Platform Comparison
D3 Morpheus AI vs. Microsoft Sentinel + Logic Apps
Why a SIEM plus iPaaS plus Copilot stack is not an AI SOC Platform. Compare Morpheus AI, the AI SOC Platform that sits beside Sentinel and delivers autonomous alert investigation and accountable response. One engine. One trail. No fleet of agents.
See Morpheus AI Investigate Your Alerts
Executive Summary
Choose Morpheus AI if you need autonomous alert investigation and accountable response beside your existing SIEM. D3 Morpheus AI is an AI SOC Platform that delivers autonomous alert investigation and accountable response on one reasoning engine, with one audit trail across every tool in the stack. Microsoft Sentinel is a cloud-native SIEM and detection platform. To attempt investigation and response on top of it, the Microsoft stack adds Security Copilot (chat-driven assistant) and Azure Logic Apps (generic iPaaS workflow runtime), three products the analyst has to stitch together.
The critical difference: Morpheus AI triages up to 95% of alerts at L2+ depth in under 2 minutes, generates playbooks from live evidence, runs across 800+ integrated tools, and executes the four autonomy tiers under one audit trail. Sentinel detects. Copilot answers questions inside Defender. Logic Apps runs analyst-authored workflows. Investigation, orchestration, and accountable response have to be bridged by the analyst.
Why a SIEM + iPaaS + Copilot Stack Isn’t Enough
Sentinel is a capable SIEM. Detection, log aggregation, and compliance reporting are real strengths. The problem is what happens after an alert fires. The Microsoft answer is to stack Sentinel with Security Copilot and Azure Logic Apps and ask the analyst to bridge the gaps:
- No autonomous investigation: Security Copilot answers analyst questions inside the Defender ecosystem. It does not investigate alerts on its own or reconstruct kill chains without being prompted.
- Analyst-authored workflows: Logic Apps executes only the sequences your engineers pre-build. Every new attack variation forces new workflow engineering.
- Three products, three meters: Sentinel charges per GB ingested. Security Copilot charges per Security Compute Unit. Logic Apps charges per execution. Each layer accrues independently and the analyst still has to stitch them together.
- Defender-bound scope: Security Copilot operates inside Microsoft-managed data. Investigation across non-Microsoft EDR, CMDB, threat feeds, and legacy infrastructure requires manual forensics or third-party tools.
- iPaaS, not investigation: Logic Apps is a generic workflow runtime. It has no reasoning about alert context, no kill chain reconstruction, and no Attack Path Discovery across the stack.
- No unified audit trail: Sentinel, Copilot, and Logic Apps each keep their own logs. There is no single record of what was investigated, what was decided, who approved it, and what ran.
