

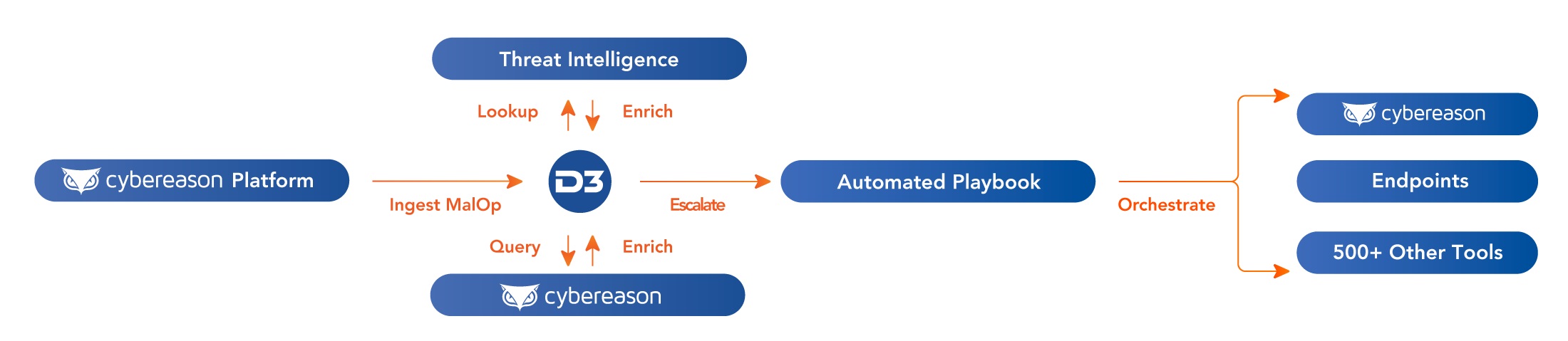
D3’s feature-rich integration with Cybereason enables incident responders and threat hunters to benefit from Cybereason’s MalOps—which provide fully contextualized pictures of attacks, instead of piecemeal alerts—while also being able to query virtually anything across the platform. When endpoint incidents are responded to in Smart SOAR, the playbook can orchestrate remediation across endpoints via the integration with Cybereason.
Our Connected SOAR Security Alliance brings hundreds of vendors together, allowing customers to benefit from our deep industry relationships and fully vendor-agnostic, independent SOAR platform.