How D3 Morpheus ingests, triages, investigates, and escalates security alerts with AI-autonomous intelligence built for the intellectual property protection, regulatory complexity, and operational technology demands of pharmaceutical manufacturers.
EXECUTIVE SUMMARY
Pharmaceutical companies sit at the intersection of several cybersecurity pressures: they hold some of the world’s most valuable intellectual property, operate under overlapping regulatory frameworks that demand data integrity and auditability, manage globally distributed manufacturing and supply chain operations, and are targeted by both financially motivated ransomware groups and state-sponsored espionage actors. D3 Morpheus is an AI-autonomous SOC built to address these pressures. The following outcomes summarize what Morpheus delivers for pharmaceutical organizations:
Protect Intellectual Property by Identifying Exfiltration Campaigns in Progress
Drug formulations, clinical trial data, manufacturing processes, and regulatory submission packages represent billions of dollars in R&D investment. Morpheus ingests alerts from SIEM, EDR, firewalls, NDR, email security, DLP, and identity security and uses its attack path discovery framework to correlate the subtle indicators of IP exfiltration (unusual data movement patterns, credential misuse, lateral movement toward research repositories) into complete attack paths. State-sponsored espionage campaigns and insider threats that would take human analysts weeks to identify are surfaced in real time.
Reduce Mean Time to Investigate from Hours to Minutes
Traditional SOC teams spend hours manually triaging, enriching, and correlating alerts across siloed tools. Morpheus autonomously performs the investigation work (enrichment, threat intelligence correlation, severity assessment based on IP sensitivity and GxP impact, and attack path reconstruction) in minutes. Analyst time shifts from repetitive triage to high-value decision-making on validated, pre-investigated findings.
Maintain 21 CFR Part 11 Data Integrity with Fully Auditable Alert Intelligence
Every action Morpheus takes is fully transparent and auditable: what alert data was analyzed, what reasoning was applied, what conclusions were drawn, and what actions were recommended. This structured audit trail provides the kind of complete, tamper-evident record that FDA inspectors expect under 21 CFR Part 11 and GxP guidelines. When regulators ask how a security event affecting GxP systems was handled, the answer is documented from alert ingestion to resolution.
Meet SEC’s 4-Business-Day Materiality Disclosure with Pre-Assembled Evidence
Publicly traded pharmaceutical companies must disclose material cybersecurity incidents on Form 8-K within four business days of materiality determination. Morpheus automatically generates investigation documentation (timeline, evidence chain, scope of impact, and classification rationale) from the structured audit trail it produces for every alert. Legal and compliance teams receive pre-assembled, disclosure-quality documentation rather than scrambling to reconstruct events under deadline pressure.
Detect Supply Chain and Third-Party Compromises Before They Cascade
The 2024 Cencora breach demonstrated how a single supply chain attack can cascade across 11 major pharmaceutical companies. Morpheus ingests alerts from the firewalls, NDR, and DLP tools that monitor CRO, CMO, distributor, and vendor connections, identifying supply chain compromise patterns before they propagate across the pharmaceutical value chain.
Scale SOC Capacity Across Global Manufacturing Without Proportional Headcount
Pharmaceutical companies operate research labs, manufacturing facilities, and distribution networks across dozens of countries, each generating alerts across IT and OT environments. Morpheus handles the high-volume work of alert triage, investigation, enrichment, and correlation autonomously while keeping humans in control of remediation decisions. This human-in-the-loop model allows organizations to handle significantly greater alert volumes without proportionally expanding SOC headcount, especially given the cybersecurity talent shortage and the industry’s historically low security spending relative to the value of assets under protection.
The Pharmaceutical Cybersecurity Crisis
The pharmaceutical industry is one of the most targeted sectors for cyberattacks. Its intellectual property is extremely high-value, its patient and clinical trial data is highly sensitive, and its manufacturing operations are critical infrastructure. A single pharmaceutical company’s R&D portfolio can represent tens of billions of dollars in investment, making drug formulations, clinical trial results, and regulatory submission packages among the most valuable digital assets in any industry.
