Platform Comparison
D3 Morpheus AI vs. Dropzone AI
Why Alert Triage Alone Isn’t Enough. Compare the AI SOC Platform (Morpheus) against narrow triage agents. One engine. One trail. No fleet of agents.
See Morpheus AI Investigate Your Alerts
Executive Summary
Choose Morpheus if you need autonomous alert investigation and accountable response across the full SOC lifecycle. D3 Morpheus AI is an AI SOC Platform that delivers autonomous alert investigation and accountable response on one reasoning engine, with one audit trail across every tool in the stack. Dropzone AI is a narrow alert-triage agent built on commercial LLMs that classifies alerts and hands investigation back to analysts.
The critical difference: Morpheus AI triages up to 95% of alerts at L2+ depth in under 2 minutes, generates contextual playbooks from live evidence, orchestrates response across 800+ integrated tools, and executes the four autonomy tiers under one audit trail. Dropzone AI classifies alerts. Someone else must investigate cross-stack, orchestrate response, and remediate.
Why Alert Triage Alone Isn’t Enough
Alert triage is a useful first step, but it leaves the hardest work undone. After a triage agent (Dropzone) classifies and enriches an alert, your team still faces critical gaps:
- No cross-stack attack path discovery: Dropzone classifies the alert in front of it. It does not correlate East-West across EDR, SIEM, cloud, identity, and network to reveal lateral movement.
- No built-in orchestration: Dropzone cannot execute response actions. You need a separate SOAR platform for any containment, isolation, or remediation step.
- No contextual playbook generation: Dropzone delivers triage findings. Analysts must hand-author playbooks or manually trigger pre-built ones in a downstream system.
- Static point integrations: Dropzone connects to a limited set of core SOC tools. API changes require manual diagnosis, creating triage blind spots during maintenance windows.
- Commercial LLM dependency: Dropzone runs on general-purpose foundation models fine-tuned for security triage. Novel attack classes outside the training distribution drop in accuracy.
- Limited governance visibility: Dropzone provides limited transparency into its triage reasoning. Analysts cannot easily audit decisions or override AI recommendations at granular steps.
Morpheus solves all of this. Investigation, orchestration, remediation, and verification run on one reasoning engine and one audit trail. Alerts flow from discovery to resolution in under 2 minutes, with no manual handoffs, no separate SOAR license, and no integration overhead.
Morpheus AI Capabilities Dropzone AI Cannot Match
The following six capabilities are core to Morpheus’s architecture. Dropzone AI is not designed to deliver them.
Attack Path Discovery (Every Alert)
Morpheus maps N-S (external-to-critical) and E-W (lateral) attack paths on every alert, in real time, aligned with MITRE ATT&CK kill chain methodology. This reveals not just what happened, but where the adversary could move next. Dropzone classifies the alert in front of it; it does not correlate cross-stack or reconstruct attacker progression.
Contextual Playbook Generation
Morpheus generates playbooks from live evidence at runtime, with no waiting for SOC engineers to author them. Each playbook is specific to the attack, the customer’s environment, and available tools. Dropzone delivers triage findings; the analyst must decide what to do next.
Unified Orchestration & Remediation
800+ integrated tools, no separate SOAR platform needed. Morpheus orchestrates containment, isolation, and remediation end-to-end on one audit trail. Dropzone findings still require a third-party SOAR handoff for any response action.
Autonomous Self-Healing
After remediation, Morpheus verifies the fix worked. If not, it re-executes automatically. This closed-loop approach delivers 80% MTTR reduction and prevents adversaries from bouncing back. Dropzone stops at triage. Self-Healing Integrations also detect API drift across 800+ tools and autonomously regenerate connector code.
Cybersecurity Triage Reasoning Graph
24 months of development, 60 security specialists, customer-extensible. The Cybersecurity Triage Reasoning Graph is tuned for SOC reasoning, attack context, tool integration, and real-world incident patterns. The graph is the moat. The underlying model is interchangeable. Dropzone runs on commercial LLMs fine-tuned for triage.
