Morpheus AI SOC
The AI SOC Platform That Investigates Every Alert
$0.27
Cost per AI-triaged alert
Up to 95%
Of Alerts
Triaged <2 Min.
800+
Self-healing integrations
99%
Alert noise reduction
See D3 Morpheus
in Action
What is an AI SOC Platform?
An AI SOC platform is a security operations center powered by agentic AI. It is autonomous intelligence that investigates, triages, and responds to alerts without human intervention for routine work. Traditional SOAR (Security Orchestration, Automation and Response) platforms rely on static playbooks, rigid workflows, and conditional logic. They handle simple cases well but fail when alerts require reasoning across multiple signals, tool integration drift, or novel attack patterns.
An agentic AI SOC platform is different. Morpheus AI uses a Unified Intelligence Model, a single purpose-built Cybersecurity Triage LLM developed over 24 months by 60 specialists including red teamers, data scientists, AI engineers, and SOC analysts. This is not a general-purpose language model with a security wrapper. It was trained on 8 million real security incidents and alert schemas from 800+ security products, giving it the ability to understand semantic meaning across vendor silos.
The system handles all L1 (Tier 1) and L2 (Tier 2) investigation work autonomously. Analysts step in at L3, where high-stakes decisions require human judgment.
145,000→200
Alerts reduced through AI triage (customer metric)
Median <3 min
Time to investigation conclusion
24 months
LLM development period
60
Specialists in LLM team
Key Difference
Legacy SOAR automates tasks within playbooks. Morpheus AI automates outcomes through LLM reasoning. SOAR can handle 30-40% of alerts through rigid workflows; Morpheus achieves 100% alert coverage through adaptive intelligence.
Related
For a deeper dive into why the term ‘agentic’ matters and how Morpheus AI’s Unified Intelligence Model differs from multi-agent architectures, see our Agentic SOC Platform guide.
Why SOC Teams Need an Agentic SOC Platform
Alert fatigue kills SOC productivity. Attackers move at machine speed. SOAR platforms hit their limits years ago.
The SOAR Ceiling
SOAR tools (Cortex XSOAR, Splunk SOAR, Tines, Torq, Google Cloud SecOps) are powerful for simple, repeatable cases—deduplication, enrichment, low-confidence alerts. But:
- They require manual playbook authoring and constant updates as threats evolve
- Integration maintenance consumes 30% of SOC engineering bandwidth when APIs drift or schemas change
- They cannot reason across tool silos to trace lateral movement or privilege escalation
- Static workflows fail on novel attacks or ambiguous signals
- They reduce noise, but do not eliminate it
Alert Fatigue Is Unsustainable
The average SOC team processes 45,000+ alerts per month. 90% are noise or duplicates. Analysts triage manually, burn out, and miss real threats. SOAR helps but doesn’t solve the problem—because SOAR is a workflow tool, not an investigator.
Attackers Move Faster Than Playbooks
By the time your team writes, tests, and deploys a playbook, threat tactics have evolved. An agentic SOC adapts to new attack patterns in real time, without code changes.