Morpheus AI solves all of this. Because autonomous alert investigation, orchestration, and accountable response are built on one reasoning engine with one audit trail, Morpheus AI sits beside Sentinel and queries it as a critical data source. The Microsoft investment stays. The analyst stops being the bridge.
Morpheus AI Capabilities the Microsoft Stack Cannot Match
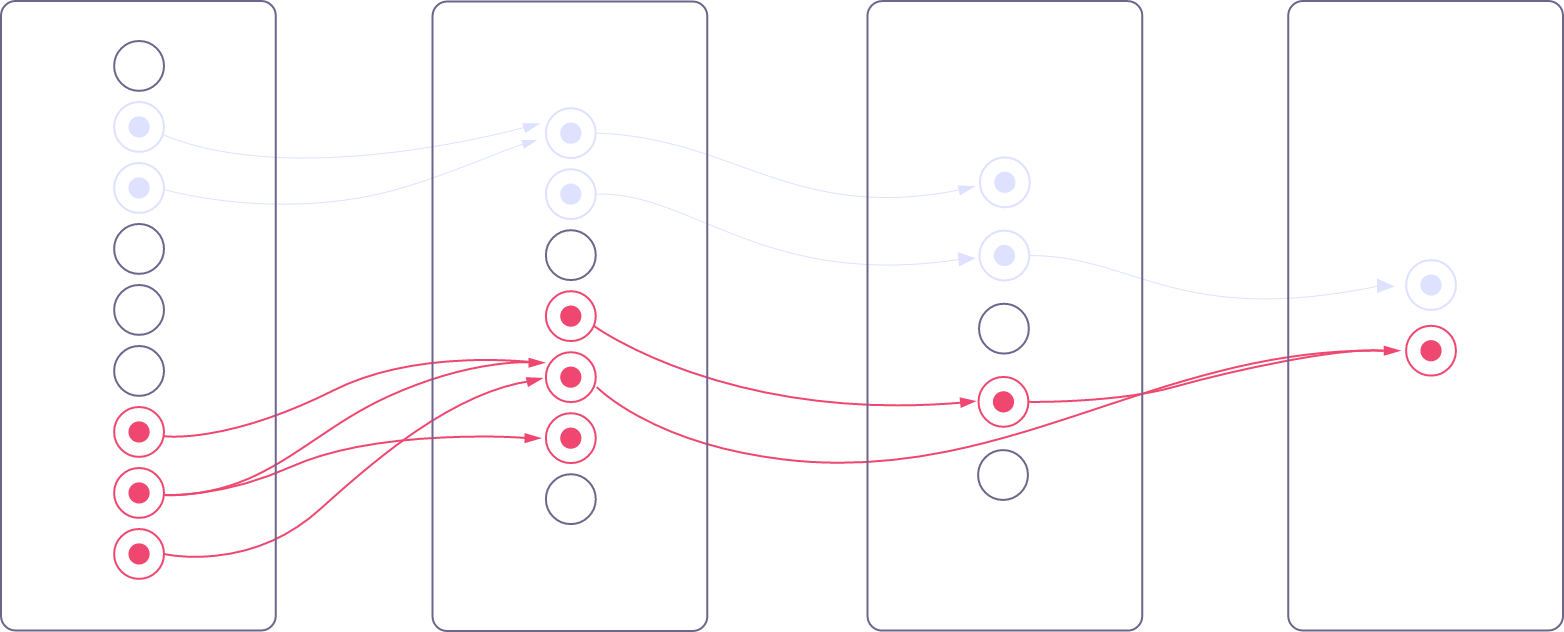
Six capabilities sit at the core of Morpheus AI’s architecture: beside-any-SIEM design, Attack Path Discovery across 800+ tools, runtime Contextual Playbook Generation, Autonomous Investigation, the Cybersecurity Triage Reasoning Graph, and four autonomy tiers under one audit trail. The Microsoft stack of Sentinel, Security Copilot, and Logic Apps is not designed to deliver them.
Beside Any SIEM (No SIEM Lock-In)
Morpheus AI sits beside Sentinel, Splunk, Sumo Logic, Elastic, or any other SIEM and queries it as a critical data source. Investment in Sentinel stays. Investigation and response move to a platform purpose-built for both. Security Copilot is bound to the Defender ecosystem, so investigation scope ends at Microsoft-managed data.
Attack Path Discovery (Across 800+ Tools)
Morpheus AI maps N-S (external-to-critical) and E-W (lateral) attack paths on every alert using MITRE ATT&CK references, then correlates across 800+ integrated tools, not just SIEM data. Sentinel correlates inside its own ingest. Security Copilot reasons only over Defender-managed assets. Lateral movement and cross-stack chains stay hidden.
Contextual Playbook Generation (Runtime, Not Analyst-Authored)
Morpheus AI generates playbooks from live evidence at runtime. Each playbook is specific to the attack, the customer’s environment, and available tools. Logic Apps executes only sequences your engineers pre-authored, so every new attack variation requires new workflow engineering.
Autonomous Investigation (Not Assistive AI on SIEM Data)
Morpheus AI investigates without being prompted. Alert fires, evidence is gathered, the kill chain is reconstructed, and the response is generated. Security Copilot is an analyst-initiated assistant; it answers questions the analyst already knows to ask. Logic Apps has no reasoning at all.
Cybersecurity Triage Reasoning Graph
Morpheus AI runs on the Cybersecurity Triage Reasoning Graph, D3’s proprietary reasoning system built over 24 months by 60 security specialists. The graph encodes attack patterns, tool integration syntax, evidence chains, and escalation logic across the SOC lifecycle. The graph is the moat. The underlying reasoning model is interchangeable. Sentinel and Security Copilot rely on Microsoft-hosted models without this purpose-built reasoning substrate.
Four Autonomy Tiers, One Audit Trail
Morpheus AI operates across four autonomy tiers (Deterministic, AI-Assisted, AI-Led, Autonomous) on one reasoning engine, gated by per-action approval policy and recorded on one audit trail. Regulated buyers get credible autonomy, not reckless autonomy. The Microsoft stack offers a chat assistant (Copilot) and a workflow runtime (Logic Apps); neither delivers tiered autonomy across one engine. See d3security.com/morpheus/autonomy-modes/.