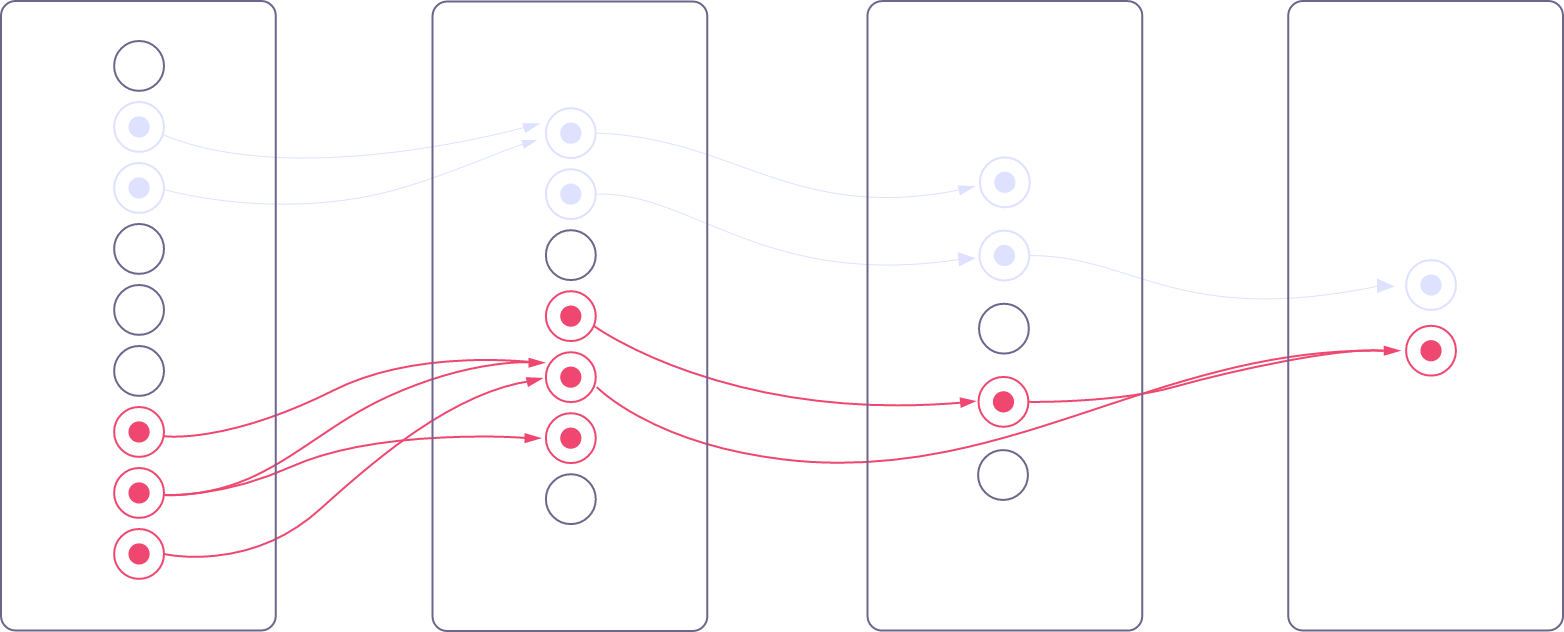
Four Autonomy Tiers
Morpheus runs across four autonomy tiers: Deterministic, AI-Assisted, AI-Led, and Autonomous. Per-action approval gates, one audit trail, evidence trees, logic chains, and confidence scores. Regulated buyers get credible autonomy, not reckless autonomy. Learn more at d3security.com/morpheus/autonomy-modes/.
Feature Comparison: Morpheus vs. Dropzone
Morpheus AI is the complete AI SOC Platform. Dropzone AI is an alert-triage agent. The table below shows what you get in each.
| Capability | D3 Morpheus AI | Dropzone AI |
|---|---|---|
| Alert Investigation | Up to 95% in <2 min (L2+ quality) | Alert-level triage and classification only |
| Attack Path Discovery (N-S + E-W) | Every alert | Not available |
| Contextual Playbook Generation | Runtime from live evidence | Not available |
| Orchestration & Remediation Engine | Built-in (800+ tools) | Requires 3rd-party SOAR |
| Triage component | Cybersecurity Triage Reasoning Graph (24 months / 60 specialists) | Commercial LLMs fine-tuned for triage |
| Autonomous Self-Healing | Verify & retry | Not available |
| Integrated Tool Ecosystem | 800+ self-healing integrations | 60+ static point integrations, limited cloud/identity coverage |
| Autonomy Spectrum | Four tiers, one engine, one audit trail | Triage-only, no orchestration tiers |
| Governance & Explainability | Evidence trees, logic chains, confidence scores — supports GDPR, EU AI Act, NIS2, SEC, CISA | Limited visibility into triage reasoning |
| MTTR (Mean Time to Remediation) | 80% reduction | Improves triage speed; remediation MTTR depends on downstream SOAR |
| Single-Vendor Solution | Investigation + Orchestration + Remediation | Triage only |
| Pricing Model | Platform Subscription + User Licenses | Per-investigation pricing, AI usage fees layered on top, plus a separate SOAR platform |

Request your free Dropzone cost comparison
WHY MORPHEUS
Why SOC Teams Choose Morpheus AI

Complete Platform, No Fragmentation
One vendor, one API, one training program. No integration glue, no vendor finger-pointing when something breaks. Investigation feeds directly into orchestration, which feeds directly into remediation, all on one reasoning engine and one audit trail. Simple.
80% Faster Remediation
Attacks are stopped in minutes, not hours. Because playbooks are generated from live evidence and executed through 800+ integrated tools without manual handoffs, adversaries do not get a second shot.

7,800 Analyst Hours Saved Annually
A global MSSP using Morpheus reduced 144,000 monthly alerts to 200 requiring human review and recovered 7,800 analyst hours annually for a 10-person SOC. Morpheus eliminates the busywork of triage, playbook writing, orchestration planning, and post-incident forensics. Analysts focus on strategic threats, not alert fatigue.

