Our latest update to Smart SOAR brings many enhancements that provide a more nuanced control over incident management and tenant operations. Key updates include a redesigned Playbook Editor with a new task bar and task templates for more intuitive playbook creation, and a more efficient workspace. We’ve also expanded the Incident Field Mapping capabilities, allowing for more granular control and customization based on incident types. We’ve also introduced a role-based access control system for utility commands. These enhancements are designed to provide more control, less clutter, and a smoother user experience. Here’s what you should know:
Playbook Editor Enhancements
Refreshed Playbook Editor UI
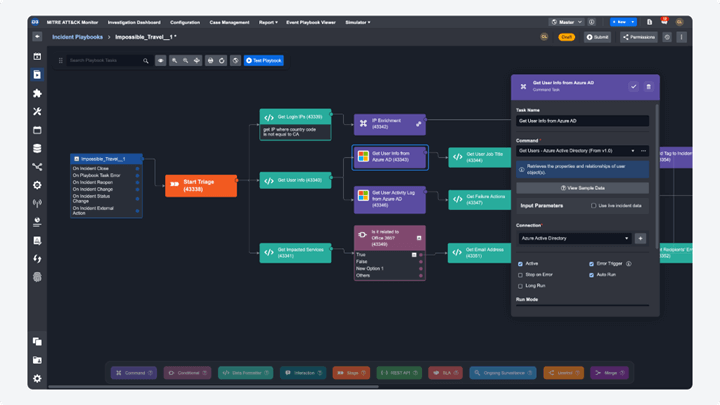
We’re excited to introduce the latest update to our playbook editor, featuring a sleek, modern design that optimizes workspace and user interaction. Here’s what’s new:
Playbook Task Bar
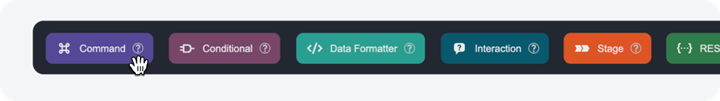
The playbook tasks have been relocated to a new horizontal bar at the bottom of the editor, providing a cleaner appearance and expanding the workspace for better playbook visibility. The feature for command searching is now integrated within the command task node, enabling quick access to integration and utility command searches upon hovering over it.
Playbook Task Templates
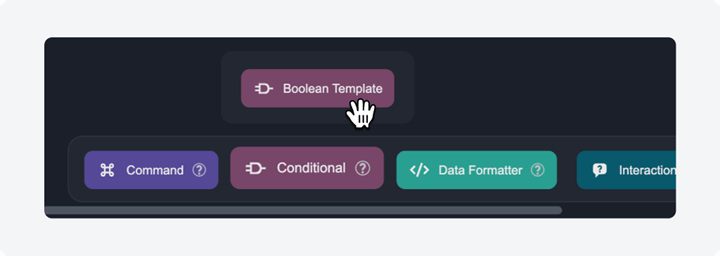
Both command and conditional tasks now feature configuration templates. To explore these templates, hover over the respective task on the horizontal playbook task bar. In version 16.5, the command task includes a template for constructing nested playbooks, while the conditional task offers a template for creating boolean conditions.
Redesigned Root Node
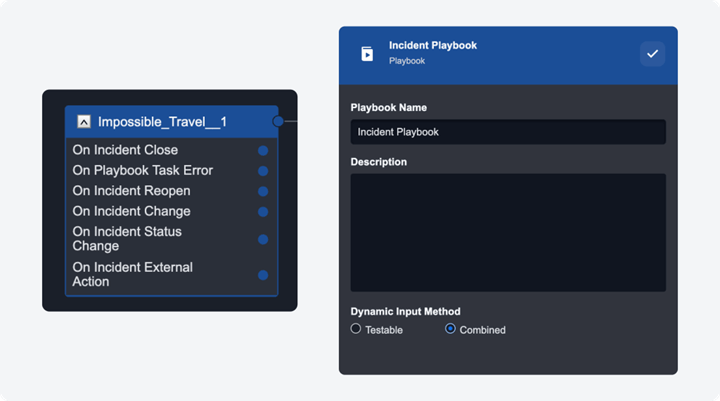
The root node in the playbook editor has been redesigned, now directly integrating the playbook trigger options. This removes the need for an additional trigger node, simplifying the overall interface. To modify the playbook’s name, description, and dynamic input method, simply click on the root node to open the configuration dialogue.
