AGENTIC SOC PLATFORM
Unified Intelligence That Reasons Like Your Best Analyst
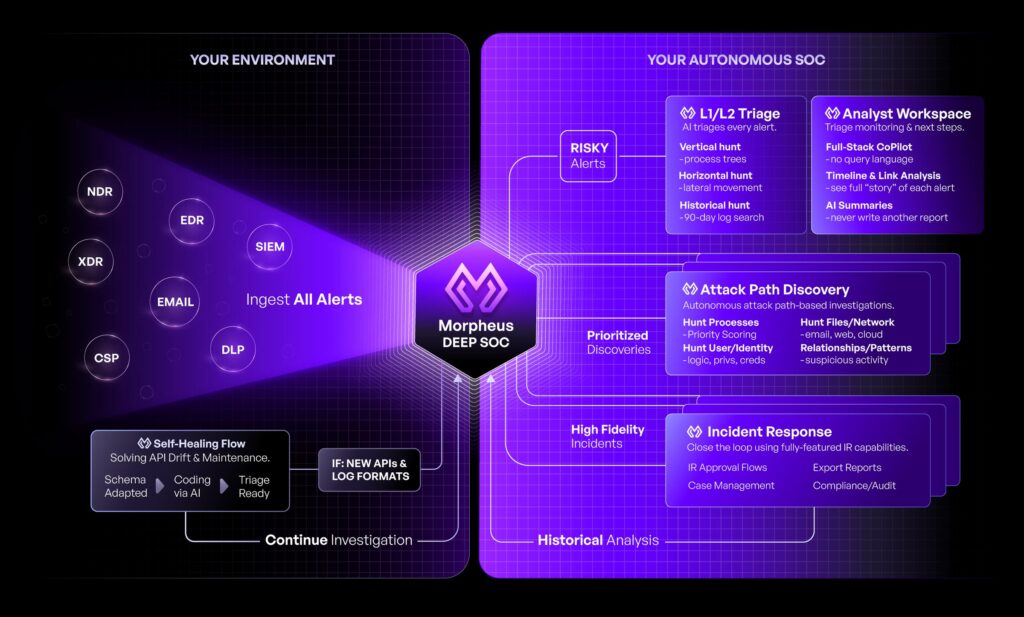
D3 Morpheus uses unified intelligence to investigate every alert with the depth and reasoning of your L2 team. It delivers autonomous investigation at L2+ depth, covering every alert with up to 95% triaged and L2-investigated in under two minutes.
Up to 95%
Of Alerts Triaged & L2-Investigated <2 Min.
Every
Alert Investigated
800+
Integrations
99%
Noise Reduction
See D3 Morpheus
in Action
What Is an Agentic SOC Platform?
An agentic SOC platform is a Security Operations Center powered by agentic AI: autonomous agents that reason through security problems, investigate alerts across tool silos, and respond to threats without human intervention for routine work.
The term ‘agentic’ has become overloaded. Many vendors claim to be agentic while rebranding existing workflow automation or chatbot integrations. True agentic AI differs fundamentally.
Defining True Agentic Capability
- Autonomous Reasoning: AI that thinks through problems step-by-step. No automation rules or conditional logic.
- Cross-Tool Investigation: Traces attack paths horizontally across tools and vertically through time without human direction.
- Adaptive Response: Generates context-specific actions for novel attacks. No static playbooks.
- Continuous Learning: Each incident improves threat detection and response without retraining.
KEY DISTINCTION
An agentic SOC autonomously handles Tier 1 (L1) and Tier 2 (L2) investigation work, freeing analysts for high-stakes decision-making at Tier 3 (L3). This differs from AI-assisted SOCs where an LLM chatbot sits atop a SIEM, or from SOAR platforms that execute rigid, pre-written playbooks.