The Math
D3 Morpheus costs $0.27 per alert to investigate. Outsourcing L2 investigation to a human SOC analyst costs $25-$45 per alert. At 45,000 alerts/month, that’s a 180x cost difference
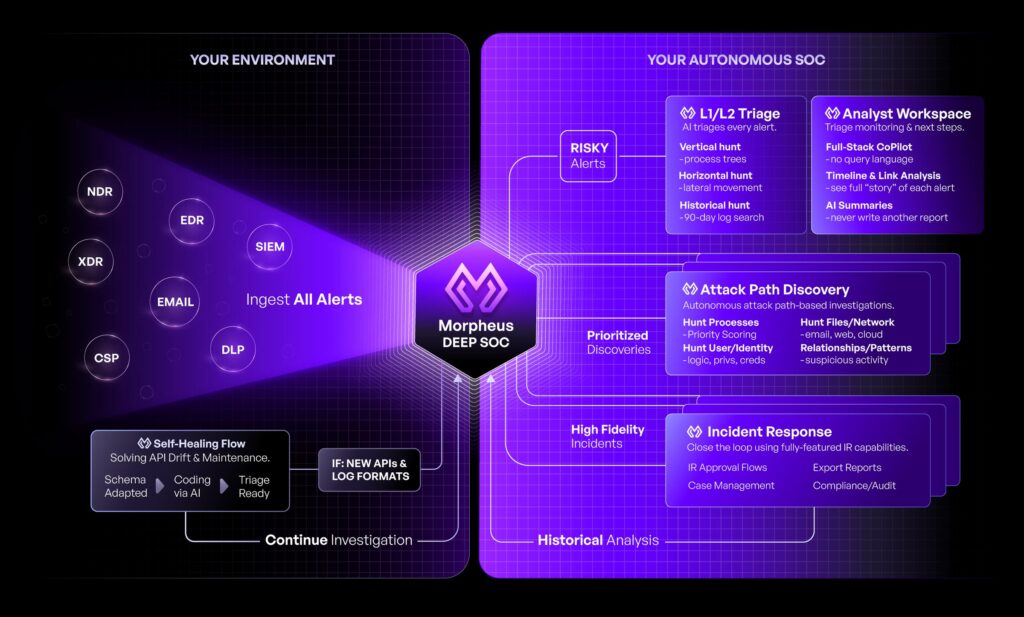
HOW IT WORKS
How D3 Morpheus Works
D3 Morpheus ingests alerts from your entire security stack, investigates them with AI-driven reasoning, and triage them autonomously—then generates contextual response playbooks at runtime.
Ingest Alerts From 800+ Tools
D3 Morpheus connects to your SIEM, EDR, NDR, cloud providers, identity platforms, and custom tools. Self-healing integrations auto-detect API changes and adapt without manual intervention.
Attack Path Discovery Across Tool Boundaries
Most SOC tools see alerts in isolation. D3 Morpheus traces attack paths horizontally (lateral movement across systems) and vertically through time (privilege escalation, persistence). It connects disparate signals—firewall blocks, failed login attempts, file modifications—into coherent threat narratives.
Autonomous L1-L2 Triage
The cybersecurity triage LLM evaluates attack likelihood, assesses business impact, and determines whether analyst intervention is needed. Up to 95% of alerts are triaged in under 2 minutes. 99% of noise is eliminated before reaching your team.
Runtime Playbook Generation
No static playbooks. For each incident, D3 Morpheus generates a bespoke response playbook at runtime, tailored to the specific attack, tools, and environment. No versioning. No maintenance. No staleness.
Automated or Manual Response
Low-risk, high-confidence cases auto-remediate (block IPs, isolate hosts, disable accounts). High-stakes cases escalate to analysts with full context and recommended actions. Analysts spend time on decision-making, not information gathering.
Continuous Learning
Each incident teaches the LLM. Over time, Morpheus gets smarter about your environment, your normal traffic patterns, and your threat profile—without retraining.
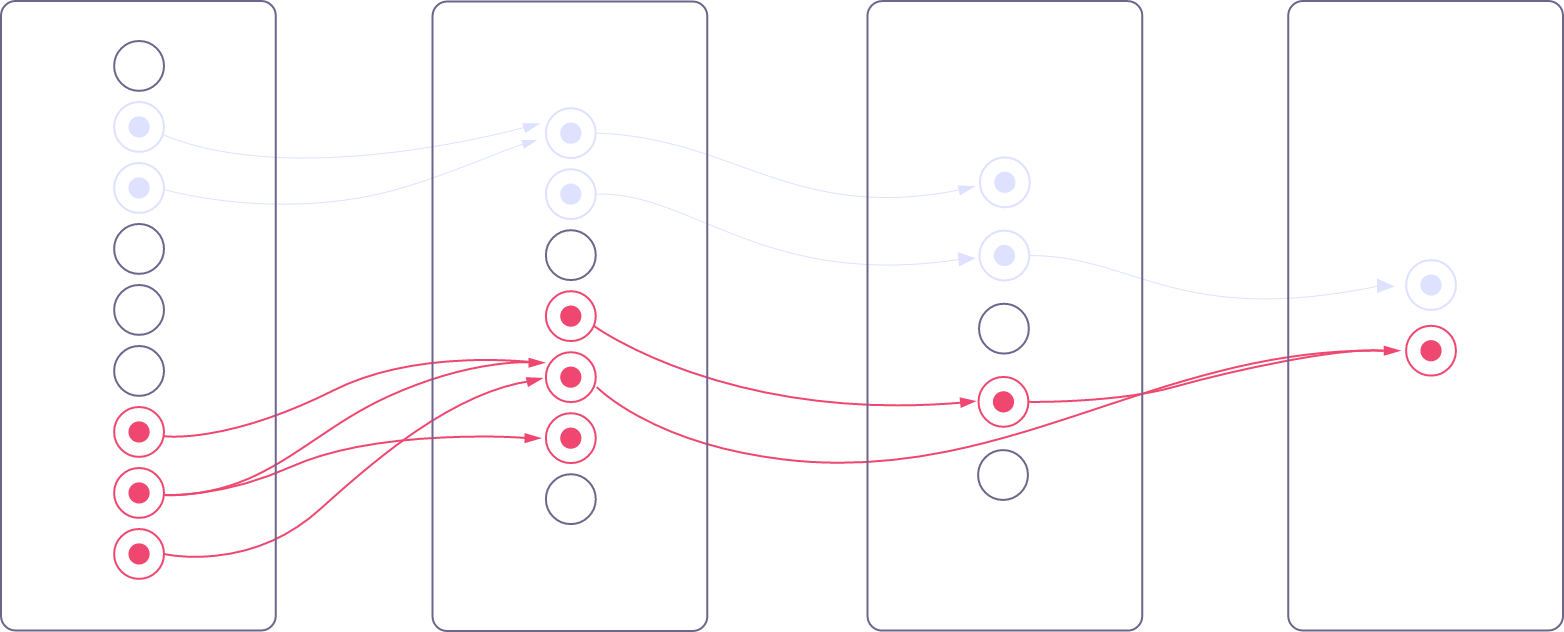
Deterministic Pattern Hardening: Efficiency by Design
