Executive Summary
Alert fatigue is the defining operational crisis of modern security operations. The average enterprise SOC receives over 4,400 alerts per day. Large organizations face 10,000 or more across 30 integrated security tools. Analysts investigate only 37% of them. The rest are triaged superficially, deprioritized, or ignored entirely.
This is not a staffing problem. It is a structural one. SIEMs were built to detect and alert. They do this well. But detection without investigation creates a bottleneck that no amount of hiring, tuning, or rule-writing can resolve. Each alert requires an average of 70 minutes to fully investigate (SANS, 2025). At 4,400 alerts per day, an organization would need 200+ full-time analysts working around the clock to investigate every alert manually.
The consequences are measurable: 61% of SOC teams admit to ignoring alerts that later proved genuine. Over 70% of SOC analysts report burnout. The average analyst stays in the role for fewer than three years.
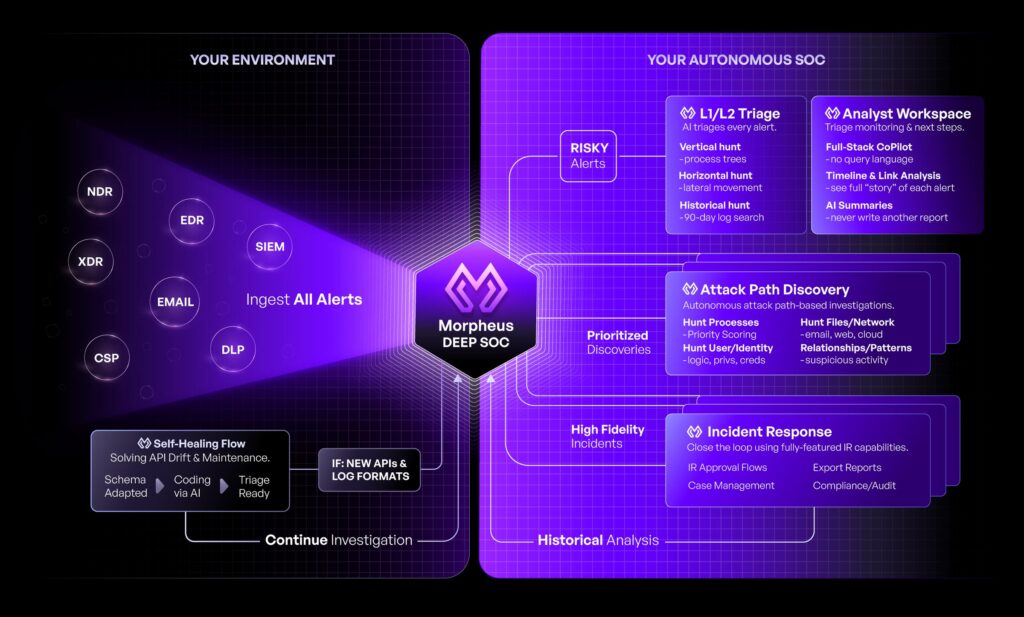
D3 Security’s Morpheus AI is an Autonomous SOC platform powered by a purpose-trained cybersecurity LLM. Morpheus AI does not filter alerts or suppress noise. It investigates every alert at L2 analyst depth—correlating across the full security stack, tracing attack paths, and generating contextual response playbooks—in under two minutes. It reduces SIEM alert fatigue by eliminating the investigation bottleneck, not by hiding the alerts.
Who should read this: CISOs, SOC directors, security architects, and anyone evaluating AI SOC or SOAR platforms to reduce SIEM alert fatigue and reclaim analyst capacity.
Table of Contents
- The Anatomy of Alert Fatigue: Why Tuning the SIEM Is Not Enough
- Five Approaches to Reduce SIEM Alert Fatigue—Compared
- How Morpheus AI Reduces SIEM Alert Fatigue
- Before and After: SOC Operations With Morpheus AI
- Where Alert Fatigue Hits Hardest: Four Use Cases
- Questions for Your Evaluation
- Next Steps
The Anatomy of Alert Fatigue: Why Tuning the SIEM Is Not Enough
Most organizations treat alert fatigue as a tuning problem. They adjust rules, thresholds, and filters to reduce noise. The result is temporary. Fatigue returns because tuning addresses symptoms, not causes.
Alert fatigue has five structural root causes. Each one persists regardless of which SIEM you run or how aggressively you tune it.
Volume Exceeds Human Capacity
Enterprise SOCs receive 4,400+ alerts per day. A single analyst can investigate 8–12 alerts per shift at full depth. The math does not work. Tuning reduces volume marginally; it does not close a 50:1 capacity gap.
False Positives Erode Trust
Over 50% of SIEM alerts are false positives. Some organizations report rates as high as 80%. When analysts know most alerts are noise, they start treating all alerts as noise. Trust in the alert pipeline degrades. Real threats get lost.
Alerts Lack Context
A SIEM alert tells you something happened. It does not tell you why it matters, what happened before and after, or what the attacker is trying to achieve. Analysts must manually pivot across 5–8 tools to build investigation context. This context-gathering consumes 56 minutes before any investigation even begins.