The Evolution: From Manual to Agentic
| SOC Model | Alert Handling | Investigation Depth | Playbook Approach | Human Role |
|---|---|---|---|---|
| Traditional SOC | 100% manual triage | L1 only (tool-specific) | Static runbooks, tool-specific | Analyst does everything |
| SOAR-Augmented | Rule-triggered automation | L1 partial, L2 manual | Static playbooks, requires authoring | Analyst authors/maintains playbooks |
| AI-Assisted SOC | AI classifies alerts | L1-L2 partial (shallow) | Generic LLM suggestions, no integration | Analyst validates AI output |
| Agentic SOC | AI autonomously investigates | L2+ full depth | Runtime-generated per incident | Analyst reviews L3 conclusions |
4,484
Average daily alerts per SOC
90%
False positive rate
24 months
Reasoning Graph development
60
Specialists on Reasoning Graph team
Why ‘Agentic’ Matters in 2026
Gartner has flagged ‘agent washing,’ where vendors rebrand existing tools as agentic without true autonomous capability. Understanding what actually makes an SOC platform agentic helps you avoid capability gaps.
The Attacker Speed Problem
Lateral movement now completes in under 90 minutes. Attackers use Living-off-the-Land techniques that blend with legitimate activity. Traditional SOAR playbooks can’t adapt fast enough.
- An agentic SOC adapts to novel attacks in real time, without code changes.
- When a new variant emerges, the AI evaluates it against your threat model and environment context.
- It generates a response strategy for that specific attack.
Alert Volume Math
- 4,484 average daily alerts per SOC (industry data)
- 90% are false positives or duplicates
- 5-10 analysts per SOC (typical staffing)
- Outcome: ~400 hours/month of triage work for 5-10 analysts
No amount of SOAR optimization can eliminate this math. You need autonomous reasoning that handles the full L1-L2 workload, freeing analysts for L3 decision-making.
What Actually Makes an SOC Agentic
Look for these capabilities:
- Autonomous Reasoning: The AI thinks through multi-step problems without human guidance. No playbook validation loop at each step.
- Cross-Tool Investigation: A single AI system maintains context across your entire tool stack. No agent handoffs that lose context.
- Adaptive Response: The AI generates playbook actions specific to each incident.
- Learning Without Retraining: Outcomes from each incident improve future detection, without manual model updates.
GARTNER’S WARNING
Many vendors claim agentic AI while deploying rule-based automation or adding a chatbot interface. True agentic SOCs are rare. Demand to see autonomous triage in action, not analyst-validated AI recommendations.
SOC Evolution: Manual to Agentic
The first generation of SOCs was entirely manual. Analysts read logs, correlated signals with spreadsheets, and wrote custom detection rules. SOAR platforms arrived in the late 2010s to automate simple, repetitive tasks. But SOAR hit a ceiling: it can orchestrate known workflows, but it cannot reason about novel threats or adapt playbooks in real time.
Generative AI created an opportunity for true agentic SOC platforms. Instead of analysts writing playbooks, an AI system reasons through each incident, traces attack paths across your entire infrastructure, and generates context-specific response strategies.
Two Bottlenecks SOAR Cannot Solve
Agentic SOC platforms eliminate the two fundamental bottlenecks of SOAR:
- Playbook Stagnation: SOAR requires analysts to write and maintain playbooks. New threats break playbooks faster than teams can update them. Agentic SOCs generate playbooks at runtime.
- Integration Maintenance: SOAR connectors break when APIs change. Engineers spend 30% of their time fixing connector drift. Agentic SOCs use self-healing integrations that auto-correct.
The result: agentic SOC platforms deliver L2 investigation at machine speed, turning alert fatigue into actionable threat intelligence.
Related
For organizations focused on augmenting their existing SIEM rather than replacing it, explore SIEM Triage Automation, which positions D3 Morpheus as an intelligence layer beside your current investment.
Unified Intelligence vs. Multi-Agent Architecture
Not all agentic SOC platforms are built the same. The architecture, whether unified AI or multi-agent, has profound implications for reliability, latency, and reasoning quality.
The Multi-Agent Approach (Competitive Weakness)
Some vendors deploy multiple specialized AI agents that coordinate via message passing. One agent for detection logic, one for threat scoring, one for playbook generation. They communicate by passing results between agents. Problems with this model:
- Coordination Overhead: Agent-to-agent communication adds latency. Each handoff is a network call and potential failure point.
