The D3 Blog
Learn about the latest from D3 and the world of cybersecurity, with news, analysis, and more.
-
GPT Can’t Trace an Attack Chain. A Purpose-Built Cybersecurity LLM Can.
A purpose-built cybersecurity LLM is trained on security data from the ground up — not a general-purpose model with a security prompt. Here’s why the…
-
The Best AI SOC Platforms 2026: Comprehensive Comparison & Guide
Comprehensive guide to the best AI SOC platforms in 2026. Compare autonomous SOC solutions, pricing, integrations, and key differentiators.
-
Amazon Lost 6.3 Million Orders to Vibe Coding. Your SOC Is Next.
Amazon mandated AI coding tools and suffered a 6-hour outage costing 6.3 million orders. The same AI quality crisis now emerging in SOC operations.
Filter by category:
Search blog:
-
 MITRE ATT&CK, SOAR
MITRE ATT&CK, SOARImplementing MITRE D3FEND for ATT&CK Technique T1059: Command and Scripting Interpreter
Command and Scripting Interpreter attacks were the second most common technique seen in MITRE’s Engenuity’s Sightings Ecosystem report, representing 15.77% of 1.1 million sightings. MITRE’s…
-
 MSSPs, SOAR
MSSPs, SOAR8x Faster Response, 99% Alert Noise Reduction: Smart SOAR’s Impact on High Wire Networks’ Cybersecurity Operations
In case you missed it, you can still watch our recent workshop featuring Stephan Tallent, CRO at US-based master MSSP High Wire Networks, and Pierre…
-
 MITRE ATT&CK, SOAR
MITRE ATT&CK, SOARImplementing MITRE D3FEND for ATT&CK Technique T1053: Scheduled Task/Job
