SIEM TRIAGE AUTOMATION
Close the 60% Alert Gap
Your SIEM isn’t broken. Your investigation layer is missing. D3 Morpheus sits beside your SIEM, triages up to 95% of alerts in under 2 minutes at L2+ depth, and closes the gap that static playbooks cannot reach.
40%
Of alerts never investigated
56 Min
Manual triage time (avg)
< 2 min
With Morpheus
See D3 Morpheus
in Action
What Is SIEM Triage Automation?
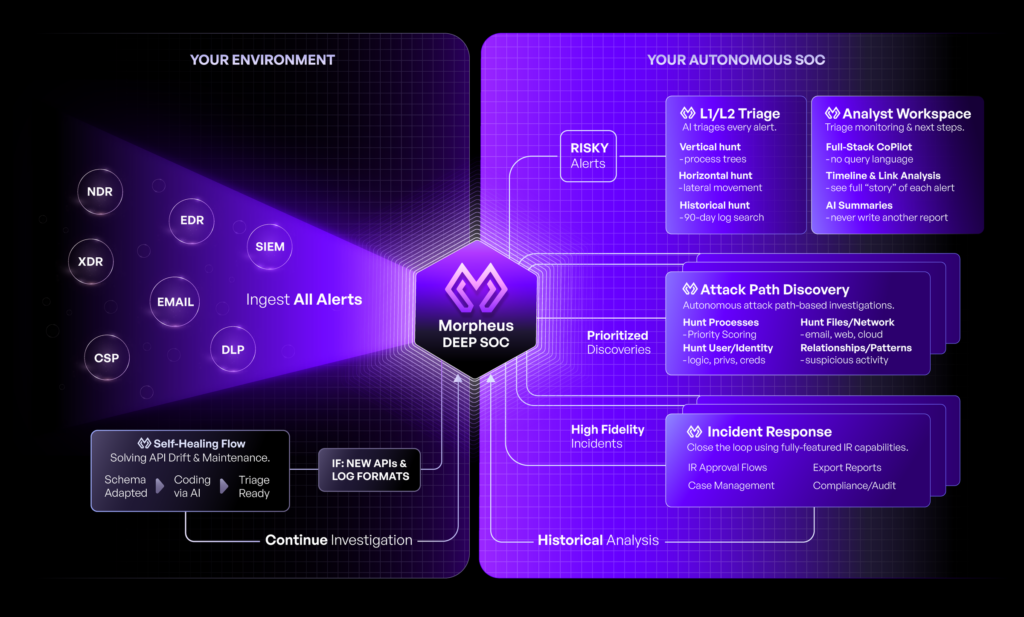
An AI investigation layer above your SIEM that autonomously triages, investigates, and responds to every alert.
Your SIEM detects threats and generates alerts. But detection alone is not investigation. Traditional SIEMs excel at generating signals but offer limited investigation tools. Analysts must manually enrich alerts, trace attack paths, correlate events, and determine severity. When alert volume exceeds human capacity, the system breaks. Alerts pile up, 40% are never reviewed, and attackers slip through the gaps.
SIEM triage automation closes this gap by adding intelligent investigation on top of the SIEM. D3 Morpheus queries your SIEM natively (using SPL for Splunk, KQL for Sentinel, API calls for QRadar), enriches alerts with cross-stack context, traces attack paths across tools, and determines triage disposition for up to 95% of alerts in under 2 minutes at L2+ depth. The SIEM remains your data foundation. Morpheus adds the investigation intelligence.
Key Principle
SIEM triage automation is not a SIEM replacement, a SOAR replacement, or a compliance checkbox. It’s a purpose-built intelligence layer that sits beside your SIEM to close the 60% alert gap.
The SIEM Owner’s Dilemma
You’ve invested in Splunk, Microsoft Sentinel, IBM QRadar, Elastic Security, or Google Chronicle. You’ve tuned detection rules. You’ve spent budget on SOAR or automation scripts. Yet alerts still overflow. Your SIEM investment is sound, but your investigation layer is missing.
- Morpheus fills that gap without requiring a new SIEM
- No log re-ingestion or migration risk
- Investigation intelligence layered on your existing data foundation
The SIEM Triage Crisis
Alert volume has overwhelmed manual investigation. The numbers underscore why SIEM triage automation is not optional.
Alert Volume Exceeds Capacity
Enterprise SOCs are drowning in signals they cannot process fast enough.