The threats facing pharmaceutical companies in 2025 and 2026 span financially motivated ransomware, state-sponsored espionage, supply chain compromise, and insider threats, often simultaneously. The convergence of IT and operational technology in modern pharmaceutical manufacturing has expanded the attack surface considerably, while the industry’s complex global supply chains create cascading risk exposure.
| $4.61M Average cost of a pharmaceutical data breach in 2025 (IBM Cost of a Data Breach Report) |
| 50+ Ransomware incidents targeting pharmaceutical organizations recorded since January 2025 |
| 87% Of healthcare and pharmaceutical companies negatively affected by a breach in their third-party ecosystem |
| 46% Increase in ransomware attacks targeting operational technology systems in Q1 2025 (Honeywell) |
| 11 Major pharma companies reporting breaches from the single 2024 Cencora supply chain attack |
| 82% Of healthcare organizations reporting cyberattacks against IoT and connected devices |
Ransomware: Production Disruption and Double Extortion
Ransomware remains the top threat to pharmaceutical companies, accounting for approximately 29 percent of all attacks on the sector. Attackers now routinely employ double-extortion tactics, combining system encryption with data theft to maximize leverage. The consequences go beyond IT disruption: when ransomware reaches manufacturing systems, drug production halts, supply chains break, and patients may lose access to critical medications.
In August 2025, pharmaceutical R&D company Inotiv was hit by a ransomware attack attributed to the Qilin group. Attackers encrypted network systems, forced operations offline, and claimed to have exfiltrated over 170 gigabytes of sensitive data including employee and partner information. In Germany, pharmaceutical wholesaler AEP suffered a similar attack that partially encrypted IT systems and put medicine deliveries to more than 6,000 pharmacies at risk. These incidents illustrate how ransomware in the pharmaceutical sector directly threatens drug availability and patient access.
The most active ransomware groups targeting pharmaceutical organizations include Qilin, INC Ransom, and Cl0p. Across all groups, the United States remains the most targeted geography, reflecting the high concentration of valuable pharmaceutical assets and the willingness of U.S. companies to pay ransoms to protect time-sensitive research and manufacturing operations.
State-Sponsored Espionage and Intellectual Property Theft
Pharmaceutical intellectual property is a priority target for state-sponsored threat actors. Drug formulations, clinical trial data, manufacturing processes, and regulatory submission packages are targeted both for competitive advantage and national security purposes. The Winnti group, linked to Chinese state-backed operations, has targeted pharmaceutical companies including Bayer. During the COVID-19 pandemic, IBM detected multiple cyberattacks against vaccine cold chain logistics, targeting companies and government agencies involved in distribution.
The espionage threat extends beyond direct attacks on pharmaceutical companies. State-sponsored actors also target contract research organizations, contract manufacturing organizations, and other supply chain partners as indirect pathways to pharmaceutical IP. The distinction between financially motivated cybercrime and state-sponsored espionage is blurring, with some groups pursuing both objectives at once.
Supply Chain Cascade Risk
The pharmaceutical industry’s complex, globally distributed supply chain creates serious cascade risk. The 2024 Cencora breach made this concrete: attackers compromised one of the largest pharmaceutical distributors in the United States, exposed patient prescription and treatment data, and the breach cascaded to at least 11 major pharmaceutical companies including AbbVie, Bayer, Genentech, GlaxoSmithKline, Novartis, and Regeneron. Eighty-seven percent of healthcare and pharmaceutical companies report being negatively affected by a breach in their third-party ecosystem.
Contract research organizations handling clinical trial data, contract manufacturing organizations running production lines, IT service providers managing GxP-validated systems, and logistics companies managing cold chain distribution all represent potential entry points for attackers targeting pharmaceutical IP and operations.
