At a glance: what Morpheus delivers for healthcare
Protect patient safety by catching attacks before they disrupt clinical systems. Morpheus identifies ransomware kill chains in progress by correlating alerts across your SIEM, EDR, firewalls, NDR, email security, DLP, and identity tools. It surfaces the complete attack path with recommended containment for analyst approval, often before encryption is deployed.
Reduce investigation time dramatically. Autonomous triage, enrichment, and investigation, with severity assessed based on ePHI exposure and patient safety impact rather than generic scores. Analysts focus on validated findings.
Meet HIPAA’s 60-day notification deadline with pre-assembled breach documentation. When an event constitutes a breach of unsecured PHI, Morpheus automatically generates the timeline, evidence package, scope of ePHI involved, and classification rationale. Compliance teams get the package ready to go.
Produce audit-ready evidence for OCR investigations and compliance certifications. Every triage decision, investigation, and recommendation includes the full logic chain. That satisfies OCR expectations, supports HITECH “recognized security practices” credit, and provides documentation for the annual audits the proposed HIPAA Security Rule would require.
Detect third-party compromises before they become your breach. Over 80% of stolen healthcare records originate from vendors, not hospitals. Morpheus identifies supply chain compromise patterns from firewall, NDR, and DLP alerts before they escalate.
Scale SOC capacity in an industry that underinvests in cybersecurity. Healthcare spends 4-7% of IT budgets on security versus 15% in finance. Morpheus handles high-volume triage and investigation autonomously, keeping humans in control of remediation. In healthcare, that’s a patient safety imperative.
When ransomware hits a bank, money is at risk. When ransomware hits a hospital, lives are at risk.