Static Playbooks Cannot Adapt
Traditional Security Orchestration, Automation and Response (SOAR) playbooks execute the same steps regardless of context. A phishing playbook runs identically whether the target is an intern or the CFO, whether the payload is known or novel. Static logic in a dynamic threat landscape guarantees stale responses.
Analyst Burnout Creates a Talent Drain
Over 70% of SOC analysts report burnout. The average analyst stays in the role under three years. When experienced analysts leave, institutional knowledge leaves with them. New hires face the same overwhelming volume with less context. The cycle accelerates.
Five Approaches to Reduce SIEM Alert Fatigue—Compared
Organizations use multiple strategies to reduce SIEM alert fatigue, each with clear tradeoffs. The table below compares the ones that matter most to security operations leaders.
| Approach | How It Works | Impact on Alert Fatigue | Limitations |
|---|---|---|---|
| SIEM Tuning | Adjust correlation rules, raise thresholds, add suppression filters | Reduces noise 10–20% temporarily | Requires ongoing analyst effort; new sources reintroduce noise; risk of suppressing real threats |
| Alert Aggregation | Group related alerts into clusters; deduplicate across sources | Reduces visible volume 20–30% | Clusters still require manual investigation; no contextual triage; does not resolve false positives |
| SOAR Playbooks | Automate fixed response steps for known alert types | Covers 30–40% of alert types at maturity | 12–18 month deployment; requires dedicated SOAR architect ($150K–$250K); static logic cannot adapt to novel threats |
| AI Alert Scoring | ML models reprioritize alerts by predicted severity | Improves prioritization accuracy | Better ranking is not investigation; analysts still must investigate top-priority alerts manually; no response generation |
| Autonomous Investigation | AI investigates every alert at L2 depth, correlates across stack, generates contextual playbooks | Reduces analyst investigation workload by 90%+; covers 100% of alerts from day one | Requires purpose-trained cybersecurity AI; not all vendors deliver true autonomous investigation |
The critical distinction: Most approaches reduce alert volume. Autonomous investigation reduces the work per alert. One hides the problem. The other solves it.
Why Layering Falls Short
Many SOCs stack these approaches: tune the SIEM, aggregate alerts, deploy SOAR for the top 30 alert types, and add an AI scoring layer. The result is marginal improvement at significant cost and complexity. Alert fatigue persists because the fundamental bottleneck—human investigation time—remains unchanged.
Morpheus AI addresses the bottleneck directly. It does not filter, score, or suppress alerts. It investigates them—every one, at full depth, in under two minutes.
How Morpheus AI Reduces SIEM Alert Fatigue
Morpheus AI eliminates alert fatigue by attacking the root cause: the investigation bottleneck. On every incoming alert, Morpheus AI performs autonomous multi-dimensional investigation at L2 analyst depth. Here is exactly what happens when an alert arrives.
Alert Ingestion
From any SIEM or detection tool
Cross-Stack Correlation
EDR + Identity + Cloud + Network
Attack Path Discovery
Vertical + Horizontal tracing
Contextual Playbook
Generated at runtime from evidence
Four Capabilities That Eliminate the Bottleneck
Attack Path Discovery
Morpheus AI traces attack progression both vertically (initial access through execution) and horizontally (lateral movement across systems). It queries the SIEM, EDR, identity provider, cloud controls, and network tools to build a complete attack timeline—the same work that takes a human analyst 56+ minutes of manual pivoting.
Contextual Playbook Generation
Instead of executing a static template, Morpheus AI generates a bespoke investigation and response playbook for each alert based on the specific evidence, target, environment, and organizational SOC preferences. No SOAR architect required. No playbook maintenance burden.
Self-Healing Integrations
When vendor API changes break tool connections, Morpheus AI detects the failure and repairs the integration autonomously. Traditional SOAR deployments lose hours or days to silent integration failures. Morpheus AI keeps the investigation pipeline running without human intervention.
Analyst-Ready Investigation Reports
Every investigation produces a structured report with full reasoning chain, evidence timeline, severity assessment, and recommended actions. Analysts review conclusions rather than build them. Escalation decisions go from hours to minutes.
Morpheus AI makes the SIEM more valuable, not less. Every SIEM log, correlation rule, and enrichment feed contributes to a more complete investigation. The SIEM is the data foundation; Morpheus AI is the investigation intelligence.
Before and After: SOC Operations With Morpheus AI
The following table compares key SOC operational metrics before and after Morpheus AI deployment. These figures reflect the structural shift from human-dependent investigation to autonomous AI investigation.
| Operational Metric | Before Morpheus AI | With Morpheus AI |
|---|---|---|
| Alerts investigated per day | 37% (limited by analyst capacity) | 100% (every alert, every time) |
| Time to investigate one alert | 70 minutes (manual cross-tool pivoting) | < 2 minutes (autonomous investigation) |
| False positive resolution | Manual review of each alert | Automated with full reasoning chain |
| Attack path visibility | Single-tool or manual correlation | Cross-stack: EDR, SIEM, identity, cloud, network |
| Playbook coverage | 30–40% of alert types at maturity | 100% of alerts from day one |
| SOAR architect dependency | Required ($150K–$250K/year) | Eliminated—intelligence embedded in platform |
| Integration maintenance | Manual; silent failures common | Self-healing; autonomous repair |
| Analyst role | Triage and investigate (repetitive) | Review, validate, and hunt (strategic) |
The Analyst’s Day, Transformed
Before Morpheus AI, a SOC analyst spends 80% of their shift on repetitive triage: opening alerts, pivoting across tools, chasing false positives, documenting findings, and escalating without confidence. After deployment, Morpheus AI handles the investigation. Analysts review completed investigation reports, validate AI-generated conclusions, and focus on proactive threat hunting and high-value security work.