Floating Components
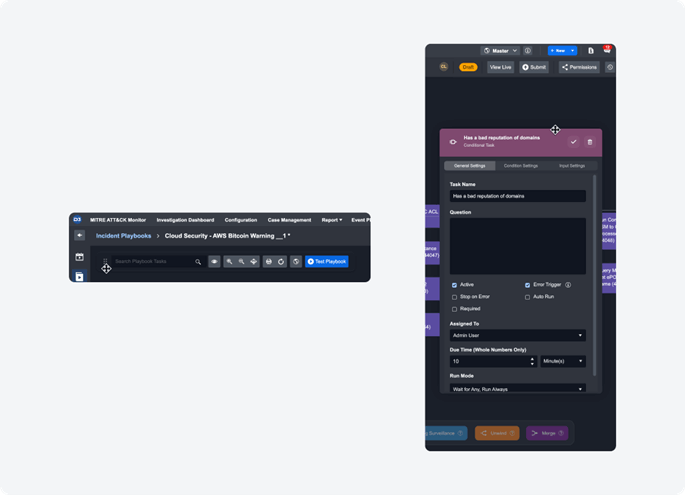
In line with modern design principles, the update introduces adaptable floating elements, such as the playbook editor toolbar and task configuration dialogues. These can be dragged and resized, offering a more flexible and efficient editing environment.
Incident Field Mapping: Dynamic Fields
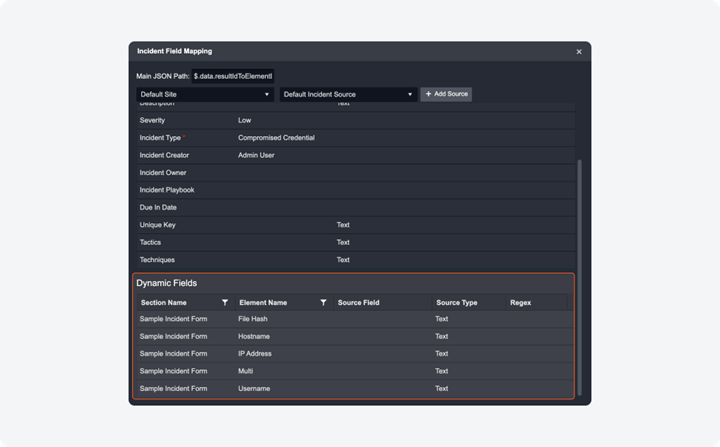
Previously, incident field mapping was limited to a set of incident-specific system fields with the ingested data of Fetch Incident commands. With this update, you can now configure custom incident field mappings by incident type, within the Incident Form Editor. Each Info Activity in an incident form will be available in the corresponding incident type as a dynamic field to configure for field mapping.
Tenant Management Enhancements
Tenant Site Status
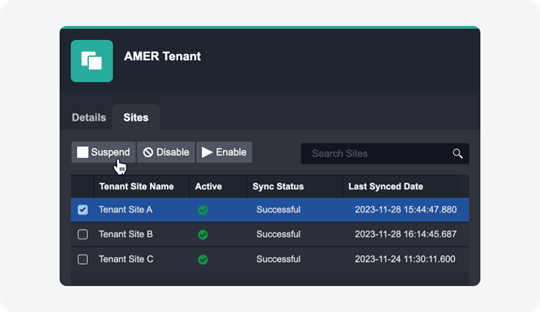
The configuration options for tenant site statuses have been updated to “Enable”, “Suspend”, and “Disable”, replacing the former “Activate” and “Deactivate”. These status options, along with the newly added Update Tenant Site Status utility command, greatly facilitate automated client tenant onboarding and offboarding for Managed Security Service Providers (MSSPs). Here’s a detailed overview:
Enable: In this mode, all systems and operations, such as health checks, event fetching, and incident fetching, function seamlessly. Automation rules and connections are restored to their normal working condition after reactivation.
