D3 Morpheus AI vs. Intezer
Autonomous AI SOC Platform Comparison: Attack Path Discovery, Investigation Breadth, Self-Healing Integrations, and Autonomous Response
See Morpheus AI in Action
The Fundamental Difference
Quick Answer: D3 Morpheus AI is an Autonomous AI SOC Platform that investigates 100% of alerts with L2+ depth in under 2 minutes, correlates attack paths across your entire infrastructure, and executes response automation. Intezer specializes in forensic malware analysis of individual alerts only—no cross-system correlation, no SOAR, no response automation.
D3 Morpheus AI is a full-stack Autonomous AI SOC Platform. For every alert, Morpheus automatically executes multi-dimensional attack path discovery—correlating alerts across EDR, SIEM, cloud, identity, and network systems simultaneously. It reconstructs the complete attacker progression (entry, privilege escalation, lateral movement, data access) in under 2 minutes, generates contextual playbooks with full Python code visibility, and executes remediation. Self-healing integrations monitor 800+ tools and autonomously repair API drift within minutes, maintaining 99.9%+ uptime with zero engineering overhead. Purpose-built cybersecurity LLM with 24 months of development and 60 domain specialists investigates all attack types.
Intezer is a forensic alert investigation platform specializing in malware analysis and code-level investigation. It combines multiple AI models with deterministic forensic methods: code analysis, sandboxing, reverse engineering, memory forensics. Claims 100% of alerts investigated in under 2 minutes with 98% accuracy. Escalates only ~4% of alerts with clear context and recommended actions. Strongest on malware and code analysis; narrows investigation scope to alert boundary without cross-system correlation.
In practice: A global MSSP using Morpheus AI reduced 144,000 monthly alerts to 200 requiring human review (99.86% reduction), recovered 7,800 analyst hours annually, and achieved 80% MTTR improvement. Morpheus AI’s investigation engine follows MITRE ATT&CK kill chain methodology to correlate attacker actions across systems and detect complete attack progression. Intezer accelerates malware investigation to ~2 minutes per alert with high accuracy but doesn’t correlate across systems, investigate identity-based attacks, or generate response automation. Morpheus investigates broader attack classes and includes full SOAR (Security Orchestration, Automation and Response); Intezer is investigation-only, requiring downstream SOAR integration.
COMPARE
Morpheus AI Capabilities Intezer Cannot Match
