Select a term…
-
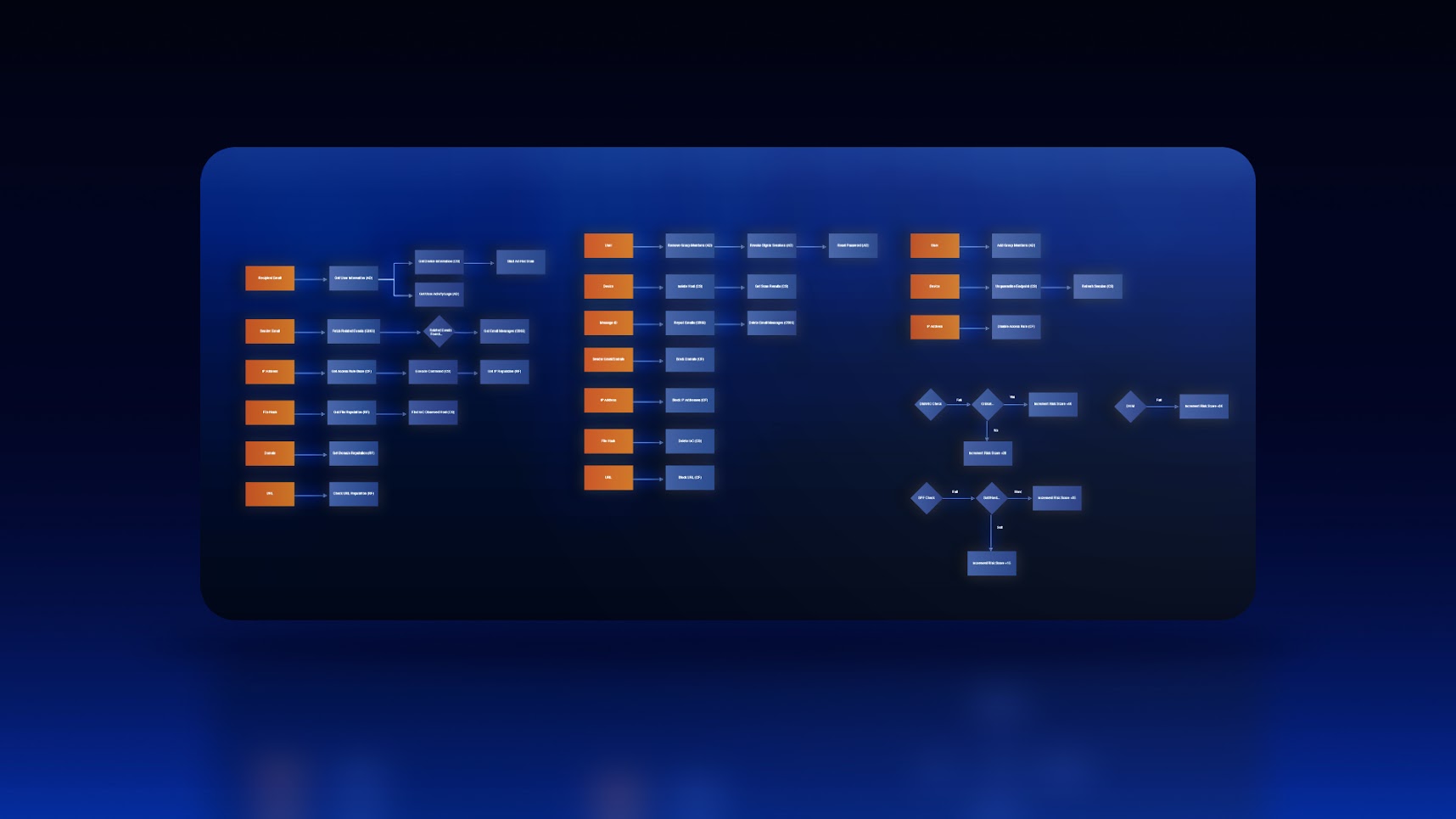
How to Build a Phishing Playbook Part 2: Wireframing
Welcome back to our series on automating phishing investigation and response with playbooks in Smart SOAR. This is a four-part series covering preparation, wireframing, development,…