Mythos Vulnerability Triage: EU Regulatory Comparison
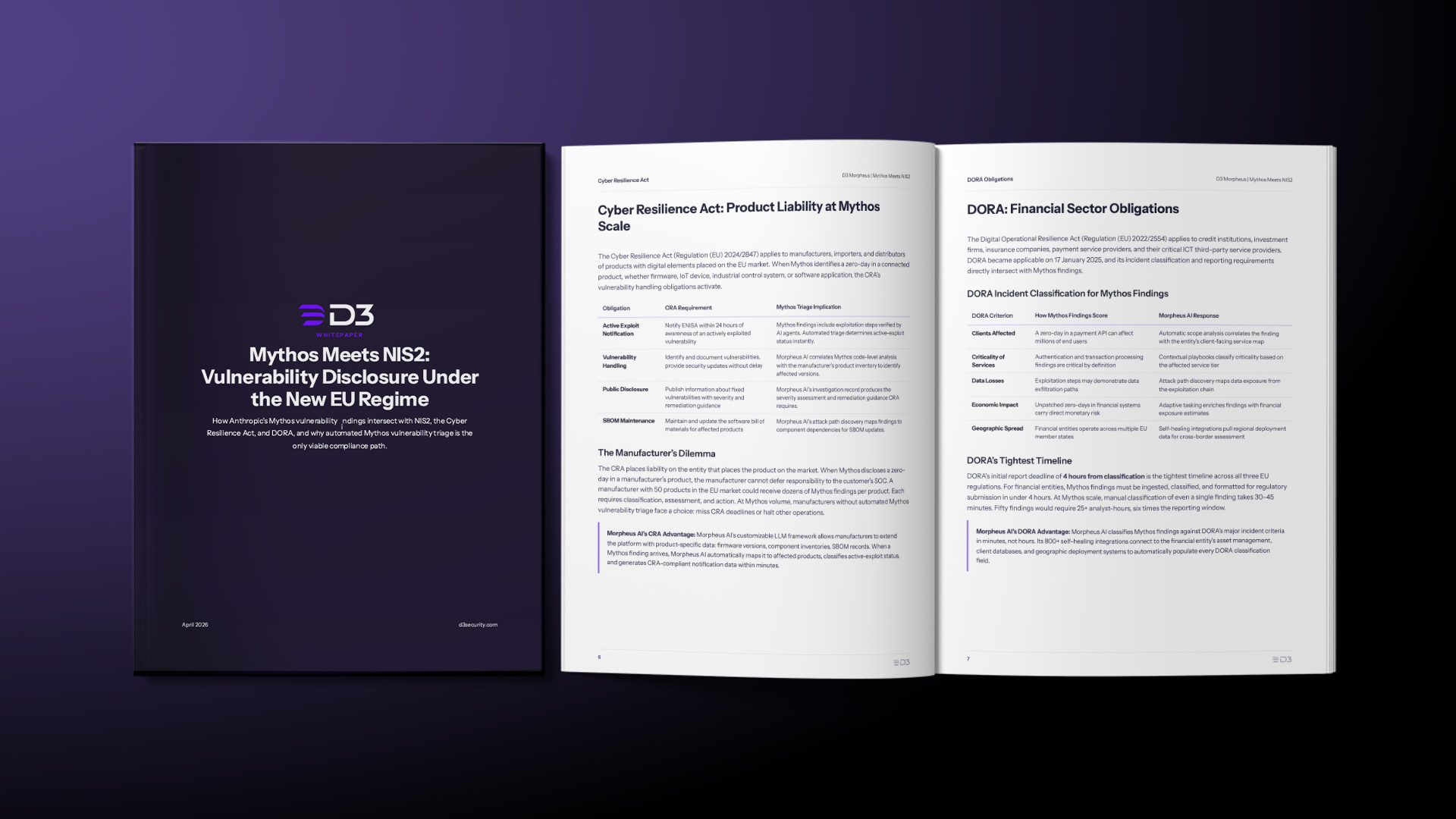
Compare how NIS2, the Cyber Resilience Act (CRA), and DORA each handle Mythos vulnerability findings. Automated Morpheus AI triage is the only viable compliance path.