IT/OT Convergence and Manufacturing Vulnerability
The pharmaceutical industry’s adoption of Industrial IoT has widened the attack surface within manufacturing operations. Connected sensors, monitoring systems, and edge devices throughout production lines create new entry points for attackers. Eighty-two percent of healthcare organizations have reported cyberattacks against their IoT and connected devices. Ransomware attacks targeting operational technology systems increased 46 percent in Q1 2025 alone.
Pharmaceutical manufacturing systems often run specialized protocols and software that conventional security tools do not recognize, creating blind spots. Production systems may include legacy equipment that cannot be patched or updated, creating persistent vulnerabilities. When attackers reach manufacturing OT environments, the consequences can include production shutdowns, drug contamination through process manipulation, and regulatory violations that trigger product recalls.
Why Traditional SOC Models Fail Pharmaceutical Companies
Traditional Security Orchestration, Automation, and Response (SOAR) platforms and legacy SIEM tools were not designed for the pharmaceutical industry’s combination of challenges:
| Static Playbooks Cannot Adapt to Hybrid Threats — Pharmaceutical companies face financially motivated ransomware groups, state-sponsored espionage actors, and insider threats at the same time. Static, manually built playbooks break when threats shift and cannot adapt to the convergence of these distinct threat categories. |
| No Contextual Understanding of IP Sensitivity — Traditional SOAR platforms treat all alerts equally regardless of what is being targeted. An alert involving a research database containing Phase III clinical trial data requires very different prioritization than an alert on a marketing workstation. Without contextual intelligence, critical IP threats are buried in alert noise. |
| IT/OT Silos Create Blind Spots — Pharmaceutical companies operate both IT environments (research, clinical, administrative) and OT environments (manufacturing, quality control, cold chain). Traditional security tools typically monitor one or the other, missing the lateral movement that attackers use to pivot from IT compromise to manufacturing disruption. |
| Integration Maintenance Overwhelms Security Teams — Every vendor API change, tool update, or infrastructure modification can break the integrations that SOAR platforms depend on. For pharmaceutical companies operating across multiple geographies with dozens of security tools, integration maintenance alone can consume a large share of SOC capacity. |
| No Regulatory-Aligned Documentation — Traditional SOAR platforms do not generate the structured, auditable documentation that pharmaceutical companies need for FDA inspections, SEC disclosures, and GxP compliance. Investigation evidence must be manually reconstructed after the fact. |
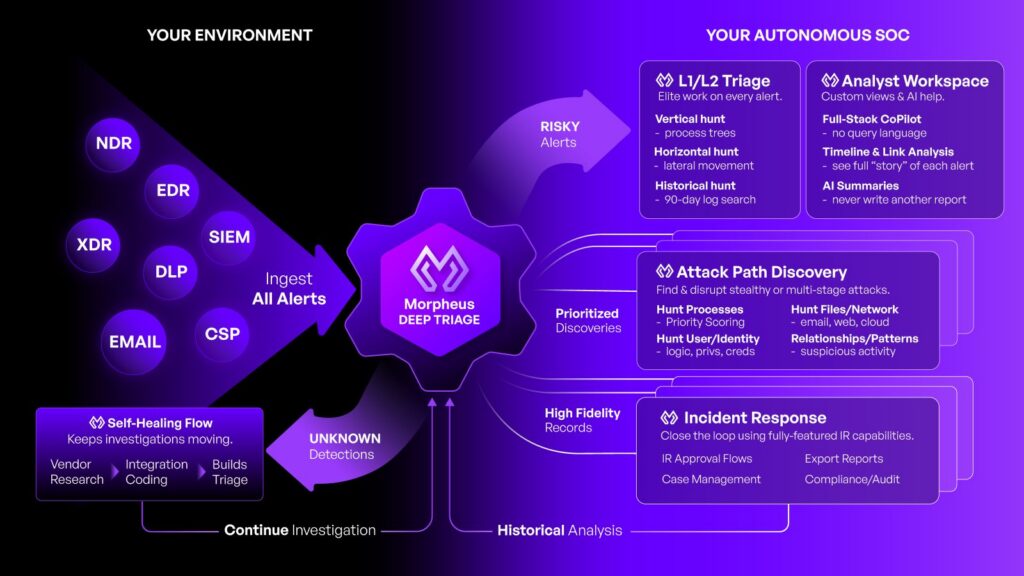
D3 Morpheus: The AI-Autonomous SOC
D3 Morpheus is designed to solve these challenges. As an AI-autonomous SOC, Morpheus ingests alerts from across a pharmaceutical organization’s existing security stack (SIEM, EDR, network firewalls, NDR, email security, DLP, and identity security) and applies a cybersecurity-specific threat LLM and attack path discovery framework to autonomously triage, investigate, and correlate those alerts into structured findings. Morpheus’s AI is customizable to each organization’s specific practices, every action and decision is fully transparent and auditable, and remediation recommendations are routed to human analysts for approval.