Proven attack patterns discovered by the LLM graduate into deterministic code over time. The system tracks a deterministic-to-LLM ratio, meaning the platform gets faster, cheaper, and more predictable with use. Novel threats flow to the LLM for reasoning; known patterns execute deterministically without LLM overhead. This creates a compounding efficiency advantage: the longer Morpheus runs, the less compute it consumes while maintaining 100% alert coverage.
Intelligence Architecture: Purpose-Built, Not Retrofitted
D3 Morpheus’s Unified Intelligence Model is engineered from the ground up for security, not adapted from a general-purpose chatbot API.
8 Million Security Incidents in Training
The LLM learned from 8 million real security incidents and alert schemas from 800+ vendors. It understands the semantic relationships between alerts that humans struggle to connect manually.
Vendor-Agnostic Semantic Understanding
Different vendors name the same concept differently. Morpheus resolves these synonyms automatically—”threat_score” vs. “risk_level” vs. “severity_grade”—enabling native cross-vendor correlation.
Customer-Expandable Intelligence
Each organization’s Morpheus instance adapts to their unique environment, processes, and analyst preferences. The proprietary triage capability belongs to your organization, not the vendor. Your data stays yours; your intelligence model stays yours.
Attack Path Discovery: The Core Differentiator
D3 Morpheus’s proprietary investigation methodology traces threats across your entire security infrastructure—both horizontally through tool silos and vertically through time.
Lateral Movement (Horizontal Traces)
Most SIEM alerts fire in isolation. A user login from an unfamiliar location. A suspicious PowerShell command. A large file transfer. In silos, each is a potential false positive. Together, they tell a story of lateral movement.
D3 Morpheus correlates signals across Sentinel, Defender, Splunk, CrowdStrike, SentinelOne, Palo Alto, Okta, Fortinet, and Elastic simultaneously—without the overhead of custom correlation rules. It identifies when an attacker moves from a compromised endpoint to another system, crosses network boundaries, or pivots to cloud resources.