Compare how NIS2, the Cyber Resilience Act (CRA), and DORA each handle Mythos vulnerability findings. Automated Morpheus AI triage is the only viable compliance path.
Anthropic’s Mythos will flood SOCs with zero-days. See why manual triage breaks, and how Autonomous Mythos Response handles every finding
How Anthropic’s Mythos AI zero-day discovery triggers NIS2 reporting obligations. Learn triage timelines, Article 20 liability, and Morpheus automation
Filter by Type:
Search Resources:

Compare how NIS2, the Cyber Resilience Act (CRA), and DORA each handle Mythos vulnerability findings. Automated Morpheus AI triage is the only viable compliance path.
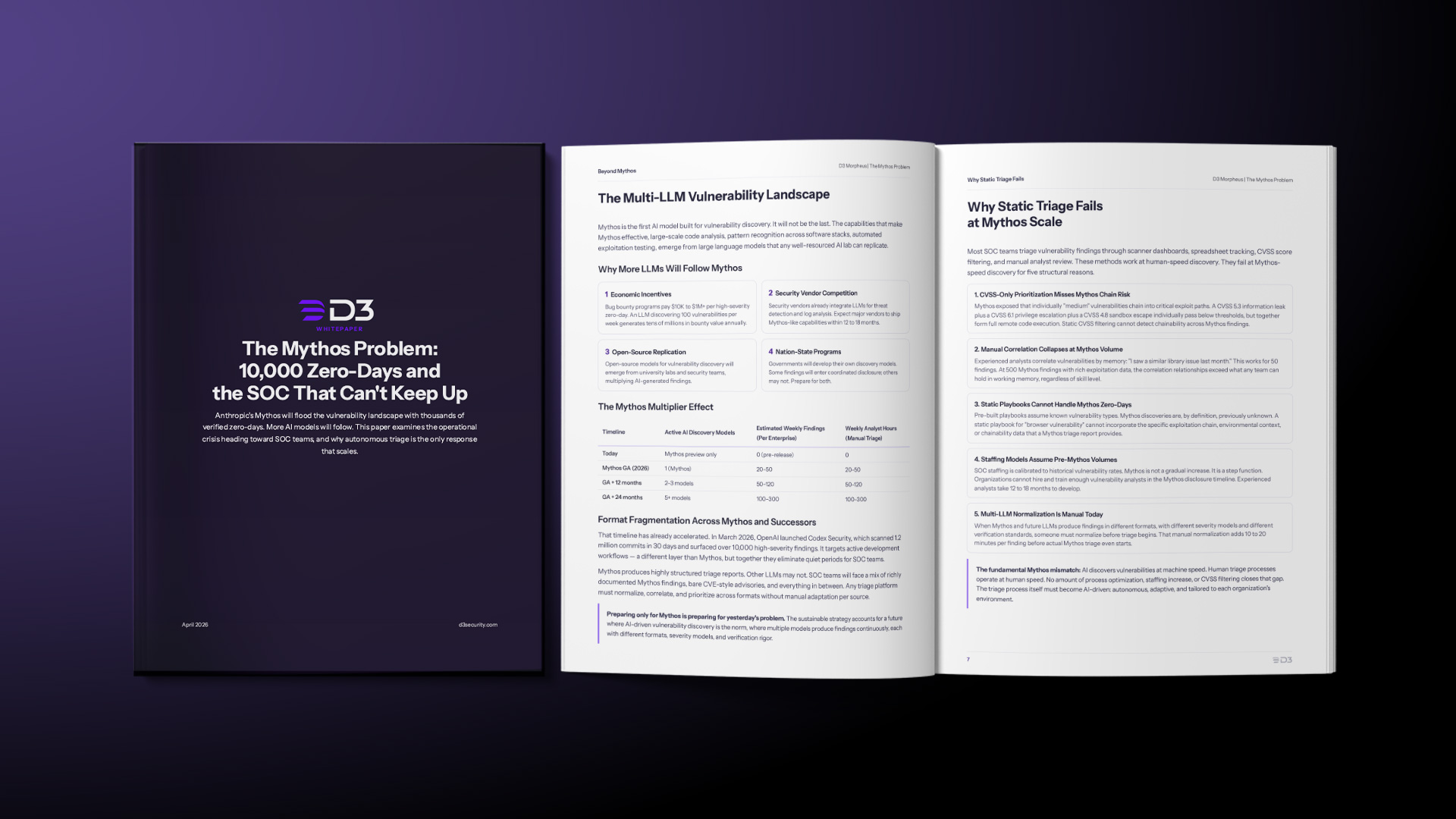
Anthropic’s Mythos will flood SOCs with zero-days. See why manual triage breaks, and how Autonomous Mythos Response handles every finding
How Anthropic’s Mythos AI zero-day discovery triggers NIS2 reporting obligations. Learn triage timelines, Article 20 liability, and Morpheus automation
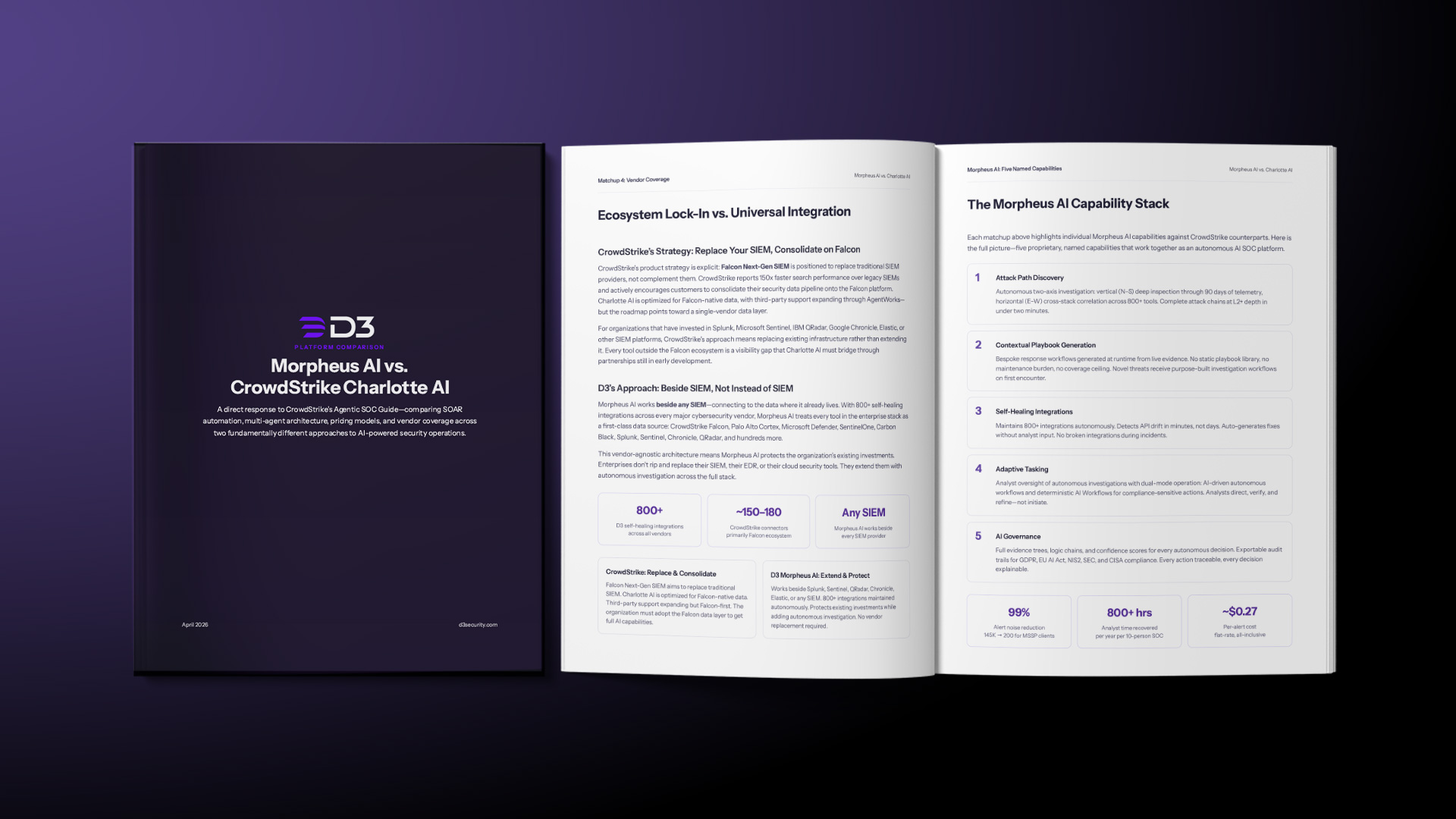
Get the whitepaper comparing D3 Morpheus AI and CrowdStrike Charlotte AI on SOAR, investigation depth, pricing, and 800+ self-healing integrations.
