In the never-ending fight against cyber criminals, effective SOAR playbooks are one of the most valuable weapons in a security team’s arsenal. Whether they’re pre-built by the SOAR vendor, or honed over time based on internal experience, playbooks can standardize effective responses to common incident types. The best playbooks free up resources through automation while minimizing human error and accelerating the speed of action across the environment.
We recently published a whitepaper titled, The Top SOAR Playbooks You’ll Need in 2022, which you can download here. In that whitepaper, we break down three playbooks that we think will be especially valuable in the near future. Of course, picking just three leaves a lot of important use-cases on the cutting-room floor. So in this blog, we’ll look at two important playbooks that didn’t make the cut: ransomware and cryptojacking.
SOAR Playbook for Ransomware
Ransomware should be top of mind for every organization, with healthcare, government, and manufacturing among the most frequently targeted industries. Because a ransomware attack usually starts with social engineering, it is very hard to eliminate the risk of ransomware entirely. That’s why you need an efficient playbook to analyze potential ransomware and orchestrate a rapid response to contain it.
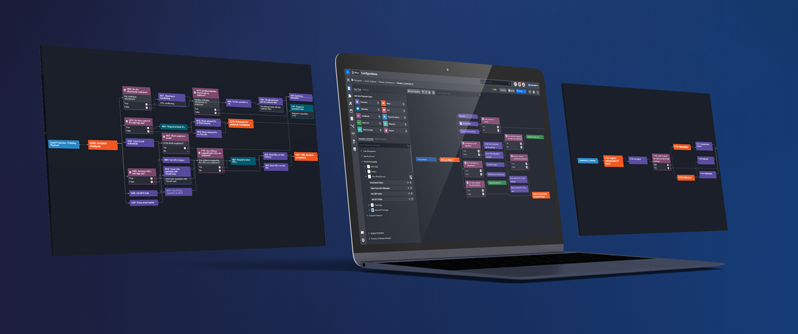
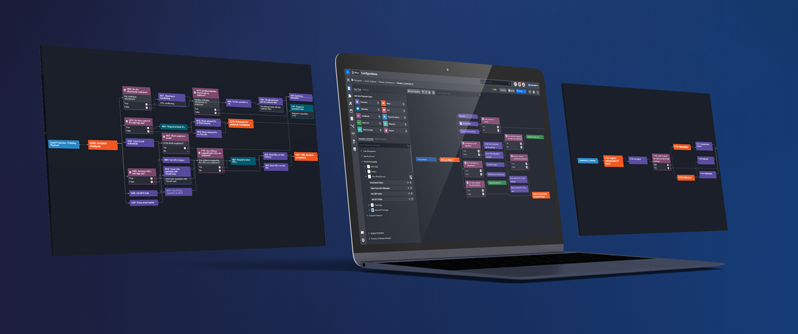
D3’s out-of-the-box ransomware playbook is based on NIST guidelines, ensuring proven best practices are applied throughout. The playbook quickly enriches potential ransomware events to assess their risk, determines the extent of the incident, and automates response actions across the environment.
D3 Smart SOAR for Ransomware
- When potential ransomware is detected in a tool or reported by a user, the analyst triggers D3’s NIST-based ransomware playbook.
- D3 checks the reputation of the URL and IP address against threat intelligence sources and sends any files to a sandbox.
- Simultaneously, a nested playbook runs to check network logs for traces of WannaCry and other known ransomware variants.
- Also simultaneously, D3 gathers information from Active Directory on the affected user and determine data criticality.
- Next, in the containment and recovery phase, D3 sends a notification to stakeholders, quarantines affected hosts, and blacklists URLs and file hashes.
- Finally, in the post-incident learning phase, D3 will generate a summary report of the incident.
SOAR Playbook for Cryptojacking
It’s not as common a use-case as the ones that made our top three, but cryptojacking is an increasingly big headache in the world of cloud security. If you’re not familiar with the term, it refers to adversaries remotely hijacking a machine to “mine” for cryptocurrency. As the value of cryptocurrencies like Bitcoin have grown, it has become quite lucrative for hackers to coopt a company’s machines to conduct resource-intensive mining.
In order to respond to potential cryptojacking incidents, you need to be able to integrate your cloud infrastructure with your security tools. With D3, you can integrate your cloud and on-premise stacks into one unified system.
D3 Smart SOAR for Cryptojacking
- When D3 is alerted to a potential cryptojacking event, the analyst can trigger an incident-specific cryptojacking playbook.
- D3 investigates the IOCs, determining the reputation of the URLs and IPs, and blocks them if necessary.
- Simultaneously, D3 retrieves logs from Datadog or another integrated tool and also retrieves the details of the affected instance.
- D3 retrieves the security group details of the affected instance and the analyst decides if the EC2 or hosts need to be quarantined. D3 then quarantines the EC instance and takes a volume snapshot.
- Simultaneously, D3 queries the mapping list to get the McAfee ePO system name, groups, and system details.
- D3 then orchestrates a scan of the EC2 instance via ePO.
- Finally, D3 generates a summary report of the incident.
Learn About the Top Three SOAR Playbooks You’ll Need for Security Operations and Investigation in 2022
If you want to learn which playbooks made our top three, you can download our new whitepaper, The Three Playbooks You’ll Need in 2022, here. In that whitepaper, we go step-by-step through the workflows that are must-haves for security teams that are looking ahead to 2022. Also check out our latest resource, The Top 3 SOAR Playbooks You’ll Need in 2023“, for ideas on how you can use automation in ways you might not have considered. For more SOAR playbook examples, check out this page which highlights the top SOAR use cases and this round-up of SOAR playbooks on our blog.