Suspend: Under this status, all operational schedules are paused, and the health check feature is deactivated. However, automation rules and connections retain their last states (active or inactive). While new events or incidents can’t be added to dashboards, editing existing records and executing related playbooks is possible. Tenant sites in the suspended state are still available for selection in playbook tests.
Disable: This status effectively renders all site-related functionalities hidden and unselectable. This includes schedules, automation rules, connections, dashboards, and playbook tests. Access to historical records is also restricted in this state. Additionally, the site will not be visible in the dropdown menu for site selection.
The Update Tenant Site Status utility command can be leveraged to allow these status changes to be automated by playbooks. This streamlines the process of onboarding and offboarding clients, making it more efficient and less prone to errors. MSSPs can automate much of the client lifecycle management, from initiating services with “Enable” to temporarily pausing with “Suspend”, and finally, securely offboarding with “Disable”.
Utility Commands
Role-based Access Control
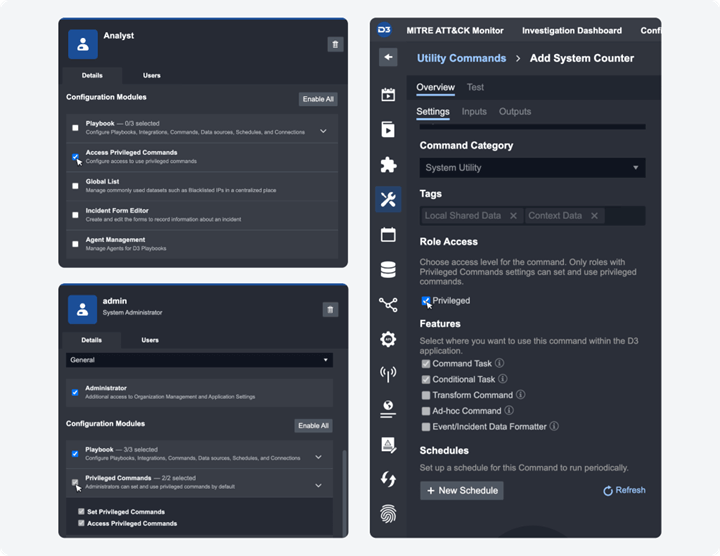
We’ve introduced a role-based access control system for utility commands. This feature allows only specific roles to configure and execute certain commands. To set this up, go to Configuration > Organization Management > Roles. Once you select a role, visit the Details tab and locate the Configuration Module section. For administrator roles, the “Privileged Commands” permission will be visible under this section, comprising two sub-permissions: “Set Privileged Commands” and “Access Privileged Commands.” These are automatically enabled for admin roles and cannot be modified. For other general access roles, only the “Access Privileged Commands” permission will be available to configure.
Administrators have the flexibility to designate which utility commands are considered privileged on a command-by-command basis. To do this, navigate to Configuration > Utility Command. Select the utility command you wish to modify, and in the Settings tab, you will see the Role Access setting. Here, use the Privileged checkbox to mark the command as privileged. This designation restricts its use to only those users who have privileged rights. Privileged users will be able to:
- Search and view the command within the Utility Commands module under Configuration.
- Add the command when configuring playbooks.
- Run it as an ad hoc command within an incident.
New Commands
The following utility commands have been added to this release of D3 SOAR.
| Commands | Functionality |
| Add New Artifacts in Event Playbook | Adds a new artifact to an event when it is ingested and processed in an event playbook. This command can only be used in the event playbook with the “On Event ingestion” trigger. |
| Update Tenant Site Status | Updates the status of a tenant site for a specified region and tenant with three options: Suspend, Disable, and Enable. |
Updated Commands
The following utility commands have been updated in this release of D3 SOAR.
| Commands | Changes |
| Save and Link Artifacts to Incident | When the “Artifact Type” parameter is not defined, the command will automatically add it to an existing system or custom artifact type based on the defined artifact fields. |