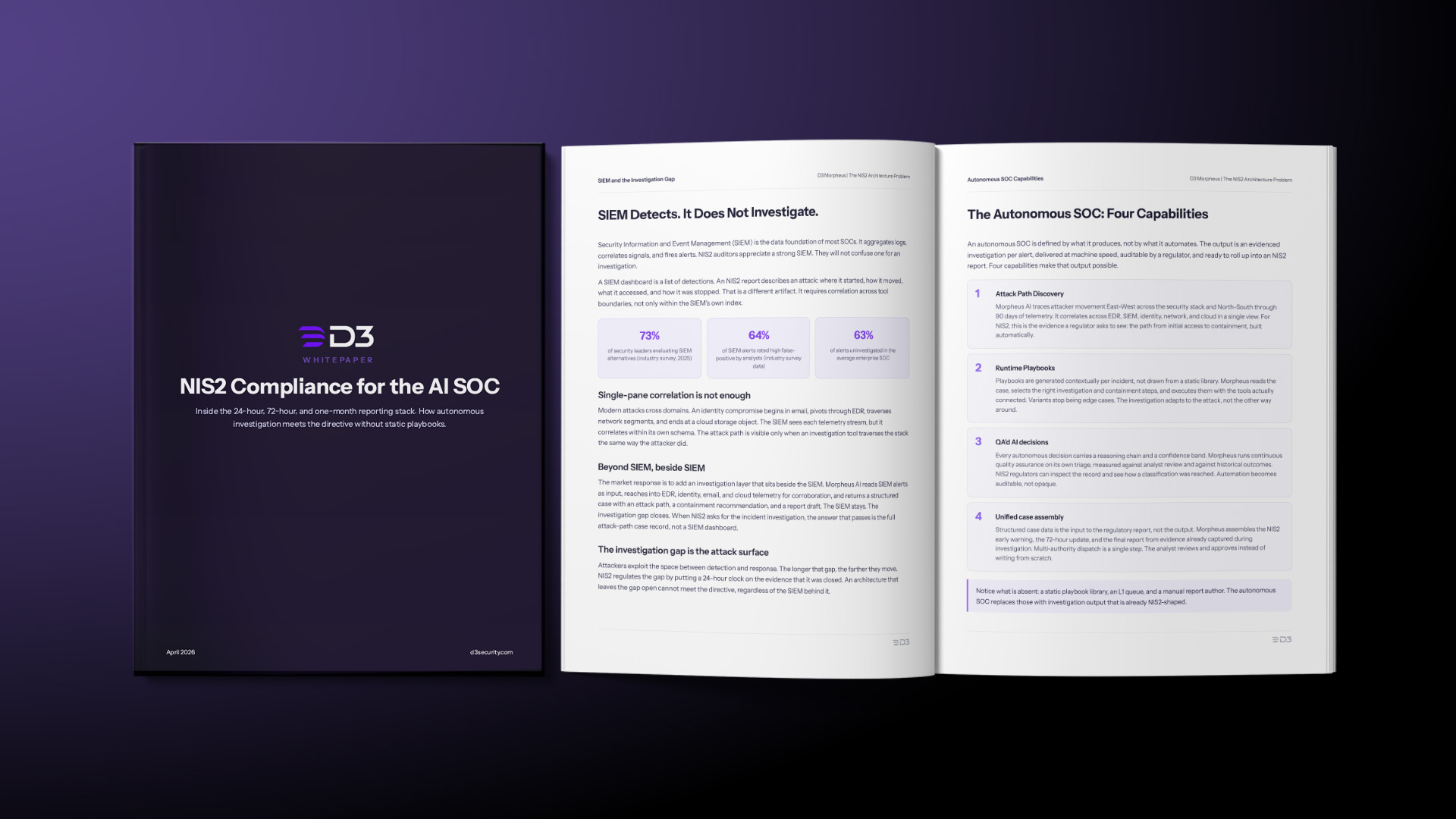
Learn how to meet EU NIS2 requirements with AI-driven SOC strategies, streamline 24 to 72 month reporting, and strengthen cyber resilience.

