IBM sold its QRadar SaaS assets to Palo Alto Networks in August 2024. The SaaS version officially hit End of Sale in April 2025, with full End of Life to follow. And while IBM says it will continue supporting on-premises QRadar for now, industry analysts aren’t betting on a long runway.
Forrester analysts put it bluntly: customers clinging to QRadar are “building on a product that will be on life support and eventually end-of-life.”
But here’s the thing: forced migrations are rare moments of leverage. The question is whether you spend that budget moving sideways to another tool with the same limitations, or whether you leapfrog to something that actually solves the problems SOAR never did.

What actually happened (and why it matters)
The QRadar exit was a signal that IBM couldn’t make traditional SOAR economics work at scale. When customers grew frustrated with what analysts called a “perceived lack of innovation,” and Palo Alto came knocking, IBM took the exit.
The deal included QRadar SOAR, QRadar EDR, X-Force Threat Intelligence, and Randori Recon. All of it now sits under Palo Alto’s roof, with a clear directive: migrate customers to Cortex XSIAM.
The “free migration” offer: what it actually covers
Palo Alto and IBM are offering “no-cost migration services” to qualified QRadar customers. In practice, it covers migration tooling and IBM Consulting hours. It doesn’t cover the harder costs.
Rewriting your SOAR workflows. SOAR playbooks are often incompatible between platforms. The logic you built in QRadar SOAR doesn’t port cleanly to XSIAM.
Re-integrating third-party tools. XSIAM integrates tightly with Palo Alto’s own EDR and firewalls. Third-party log sources, particularly cloud and SaaS applications, often require custom work. One analysis noted that XSIAM “struggles to ingest logs comprehensively from third-party sources, potentially creating gaps in security visibility.”
Training your team. Productivity drops during the learning curve, and experienced analysts may resist yet another platform shift.
Accepting ecosystem lock-in. XSIAM is bundled with Palo Alto’s XDR. You’re not buying a modular tool; you’re buying an ecosystem. The real cost shows up in what you have to change around it.
The deeper question: do you want another SOAR, or the problem solved?
Let’s be honest about QRadar SOAR’s pain points. Playbooks required scripting expertise. Integration drift broke workflows whenever a vendor changed an API field. Your best analysts spent their time debugging automation instead of investigating threats. The maintenance burden never went away; it just got reclassified as “SOAR operations.”
Traditional SOAR is a deterministic workflow engine. If A happens, do B. If B returns X, do C. But modern SOCs don’t operate in stable environments. Detection rules change. APIs evolve. Attackers adapt faster than playbook updates.
The result is a maintenance treadmill. Migrating from QRadar SOAR to another traditional SOAR, whether that’s XSIAM, Splunk SOAR, or anything else built on static playbooks, means relocating the same problem to a new address.
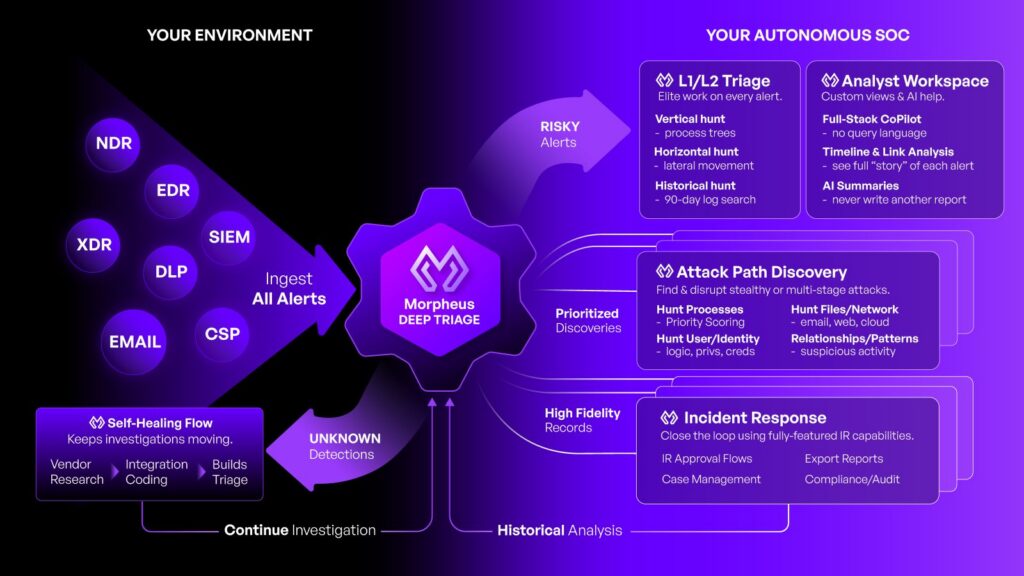
A different operating model: autonomous security operations
| IBM QRadar | Cortex XSOAR | Morpheus (D3 Security) | |
| Triage | Rule/correlation driven | Playbook-driven (analyst-authored) | Autonomous (AI-led, always-on) |
| Investigation | Correlation; not attack-path centric | Depends on upstream telemetry | Native attack-path investigations |
| Integrations | Require ongoing upkeep | Require ongoing upkeep | Self-healing (reduced break/fix) |
| Incident response | Separate SOAR component | Built-in case management | AI-driven remediation + approvals |
Here’s how the operating model differs:
‘Dynamic playbooks instead of static scripts. Morpheus generates automation from live alert context. When an alert fires, the platform builds an investigation path based on what’s actually present in your environment, not what someone pre-scripted six months ago.