Cybersecurity-Specific Threat LLM
Morpheus is powered by a large language model trained specifically on cybersecurity threat intelligence, attack methodologies, and adversary tactics, techniques, and procedures. Unlike general-purpose AI or rule-based systems, this threat LLM understands the context and significance of security events in ways that mirror how experienced threat analysts think. It can assess whether an alert pattern indicates ransomware pre-encryption activity, IP exfiltration staging, or state-sponsored reconnaissance, and prioritize accordingly based on the pharmaceutical context.
Attack Path Discovery Framework
Morpheus’s attack path discovery framework correlates alerts across all ingestion sources (SIEM, EDR, firewalls, NDR, email security, DLP, and identity security) and across time windows to reconstruct the complete sequence of attacker behaviors. In the pharmaceutical context, this means identifying how an attacker progressed from an initial phishing email to credential compromise to lateral movement toward research databases or manufacturing control systems. Multi-stage IP exfiltration campaigns, supply chain infiltrations, ransomware kill chains, and insider threat progressions are surfaced as complete attack paths rather than isolated tickets.

Institution-Customizable AI
Morpheus’s AI is customizable to each pharmaceutical organization’s specific risk profile, regulatory environment, technology stack, and operational workflows. The platform generates organization-specific playbooks that align with the company’s IP classification hierarchy, GxP system inventory, manufacturing criticality levels, and incident response procedures. It incorporates historical incident data and learns from each organization’s alert patterns to improve triage accuracy and relevance over time. Self-healing integrations automatically adapt when security tools change, eliminating the integration maintenance burden that consumes traditional SOC capacity.
Human-in-the-Loop Remediation
Morpheus operates on a human-in-the-loop model: the platform autonomously triages, investigates, enriches, and correlates alerts, then routes remediation recommendations to human analysts for approval. Analysts review prioritized, pre-investigated findings and approve or reject recommended actions. This model is especially important in pharmaceutical environments where automated actions could affect GxP-validated systems, manufacturing processes, or clinical trial infrastructure. When configured to do so, Morpheus can execute approved actions proactively, but human authority over response decisions is maintained by default.
Full Transparency and Auditability
Every action Morpheus takes produces a complete, structured audit trail: what alert data was ingested, what enrichment was performed, what threat intelligence was correlated, what reasoning was applied, what conclusions were drawn, and what remediation actions were recommended. This audit trail is designed for the pharmaceutical regulatory environment where FDA inspectors, SEC examiners, and internal compliance teams expect verifiable, reproducible evidence of how security events were handled. The complete logic chain for every decision is available for review, supporting the data integrity principles required by 21 CFR Part 11 and GxP compliance.