Scheduled task/job threats, which make up MITRE ATT&CK Technique T1053, can have severe implications for an organization’s security. MITRE also outlines how to address this…
-
 SOAR
SOARHow SOAR and OSINT Work Together
The collection and analysis of open-source threat intelligence (OSINT) are valuable stages in incident response. However, with large datasets and alert volumes, this process becomes…
-
 Reports, SOAR
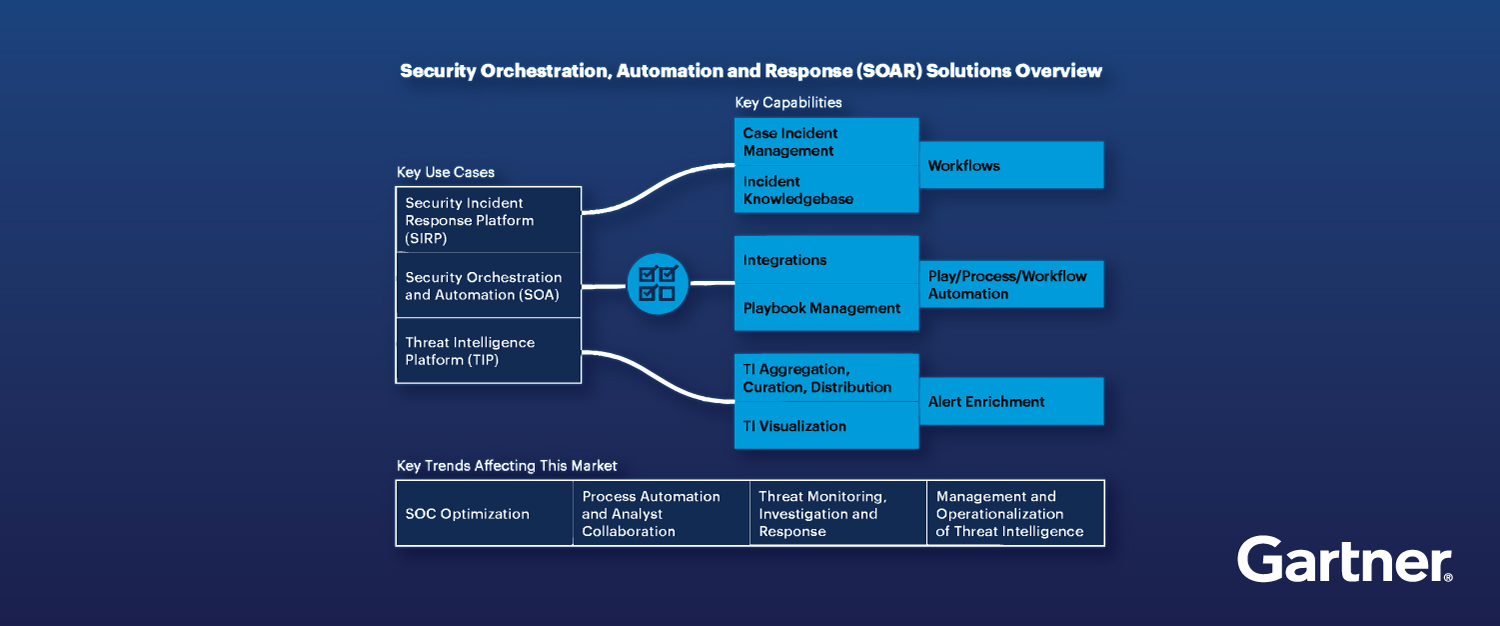
Reports, SOARTop 5 Takeaways From Gartner’s 2023 Market Guide for SOAR
As an independent, vendor-agnostic SOAR provider, we‘re thrilled to announce that D3 Security has been recognized for the third consecutive time as a Representative Vendor…
-
 MITRE ATT&CK, SOAR
MITRE ATT&CK, SOARHow to Automate Incident Response to MITRE ATT&CK Technique T1003: OS Credential Dumping
In this blog post, we will outline four incident response playbooks for MITRE ATT&CK Technique T1003: OS Credential Dumping. Credential Dumping is a technique that…
-
 SOAR
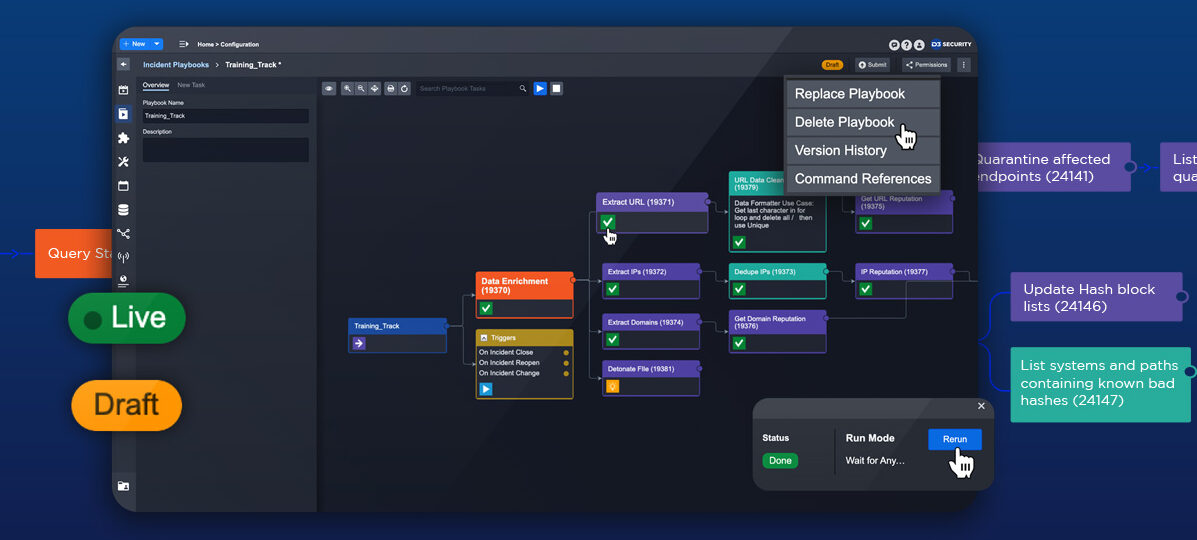
SOARSmart SOAR Gives You the Best Cybersecurity Playbooks
Security operation center (SOC) teams need security orchestration, automation, and response (SOAR) because it provides a simple, efficient, and effective method for response to the…
-
 News, SOAR
News, SOARTackle Automation Challenges With Smart SOAR at FutureCon St. Louis
We’re thrilled to announce that we are a gold sponsor of FutureCon St. Louis, where cybersecurity leaders, executives, and CISOs (chief information security officers) will…