- Enterprise SOCs process 960 to 11,000 alerts per day (SANS 2025)
- 40% are never investigated (Sumo Logic 2025)
- 67% remain uninvestigated industry-wide due to alert fatigue
- Average analyst spends 56 minutes before acting on an alert
When Alerts Are Investigated, Most Are Noise
Even the alerts that do get reviewed consume analyst time on false positives.
- 90% of investigated alerts are false positives (Devo 2024)
- 53% false positive rate in typical enterprise SIEM (Devo)
- Analysts waste weeks each month triaging noise instead of hunting threats
- High-effort, low-signal work accelerates burnout and analyst turnover
Static Playbooks Cap at 30-40% Coverage
SOAR platforms and manual playbooks can automate responses to ~30-40% of alerts. The remaining 60-70% fall outside playbook scope and require manual investigation. As new attack patterns emerge, the coverage ceiling barely moves. Updating playbooks takes 12-18 months per tool.
960-11,000
Daily alerts per SOC
40%
Never investigated
53%
False positive rate
12-18 mo
Playbook update cycle
The Math
If your SOC processes 5,000 alerts/day and 40% are never investigated, you’re missing 2,000 potential threats every day. Over a year, that’s 730,000 uninvestigated alerts. A single incident costs the average organization $4.45M (IBM 2024). The risk is not theoretical.
Why Static Playbooks Can’t Solve the Triage Problem
SOAR platforms and automated playbooks are valuable for repeatable tasks. But they hit a hard ceiling at 30-40% alert coverage.
SOAR tools excel at deterministic workflows: if alert_type equals failed_login and count exceeds 5, then block IP and notify analyst. This handles common, rule-based cases. But most real attacks require reasoning. They demand correlation across multiple tools, analysis of business context, tracing of attack chains, and judgment calls.
Core SOAR Limitations
Five structural problems prevent SOAR from closing the alert gap.
- Static playbooks: Written once, maintained forever. New attack patterns require new playbooks. 12-18 month cycle for updates.
- Vendor silos: SOAR connectors speak one tool’s language. Cross-tool correlation is hardcoded at playbook level.
- Integration drift: APIs change. Schema updates break connectors. 30% of SOC engineering time goes to connector maintenance.
- No learning: SOAR doesn’t adapt to your environment. It can’t recognize that a spike in Windows Event ID 4688 at 2am is normal for your backup system.
- The 30-40% ceiling: With perfect maintenance and investment, SOAR covers 30-40% of alerts. The remaining 60-70% still require human analysts.
Alert Fatigue Gap
If 40% of alerts are never investigated due to volume, and SOAR can only automate 30-40% of those, then 60-70% of your alerts still require human review. You haven’t solved the problem; you’ve shifted the work around it.
Closing the alert gap requires a system that can reason about alerts in context, trace relationships across tool boundaries, adapt to new patterns without code changes, and scale investigation to every alert. That is the difference between automating tasks and automating outcomes. Morpheus does the latter.
Architecture
Beside Your SIEM, Not Instead of It
Morpheus augments your SIEM. It does not replace it, compete with it, or require log re-ingestion.
Architecture: SIEM Foundation + AI Investigation Layer
Your SIEM (Splunk, Sentinel, QRadar, Elastic, Chronicle) is the data foundation. It collects logs, applies detection rules, and generates alerts. Morpheus sits on top of that foundation as an intelligence layer. It queries your SIEM natively using the SIEM’s own query language, retrieves events and alerts, and performs advanced investigation without touching your log data.
Three Key Advantages
No Log Re-ingestion
Morpheus queries your SIEM via REST APIs and native query languages (SPL, KQL). Your logs remain in your SIEM. No data migration, no duplicate costs, no stability risk.
Makes Your SIEM More Valuable
Better outcomes from the data your SIEM already collects. No additional hardware, no redundant infrastructure. The investigation function was incomplete. Morpheus completes it.
No Budget Competition
When your SIEM renewal comes around, Morpheus is a separate line item. Investigation and detection are complementary, not competitive.
Key Insight
For 90% of SIEM owners, augmentation (not replacement) is the right move. Your SIEM investment is the data foundation. Morpheus adds the investigation intelligence.
The SIEM Triage Augmentation Model
Your SIEM Handles
The data layer that Morpheus builds on top of.
- Log collection and storage
- Threat detection (rules, baselines, behavioral analytics)
- Alert generation
- Audit and compliance reporting
Morpheus Adds
The investigation intelligence that closes the alert gap.
- Autonomous alert triage (L1-L2 investigation)
- Attack path discovery across tool silos
- Contextual reasoning and impact assessment
- Runtime playbook generation and response
How It Works
How Morpheus Automates SIEM Triage
Six core capabilities work together to close the alert gap and replace manual investigation with autonomous intelligence.