Pharmaceutical Use Cases
Intellectual Property Exfiltration Detection
Pharmaceutical IP theft often follows a multi-stage pattern: initial access through phishing or credential purchase, lateral movement toward high-value research repositories, data staging in preparation for exfiltration, and data transfer to external destinations. Each stage generates alerts across different security tools. Morpheus ingests these alerts and uses attack path discovery to reconstruct the complete exfiltration campaign. When the platform identifies an IP exfiltration pattern, it routes the complete attack path with recommended containment actions to analysts for immediate review and approval.
Ransomware Kill Chain Identification in Manufacturing
Ransomware attacks on pharmaceutical manufacturers follow recognizable progressions that span IT and OT environments. Morpheus correlates alerts from email security (initial phishing vector), identity systems (credential compromise and privilege escalation), EDR (malware execution and lateral movement), NDR (network reconnaissance and C2 communication), and SIEM (aggregate anomaly detection) to identify ransomware kill chains before encryption is deployed. In manufacturing environments, early detection is the difference between containment and a production shutdown that disrupts drug supply.
Supply Chain and CRO/CMO Risk Monitoring
Morpheus ingests alerts from the firewalls, NDR, and DLP tools that monitor connections to contract research organizations, contract manufacturing organizations, distributors, and other supply chain partners. The platform identifies supply chain compromise patterns (unusual data flows from vendor connections, anomalous API behavior, unexpected access patterns from partner credentials) so pharmaceutical companies can detect and contain supply chain-originating threats before they cascade across the organization.
Clinical Trial Data Protection
Clinical trial data represents years of research investment and is subject to strict regulatory protections under GCP (Good Clinical Practice) and 21 CFR Part 11. Morpheus monitors the security telemetry surrounding clinical trial management systems, electronic data capture platforms, and regulatory submission repositories. When the platform detects access anomalies, data movement patterns, or credential misuse targeting clinical trial infrastructure, it surfaces the threat with full context for analyst review.
Insider Threat and Privileged Access Anomaly Detection
Pharmaceutical companies face serious insider threat risk: departing researchers, contractors with access to sensitive systems, and employees targeted for recruitment by competitors or nation-states. Morpheus correlates identity security alerts, DLP events, email security signals, and EDR telemetry to identify insider threat progressions, from initial indicators like after-hours access to research databases through data staging and attempted exfiltration.
Regulatory Incident Documentation
When Morpheus determines an event meets a regulatory notification or disclosure threshold, it automatically generates the investigation documentation package from the structured audit trail it produces for every alert. For SEC-mandated disclosures, this includes the timeline, scope, and materiality assessment evidence. For FDA inspections, it provides the complete record of how a security event affecting GxP systems was detected, investigated, and resolved. Compliance teams receive pre-assembled documentation rather than spending weeks reconstructing events after the fact.
Regulatory Alignment
Pharmaceutical companies operate under multiple overlapping regulatory frameworks. Morpheus’s capabilities map directly to the specific requirements of each:
| Regulation / Framework | Key Requirement | Morpheus Capability |
| 21 CFR Part 11 | Electronic records must maintain data integrity with audit trails, access controls, and system validation | Complete, tamper-evident audit trail for every alert triage, investigation, and recommendation; full logic chain available for FDA inspection |
| FDA OT Guidance (June 2025) | Securing operational technology in pharmaceutical manufacturing; identity-based access, network segmentation monitoring, documentation and audit requirements | Ingests alerts from OT-monitoring tools (NDR, firewalls); correlates IT/OT alert streams to identify lateral movement from IT into manufacturing environments |
| GxP (GMP, GLP, GCP) | Data integrity, validated systems, controlled processes, complete documentation for regulated activities | Organization-customizable AI aligns with GxP system inventories; audit trail supports data integrity expectations across manufacturing, laboratory, and clinical environments |
| SEC Cybersecurity Rules (2023) | Material incident disclosure on Form 8-K within 4 business days; annual risk management and governance disclosures on Form 10-K | Pre-assembled investigation documentation with timeline, evidence, scope, and classification rationale; structured audit trail accelerates materiality determination |
