Investigation engine
Attack Path Discovery: Autonomous L2 investigation on every alert.
Attack Path Discovery (APD) is D3 Morpheus’s autonomous investigation engine. It performs L2-depth investigation on every security alert — correlating signals across identities, endpoints, cloud, and email infrastructure, validating IOCs, and reconstructing attack timelines before your analyst opens the case.
APD hunts horizontally across your stack and vertically through 90 days of telemetry — querying 800+ self-healing integrations in parallel. Up to 95% of alerts reach L2+ depth in under 2 minutes.
Up to 95%
Alerts reaching L2+ depth — triaged and investigated in under 2 minutes
90 days
Telemetry traced per alert — vertical walk-back through the originating tool
800+
Integrations queried in parallel — self-healing across SIEM, EDR, identity, cloud, and email
How APD Investigates
Two hunting dimensions: horizontal and vertical.
Every Attack Path Discovery investigation hunts in two directions at the same time. Horizontally across your security stack — SIEM, EDR, identity provider, cloud security, and email security tools investigated simultaneously. Vertically through up to 90 days of telemetry — walking back through time to find the precursor events the alert is the consequence of.
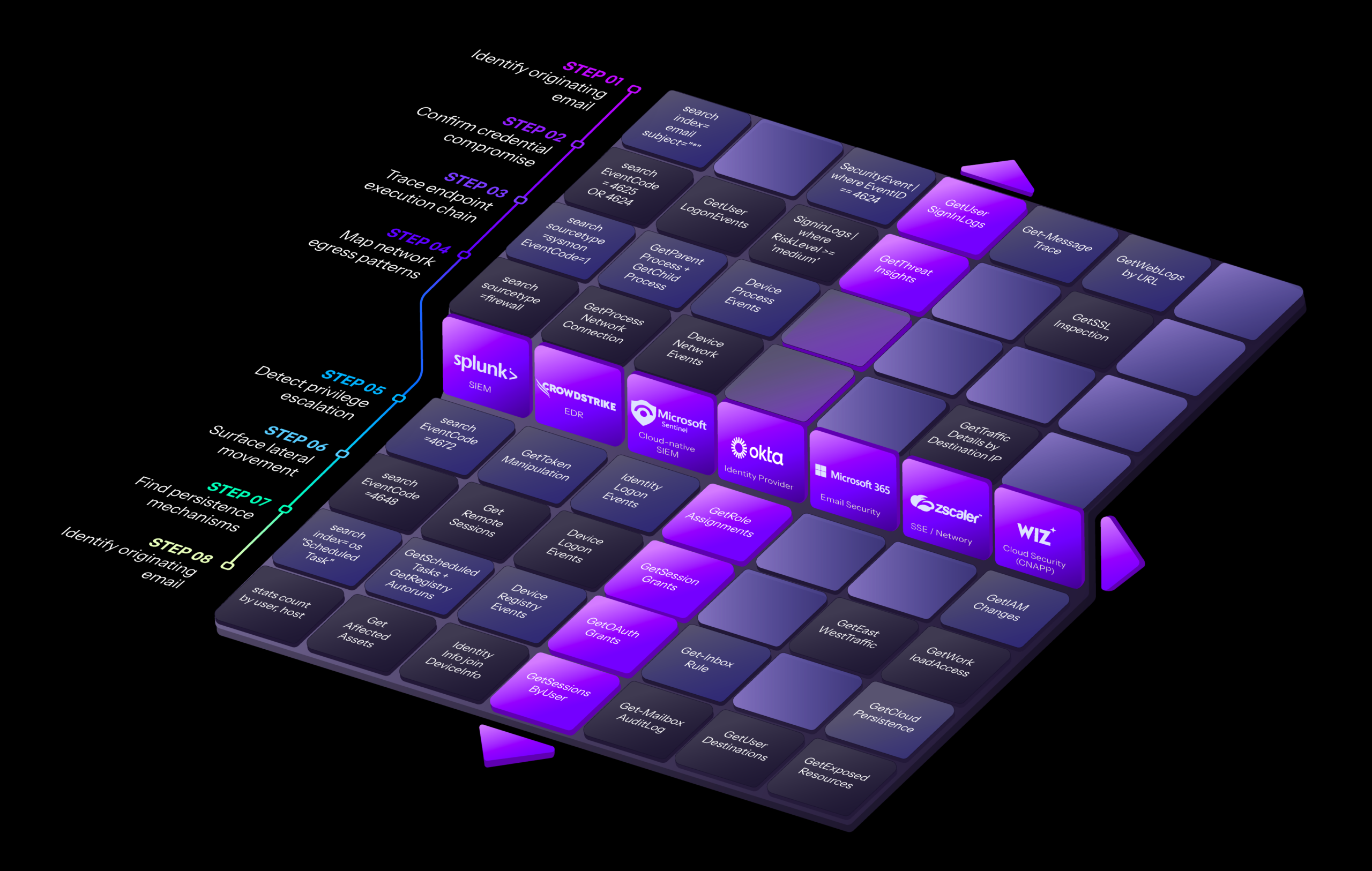 FIG · Morpheus APD investigating horizontally across the tech stack and vertically through tool and time — in parallel
FIG · Morpheus APD investigating horizontally across the tech stack and vertically through tool and time — in parallel
| Property | Horizontal hunting | Vertical hunting |
|---|---|---|
| Direction | Across multiple security tools at the same point in time | Into a single tool through up to 90 days of telemetry |
| Question it answers | What was happening across the rest of the environment at the moment the alert fired? | What earlier events on this host or identity led to the alert being possible? |
| Named data sources | SIEM (Splunk, Sentinel, Chronicle) · EDR (CrowdStrike, SentinelOne, Defender) · Identity (Okta, Entra ID) · Cloud (Wiz, AWS, Azure) · Email (Microsoft 365, Proofpoint) | The originating tool — whichever security platform fired the alert — queried recursively across its retained telemetry window |