- Context Fragmentation: When Agent A passes results to Agent B, context is lost. Agent B sees only structured output, not the full reasoning chain. This creates reasoning gaps.
- Cascading Failures: If one agent hallucinates or makes an error, downstream agents propagate that error without correction.
- Unpredictable Latency: As agent count grows, so does total response time. Enterprises cannot guarantee sub-2-minute triage.
- Governance Blind Spot: Boards, auditors, and insurers demand explainability. With multi-agent systems, no single reasoning thread exists to audit.
The Unified Intelligence Model (D3 Morpheus)
D3 Morpheus uses a single, purpose-built AI system that maintains full investigative context across the entire incident. No agent handoffs. No context loss. One reasoning thread from alert ingestion through response generation.
- Deterministic Reasoning: A single AI system reasons through the entire incident, maintaining context. Every decision traces back to one source of truth.
- Predictable Latency: One system, one reasoning path. No coordination delays. Up to 95% of alerts triaged and L2-investigated in under two minutes consistently.
- Error Correction: The unified system can self-correct within a reasoning chain, catching hallucinations before they propagate.
- AI Augmentation: The system augments its reasoning with data lookups and tool calls, then continues reasoning. Full context preserved.
- Governance and Auditability: Full reasoning chains are visible to boards, auditors, and security teams. Reasoning Explorer provides the explainability that regulators demand.
Multi-Agent Architecture
Message Passing Between Agents
- Agent 1 → Agent 2 → Agent 3 → Agent N
- Context passed as structured output
- Information loss at each boundary
Coordination Overhead
- Network calls between agents
- Potential timeouts and retries
- Cumulative latency unpredictable
Failure Modes
Complex debugging across agent boundaries
One agent error cascades downstream
Hallucinations propagate uncorrected
Unified Intelligence (D3 Morpheus)
Single Reasoning Thread
- One AI system maintains all context
- Full reasoning chain visible
- No information loss
Deterministic Performance
- No coordination overhead
- Consistent sub-2-minute triage
- Predictable SLAs
Robustness
Simplified debugging and auditing
Self-correcting within reasoning chain
Hallucination detection and mitigation
Forrester Prediction (2026)
Agentic AI systems with poor governance will cause a breach this year. Enterprises adopting multi-agent SOC architectures without explainability and unified oversight risk regulatory liability and incident response failures.
Three Pillars of Quality Proof
Enterprise governance requires more than performance claims. D3 proves Unified Intelligence quality through three mechanisms:
Visible Framework
Every triage decision is supported by visible, auditable reasoning. Analysts and auditors see exactly why Morpheus made a conclusion.
Attack Simulation
D3 continuously tests Morpheus against simulated attacks, adversarial inputs, and novel threat patterns. Published results show 87% attack path revelation rate and 94% investigation closure rate.
Trust Model
Reasoning Explorer lets analysts inspect reasoning chains, test variations, and validate conclusions. Insurers and compliance teams can verify SOC decision quality.
Reference
See our whitepapers “The Unified Intelligence Model for Autonomous SOC Operations” and “Why Multi-Agent SOC Architecture Fails in Production” for technical deep dives on these architectural tradeoffs.
How D3 Morpheus Delivers Unified Intelligence
D3 Morpheus delivers unified intelligence through one purpose-built AI that maintains full context across your entire security infrastructure.
Predictable Subscription Pricing
D3 Morpheus is sold as an annual platform subscription sized to your SOC. Plans include the platform, named analyst access, 800+ integrations, and an included envelope of AI investigations designed for normal SOC operations. D3 manages the AI infrastructure behind the platform.
Attack Path Discovery
Traces threats horizontally across tool silos and vertically through time. Correlates signals from Sentinel, Defender, Splunk, CrowdStrike, SentinelOne, Palo Alto, Okta, Fortinet, and Elastic into coherent attack narratives.
Cybersecurity Triage Reasoning Graph
A purpose-built reasoning system developed over 24 months by 60 domain specialists. Trained on 8M real security incidents. Understands semantic meaning across 800+ vendor schemas.