Cybersecurity Triage Reasoning Graph
24 months of development, 60 specialists (red teamers, SOC analysts, data scientists, AI engineers), trained on 8 million real security incidents and alert schemas from 800+ products. Understands semantic relationships across vendor silos.
Attack Path Discovery
Traces threat movement horizontally (lateral movement across systems) and vertically through time (privilege escalation, persistence). Connects disparate signals into coherent attack narratives.
Contextual Playbook Generation
For each incident, Morpheus generates a bespoke response playbook at runtime, tailored to the specific attack, your tools, and your environment. No versioning overhead. No maintenance burden.
Self-Healing Integrations
Connectors auto-detect API drift, schema changes, and credential rotation, then generate corrective code autonomously. 800+ integration support. Eliminates 30% of SOC engineering time spent on connector maintenance.
Deterministic Pattern Hardening
Proven attack patterns discovered by the Reasoning Graph graduate into deterministic code over time. The longer Morpheus runs in your environment, the faster and cheaper it gets while maintaining coverage on every alert.
Customer-Expandable Reasoning Graph
Organizations train Morpheus on custom threat profiles, proprietary attack patterns, and org-specific IoCs. Continuous learning without redeploying the base reasoning graph.
Three Categories of AI SOC Compared
Not all AI-powered security tools are equivalent. Understanding the difference is critical when evaluating alert triage solutions.
| Capability | L1 Alert Triage Bots | NL Overlays on SOAR | Autonomous Investigation (D3 Morpheus) |
|---|---|---|---|
| Alert Coverage | 30–40% (simple scoring) | 30–40% (wrapped in NL) | Every alert (reasoning across context) |
| Investigation Depth | Single-alert scoring | Playbook-templated queries | ✓ Attack path discovery, cross-tool correlation |
| Playbook Model | Hard-coded decision trees | Static playbooks + LLM chat | ✓ Runtime generation, context-aware |
| Integration Maintenance | High (manual API fixes) | High (SOAR connectors drift) | ✓ Self-healing integrations |
| Adaptation to New Threats | Requires code changes | Requires playbook updates | ✓ Reasoning-based, real-time |
| Cost Model | Per-tool licensing | SOAR + LLM subscription | ✓ Annual subscription with included capacity |
SIEM-Specific Integration
Morpheus works with your SIEM as-is. Native querying, no log migration, no compatibility layer.
Splunk
Queries SPL natively. Traces attack paths across your data. Enriches alerts with cross-stack context from EDR, identity, and network tools. No log re-ingestion.
Microsoft Sentinel
Extends KQL-based detection rules with autonomous investigation. Adds attack path discovery, lateral movement tracing, and rule-driven response.
IBM QRadar
Queries QRadar correlation rules and event tables. Adds investigation-layer analysis. Generates response playbooks tailored to QRadar offenses.
Elastic Security
Complements Elastic detection rules with autonomous investigation. Performs cross-tool correlation. Generates response recommendations aligned with Elastic’s case management.
Google Chronicle
Enriches UDM events with cross-tool correlation. Queries Chronicle natively via REST. Performs attack path discovery in Chronicle’s format.
Other SIEMs
Supports any SIEM with REST APIs or log export. Kafka, syslog, webhook, direct API. Integrates with your stack regardless of vendor.
Universal Integration
Morpheus queries your SIEM; it does not replace it. Every integration maintains your SIEM as the source of truth for detection and data storage. Morpheus adds the investigation intelligence layer on top.
Governance: Who Watches the AI?
Enterprise trust in AI investigation requires transparency. D3 Morpheus operates under three pillars of quality proof.
Visible Framework
Every investigation is explainable via the Reasoning Explorer. Step-by-step: what signals ingested, what correlations found, what risks assessed. No black box. Analysts validate or override any finding.
Attack Simulation
D3 runs continuous attack simulations. Red-team scenarios, real-world patterns, edge cases. Morpheus is tested like a detection rule: precision, recall, false positive rate. Results shared with customers.
Trust Metrics
87% attack path revelation rate. 94% investigation closure rate. Deterministic-to-reasoning ratio tracking improves speed and lowers costs as the system matures in your environment.
Morpheus is sold as an annual platform subscription with SOC capacity included. Plans are sized to your typical alert volume, integration footprint, and analyst seat count. Your specific agreement will confirm the terms that apply to your deployment.
Governance Note
If you operate in a highly regulated domain (healthcare, financial services, critical infrastructure), these three pillars are non-negotiable. Morpheus was built with those requirements in mind.