| Sample queries issued | Get Emails by Sender Address · Get User Signing Logs · Search Files by Hash · Get Process Network Connection | Get Parent Process · Get Child Process · Get File Creating Process · Get File Zone Identifier |
| What it surfaces | Blast radius — every system, identity, and resource the same campaign touched, in one consolidated case file | Root cause — the precursor event the alert is the downstream consequence of (often hours or days earlier and never alerted on its own) |
| Runs in parallel? | Yes — all integrations queried simultaneously, not sequentially. 800+ self-healing integrations available in the query pool. | Yes — telemetry walked recursively while horizontal queries fire in parallel. Both dimensions complete inside the same investigation window. |
| Completion time | Up to 95% of alerts reach L2+ investigation depth in under 2 minutes — both dimensions complete inside one case file | |
For a single suspicious sign-in alert
APD returns parallel evidence from four named tools — in one consolidated case file, before the analyst opens the case.
- Okta — sign-in source IP and risk score
- CrowdStrike — process activity on the originating endpoint
- Microsoft 365 — mailbox forwarding-rule changes attributed to the session
- Wiz — cloud workload patterns inside the session’s access window
- → Same alert, four tools, one timeline
For a CrowdStrike detection on a payment host
APD pulls 90 days of telemetry from the originating tool and surfaces the precursor event that fired hours earlier and never triggered an alert on its own.
- T-36h · dropper process executed on host
- T-32h · outbound connection to staging IP
- T-08h · file zone identifier modified
- T-0 · CrowdStrike detection fires
- → Root cause identified, 36 hours upstream
After hunting
Timeline reconstruction: order, causality, blast radius.
Timeline reconstruction is the step where APD orders every event from horizontal and vertical hunting into a single chronological case file — ranked by causal relevance, with blast radius computed at every stage.
When one investigation isn’t enough
Chainability: one finding becomes the next investigation.
