A playbook is a structured strategy procedure for handling any situation. The first known usage of the word goes back to 1511 AD, predating Shakespeare. Playbooks are commonly associated with sports, particularly football, though the term is used frequently in other realms. In the context of cybersecurity, playbooks refer to incident response SOPs (standard operating procedure). Just like a football playbook, an IR (incident response) playbook for any organization is tailored to fit its unique needs. AWS provides a handy playbook definition:
“Enable consistent and prompt responses to failure scenarios by documenting the investigation process in playbooks. Playbooks are the predefined steps to perform to identify an issue. The results from any process step are used to determine the next steps to take until the issue is identified or escalated.”
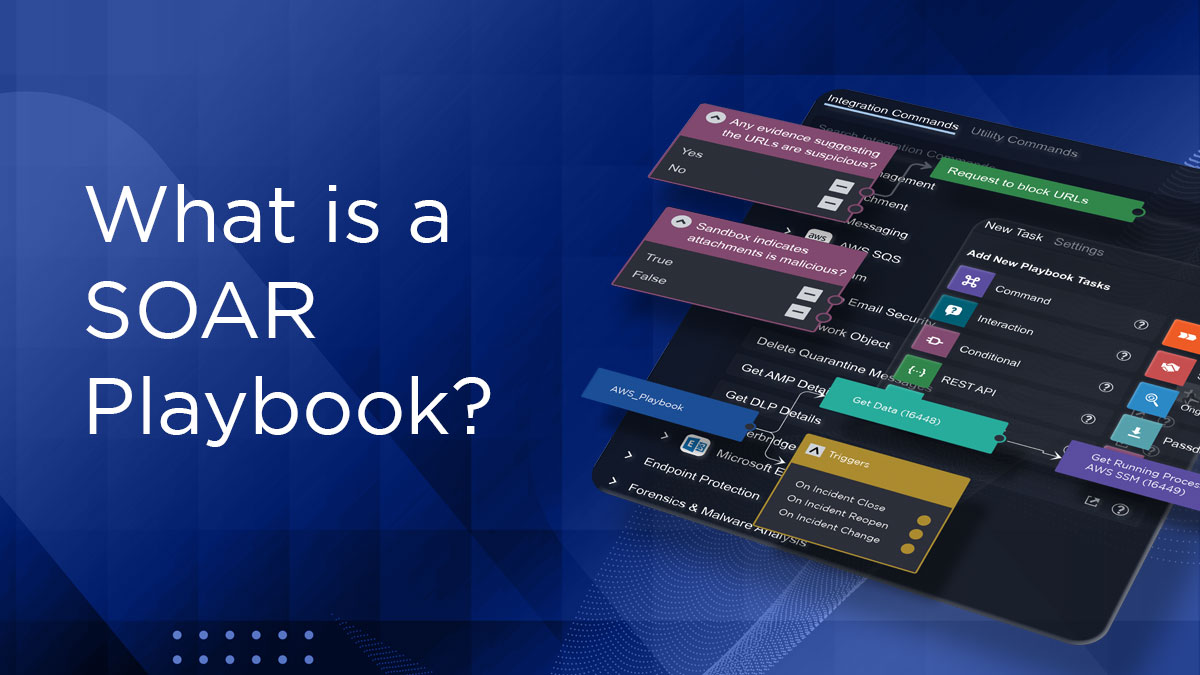
IR playbooks are documents created by SOC teams to prepare an end-to-end process to handle routine incidents and bring predictability, repeatability, and measurability to the response handling process. You can’t really use the automation features of a SOAR (Security Orchestration Automation and Response) platform without having well-documented SOPs on actions to take. In this post, we’ll try to answer some of the most frequently asked questions we’ve come across when demoing our Smart SOAR platform.
What is a Cyber Security Playbook?
A cyber security playbook is a step-by-step guide for handling cyber incidents and threats. It’s purpose is to provide organizations a structured approach to cyber events, and ensure swift and confident actions to minimize potential damage.
Key Features:
- Roles & Responsibilities: Clearly defined for each team member.
- Procedures: Specific actions for different cybersecurity scenarios.
- Dynamic: Incorporates lessons from past incidents and industry best practices.
Playbooks vs Runbooks – Are they the same? What’s the difference?
Both are a means to document, preserve, and share technical know-how in an organization. While the two terms are used interchangeably by some, they do not mean the same thing. If you go by AWS definitions, runbooks are predefined procedures to achieve a specific outcome, while playbooks are predefined steps to perform to identify an issue. Playbooks are what you would use when doing troubleshooting, investigations, and root-cause analysis, while runbooks are what you would use post-incident to recover and resume normal operations.
What is the difference between a playbook and a workflow?
In the context of incident response, a workflow is a subset of tasks in a playbook. A playbook is a collection of workflows.
What are the benefits of using SOAR playbooks?