SOCs face 4,400+ daily alerts and investigate only 37%. Learn how autonomous AI investigation eliminates the SIEM alert fatigue bottleneck without replacing your SIEM.
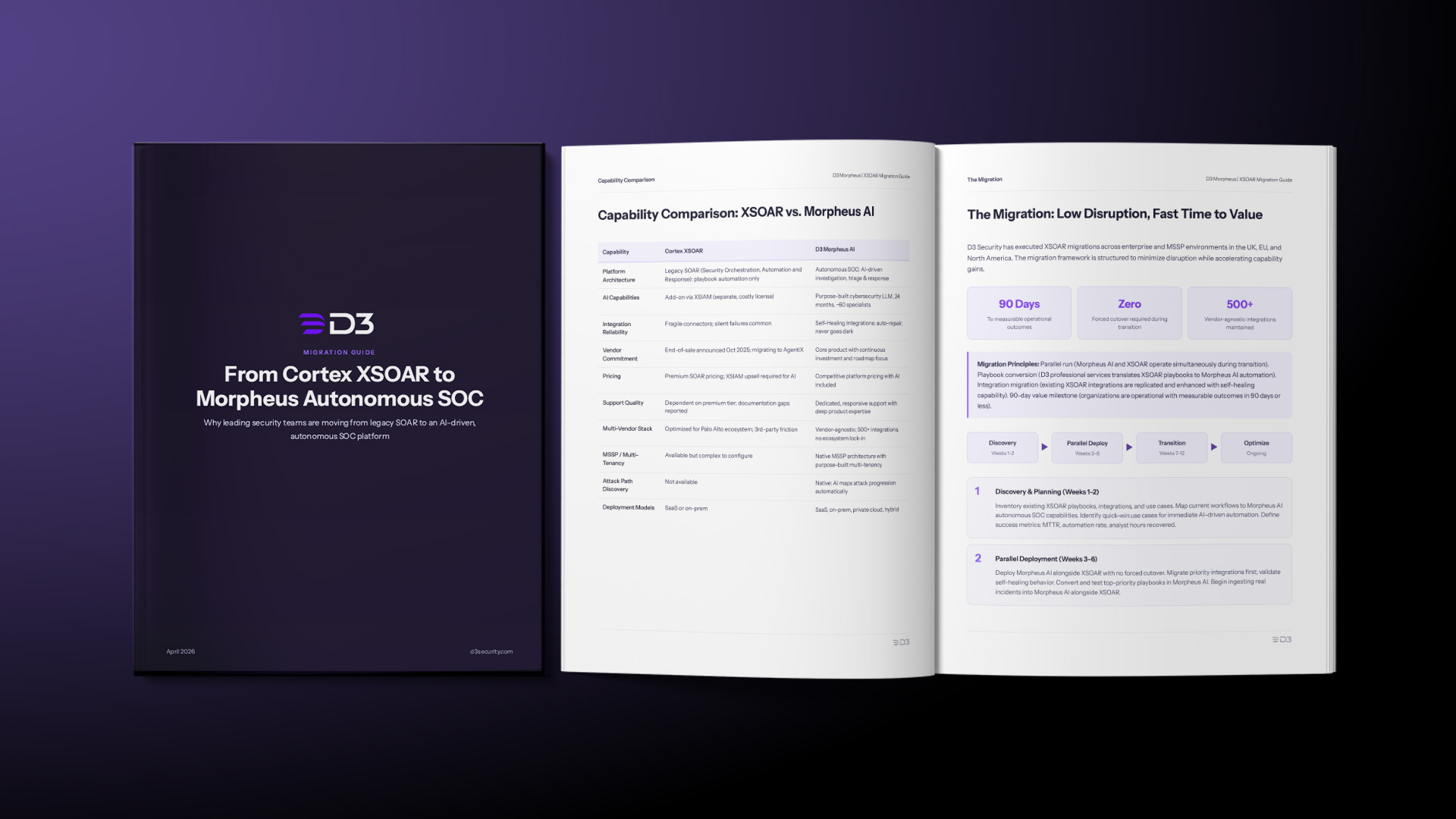
Why leading security teams are moving from legacy SOAR to an AI-driven, autonomous SOC platform. Includes a capability comparison, 90-day migration framework, and customer outcomes.