99% False Positive Elimination
Morpheus’s contextual investigation cuts false positives to 1%. No more investigating non-threats. Analysts investigate actual attacks and escalate with context, not hunches.
Lower Total Cost of Ownership
Morpheus uses a subscription pricing model. The customer pays a Platform Subscription plus User Licenses that together form the Expected Cost of running an AI SOC. The model is designed to absorb the operational cost of token consumption and AI compute internally rather than passing it through as a usage meter. By contrast, Dropzone AI prices per investigation with AI usage fees layered on top, and you still need a separate SOAR platform to act on findings. One platform, one budget line. Visit d3security.com/morpheus/pricing/ for details.
Bounded Reasoning, Customer-Extensible
Morpheus’s Cybersecurity Triage Reasoning Graph is customer-extensible. Your organization can extend the graph for your threats, your tools, and your playbooks, while bounded reasoning runs inside deterministic governance. Dropzone AI’s commercial-LLM dependency does not offer this level of architectural extension.
Morpheus Performance Metrics at a Glance
Real-world data from live Morpheus deployments:
Frequently Asked Questions
Can Dropzone AI be paired with a SOAR platform to match Morpheus?
Technically yes, but this creates significant overhead. You would license Dropzone AI for triage, license a separate SOAR platform for response actions, build custom integrations between them, train your team on both tools, and maintain two separate systems. Even then, Dropzone’s triage and the SOAR platform remain separate systems with different interfaces, different audit logs, and different learning curves. Morpheus AI unifies investigation, orchestration, and remediation on one reasoning engine and one audit trail. The result: faster remediation, lower total cost of ownership, fewer integration breakpoints.
What makes the Cybersecurity Triage Reasoning Graph different from the commercial LLMs Dropzone AI uses?
The Cybersecurity Triage Reasoning Graph was purpose-built for SOC reasoning over 24 months by 60 security specialists. It understands attack patterns, tool integration syntax, context-aware playbook logic, and incident escalation criteria in ways general-purpose models do not. Dropzone AI is built on commercial LLMs fine-tuned for security triage. Morpheus AI applies the Cybersecurity Triage Reasoning Graph to the entire SOC lifecycle: discovery, investigation, orchestration, remediation, and verification. The graph is the moat. The underlying model is interchangeable.
Does Dropzone AI offer contextual playbook generation?
No. Dropzone AI classifies and enriches alerts and hands findings back to analysts. Playbooks must be pre-built by SOC engineers or manually executed by analysts in a separate SOAR platform. Morpheus AI generates playbooks in real time from live evidence, so each response is tailored to the specific attack, the customer’s environment, and available tools.
How does Morpheus AI discover east-west attacks that Dropzone AI misses?
Dropzone AI focuses on triage of individual alerts. Morpheus AI maps attack paths across the entire stack: North-South (external-to-critical) and East-West (lateral movement) on every alert. Attack Path Discovery asks on every alert what else the attacker could do and where else they could move. This reveals hidden breach chains, privilege escalation paths, and data exfiltration routes that single-alert triage cannot see. This matters for advanced threats like lateral movement in cloud environments or multi-stage attacks.
How does Morpheus AI pricing compare to Dropzone AI?
Morpheus AI uses a subscription pricing model: a Platform Subscription plus User Licenses that together form the customer’s Expected Cost. The model is designed to absorb the operational cost of token consumption and AI compute internally rather than passing it through as a usage meter. Dropzone AI prices per investigation, with AI usage fees layered on top and overage charges when teams exceed their investigation threshold. You also still need a separate SOAR platform to act on Dropzone’s findings. See d3security.com/morpheus/pricing/ for details.
What compliance and governance documentation does Morpheus AI produce?
Morpheus AI produces documentation for every autonomous decision: evidence trees, logic chains, and confidence scores. The artifacts support audit and reporting requirements under GDPR, EU AI Act, NIS2, SEC, and CISA. Every AI action is traceable and every decision is explainable. D3 Security is SOC 2 Type II certified and ISO 27001 certified. Dropzone AI offers limited visibility into its triage reasoning, restricting analyst control and audit capability.
Ready to See Morpheus in Action?
Dropzone AI is an excellent alert-triage agent. But triage alone isn’t enough to stop modern attacks. See how Morpheus delivers autonomous alert investigation and accountable response in under 2 minutes per alert.
About D3 Security
D3 Security is the maker of Morpheus AI, the AI SOC Platform that combines autonomous investigation, orchestration, and remediation on one reasoning engine and one audit trail. Founded in 2015, D3 is trusted by Fortune 500 enterprises, government agencies, and leading financial institutions.
Learn more: www.d3security.com
D3 Security is not affiliated with Dropzone AI. All trademarks are the property of their respective owners. This comparison reflects publicly available information and our team’s evaluation as of May 2026.