Self-healing integrations. When APIs drift or detection logic changes, Morpheus adapts without requiring your team to patch connectors. The integration drift tax that consumed your engineers’ Fridays goes away.
Investigation, not just enrichment. Morpheus investigates like an elite analyst: correlating across your stack, building attack paths, validating hypotheses, and producing evidence-backed case narratives.
Controlled autonomy with guardrails. Autonomous doesn’t mean ungoverned. Morpheus routes high-impact actions through approval gates, logs every decision for audit, and produces YAML playbooks you can inspect. The platform does the work; your team retains control.
The practical difference shows up in your queue. Instead of analysts triaging, enriching, and escalating, they’re validating conclusions and approving response actions. Instead of maintaining playbooks, your engineers are focusing on strategic initiatives.
We’ve written extensively about how this compares to traditional SOAR in Morpheus (AI SOC) vs. Traditional SOAR. The short version: it’s not a better SOAR. It’s a different category.
What migration to Morpheus looks like
If you’ve been burned by platform migrations before, you’re right to be skeptical. Here’s how Morpheus handles the transition:
No playbook rebuilding. Because Morpheus generates automation from live data, you don’t need to recreate your QRadar SOAR playbooks. Connect your alert sources (CrowdStrike, Sentinel, Splunk, whatever you’re running), and Morpheus starts generating investigations immediately. Your existing detection logic stays in place.
800+ integrations. We support the tools you’re already using. The platform connects via CI/CD pipelines and version control with GitHub, so your security engineering workflows don’t need to change.
Run alongside your existing stack. You don’t need a big-bang cutover. Morpheus can operate in parallel with your current SOAR during transition, giving your team time to validate outcomes before fully switching over.
Transparent logic. Every investigation produces open YAML playbooks and visible reasoning. If you need to understand why Morpheus made a particular call, you can inspect the logic. No black boxes.
Questions to ask any vendor (including us)
Whether you’re evaluating Morpheus, XSIAM, or any other platform, these questions will help you separate marketing from operational reality:
1. Will I need to rebuild static playbooks, or does automation generate dynamically from alert context?
2. Who maintains integrations when vendor APIs change—my team or the platform?
3. Can I run this alongside my existing stack during transition, or does it require rip-and-replace?
4. Does “AI” mean a chatbot copilot that suggests actions, or actual autonomous investigation that produces conclusions?
5. What happens to the workflows I’ve already built—are they portable or stranded?
6. What does the audit trail look like for regulators and leadership?
7. Am I solving my playbook maintenance problem, or just relocating it to a new vendor?
If you’re going through the pain of migration anyway, you might as well come out the other side with a fundamentally better operating model.
When platforms sunset, assumptions should too
QRadar SOAR’s sunset is a rare chance to step back and ask whether it was ever delivering what your SOC actually needed.
You can use this moment to leapfrog to autonomous security operations, where every alert gets investigated, every decision is explainable, and every action is governed.
If you’re facing a QRadar SOAR renewal or migration decision, we’d rather show you than tell you. Request a demo, bring your own alert data, and see what changes when investigation happens at machine speed without adding a maintenance burden to your team.




