The AI-Autonomous SOC for High-Tech Companies
How D3 Morpheus ingests and triages, then investigates and escalates security alerts with AI-autonomous intelligence purpose-built for the cloud-native environments, SaaS supply chains, source code…
How D3 Morpheus ingests and triages, then investigates and escalates security alerts with AI-autonomous intelligence purpose-built for the cloud-native environments, SaaS supply chains, source code…
How D3 Morpheus ingests and investigates security alerts with AI-autonomous intelligence purpose-built for the regulatory demands and NERC CIP compliance requirements facing U.S. electric utilities.
How D3 Morpheus ingests, triages, investigates, and escalates security alerts using AI-autonomous intelligence built for the regulatory demands and patient safety requirements of U.S. healthcare…
Filter by Type:
Search Resources:

How D3 Morpheus ingests and triages, then investigates and escalates security alerts with AI-autonomous intelligence purpose-built for the cloud-native environments, SaaS supply chains, source code…
How D3 Morpheus ingests and investigates security alerts with AI-autonomous intelligence purpose-built for the regulatory demands and NERC CIP compliance requirements facing U.S. electric utilities.
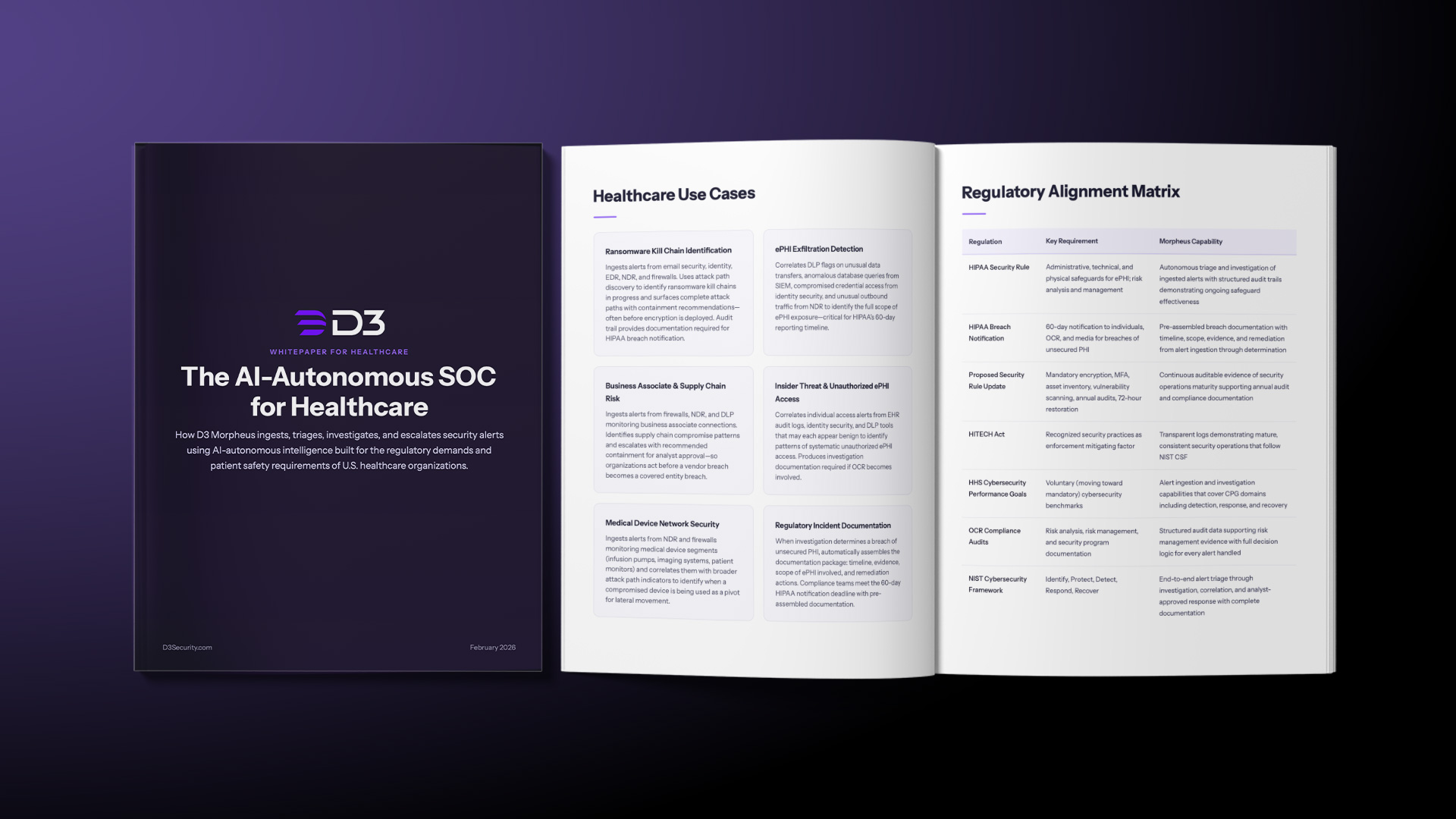
How D3 Morpheus ingests, triages, investigates, and escalates security alerts using AI-autonomous intelligence built for the regulatory demands and patient safety requirements of U.S. healthcare…

How D3 Morpheus ingests, triages, investigates, and escalates security alerts with AI-autonomous intelligence built for the intellectual property protection, regulatory complexity, and operational technology demands…

We tested D3 Morpheus AI against Microsoft Security Copilot across three real attack scenarios. Morpheus found root cause in all three. Copilot found it in…

How D3 Morpheus lets MSSPs run AI-driven and deterministic SOC operations from a single multi-tenant instance with per-client AI governance.

Stop investigating alerts in isolation. A technical guide to Attack Path Discovery, separating vertical privilege escalation from horizontal lateral movement using specialized LLMs.

Watch our on-demand workshop on how to safely automate Tier 1 and 2 SOC investigations with AI-driven autonomy and policy guardrails

A blueprint for autonomy you can control. Learn how to blend deterministic precision with cognitive scale to autonomously triage 95% of alerts.