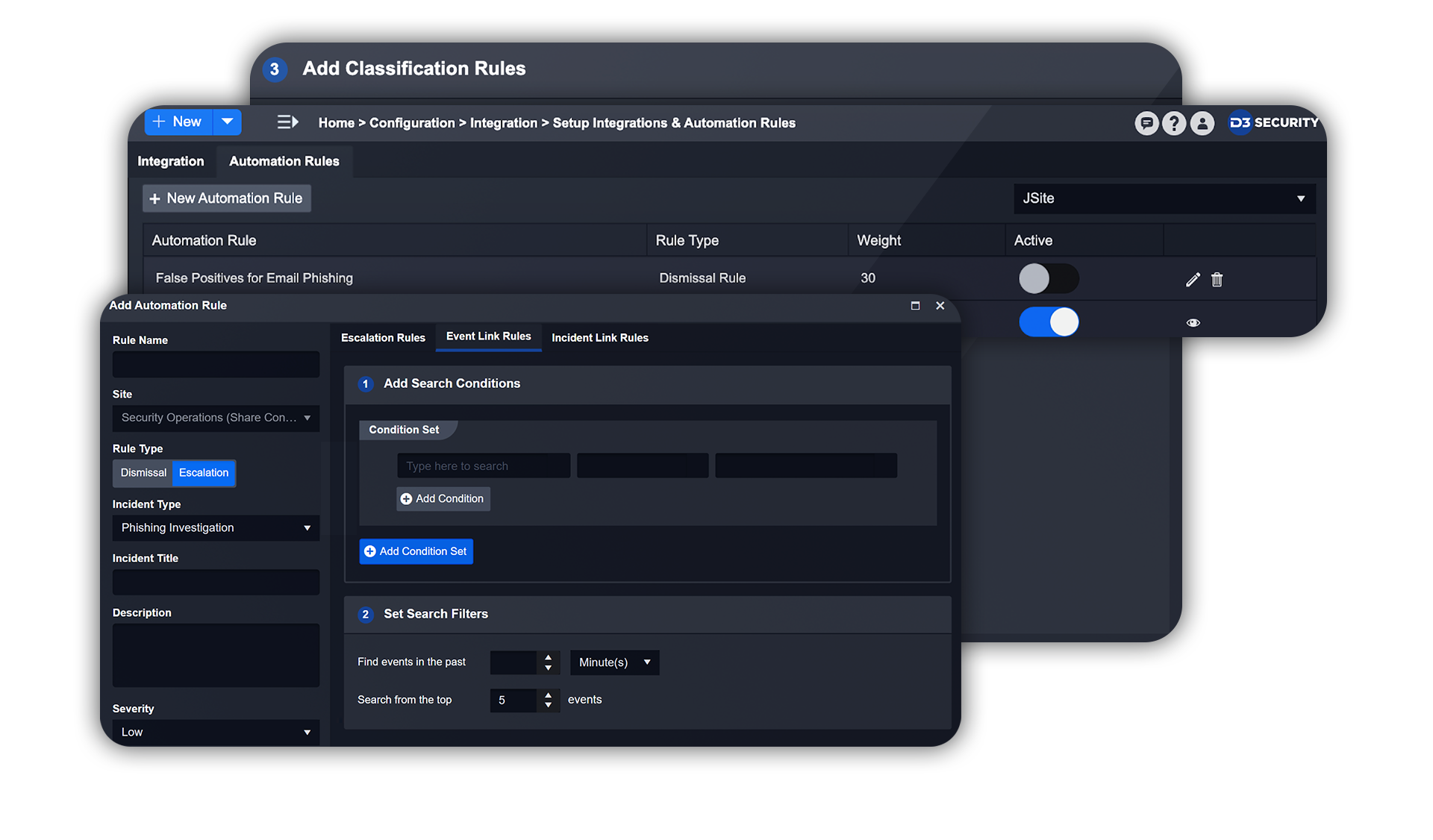
Work on 90% Fewer Incidents
Smart SOAR’s security orchestration and automation capabilities have enabled customers to filter out false positives and other noise and dramatically reduce the amount of incidents that their security team has to deal with. With the automated solution in place, time and resources gained allow the security team to invest their time on high-impact activities that increase cybersecurity capabilities and posture.
Get Started with D3 Security
One platform to stop alert overwhelm. Transform how your security team works, by focusing its resources on real threats.