Chainability is what happens when APD finds evidence in one investigation that warrants its own. Morpheus opens a follow-on investigation automatically — with its own audit trail, linked to the parent case.
Phishing alert investigation
APD investigates a flagged phishing email — traces the recipient, examines the delivery infrastructure, queries identity logs for related activity, and reconstructs the timeline.
OAuth token grant to an unknown application appears in the recipient’s identity log — granted 14 minutes after the phishing email was opened.OAuth grant investigation
APD opens a second case automatically — queries the OAuth registry, identity provider, and cloud audit logs for the unknown application. The investigation runs in parallel with the parent case.
audit trail entry. The chain is preserved.The moat
Powered by the Cybersecurity Triage Reasoning Graph.
The Cybersecurity Triage Reasoning Graph is D3’s domain-specific reasoning architecture for SOC investigation. Nodes encode security entities and concepts; edges encode the relationships and reasoning patterns. The graph constrains what the LLM considers at every step of an APD investigation.
A general-purpose LLM, asked to investigate a suspicious sign-in, will reason about anything it has seen in its training data — including patterns irrelevant to the alert type, the customer’s environment, or the security domain itself.
The reasoning graph routes the LLM along defined edges — from identity nodes to endpoint nodes to cloud nodes — based on the alert type and the evidence surfaced at each step. The LLM never reasons about telemetry the graph hasn’t determined is relevant.
Convinced by the architecture?
See APD investigate a live alert.
30-minute walkthrough · Bring an alert from your stack · No slides
When the stack breaks
Self-healing integrations keep investigations running.
APD reaches across 800+ integrations to assemble evidence. When a vendor pushes an API change that breaks a connector, self-healing detects the break, generates corrective code, and restores the integration without analyst intervention.
The integration-drift tax that erodes every SOAR ROI — eliminated structurally, not patched operationally.
schema-diff applied. The analyst never knew.In your console
What an APD investigation looks like in your console.
Every APD investigation returns a structured case file — six elements an analyst reviews on every alert. The structure is identical whether APD is triaging a phishing alert, a CrowdStrike detection, or a vulnerability finding. Only the contents change.
Ranked attack timeline
Every event APD discovered during horizontal and vertical hunting — ordered chronologically, ranked by causal relevance. Attacker actions, system reactions, and downstream alerts in one stream with timestamps, source tool, and confidence scoring.
- 14:02 — OAuth token theft on user X
- 14:07 — mailbox forwarding rule created
- 14:09 — privileged role assignment
- 14:14 — Wiz alert: workload deployment
Data-source panel
Every tool APD queried during the investigation — with response time, result-set size, and connector version. Evidence provenance at a glance, across any of 800+ integrations.
- Okta · 142ms · 8 events v4.2
- CrowdStrike · 89ms · 31 events v6.1
- Microsoft 365 · 220ms · 4 events v3.0
- Wiz · 156ms · 12 events v2.8
Attack path graph
A visual map of entities and the relationships APD discovered between them — user accounts, hosts, processes, mailboxes, cloud resources, and the lateral or privilege-escalation paths connecting them. Click any node to inspect underlying evidence.
- user/jdoe → logged-in → host/finlap-01
- host/finlap-01 → spawned → powershell.exe
- powershell.exe → connected → 185.x.x.x
- user/jdoe → granted → role/admin
MITRE ATT&CK mapping
Every action APD attributed to the attacker, tagged with the relevant ATT&CK technique ID and tactic. Analysts and auditors trace the campaign against the framework without rebuilding the mapping themselves.
- T1078.004 · Cloud Accounts Initial Access
- T1114.003 · Email Forwarding Rule Collection
- T1098.003 · Role Assignment Persistence
- T1530 · Cloud Storage Object Exfiltration
Next action + command-risk tier
APD recommends the next response step and tags it with a command-risk tier — read-only enrichment, contained remediation, or state-changing action. The tier controls which autonomy level can execute without analyst approval.