This is not about replacing analysts. It is about removing the repetitive work that drives them out of the profession.
Where Alert Fatigue Hits Hardest: Four Use Cases
Alert fatigue manifests differently depending on the alert type, the security stack, and the organization’s operational maturity. The following scenarios illustrate how Morpheus AI resolves the fatigue pattern in each case.
Phishing Alert Overload
A mid-market SOC receives 600+ phishing alerts daily from its email gateway. Analysts can investigate 40. Morpheus AI investigates every alert: checks sender reputation, detonates attachments, correlates with identity logs, traces any credential harvesting attempts, and generates a targeted response playbook. Analysts review only confirmed threats.
EDR Noise From Legitimate Admin Tools
Endpoint detection tools flag PowerShell, PsExec, and WMI usage thousands of times per day. Most are legitimate IT operations. Morpheus AI correlates each alert against identity context, scheduled change windows, asset criticality, and behavioral baselines. Genuine lateral movement is surfaced with full attack path context. Noise is resolved with documented reasoning.
Cloud Misconfig Alert Storms
After a cloud migration, CSPM tools generate hundreds of configuration alerts daily. Security teams cannot distinguish between critical exposures and low-risk findings at scale. Morpheus AI correlates each misconfiguration against network exposure, asset sensitivity, and active exploit intelligence to prioritize what actually requires action.
Identity and Access Anomalies
Identity providers flag impossible travel, unusual access patterns, and MFA failures in high volume. Most are benign—VPN routing, mobile device switches, time zone changes. Morpheus AI investigates each anomaly against the full identity timeline, correlates with endpoint and network telemetry, and surfaces only confirmed compromise indicators.
The Common Pattern
In each case, the SIEM or detection tool generates the alert correctly. The tool is doing its job. The fatigue comes from the gap between detection and investigation—the gap where alerts pile up, analysts burn out, and real threats hide in the noise. Morpheus AI closes that gap on every alert, across every source, without requiring custom playbooks or additional headcount.
Key insight: Alert fatigue is not caused by bad detection. It is caused by the absence of automated investigation. Fix the investigation bottleneck and the fatigue disappears—without sacrificing detection fidelity.
Questions for Your Evaluation
Not every product that claims to reduce SIEM alert fatigue delivers the same depth of capability. The following questions help distinguish between surface-level noise reduction and genuine investigation automation. Use them when evaluating any AI SOC, SOAR, or alert management platform.
| # | Evaluation Question | What the Answer Reveals |
|---|---|---|
| 1 | Does the platform investigate alerts or only score and prioritize them? | Scoring still leaves the investigation burden on humans. Investigation automation is the structural fix. |
| 2 | What percentage of alert types does the platform cover on day one? | Static playbook platforms cover 30–40% at maturity. Autonomous investigation covers 100% immediately. |
| 3 | Does the platform correlate across EDR, SIEM, identity, cloud, and network? | Single-source correlation misses multi-stage attacks. Cross-stack correlation catches lateral movement. |
| 4 | Are response playbooks generated from evidence or selected from templates? | Template-based playbooks cannot adapt to novel threats. Contextual generation matches response to evidence. |
| 5 | Does the platform require a dedicated SOAR architect? | Architect dependency creates a single point of failure, ongoing cost, and knowledge loss on turnover. |
| 6 | How does the platform handle vendor API changes? | Silent integration failures are the most common cause of automation breakdown. Self-healing is the fix. |
| 7 | Is the AI purpose-trained for cybersecurity or a general-purpose LLM? | General-purpose models lack domain-specific reasoning about attack progression and security telemetry. |
| 8 | Can the platform show its reasoning chain for every investigation? | Explainability is not optional. Analysts and auditors must understand why the AI reached its conclusion. |
Morpheus AI answers every question above affirmatively. Purpose-trained cybersecurity LLM. 100% alert coverage from day one. Cross-stack correlation. Contextual playbook generation. Self-healing integrations. Full reasoning chain on every investigation. No SOAR architect required.
Next Steps
Alert fatigue will not resolve itself. SIEMs will continue to detect. Alert volumes will continue to grow. The question is whether your analysts spend their time investigating noise or whether autonomous AI handles the investigation so your team can focus on what matters.
Morpheus AI is available for live demonstration. See how it investigates your alerts, correlates across your stack, and generates contextual response playbooks—on real data, in real time.
To schedule a demonstration, visit d3security.com.