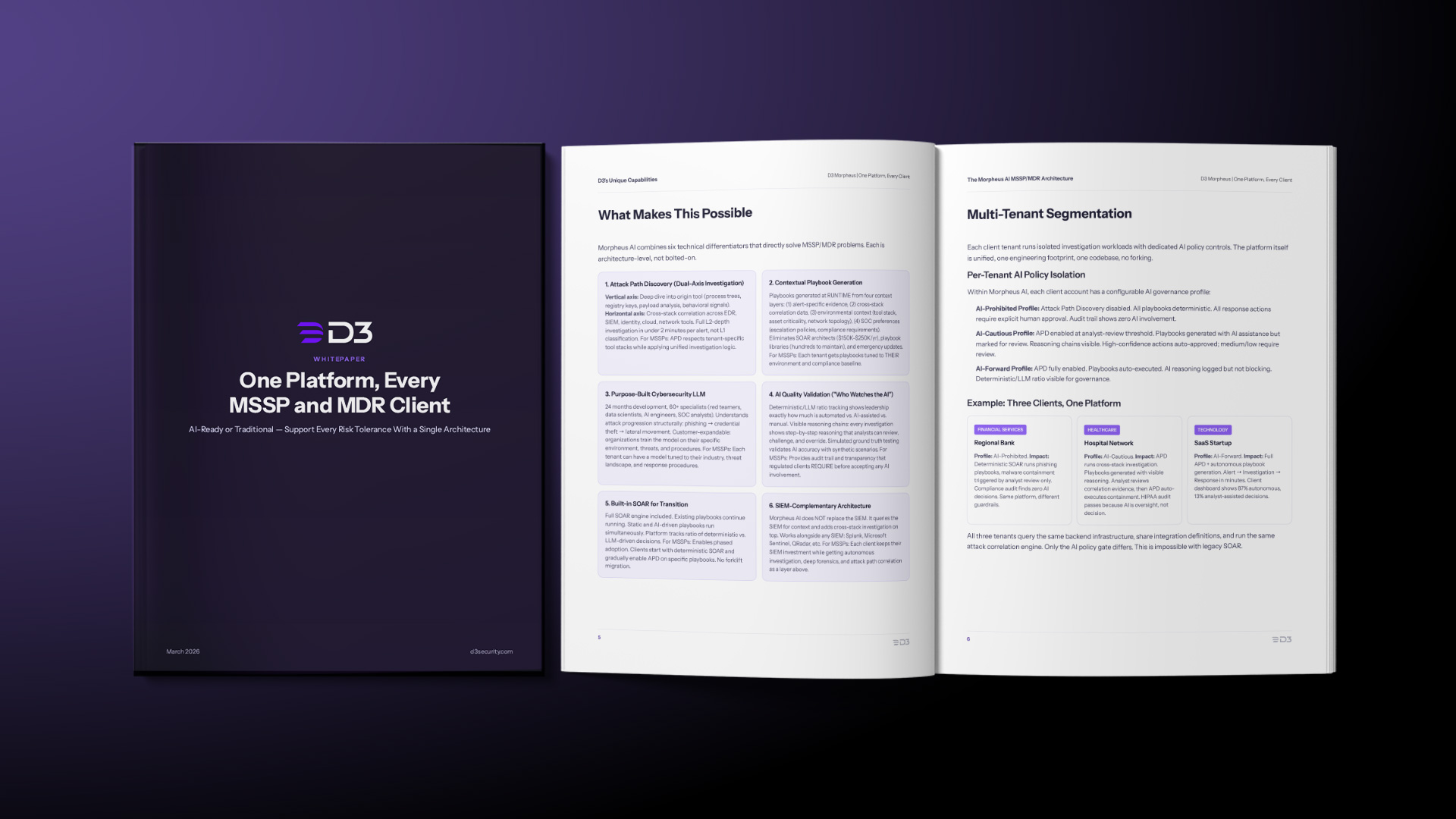
Legacy SOAR forces MSSPs to choose one AI model for all clients. Morpheus AI enables per-tenant AI governance with Attack Path Discovery, contextual playbook generation,…