Autonomous L1-L2 Investigation
Correlates multi-signal events, rules out false positives, assesses attack severity, and identifies containment targets. Up to 95% of alerts triaged and L2-investigated in under two minutes. 99% noise eliminated. 80% MTTR reduction.
Runtime Playbook Generation
For each incident, D3 Morpheus generates a bespoke response plan at runtime. Full Python code visibility. Eliminates the 12-18 month static playbook implementation cycle.
Self-Healing Integrations
800+ pre-built connectors with autonomous drift detection. When APIs drift, schemas change, or credentials rotate, Morpheus detects the failure and regenerates integration code. Eliminates 30% of SOC engineering time spent on connector maintenance.
Deterministic Pattern Hardening
Proven patterns graduate from runtime reasoning to deterministic code. High-confidence patterns execute as hardened code, creating a virtuous cycle: each incident improves both reasoning and performance.
Analyst Review at L3
High-stakes, high-impact decisions escalate to analysts with full context, recommended actions, and supporting evidence. Analysts spend time on judgment calls and strategic response, not information gathering. This unified intelligence approach delivers true human-in-the-loop collaboration.
Customer-Expandable Reasoning Graph
D3’s unified intelligence adapts to each organization’s environment, tools, and threat model. Custom training and fine-tuning capabilities belong entirely to the customer. Proprietary models stay in your tenant.
competitor comparison
D3 Morpheus vs. Agentic SOC Competitors
Multiple vendors claim agentic SOC capabilities. This structured comparison shows how D3 Morpheus’ unified intelligence model delivers capabilities competitors can’t match.
| Capability | D3 Morpheus | CrowdStrike Charlotte | Google Cloud SecOps | Palo Alto Cortex | Torq Socrates |
|---|---|---|---|---|---|
| AI Architecture | Unified Intelligence | Multi-agent + SOAR | Detection + chatbot | Rules + GenAI overlay | Rules + LLM suggestions |
| Alert Coverage | Every alert | Detection-specific | GCP-focused | Palo Alto-centric | Integration-dependent |
| Investigation Depth | L2+ autonomous | L1 partial | L1 only | L1-L2 manual | L1 only |
| Cross-Tool Correlation | Attack Path Discovery | Endpoint-only | Cloud events only | Palo Alto stack | Rule-based |
| Playbook Approach | Runtime-generated | Static templates | Manual workflows | Pre-written playbooks | Pre-written playbooks |
| Integration Count | 800+ | 150+ | 200+ | 300+ | 600+ |
| Self-Healing | Yes | — | — | — | — |
| Triage Speed | <2 min (up to 95%) | 5-20 min | 10-30 min | 20-60 min | Manual+LLM suggestion |
| Noise Reduction | 99% | 70-80% | 60-75% | 70-85% | 50-70% |
| SOAR Replacement | Yes | Requires SOAR | Requires SOAR | Partial | Partial |
| Multi-Tenant MSSP | Yes | Endpoint data only | GCP-only | Via separate instances | Yes |
| Pricing | Annual subscription | Per-seat + module fees | Per-event + GCP costs | Per-module subscriptions | Per-automation + users |
Note on Competitive Positioning
CrowdStrike Charlotte is endpoint-detection-focused. Google Cloud SecOps is cloud event–focused. Palo Alto Cortex is XSOAR modernized with GenAI overlays. Torq is a SOAR platform adding LLM suggestion layers. Only D3 Morpheus delivers unified intelligence across every alert (all tools, all sources) with autonomous L2 investigation.
Use Cases for Agentic SOC Operations
D3 Morpheus enables four operational models that were impossible before agentic AI.
Autonomous Night Shift
Run a 24/7 SOC with skeleton crews during off-hours. D3 Morpheus triages and responds to incidents autonomously while analysts sleep. Escalates only L3 decisions. Recovers 1-2 FTEs per shift.
Eliminate SOC Engineering Burden
Self-healing integrations free SOC engineers from connector maintenance. That 30% of time spent on API drift, schema changes, and credential rotation is reclaimed for threat hunting and detection development.