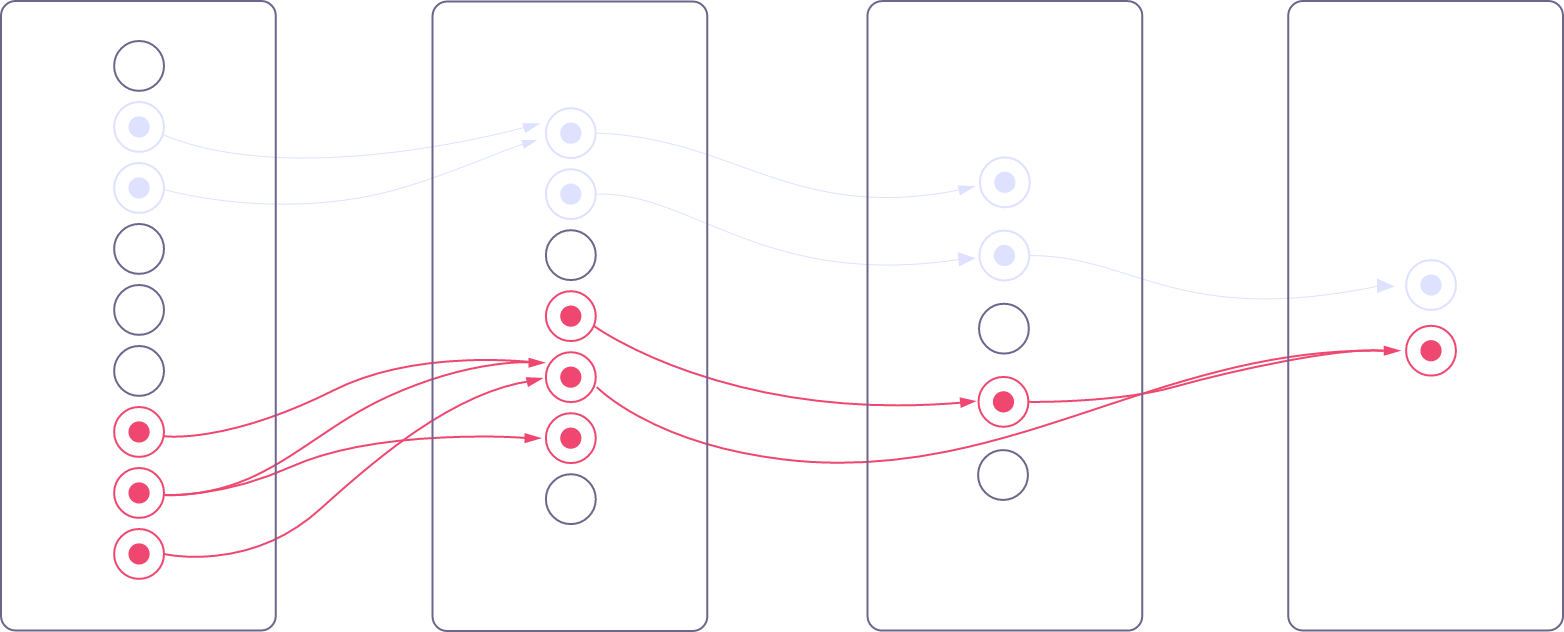
Attack Path Discovery: Cross-System Correlation Across Full Infrastructure
Multi-dimensional investigation combining north-south (process trees, registry modifications, file system forensics, memory analysis) with east-west (EDR, SIEM, cloud, identity, network correlation). Every alert produces a complete attack timeline: entry point, privilege escalation, lateral movement across systems, and data access pathways. Analysts see the full investigative reasoning and can override at any step. Automatically correlates events across 800+ tools: a file creation alert becomes a complete lateral-movement chain showing which systems were accessed and when.
Intezer: Not available. Specializes in code-level forensics on the alerted endpoint or artifact. Does not correlate across systems or build timelines of multi-stage attacks. Investigation boundary is the individual alert, not the attack sequence.
Self-Healing Integrations: 99.9%+ Uptime, Zero Manual Maintenance
Continuous health monitoring across 800+ tools. When API drift is detected (credential rotation, firewall rule change, endpoint offline, endpoint misconfiguration), Morpheus executes autonomous repair: (1) drift detection within minutes, (2) LLM-powered change analysis, (3) autonomous code regeneration, (4) attack path framework re-adaptation. Result: 99.9%+ integration uptime with zero engineering involvement. “Adding the 51st tool adds zero additional maintenance cost.” Engineering time reclaimed: 20-40% of integration maintenance budget, reallocated to development and threat hunting.
Intezer: Not available—standard API integrations. API changes require manual diagnosis and troubleshooting. Investigation blind spots occur during integration maintenance windows or credential rotation events.
Contextual Playbook Generation: Orchestration and Automation Included
Playbooks generated at runtime from investigation evidence, tailored to the specific attack. Ransomware payloads trigger isolation and decryption steps. Lateral movement triggers credential resets and network segmentation. Each playbook includes full Python code, is visible to analysts, can be modified in real-time, and executes on approval. Coverage is 100% on day one; no authoring, versioning, or maintenance required. Built-in SOAR engine handles orchestration, multi-step workflows, conditional logic, and third-party API calls.
Intezer: No playbook engine and no SOAR automation. Investigation yields recommended actions, but remediation is manual or requires downstream integration with a separate SOAR platform. Adds architectural complexity and tool sprawl.