Feature Comparison: Morpheus vs. Microsoft Sentinel + Logic Apps
Morpheus AI is the AI SOC Platform that sits beside Sentinel. The Microsoft stack is a SIEM, a chat assistant, and a generic iPaaS workflow runtime. The table below shows what each side delivers.
| Capability | D3 Morpheus AI | Microsoft Sentinel + Logic Apps |
|---|---|---|
| Alert Investigation | Up to 95% in <2 min (L2+ quality) | Detection only; Copilot answers analyst queries |
| Attack Path Discovery (N-S + E-W) | Every alert | Manual forensics; no autonomous reconstruction |
| Contextual Playbook Generation | Runtime from live evidence | Logic Apps: analyst-authored workflows only |
| Orchestration & Remediation Engine | Built-in (800+ tools) | Logic Apps (generic iPaaS); no native investigation |
| Triage component | Cybersecurity Triage Reasoning Graph (24 months / 60 specialists) | Microsoft-hosted Copilot model; no purpose-built SOC reasoning substrate |
| Autonomous Self-Healing | Verify & retry | Manual workflow repair when APIs drift |
| Integrated Tool Ecosystem | 800+ self-healing integrations | Defender ecosystem first; non-Microsoft tools via Logic Apps connectors |
| Autonomy Spectrum | Four tiers, one engine, one audit trail | Chat assistant + workflow runtime; no tiered autonomy |
| Governance & Explainability | Evidence trees, logic chains, confidence scores — supports GDPR, EU AI Act, NIS2, SEC, CISA | Sentinel audit logs; no unified investigation evidence chain |
| MTTR (Mean Time to Remediation) | 80% reduction | Variable; gated by workflow engineering capacity |
| Single-Vendor Solution | Investigation + Orchestration + Remediation | Three products to stitch together (SIEM + Copilot + iPaaS) |
| Pricing Model | Platform Subscription + User Licenses | Sentinel per GB ingested; Copilot per Security Compute Unit; Logic Apps per execution |

Request your free Microsoft Sentinel cost comparison
WHY MORPHEUS
Why SOC Teams Choose Morpheus AI

Complete Platform, No Fragmentation
One AI SOC Platform, one API, one training program. Morpheus AI sits beside Sentinel and queries it as a critical data source, so detection, log aggregation, and compliance reporting stay where they already work. Investigation, orchestration, and accountable response move onto one reasoning engine with one audit trail. The analyst stops being the bridge between Sentinel, Copilot, and Logic Apps.
80% Faster Remediation
Attacks are stopped in minutes, not hours. Because playbooks are generated from live evidence and executed through 800+ integrated tools without manual handoffs, adversaries do not get a second shot. MTTR improves by 80% versus a SIEM-plus-Logic-Apps workflow that depends on engineering capacity to keep up with new attack variations.

7,800 Analyst Hours Saved Annually
Per 1,000 alerts, Morpheus AI eliminates the busywork of triage, playbook writing, orchestration planning, and post-incident forensics. Analysts focus on strategic threats, not alert fatigue and Logic Apps workflow maintenance.

99% False Positive Elimination
Morpheus AI’s contextual investigation cuts false positives to 1%. Analysts investigate actual attacks and escalate with context, not hunches. Sentinel correlation rules trigger volume; Morpheus AI determines which of those alerts deserve attention.
Lower Total Cost of Ownership
Morpheus AI uses a subscription pricing model. The customer pays a Platform Subscription plus User Licenses that together form the Expected Cost of running an AI SOC. The model is designed to absorb the operational cost of token consumption and AI compute internally rather than passing it through as a usage meter. By contrast, the Microsoft stack runs three meters in parallel: Sentinel per GB ingested, Security Copilot per Security Compute Unit, and Logic Apps per execution. Each layer accrues independently, and you still need an investigation platform on top. One platform, one budget line. Visit d3security.com/morpheus/pricing/ for details.
Bounded Reasoning, Customer-Extensible
Morpheus AI operates inside bounded reasoning under deterministic governance. The Cybersecurity Triage Reasoning Graph stays the moat; the underlying reasoning model is interchangeable. Your organization can extend the graph with environment-specific patterns, tools, and escalation logic. Security Copilot is tied to Microsoft’s roadmap and the Defender data boundary.
