6 Minutes and a Prayer: The Math That Proves Your SOC Is Gambling with Every Alert
This whitepaper presents a math-driven analysis that exposes an inconvenient truth hiding in plain sight across the cybersecurity industry.
This whitepaper presents a math-driven analysis that exposes an inconvenient truth hiding in plain sight across the cybersecurity industry.
Stop investigating alerts in isolation. A technical guide to Attack Path Discovery, separating vertical privilege escalation from horizontal lateral movement using specialized LLMs.

How unified security operations reduce complexity, cut costs, and strengthen cyber resilience — a strategic guide for CISOs and security leaders.
Filter by Type:
Search Resources:
This whitepaper presents a math-driven analysis that exposes an inconvenient truth hiding in plain sight across the cybersecurity industry.

Stop investigating alerts in isolation. A technical guide to Attack Path Discovery, separating vertical privilege escalation from horizontal lateral movement using specialized LLMs.
How unified security operations reduce complexity, cut costs, and strengthen cyber resilience — a strategic guide for CISOs and security leaders.

How D3 Morpheus lets MSSPs run AI-driven and deterministic SOC operations from a single multi-tenant instance with per-client AI governance.

How D3 Morpheus ingests and triages, then investigates and escalates security alerts with AI-autonomous intelligence purpose-built for the cloud-native environments, SaaS supply chains, source code…
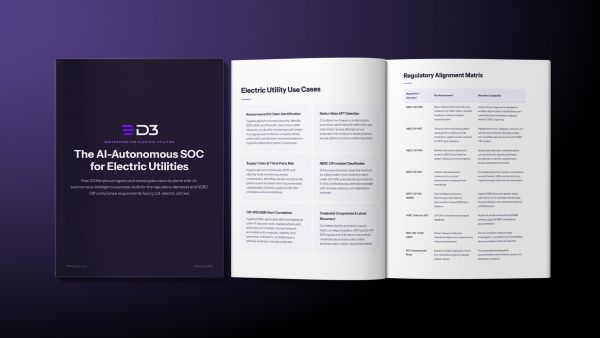
How D3 Morpheus ingests and investigates security alerts with AI-autonomous intelligence purpose-built for the regulatory demands and NERC CIP compliance requirements facing U.S. electric utilities.
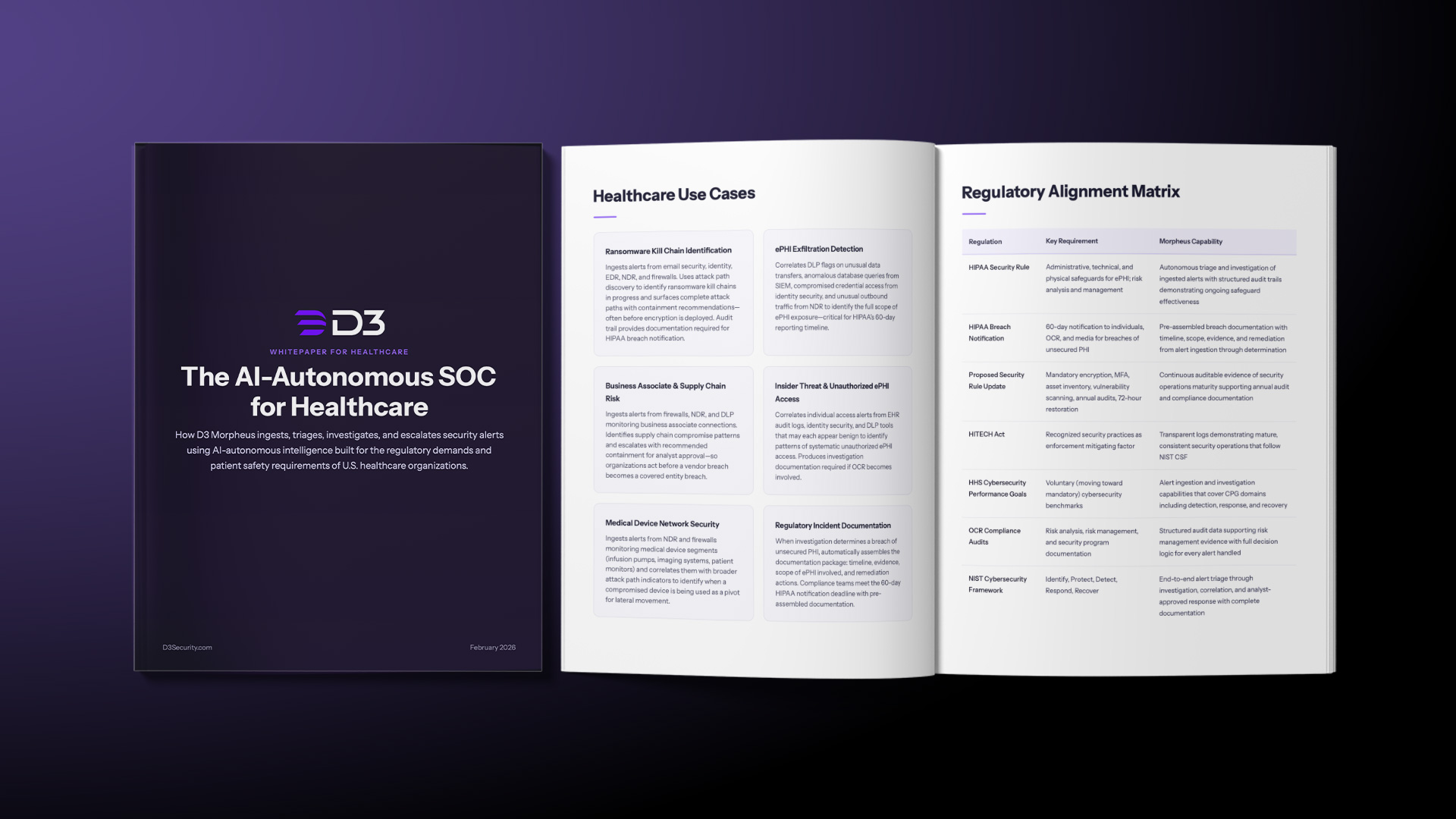
How D3 Morpheus ingests, triages, investigates, and escalates security alerts using AI-autonomous intelligence built for the regulatory demands and patient safety requirements of U.S. healthcare…

How D3 Morpheus ingests, triages, investigates, and escalates security alerts with AI-autonomous intelligence built for the intellectual property protection, regulatory complexity, and operational technology demands…

We tested D3 Morpheus AI against Microsoft Security Copilot across three real attack scenarios. Morpheus found root cause in all three. Copilot found it in…