Breadth of Attack Investigation: Beyond Malware to Full Attack Lifecycle
Investigates all attack types automatically: ransomware, lateral movement, privilege escalation, data exfiltration, zero-day exploits, fileless malware, supply-chain compromise, identity-based attacks (compromised credentials, session hijacking), and cloud misconfigurations. Purpose-built cybersecurity LLM understands attack progression natively across all vectors.
Intezer: Specializes in malware investigation—code analysis, sandboxing, reverse engineering, memory forensics. Strong on ransomware, malware variants, supply-chain binaries, and fileless malware detection. Narrower on identity attacks, cloud misconfigurations, lateral movement investigation, and attack classes that don’t involve executable code.

Purpose-Built Cybersecurity LLM: 24 Months Development, 60 Domain Specialists
A large language model built specifically for cybersecurity investigation from the ground up. 24-month development cycle. 60 domain specialists: red teamers, security data scientists, penetration testers, SOC analysts. Native understanding of attack progression: phishing → credential theft → lateral movement → exfiltration. Distinguishes benign administrative PowerShell from fileless malware indicators. Investigates zero-day exploits with full contextual reasoning. Expandable by customers to include proprietary attack signatures and organizational threat models.
Intezer: Uses multiple AI models combined with deterministic forensic methods. Strong pattern matching for known malware families and code similarity detection. Smaller scope: optimized for malware identification rather than cross-domain attack understanding. Less flexible for novel, unseen attack classes outside malware patterns.

Visible AI Governance: Transparent, Editable, Overridable Reasoning
Every decision—attack classification, path reconstruction, playbook generation, remediation recommendation—is transparent and reviewable. Analysts see the investigation logic, can edit findings in real-time, and can override AI recommendations. Hardening mechanism: patterns that prove reliable are converted from AI-assisted to deterministic code, creating a hybrid architecture that improves over time. 87% Attack Path Revelation Rate with deterministic/indeterministic architecture documented and auditable.
Intezer: Provides investigation reports and recommended actions, but governance transparency is limited. Less visibility into AI decision-making or mechanisms for analyst override and customization.
Feature Comparison Table
D3 Morpheus AI is the complete investigation and orchestration platform. Intezer is a forensic alert investigation tool. The table below shows what you get in each.
| Capability | Morpheus AI | Intezer |
|---|---|---|
| Investigation Model | Multi-dimensional attack path discovery (north-south + east-west correlation across 800+ tools) | Code-level forensic investigation and alert-level malware analysis |
| Investigation Scope | Full L2 investigation: entry, privilege escalation, lateral movement, data access, remediation across entire attack lifecycle | Individual alert investigation with malware focus; cross-system correlation not included |
| Investigation Time | Up to 95% triaged in under 2 minutes (L2-quality report with timeline, scope, remediation steps) | Under 2 minutes per alert (code analysis and malware determination) |
| Attack Path Discovery | Built-in, automatic for every alert. Process trees, registry keys, file system forensics, lateral movement, privilege escalation, cross-system correlation. 100% alert coverage. | Not available. Code analysis within single alert; no cross-system correlation or lateral movement timelines. |
| Malware Analysis Depth | Strong: reverse engineering, code analysis, sandboxing integrated into attack path discovery | Strongest area: code similarity, binary analysis, malware family classification, memory forensics |
| Identity Attack Investigation | Automatic: compromised credentials, session hijacking, privilege escalation via identity, cloud access abuse | Limited. Not a primary focus; requires manual investigation or downstream tools. |
| Cloud Misconfiguration Investigation | Automatic: AWS, Azure, GCP config analysis, RBAC violations, data exposure, cloud-native attack paths | Limited. Primary focus is endpoint malware, not cloud infrastructure investigation. |
| Playbook Automation | Contextual generation at runtime. Full Python code visible and modifiable. L2+ investigation depth. Built-in SOAR execution. | Not available—recommended actions only. Requires manual remediation or downstream SOAR integration. |