Morpheus Performance Metrics at a Glance
Real-world data from live Morpheus deployments:
Frequently Asked Questions
Does Morpheus AI replace Microsoft Sentinel?
No. Morpheus AI sits beside Sentinel. Sentinel handles detection, log aggregation, and compliance reporting. Morpheus AI handles autonomous alert investigation and accountable response across Sentinel data and 800+ other integrated tools. Together, they form a complete AI SOC. Morpheus AI queries Sentinel as a critical data source, so your existing SIEM investment stays valuable.
Why is a SIEM + iPaaS + Copilot stack not enough?
Sentinel detects. Logic Apps executes pre-authored workflows. Security Copilot answers analyst questions inside the Defender ecosystem. None of the three investigate autonomously, reconstruct kill chains on their own, or generate playbooks from live evidence. The analyst still has to bridge investigation, orchestration, and response across three products, three meters, and three audit logs. Morpheus AI delivers autonomous alert investigation and accountable response on one reasoning engine with one audit trail, beside whatever SIEM you already own.
How does Morpheus AI work alongside the Microsoft stack?
Morpheus AI queries Sentinel as a critical data source, then correlates across 800+ other tools through Self-Healing Integrations. You keep Sentinel for detection, compliance, and log aggregation. Morpheus AI handles investigation and response. D3 Security is a Microsoft Intelligent Security Association (MISA) member, and Morpheus AI is available on Azure Marketplace, purchasable with existing Azure committed spend (MACC). Zero new vendor procurement for Microsoft shops.
What is the Cybersecurity Triage Reasoning Graph, and how is it different from Security Copilot?
The Cybersecurity Triage Reasoning Graph is D3’s proprietary reasoning system, built over 24 months by 60 security specialists. It encodes attack patterns, tool integration syntax, evidence chains, and escalation logic across the SOC lifecycle. The graph is the moat; the underlying reasoning model is interchangeable. Security Copilot is an analyst-initiated chat assistant that operates on Microsoft-hosted models within the Defender data boundary, without this purpose-built SOC reasoning substrate. That is why Morpheus AI can investigate autonomously and Copilot cannot.
What are the four autonomy tiers and how do they differ from a chat assistant?
Morpheus AI runs across four autonomy tiers: Deterministic, AI-Assisted, AI-Led, and Autonomous. Each action is gated by per-action approval policy and recorded on one audit trail. Regulated buyers get credible autonomy, not reckless autonomy. Security Copilot is a single chat-driven assistant. Logic Apps is a single workflow runtime. Neither offers tiered governance across the same reasoning engine. Morpheus AI produces documentation for every autonomous decision: evidence trees, logic chains, and confidence scores. The artifacts support audit and reporting requirements under GDPR, EU AI Act, NIS2, SEC, and CISA. Every AI action is traceable and every decision is explainable. D3 Security is SOC 2 Type II certified and ISO 27001 certified. See d3security.com/morpheus/autonomy-modes/.
How does Morpheus AI pricing compare to Sentinel + Copilot + Logic Apps?
Morpheus AI uses a subscription pricing model, a Platform Subscription plus User Licenses that together form the customer’s Expected Cost. The model is designed to absorb the operational cost of token consumption and AI compute internally rather than passing it through as a usage meter. The Microsoft stack runs three meters in parallel: Sentinel charges per GB ingested, Security Copilot charges per Security Compute Unit, and Logic Apps charges per execution. Each layer accrues independently. See d3security.com/morpheus/pricing/ for details.
Ready to See Morpheus in Action?
Microsoft Sentinel is an excellent cloud-native SIEM. But a SIEM plus iPaaS plus Copilot stack is not an AI SOC Platform. See how Morpheus AI delivers autonomous alert investigation and accountable response beside Sentinel, on one reasoning engine with one audit trail.
About D3 Security
D3 Security is the maker of Morpheus AI, the AI SOC Platform that combines autonomous investigation, orchestration, and remediation on one reasoning engine with one audit trail. Founded in 2015, D3 is trusted by Fortune 500 enterprises, government agencies, and leading financial institutions.
Learn more: www.d3security.com
D3 Security is not affiliated with Microsoft. All trademarks are the property of their respective owners. This comparison reflects publicly available information and our team’s evaluation as of May 2026.