SOAR playbooks improve the quality of investigations by bringing the rigor and repeatability of checklists to incident response. They enhance the speed of incident response by orchestrating and automating response actions from a single pane of glass. By eliminating copy-pasting, alt-tabbing, and swivel-chairing, SOAR playbooks significantly reduce repetitive and manual tasks from the SOC analyst’s workload, reducing their stress levels and making them more productive.
Do D3’s SOAR playbooks support NIST cybersecurity standards? How about SANS?
Yes. D3’s SOAR playbooks are based on the recommendations made by NIST Computer Security Incident Handling Guide 800-61 Revision 2, an incident response framework that breaks down the incident response lifecycle into four phases:
- a) preparation,
- b) detection and analysis
- c) containment, eradication and recovery
- d) post-incident activity.
This framework is similar to the SANS Incident Framework, which divides IR into six phases.
- a) Preparation
- b) Identification
- c) Containment
- d) Eradication
- e) Recovery
- f) Lessons Learned
It’s not possible for SOAR to programmatically manage every part of an incident response playbook – especially in the preparation phase. A SOAR playbook tries to orchestrate and automate whatever is feasible from the IR playbook with the goal of saving as much time and hassle as possible for the analyst.
What are some standout features and benefits of D3’s SOAR playbooks?
D3’s Smart SOAR Playbooks are codeless. SOC analysts who don’t have a background in programming can build and maintain them. They can drag and drop from our unlimited integrations and use our library of built-in playbooks to automate and orchestrate incident response for key use cases.
Our playbook editor also comes loaded with a library of hundreds of utility actions. These range from tasks like data processing and manipulation, to enrichment, TTP (tactics techniques and procedures) and IOC (indicators of compromise) searches, custom correlations, and remedial actions. You can also create custom utility commands which can be used in our codeless playbooks. You can also test playbooks, tasks, and data inputs in a sandbox environment from within the playbook editor. Our playbooks also give you the flexibility to run custom Python code in SOAR playbooks as custom utility actions and integrations. Our playbooks are geared for swift remediation – features like nested playbooks help run IR tasks independently, and in parallel, speed up incident response times significantly.
Read: The Top 3 SOAR Playbooks You’ll Need in 2023
What are the top use cases for SOAR playbooks?
SOAR playbooks can be used to automate key functions of the SOC (security operations center), based on processes documented in IR playbooks. The SOC automation possibilities are endless. Here are some of the top use cases:
Triage: Smart SOAR ships with Event Pipeline, a global event playbook designed to normalize, de-duplicate, and dismiss or escalate security alerts. Event Pipeline helps tame alert overwhelm in the SOC, reducing false positives by as much as 90%.
Phishing: Spearphishing and whaling are some of the most common attack vectors used by APT groups to gain access to an organization’s network. Phishing playbooks can automate and orchestrate response actions like detonating suspicious email attachments in a sandbox, checking IPs and URLs on threat intelligence sources, quarantining hosts, blocking IPs and URLs, and more. For more information, read our four-part series on how to build a phishing playbook.
Ransomware: Automate IR actions to locate malicious files, quarantine hosts, block file hashes and find signs of further compromise.
Cryptojacking: Adversaries weaponize access to public cloud instances by mining cryptocurrency at your expense. SOAR playbooks can check for suspicious in activity logs, instance metadata, and IP addresses. Furthermore, it can remove attackers’ access to your environment, restore legitimate processes, and remediate compromised endpoints.
Endpoint Incident Response: Retrieve processes from an integrated SIEM/EDR tool, the user audit log, host information, and user details from Active Directory. The playbook then queries the SIEM/EDR for related events, extracts artifacts from collected data, determines if critical assets are involved, assembles the investigation data for review by an analyst, and determines the incident severity.
Vulnerability Management: Parse vulnerability reports and trigger scripts to automatically patch endpoints or send emails to results to the appropriate stakeholders.
Breach Simulation: Leverage security optimization platforms like AttackIQ to run assessments, centralize results and reporting, and notify teams that may need to fix configuration issues.
Read: Smart SOAR Gives You the Best Cybersecurity Playbooks
How many SOAR playbooks does a SOC typically use?
Forrester analyst Allie Mellen published a poll on Twitter a few months ago asking this question. The poll received 210 votes, and reveals that most SOCs use less than 10 playbooks. This reflects the experiences of our clients.
What is an effective method for building SOAR playbooks?
An artifact-based methodology can simplify SOAR playbook development. This approach focuses on the specific data elements, or “artifacts,” that are relevant to security incidents in your environment.
See Smart SOAR Playbooks in Action
Time is money. You waste time and money when your SOC team is forced to do incident response manually – missing out on the repeatability, speed and consistency that security automation and orchestration provides. Smart SOAR facilitates coordinated alert triage and investigation in seconds or minutes rather than hours, enabling you to detect intrusions earlier, respond faster, contain and eradicate breaches faster, and protect your business better. Sign up for a one-on-one demo to have all your questions about Smart SOAR’s capabilities answered. Save your seat.