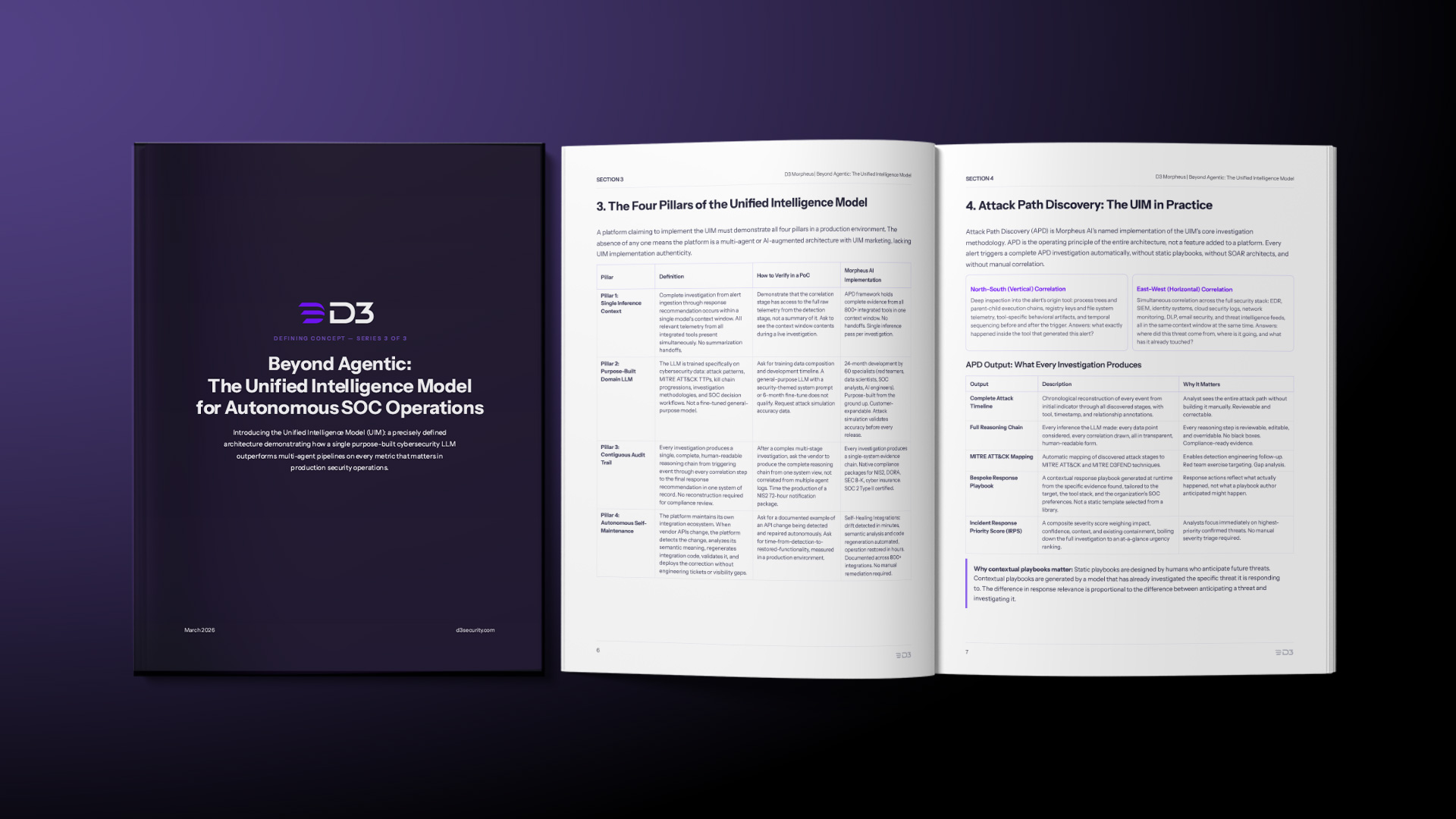
D3 Security introduces the Unified Intelligence Model (UIM) as a precisely defined architecture for autonomous SOC operations, with testable properties that distinguish it from multi-agent…