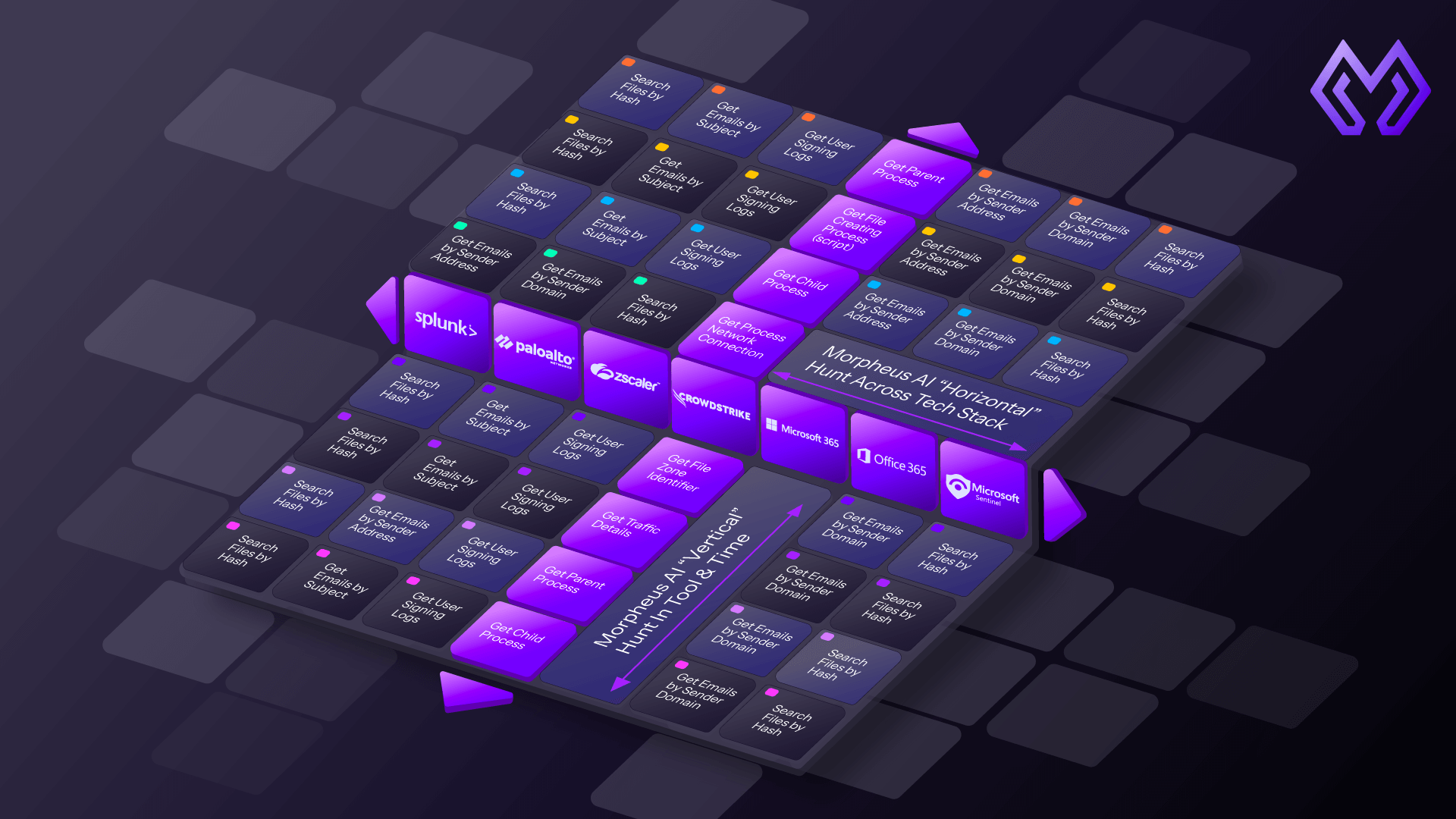
Privilege Escalation & Persistence (Vertical Traces)
An isolated alert on “user added to admin group” might not trigger your SOAR playbooks. But when correlated with failed login attempts from 2 days ago, suspicious process execution yesterday, and file modifications in /etc/sudoers this morning—the attack path becomes clear.
D3 Morpheus traces attack progression through time, identifying when an attacker has moved from reconnaissance to exploitation to persistence.
why this matters
SOCs spend 60% of L2 investigation time manually correlating data across tools. Attack Path Discovery automates this and uncovers threats that would otherwise slip through tool-specific alerting.
Example: Ransomware Campaign
A legacy SOAR might see:
- Endpoint detection: Suspicious process behavior (not critical)
- Network detection: Lateral movement to file server (needs investigation)
- SIEM alert: Large exfiltration event (high risk)
Your team spends 30 minutes connecting the dots. D3 Morpheus does this in 90 seconds, traces the full attack path, and recommends containment actions.