- Revoke OAuth grant Tier 2
- Contained remediation · approval required at Level 2
- Suspend session Tier 3
- State-changing · approval required at all levels ≤ 3
Audit trail
One document per incident. Every reasoning step the graph took, every query APD issued, every action recommended or executed, every analyst decision. Mapped structurally to NIS2, DORA, and EU AI Act oversight obligations.
- 14:02:11 · graph: phishing branch entered
- 14:02:12 · query: Get-MessageTrace
- 14:02:14 · evidence: 1 match · scored 0.91
- 14:02:18 · analyst-approved: revoke token
Same six elements. Every alert. Whether phishing, endpoint detection, or vulnerability finding.

Morpheus for Microsoft · Benchmark report · 12 pages · 8 min read
The autonomous SOC for Microsoft Security environments.
Morpheus runs natively on Azure and ingests from Microsoft Sentinel, Defender XDR, Defender for Endpoint, Defender for Office 365, and Entra ID — plus 800+ additional integrations. The autonomous investigation layer that completes your Microsoft Security stack.
In a head-to-head benchmark against Microsoft Security Copilot across three phishing scenarios, Attack Path Discovery identified root cause in 3 of 3 — tracing each campaign across Microsoft 365, Defender, and Entra ID end-to-end. Read the full evaluation — methodology, scenarios, and capability comparison.
Extensions · Beyond alert investigation
The same engine, extended to vulnerability triage.
APD is built around alert investigation, but the engine is general enough to apply elsewhere. Morpheus uses the same horizontal-hunting, vertical-hunting, and timeline-reconstruction pattern to triage AI-discovered vulnerability findings.
Same engine · Different input
Chainability analysis, asset-impact mapping, prioritization.
Each vulnerability finding receives the same case-file output, the same six console elements, and the same audit trail as an alert investigation. Only the input source changes.
Built for the volume of AI-discovered vulnerabilities arriving from Anthropic Mythos, OpenAI Codex Security, and the multi-LLM vulnerability discovery landscape that follows.
faqs
APD — frequently asked.
Eight questions the SOC director, the architect, and the procurement team ask before they sign.
What is Attack Path Discovery?
Attack Path Discovery (APD) is D3 Morpheus’s autonomous investigation engine. It performs L2-depth investigation on every security alert by hunting horizontally across identities, endpoints, cloud, and email infrastructure — and vertically through up to 90 days of telemetry from the originating tool. APD correlates evidence, validates IOCs, reconstructs attack timelines, computes blast radius, and drafts context-aware remediation before an analyst opens the case.
Up to 95% of alerts reach L2+ investigation depth in under 2 minutes. The investigation is governed by the Cybersecurity Triage Reasoning Graph, which constrains the LLM’s reasoning at every step.
How is APD different from an L1 triage bot like Dropzone or Prophet Security?
L1 triage bots classify and summarize alerts. They route alerts into queues, recommend escalations, and produce executive summaries. They do not perform investigation. The L2 work — pivoting across tools, reconstructing causal timelines, validating IOCs, computing blast radius — still falls to a human analyst.
APD performs the L2 work itself. The output is a complete case file with a reconstructed attack timeline, a data-source panel showing every tool queried, a MITRE ATT&CK mapping, a command-risk-tiered next action, and a unified audit trail — on every alert, not just the criticals.
How is APD different from a SOAR playbook?
SOAR playbooks execute predetermined steps in a fixed order — written by a human, run by the platform. When an investigation requires a step the author didn’t anticipate, the playbook fails or hands off to an analyst. APD doesn’t run playbooks; it generates the investigation by routing the LLM through the Cybersecurity Triage Reasoning Graph based on the alert type and the evidence surfaced at each step.
The graph constrains what the LLM considers — but the LLM decides how to investigate. This is the architectural difference between automation and autonomous reasoning. Morpheus includes a SOAR engine for cases where deterministic execution is the right choice, but APD is the investigation primitive.