| SOAR Engine | Full SOAR built-in. Orchestration, automation, multi-step workflows, 800+ tool integration, conditional logic. | Not included—requires separate third-party SOAR platform for orchestration. |
| Self-Healing Integrations | 800+ tools, drift detection in minutes, 4-phase autonomous repair, 99.9%+ uptime, 30% SOC engineering time recovered | Standard integrations, manual troubleshooting required, no autonomous drift repair |
| False-Positive Reduction | 99% reduction in false-positive investigation time. Production: 144,000 → 200 alerts (99.86% reduction). 100% alert coverage. | ~4% escalation rate (96% of alerts triaged without escalation); still requires investigation of those 4% |
| MTTR Impact | 80% reduction (70 minutes manual → under 2 minutes automated, including response automation). L2+ investigation depth. | Improves investigation speed; full remediation MTTR depends on downstream processes and manual response |
| AI Architecture | Purpose-built cybersecurity LLM. 24-month development. 60 domain specialists: red teamers, data scientists, analysts. | Multiple AI models + deterministic forensic methods. Optimized for malware; smaller scope than full attack investigation. |
| Zero-Day & Novel Attacks | Yes. LLM understands attack progression natively. Handles unseen attack classes with contextual reasoning. | Limited. Pattern-based detection; novel attacks outside malware distribution struggle without code signature. |
| AI Governance | Transparent reasoning, editable, overridable, 87% APR. Deterministic/indeterministic hybrid. MITRE ATT&CK methodology integrated. | Reports provided; limited visibility into AI decision-making and override mechanisms. |
| Integration Breadth | 800+ tools with self-healing: SIEM, EDR, cloud (AWS, Azure, GCP), identity, network, threat intelligence, ticketing | File scanning, sandboxing, URL scanning, memory forensics, interactive browsing; narrower ecosystem breadth |
| Multi-Tenancy & MSSP | Full multi-tenant support with complete isolation, 100% alert coverage per tenant | Limited MSSP capabilities |
| Pricing Model | Flat-rate subscription: Platform + Licenses. No per-alert, per-user, or token fees. D3’s AI cost: $0.27/triaged alert (absorbed by D3, not charged to customers) vs. ~$2.50/alert for human L2 triage. | Fixed pricing regardless of alert volume. No per-alert fees, but narrower platform scope (investigation only, no SOAR). |
| Time to Value | Day-one full investigation coverage for all attack types with L2+ depth. 100% alert coverage, 100% automation ready. | Immediate deployment for malware triage; requires tuning and downstream tool integration for SOAR/orchestration. |

Request your free Intezer cost comparison
Why SOC Teams Switch to Morpheus AI
| Reason | Details |
|---|---|
| Full-Stack Platform Beats Tool Sprawl | Intezer covers malware investigation; Morpheus covers all attack types plus response automation. Separate investigation tool + separate SOAR + separate SIEM creates integration debt and alert routing complexity. Morpheus AI consolidates investigation and SOAR in one platform with unified data context. Engineering time spent on tool integration is freed for threat hunting and detection engineering. |
| Attack Path Discovery: Investigation Beyond Malware | Malware analysis is critical but represents 30-40% of real-world attacks. Identity attacks, cloud misconfigurations, and lateral movement require cross-system investigation. Morpheus AI automatically discovers lateral movement, privilege escalation, and multi-stage attacks. Intezer’s code-centric approach misses non-malware attack progression. |
Frequently Asked Questions
What can Morpheus AI do that Intezer cannot?
D3 Morpheus AI automatically investigates complete attack paths using multi-dimensional correlation (north-south + east-west), generates contextual playbooks with full Python code at runtime, detects and repairs integration drift in minutes (99.9%+ uptime), investigates all attack types with a purpose-built cybersecurity LLM, and includes full SOAR automation. Intezer specializes in malware investigation and triage—it does not correlate across systems, does not generate playbooks, and does not include SOAR automation.
Does Morpheus AI include a SOAR engine?
Yes. D3 Morpheus AI includes a full SOAR engine built directly into the platform. Contextual playbooks are generated at runtime and executed automatically on analyst approval. Intezer does not include SOAR; remediation and orchestration require a separate third-party platform.