That’s not hyperbole. A 2023 study published by researchers at the University of Minnesota School of Public Health estimated that ransomware-related delays in care may have contributed to the deaths of 42 to 67 Medicare patients between 2016 and 2021. When a hospital’s EHR goes dark, clinicians lose access to medication histories, allergy information, lab results, imaging. Emergency departments divert ambulances. Surgeries get canceled. Pharmacies can’t verify prescriptions. In 2025, hospitals that suffered ransomware attacks reported operating at half capacity for weeks.
The scale is staggering. In 2024, 259 million Americans had their protected health information reported as compromised. In 2025, over 445 ransomware attacks targeted hospitals and direct care providers, attacks on healthcare businesses surged 25 percent, and the average breach cost the industry $9.77 million, the highest of any sector.
Healthcare isn’t just one of the most targeted industries. It’s the most targeted. And unlike every other sector, a successful attack here has a direct path to patient harm.
The alert flood and the SOC gap
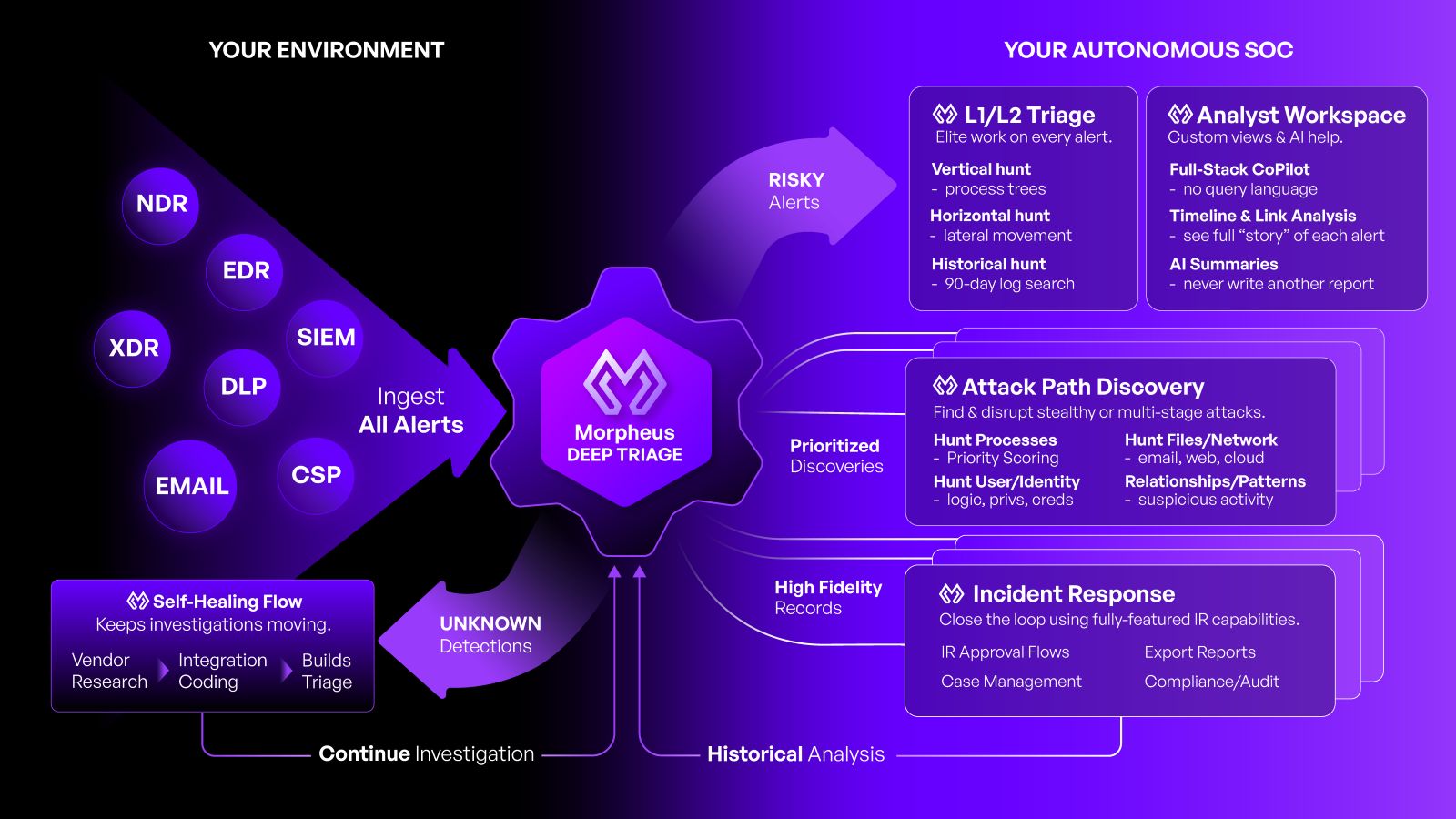
Most hospitals have invested in SIEMs, EDR, network firewalls, NDR, email security, DLP, and identity platforms. These tools are doing their job. They’re generating alerts.
The problem is what happens next.
A mid-size health system’s security stack can produce thousands of alerts a day. SOC analysts, already scarce in an industry that spends 4-7% of IT budgets on security (versus 15% in finance), burn their time triaging false positives. The real threats hide in the noise. The phishing email that led to the credential compromise that led to the privilege escalation that led to the lateral movement into the EHR environment: each stage generated an alert in a different tool, and nobody connected them in time.
Traditional SOAR playbooks were built for last year’s attack patterns. When the attack spans email security, identity, EDR, NDR, and the SIEM simultaneously, static playbooks break down.
That gap costs lives.
What Morpheus does, and what it doesn’t
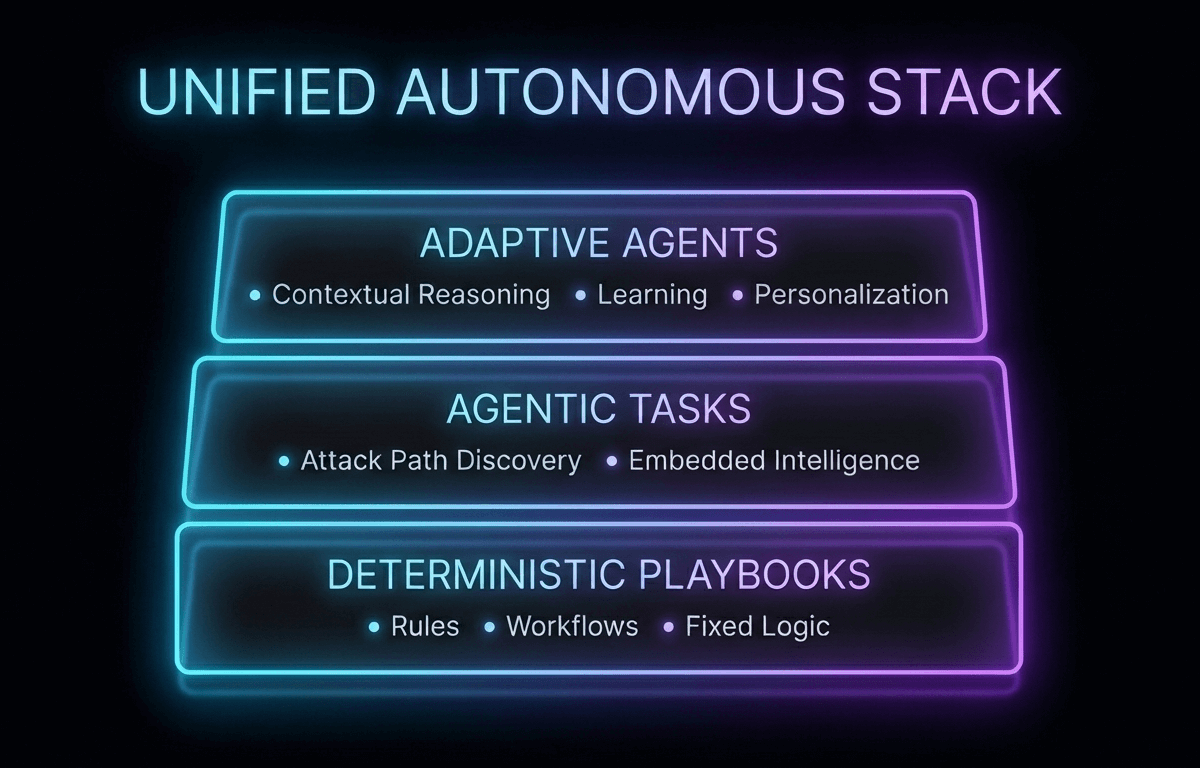
D3 Morpheus is an AI-autonomous SOC built for exactly this problem. It’s worth being precise about what that means.