Self-Healing Integrations: Eliminate Integration Maintenance
Integration maintenance is the hidden tax on SOC engineering. SOC teams spend 30% of their time keeping connectors alive as APIs drift, schemas change, and credentials rotate. D3 Morpheus eliminates this burden.
The Integration Maintenance Problem
Your SIEM vendor pushes an API update. Your EDR provider changes the authentication scheme. A connector breaks silently. Your SOAR workflows fail. Your team debugs. You lose visibility. Attackers act.
This happens constantly. SOAR and orchestration teams estimate they spend a full day per week per integration fixing breaks.
How Self-Healing Integrations Work
Morpheus AI integrations monitor themselves. They detect:
- API schema changes (new fields, deprecated endpoints)
- Authentication failures (token expiration, permission changes)
- Rate limit adjustments and timeout patterns
- Credentials that need rotation
When a change is detected, Morpheus automatically generates corrective code—updating field mappings, refreshing auth tokens, adjusting retry logic—and deploys the fix without human intervention.
The Impact
One 8-person SOC team recovers ~2.5 engineer-days per week previously lost to integration maintenance. That is 130 engineer-days per year, or 2.5 FTEs, freed to focus on threat hunting and response strategy.
800+ Pre-Built Integrations
Morpheus AI ships with connectors to all major security and IT platforms:
- SIEM & Detection: Microsoft Sentinel, Splunk, Elastic, Datadog
- Endpoint Security: Defender, CrowdStrike, SentinelOne, Carbon Black
- Network & Cloud: Palo Alto Networks, Fortinet, Azure, AWS, GCP
- Identity & Access: Okta, Azure AD, Duo
- Custom Tools: REST/SOAP API framework for any tool with an interface
D3 Morpheus vs. Legacy SOAR
SOAR platforms automate workflows. Agentic AI SOC platforms automate reasoning. Here’s how they compare.
| Capability | D3 Morpheus (Agentic AI SOC) | Legacy SOAR (Cortex XSOAR, Splunk SOAR, Tines, Torq, Google Cloud SecOps) |
|---|---|---|
| Alert Ingestion | ✓ | ✓ |
| Cross-Tool Alert Correlation | ✓ Attack Path Discovery | — |
| Alert Coverage | ✓ 100% (outcome automation) | 30-40% (via playbooks) |
| Autonomous Alert Triage | ✓ Up to 95% in <2 min | — |
| Playbook Authoring | ✓ Auto-generated at runtime | Manual, requires coding |
| Integration Maintenance | ✓ Self-healing | Manual (30% of SOC eng time) |
| Novel Threat Adaptation | ✓ AI reasoning | Requires new playbooks |
| Investigates L1-L2 Work | ✓ Autonomous | Partial (automation only) |
| Noise Reduction | ✓ 99% | 50-70% |
| Cost Per Alert | ✓ $0.27 | $2-8 (with analyst time) |
| Speed (Median Investigation) | ✓ <3 minutes | 20-60 minutes (manual triage: 56 min average) |
| Analyst Time Freed | ✓ 60-70% triage → 5-10% review only | Limited |
Flat-Rate Pricing: No Per-Alert Bills
Morpheus AI charges a flat-rate subscription plus user licenses. No per-alert fees. No token overage charges. D3 absorbs all LLM token costs.
Pricing Model
Unlike SOAR tools that charge per alert or per integration, or AI services that bill by token consumption, Morpheus AI offers predictable, all-inclusive pricing. D3 absorbs all LLM token costs, a major procurement advantage for security leaders evaluating competing solutions:
- Flat-rate annual subscription based on alert volume, no per-alert overages
- User licenses for analysts and investigators
- All integrations included, 800+ connectors, no per-connector fees
- All LLM token costs absorbed by D3, unprecedented cost predictability compared to token-metered competitors
- Unlimited alerts, process 10,000 or 1 million alerts per month at the same flat rate
cost comparison
At 145,000 alerts/month, legacy SOAR platforms charge $15K-$50K/month in base fees plus per-alert overages. D3 Morpheus flat rate covers the full volume. Plus, every alert automated saves 30-60 minutes of analyst time (~$150-$300/alert at fully-loaded analyst cost).