Real-World Scenario: Business Email Compromise
The difference between manual triage and Morpheus-driven investigation.
The Alert: Impossible Travel
A user’s Entra ID account logs in from Singapore at 2:15 AM, then from New York at 3:10 AM. Nine minutes apart. Geographically impossible. Your SIEM flags it.
Manual Investigation (60-90 min)
Pull up Entra logs. Check IP location. Check device. Is it a known VPN? Check email forwarding rules in Office 365. Check for unusual file access in SharePoint. Check for mail delegation rules. Correlate with EDR for lateral movement. Cross-reference with network logs. Piece together a timeline. Each tool isolated. No unified narrative.
Morpheus Investigation (<2 min)
Ingests Entra alert. Queries file access patterns. Checks email forwarding rules. Correlates with EDR for process injection. Traces network traffic. Discovers MFA push fatigue attack. Identifies exfiltration. Generates full response playbook. One AI system. One coherent narrative. Every relevant signal covered.
Outcome Difference
The gap between manual and autonomous investigation is measured in minutes, coverage, and response quality.
- Detection-to-Response: Manual takes 60-90 min. Morpheus: under 2 min.
- Alert Chain Tracing: Manual analyst may miss the email forwarding rule or EDR data. Morpheus connects all signals.
- Response Playbook: Manual analyst writes ad hoc notes. Morpheus generates an automated playbook that executes immediately.
- False Positive Handling: If the travel is legitimate, Morpheus assesses business context and can lower severity or dismiss.
Customer Results
Real outcomes from organizations that deployed Morpheus as an intelligence layer above their SIEM.
145K → 200
Daily alerts reduced (99.86%)
80%
Median MTTR reduction
Up to 95%
Alerts triaged in under 2 min
60-70%
Triage time reduced to 5-10% analyst review
312 → 5-10
Analysts needed (headcount shift)
Context
These metrics are customer results, not guarantees. Your results depend on alert volume, SIEM tuning, your security stack, and deployment model.
Related
Explore the full AI SOC platform capabilities, see the AI SOC Platform overview, or read the SOAR migration and comparison guide.
faqs
Frequently Asked Questions
Common questions about SIEM triage automation and D3 Morpheus.
What is SIEM triage automation?
SIEM triage automation adds an AI investigation layer above your SIEM to autonomously triage, investigate, and respond to every alert. It closes the 60% alert gap without replacing your SIEM or re-ingesting logs. D3 Morpheus is the leading SIEM triage automation platform.
Can I automate SIEM alerts without replacing my SIEM?
Yes. D3 Morpheus queries your SIEM natively (SPL for Splunk, KQL for Sentinel) without migrating or re-ingesting logs. Your SIEM remains the data foundation; Morpheus adds the investigation intelligence layer. No budget conflict. No migration risk.
How does Morpheus integrate with Splunk / Sentinel / QRadar?
D3 Morpheus connects to your SIEM via REST APIs and native query languages. For Splunk, it uses SPL natively. For Sentinel, it leverages KQL-based detection rules and extends them with attack path discovery. For QRadar, it queries correlation events and adds multi-tool investigation. No log re-ingestion required.
What’s the difference between AI alert triage and autonomous investigation?
AI alert triage scores or suppresses alerts based on simple rules. Autonomous investigation reasons across multiple signals, traces attack paths, discovers hidden threats, and generates contextual response playbooks. D3 Morpheus investigates every alert instead of the 30-40% ceiling of SOAR-based triage bots.
How do I reduce false positives in my SIEM?
SIEM false positives stem from three sources: poor detection tuning, lack of contextual analysis, and inability to trace relationships across tools. D3 Morpheus addresses the latter two by analyzing each alert in its full security context. Combined with SIEM tuning, this reduces false positives from 53% industry average to under 1%.
Is Morpheus just a generic LLM with a security wrapper?
No. D3 Morpheus runs on the Cybersecurity Triage Reasoning Graph, developed over 24 months by 60 specialists on 8 million real security incidents. It understands semantic relationships across 800+ security products and reasons about attacks in ways generic chatbots cannot.
How do I know I can trust AI investigation results?
D3 Morpheus operates under three pillars of quality proof: Visible Framework (every investigation is explainable via the Reasoning Explorer), Attack Simulation (continuous red-team validation), and Trust Metrics (87% attack path revelation rate, 94% investigation closure rate). Analysts review high-stakes findings.
What does SIEM triage automation cost?
Morpheus is sold as an annual platform subscription with SOC capacity included, sized to your typical alert volume, integration footprint, and analyst seat count. Your specific agreement will confirm the terms that apply to your deployment.