| HIPAA Security Rule | Protection of patient and clinical trial participant PHI; breach notification within 60 days for 500+ individuals | Monitors security telemetry around PHI-containing systems; generates breach scope documentation for notification decisions |
| NIST CSF / IEC 62443 | Risk-based cybersecurity framework; industrial automation and control system security standards | Autonomous triage and investigation aligned with risk-based prioritization; ingests OT security telemetry for manufacturing environment monitoring |
| EU NIS2 Directive | Incident reporting within 24 hours (early warning) and 72 hours (detailed); supply chain security; risk management measures | Real-time investigation documentation supports rapid EU notification timelines; supply chain alert monitoring across vendor connections |
| GDPR | Protection of personal data; 72-hour breach notification to supervisory authorities; data protection impact assessments | Identifies data exposure scope from alert correlation; pre-assembled documentation supports 72-hour notification timeline for EU operations |
Implementation and Deployment
D3 Morpheus integrates with a pharmaceutical organization’s existing security infrastructure without requiring replacement of current tools or disruption to validated environments. The platform connects to the organization’s SIEM, EDR, firewalls, NDR, email security, DLP, and identity security tools through pre-built integrations that ingest alert data in real time.
Implementation follows three phases:
| Phase 1: Environment Discovery and Integration — Morpheus connects to the organization’s existing security tools and begins ingesting alert data. The platform’s self-healing integrations automatically adapt to tool configuration changes, eliminating ongoing integration maintenance. During this phase, Morpheus maps the organization’s technology environment including GxP-validated systems, manufacturing OT environments, research infrastructure, and clinical trial platforms. |
| Phase 2: Customization and Calibration — Morpheus’s AI is configured to align with the organization’s specific risk profile, IP classification hierarchy, GxP system inventory, regulatory obligations, and incident response procedures. The platform generates organization-specific playbooks and begins processing alerts with pharmaceutical-contextualized intelligence. |
| Phase 3: Operational Integration — Morpheus is integrated into the organization’s SOC workflow. Analysts begin reviewing and acting on Morpheus’s pre-investigated findings and remediation recommendations. The platform’s performance improves as it incorporates feedback from analyst decisions and learns from the organization’s specific alert patterns and incident history. |
Throughout deployment, Morpheus operates alongside existing security operations rather than replacing them. The platform improves over time as its customizable AI becomes better aligned with the organization’s specific pharmaceutical environment, threat profile, and operational workflows.

The Case for Autonomous Alert Intelligence
The pharmaceutical industry’s security problem is getting worse, not better. The volume and sophistication of cyberattacks are increasing. Regulatory requirements are expanding. The attack surface is growing as IT/OT convergence, cloud adoption, and supply chain digitization create new exposure. And the cybersecurity talent gap makes it increasingly impractical to address these challenges through headcount alone.
D3 Morpheus is a different kind of solution: an AI-autonomous SOC that ingests alerts from across the entire security stack, autonomously triages and investigates those alerts with a cybersecurity-specific threat LLM, reconstructs complete attack paths through the attack path discovery framework, and routes validated findings with remediation recommendations to human analysts for approval.
For pharmaceutical companies, the implications are concrete: IP exfiltration campaigns identified in minutes instead of weeks. Ransomware kill chains detected before encryption reaches manufacturing systems. Supply chain compromises contained before they cascade. Clinical trial data protected with intelligence that understands its regulatory significance. SEC disclosure deadlines met with pre-assembled evidence. FDA inspections supported with complete, auditable records. SOC capacity scaled to match a global pharmaceutical operation without proportional headcount growth.
These cybersecurity challenges are not going away. The question is whether pharmaceutical organizations will continue to rely on tools built for a simpler threat environment, or adopt AI-autonomous intelligence that matches the scale and complexity of what they’re actually facing.