Use Cases
D3 Morpheus reduces alert fatigue and improves MTTR (Mean Time To Response) across your entire security program.
Phishing & Account Compromise
Traces email phishing attempts through login anomalies, suspicious file access, and lateral movement. Autonomous triage isolates compromised accounts and blocks attacker IP addresses in under 2 minutes.
Ransomware & Encryption Events
Correlates suspicious process execution, large file transfers, and backup access into ransomware attack narratives. Identifies patient Zero and containment targets before encryption spreads.
Cloud Workload Compromise
Monitors Azure, AWS, and GCP for privilege escalation, credential theft, and persistence mechanisms. Detects lateral movement across cloud services and on-premises resources.
Insider Threat Detection
Correlates unusual access patterns, data exfiltration, and privilege escalation to identify malicious insiders. Captures full attack path for forensic investigation.
Compliance Monitoring
Tracks security events required for PCI-DSS, HIPAA, SOC 2, and regulatory compliance. Auto-generates incident reports with full audit trails and attack path documentation.
MSSP/Managed Security Services
MSSPs run D3 Morpheus across customer environments. One AI SOC platform handles triage for 50+ customers simultaneously. Analysts focus on high-value investigations and breach response.
Deployment & Integration
Morpheus AI deploys in 2 weeks. Cloud-native, fully managed, with 800+ pre-built integrations and no on-premises infrastructure.
Deployment Timeline
- Week 1: Onboarding, integration setup, alert ingestion begins
- Week 2: Triage tuning, playbook customization, go-live with 80% MTTR reduction
Integration Partners
Morpheus AI integrates with your entire security stack:
- SIEM & Detection: Microsoft Sentinel, Splunk, Elastic, Datadog, Cloudflare
- Endpoint Security: Microsoft Defender, CrowdStrike, SentinelOne, VMware Carbon Black
- Network & Cloud: Palo Alto Networks, Fortinet, Cisco, Azure, AWS, GCP
- Identity & Access: Okta, Azure AD, Duo, CyberArk
- Custom Tools: REST/SOAP API framework for any system with an interface
Azure Marketplace Availability
Morpheus AI is available on Azure Marketplace for native deployment in Azure environments. Integrate directly with Azure costs and leverage Azure spending commitments.
Cloud-Native Architecture
- Multi-tenant, fully managed SaaS platform, zero infrastructure overhead
- 99.99% SLA with automated failover and geographic redundancy
- Real-time processing, alerts triage within seconds of ingestion
- End-to-end encryption for all data in transit and at rest
For detailed integration documentation and deployment guides, visit the D3 Integrations Hub.
Governance & Trust
Who Watches the AI?
Enterprise security requires transparency. D3 Morpheus operates on the principle that every AI decision must be explainable, testable, and auditable.
Visible Framework
Every decision node, connection, and reasoning step is exposed and browsable. Through the Reasoning Explorer tool, your team can examine any Morpheus investigation in detail—see what data was considered, which patterns matched, and why a specific triage outcome was reached. No black boxes.
Attack Simulation Testing Morpheus runs simulated multi-stage attacks with known ground truth. The platform continuously tests itself against realistic attack scenarios to verify that its reasoning paths are sound and that it catches the threats it should.
Trust Model: Deterministic vs. Indeterministic Zones
The platform identifies which parts of its reasoning are deterministic (proven patterns executing as code) and which are indeterministic (LLM reasoning). Your team can set confidence thresholds and escalation rules around indeterministic zones, ensuring high-stakes decisions never slip through without human oversight.
87%
Attack path revelation rate
94%
Investigation closure rate
The Reasoning Explorer
Click any decision in your incident timeline and browse the full reasoning chain. See the alerts that triggered investigation, the patterns that matched, the confidence scoring, and the recommendation, all auditable, all explainable. This is your governance dashboard for AI-driven security.
faqs
Frequently Asked Questions
Everything buyers ask before an Autonomous AI SOC demo. If you don’t see your question here, we’ll answer it live.
What is an agentic SOC?
An agentic SOC is a Security Operations Center powered by autonomous AI that reasons through security problems, investigates alerts across tool silos, and triages cases without human intervention for routine work. Unlike traditional SOAR (which executes static playbooks), an agentic SOC adapts to novel threats and learns from each incident.