How does Morpheus AI pricing compare to Intezer?
D3 Morpheus AI uses a flat-rate subscription model: Platform Subscription + User Licenses with no per-alert charges, no per-user fees, no token fees, and no investigation caps. D3 absorbs all AI token costs. Intezer also uses fixed pricing regardless of alert volume (not per-alert), which is similar in structure. However, Morpheus AI includes investigation, response automation, and SOAR in one platform; Intezer is investigation-only and requires a separate SOAR platform for orchestration. See d3security.com/morpheus/pricing/ for details.
What is attack path discovery and why doesn’t Intezer have it?
Attack path discovery reconstructs the complete sequence of attacker actions across your entire infrastructure: process execution, registry modifications, file system changes, privilege escalation, lateral movement between systems, and data access. D3 Morpheus AI combines north-south investigation (single-system telemetry) with east-west investigation (cross-system correlation across EDR, SIEM, cloud, identity, network). Result: forensic-grade timelines showing how an attacker moved from initial access to data exfiltration, all in under 2 minutes. Intezer investigates individual alerts with code-level forensics but does not correlate across systems or provide attack progression context.
Can Morpheus AI replace both Intezer and my existing SOAR?
Yes. D3 Morpheus AI combines AI-powered investigation (including malware analysis integrated into broader attack path discovery), contextual playbook generation, and full SOAR automation in one platform. It eliminates the need for separate investigation or SOAR tools. Intezer is investigation-only and cannot replace SOAR; it requires a separate SOAR platform for any orchestration or automation beyond malware investigation.
How does Morpheus AI handle integration maintenance?
D3 Morpheus AI uses self-healing integrations across 800+ tools. The platform continuously monitors API health and detects drift within minutes. When drift occurs, Morpheus executes autonomous repair: (1) drift detection, (2) LLM-powered change analysis, (3) code regeneration, (4) attack path framework re-adaptation. Result: 99.9%+ uptime with zero manual engineering overhead. Intezer uses standard API integrations that require manual troubleshooting when endpoints fail or credentials rotate.
What types of attacks does Morpheus AI investigate automatically?
D3 Morpheus AI investigates all attack types: ransomware, lateral movement, privilege escalation, data exfiltration, zero-day exploits, fileless malware, supply-chain compromise, identity-based attacks, and cloud misconfigurations. Its purpose-built cybersecurity LLM understands attack progression natively across all vectors. Intezer is strongest on malware and code analysis (ransomware, malware variants, supply-chain binaries, fileless malware detection) but has narrower coverage of identity attacks, cloud misconfigurations, and lateral movement within non-malware attack classes.
How much analyst time does Morpheus AI recover?
A global MSSP reduced 144,000 monthly alerts to 200 requiring human review (99.86% reduction), recovering 7,800 analyst hours annually for a 10-person SOC. At that scale, investigation and response time dropped 99%; MTTR improved 80%. For a typical 50-alert-per-day environment, Morpheus AI frees 2+ full analysts from false-positive triage for proactive threat hunting and security strategy. Intezer reduces investigation time for malware-focused alerts (~2 minutes per alert) but does not investigate all alert types, provide response automation, or correlate across systems, limiting overall analyst time recovery to investigation acceleration only.
Related Resources
Explore D3 Security’s AI SOC platform capabilities:
- Morpheus AI: Full-Stack Investigation and Response — Autonomous attack path discovery, contextual playbook generation, and visible governance
- Built-In SOAR: Orchestration and Automation — Full workflow automation, conditional logic, and integration across 800+ tools
- Attack Path Discovery Explained — Multi-dimensional investigation combining north-south and east-west correlation
- Self-Healing Integrations — Autonomous API drift repair, 4-phase response, 99.9%+ uptime
D3 Security is not affiliated with Intezer. All trademarks are the property of their respective owners. This comparison reflects publicly available information and our team’s evaluation as of April 2026.