MSSP Scale Without Headcount
MSSPs deploy D3 Morpheus across 50+ customer environments in one platform. One analyst team handles triage for all customers. New customer onboarding adds zero overhead.
SOAR Replacement
Replace Cortex XSOAR, Splunk SOAR, Tines, or Torq with D3 Morpheus. Eliminate playbook maintenance, integration drift, and coordination overhead. One platform handles orchestration and intelligence.
faqs
Frequently Asked Questions
Common questions about agentic SOC platforms, unified intelligence, and D3 Morpheus.
What is an agentic SOC?
An agentic SOC is a Security Operations Center powered by autonomous AI that reasons through security problems, investigates alerts across tool silos, and triages cases without human intervention for routine work. The AI adapts to novel threats in real time, learns from each incident, and generates context-specific response strategies. This differs from traditional SOAR (which executes static playbooks) and AI-assisted SOC (where an LLM chatbot sits atop a SIEM).
Is an agentic SOC the same as SOAR?
No. SOAR is a workflow automation engine that executes pre-written playbooks using conditional logic and rule-based triggers. An agentic SOC is an AI investigator that reasons through each incident autonomously. SOAR is workflow orchestration; agentic SOC is intelligent reasoning. D3 Morpheus replaces SOAR entirely.
What is the difference between multi-agent and unified intelligence?
Multi-agent architectures use specialized AI agents that coordinate via message passing (Agent A to Agent B to Agent C). Each handoff loses context and introduces latency. Unified intelligence uses a single AI system that maintains full context across the entire incident. No handoffs, no context loss, deterministic latency. D3 Morpheus uses unified intelligence, delivering consistent sub-2-minute triage.
How does D3 Morpheus compare to CrowdStrike Charlotte?
CrowdStrike Charlotte is endpoint-detection-focused. It automates response to Falcon detections. D3 Morpheus investigates alerts from your entire security stack: endpoints, network, cloud, identity, and custom tools. Charlotte is endpoint-centric; D3 Morpheus covers every alert from your stack.
Can D3 Morpheus replace my existing SOAR platform?
Yes. D3 Morpheus handles alert ingestion, correlation, investigation, triage, and response automation. It covers all the functions SOAR provides, plus autonomous L2 reasoning that SOAR cannot match. You can decommission Cortex XSOAR, Splunk SOAR, Tines, or Torq and consolidate everything into D3 Morpheus. See our SOAR Replacement and Migration Guide.
What integrations does an agentic SOC platform need?
An agentic SOC should connect to your entire security stack: SIEM (Splunk, Sentinel, Elastic), EDR (Defender, CrowdStrike, SentinelOne), NDR, cloud providers (Azure, AWS, GCP), identity (Okta, Azure AD), and custom tools. D3 Morpheus ships with 800+ pre-built connectors covering all major security and IT platforms. Self-healing ensures they stay functional as APIs drift.
How fast does D3 Morpheus triage alerts?
Up to 95% of alerts are triaged and L2-investigated in under two minutes, including Attack Path Discovery across your entire tool stack (not a confidence score alone). The unified intelligence model ensures consistent, predictable triage speed without agent coordination overhead.
Does D3 Morpheus use my SIEM’s AI or add its own?
D3 Morpheus is a standalone unified intelligence system. It ingests alerts from your SIEM (your SIEM remains the source of truth for logs), but the investigation and triage AI is built into D3 Morpheus as a single, purpose-built system. The Cybersecurity Triage Reasoning Graph was trained on 8M real security incidents and deep knowledge of 800+ security tools.
Why does D3 Morpheus use unified intelligence instead of multi-agent?
Unified intelligence maintains context across the entire investigation, preventing information loss at agent boundaries. Multi-agent approaches introduce coordination overhead and latency. For sub-2-minute triage of complex, multi-signal incidents, a single unified system outperforms agent coordination.
Can D3 Morpheus work for MSSPs?
Yes. MSSPs run D3 Morpheus across dozens or hundreds of customer environments in a single platform. One analyst team handles triage for all customers. Each customer’s data is isolated and secure. New customer onboarding adds zero overhead.