How is D3 Morpheus different from SOAR?
SOAR is a workflow engine that executes predefined playbooks. D3 Morpheus is an AI investigator. It autonomously correlates alerts across tools, traces attack paths, reasons about threat likelihood, and generates custom response playbooks at runtime. Where SOAR requires playbook authoring and updates, Morpheus adapts to new threats in real time.
Does D3 Morpheus replace my SIEM?
No. D3 Morpheus ingests alerts from your SIEM (Splunk, Sentinel, Elastic, etc.) and augments it with AI-driven triage and investigation. Your SIEM remains your source of truth for log data. Morpheus is the analyst layer on top.
How does Attack Path Discovery work?
Attack Path Discovery traces threats horizontally (across tools and systems) and vertically (through time). It correlates alerts from Defender, CrowdStrike, Sentinel, Palo Alto, and others into cohesive attack narratives. A single suspicious alert might be noise; Attack Path Discovery identifies when multiple signals indicate a real threat.
What happens if an integration breaks?
Self-healing integrations auto-detect and fix most common issues—API schema changes, authentication failures, rate limit adjustments, credential rotation. If an issue requires manual intervention, the platform alerts your team with recommended fixes. This eliminates the 30% of SOC engineering time traditionally spent on connector maintenance.
How fast does D3 Morpheus triage alerts?
Up to 95% of alerts are triaged (investigated and severity-ranked) in under 2 minutes. The platform processes real-time streaming alerts, so triage happens within seconds of alert ingestion. This speed frees your team to focus on high-stakes investigation and response.
Can I customize playbooks?
D3 Morpheus generates playbooks at runtime, so there’s no static playbook library to customize. Instead, you configure triage sensitivity, response automation rules, and escalation policies. The AI generates the playbook execution plan for each incident based on these policies and the attack context.
Does this work for MSSPs?
Yes. MSSPs run D3 Morpheus across dozens or hundreds of customer environments in a single platform. One analyst team handles triage for all customers. Each customer’s data is isolated and secure. This model scales MSSP SOC services without proportional headcount growth.
How much does it cost?
D3 Morpheus uses flat-rate subscription pricing based on alert volume, plus user licenses. There are no per-alert fees, no per-integration charges, and no LLM token overages. For a custom quote, visit the pricing page or request a demo.
What about data privacy and compliance?
D3 Morpheus is cloud-native with end-to-end encryption, role-based access control, and audit logging. Data processing occurs in isolated tenant environments, and we never share your data with third parties.
What is the difference between an AI SOC and an agentic SOC?
An AI SOC uses artificial intelligence for alert triage and investigation. An agentic SOC takes this further — the AI reasons autonomously through multi-step problems, adapts to novel threats, and takes action within human-defined guardrails. D3 Morpheus is both. For a detailed architectural comparison, see our Agentic SOC Platform guide.
Is D3 Morpheus’s LLM a general-purpose model with a security wrapper?
No. D3 Morpheus uses a Unified Intelligence Model—a purpose-built cybersecurity LLM trained over 24 months on 8 million real security incidents and alert schemas from 800+ security products. It’s not ChatGPT or a generic LLM retrofit for security. It understands vendor-specific semantics and alert correlations that general models cannot.
Does my organization own its Morpheus intelligence model?
Yes. Each customer’s Morpheus instance adapts to their unique environment, processes, threat profile, and analyst preferences. The triage intelligence that Morpheus learns is proprietary to your organization—it remains your data, your capability, and your competitive advantage. You’re not sharing your security intelligence with other customers.
How is this different from SOAR in terms of automation?
SOAR automates tasks within rigid playbooks (enrichment, notification, API calls). It handles 30-40% of alerts through conditional logic. D3 Morpheus automates outcomes through LLM reasoning. It investigates and triages 100% of your alerts by reasoning through complex, multi-signal security problems—no playbooks required, no case falls through cracks.
What is the Reasoning Explorer?
The Reasoning Explorer is D3 Morpheus’s transparency and governance tool. Click any investigation decision and browse the full reasoning chain—what alerts triggered investigation, which patterns matched, confidence scores, what data was considered, and the final triage recommendation. Every decision is auditable and explainable. This is critical for enterprise security teams that need to understand and defend AI-driven decisions.