Does APD work for vulnerability findings, or just alerts?
Both. APD was designed around alert investigation, but the engine generalizes. Morpheus uses the same horizontal-hunting, vertical-hunting, and timeline-reconstruction pattern to triage vulnerability findings — including AI-discovered vulnerabilities from systems like Anthropic Mythos and OpenAI Codex Security.
Each vulnerability finding receives the same six-element case file as an alert investigation: ranked timeline (mapped to the vulnerability chain), data-source panel, attack path graph (showing chainability across findings), MITRE ATT&CK mapping, recommended next action, and audit trail. Only the input source changes. See the vulnerability triage use case for the full extension positioning.
What’s the difference between horizontal and vertical hunting?
Horizontal hunting is investigation across multiple security tools at the same point in time. APD correlates evidence from SIEM (Splunk, Sentinel), EDR (CrowdStrike), identity (Okta), cloud (Wiz), email (Microsoft 365), and network (Zscaler) tools simultaneously — assembling the full cross-domain picture of what was happening when the alert fired.
Vertical hunting is investigation into a single tool through time. APD walks back through up to 90 days of telemetry from the originating tool to surface the precursor events — the dropper that fired 36 hours earlier, the dormant scheduled task, the mailbox rule created last week — that the alert is the downstream consequence of.
Every APD investigation runs both dimensions in parallel.
What is the Cybersecurity Triage Reasoning Graph?
The Cybersecurity Triage Reasoning Graph is D3’s domain-specific reasoning architecture for SOC investigation. Nodes encode security entities and concepts (alert types, attacker behaviors, tool capabilities, evidence categories); edges encode the relationships and reasoning patterns that connect them. The graph constrains what the LLM considers at every step of an APD investigation.
When APD investigates a suspicious sign-in, the graph routes the LLM to identity nodes first, then to endpoint nodes for processes associated with the user session, then to cloud nodes for resources the session accessed. The LLM never reasons about telemetry the graph hasn’t determined is relevant to the alert type.
Built over 24 months by 60 specialists in red teaming, data science, AI engineering, and SOC operations. The graph is the moat; the LLM is interchangeable — our defensible IP is the cybersecurity domain modeling, not the LLM. When a better model ships, we swap it in.
How does APD handle vendor API changes that break integrations?
APD reaches across 800+ self-healing integrations. When a vendor pushes an API change that breaks a connector, Morpheus’s self-healing layer detects the break, generates a patched connector that maps the new schema to the same internal fields, runs the patched query, and returns evidence as if nothing changed.
Production MTTR on API drift: 18 minutes, measured across the Morpheus production fleet. Industry baseline for manual repair on traditional SOAR platforms: 4–6 weeks (connector triage, code patch, regression test, redeploy). The integration-drift tax that erodes every SOAR ROI is eliminated structurally, not patched operationally.
The audit trail records what changed and what was generated. The analyst never had to know.
What does an APD investigation produce that a human analyst doesn’t?
An APD investigation produces the same artifact a senior L2 analyst would produce — a complete case file with timeline, evidence panel, attack-path graph, MITRE ATT&CK mapping, recommended response, and audit trail. The difference is consistency.
APD investigates every alert at L2+ depth, including the long tail of low-severity alerts a human analyst doesn’t have time for. It investigates at 3 AM Saturday with the same depth as Tuesday afternoon. It produces an investigation before the analyst opens the case — so analyst time is spent reviewing the work, not building it from scratch.
The audit trail is also a strict improvement over a human investigation: every reasoning step the graph took, every query APD issued, every action recommended or executed, every analyst decision — in one document per incident, structured for SEC, NIS2, DORA, and EU AI Act oversight obligations.
See it run
Every alert. Fully investigated. In under 2 minutes.
Watch APD trace a live alert across identities, endpoints, cloud, and email — and return the full case file before your analyst opens the case.
30-minute walkthrough · Live on real alerts · No slides