Morpheus is not a detection engine. It doesn’t scan your environment or replace your existing security tools. Your SIEM, EDR, firewalls, NDR, email security, DLP, and identity platforms are already generating the alerts. Morpheus ingests all of those alerts and applies a purpose-built cybersecurity threat LLM and attack path discovery framework to triage, investigate, correlate, and act on them at a speed and depth that human-only SOC teams can’t match.
Morpheus keeps humans in control of remediation. In healthcare, an automated action could disable a clinical workstation mid-procedure, interrupt EHR access during a code blue, or take a medical device network segment offline. Human oversight of remediation isn’t a regulatory box to check. It’s a patient safety requirement. Morpheus surfaces the finding, the evidence, and the recommended action. Your analyst makes the call.
The cybersecurity threat LLM
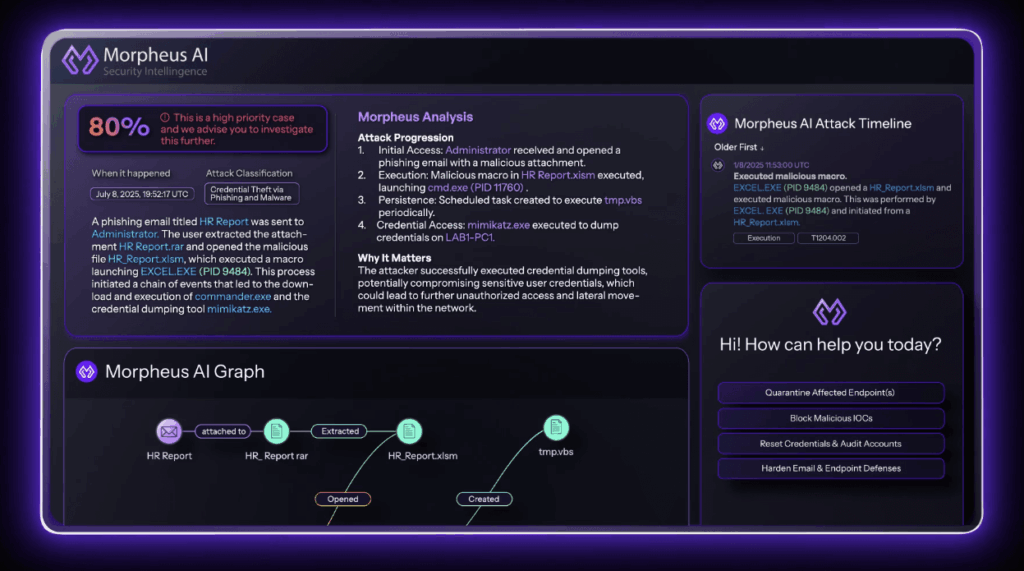
Morpheus’s LLM was trained on cybersecurity threat intelligence, attack methodologies, and defensive techniques. For healthcare, this means it understands the context behind healthcare-specific alerts: EHR access anomalies, medical device network events, PACS system security flags. It adds threat intelligence to every ingested alert, recognizing when an indicator is associated with INC, Qilin, or Medusa (the ransomware strains that dominated healthcare attacks in 2025). It assesses severity based on ePHI exposure risk and patient safety impact, not generic scores.
Attack path discovery from your existing alerts
This is the capability that changes everything for healthcare security teams.
Morpheus evaluates alerts collectively. Its attack path discovery framework correlates alerts across your entire security stack to reconstruct the behaviors, actions, and functions performed by an attacker.
Here’s what that looks like: Email security flags a suspicious link clicked by a nurse. Identity security logs a new authentication from an unusual location using her credentials. EDR detects PowerShell execution and privilege escalation on the clinical workstation. NDR captures lateral movement traffic toward the EHR database servers. The SIEM logs an unusual bulk query against patient records.
Individually, each alert might be triaged as medium severity. Morpheus’s attack path discovery framework connects them into a single ransomware kill chain and surfaces the complete attack path with recommended containment for analyst approval, often before encryption starts.
It’s correlation across your existing alert sources, finding the attack stories your tools are already telling.

Customized to your organization
A rural critical access hospital faces different threats and runs different technology than a large integrated delivery network. Morpheus adapts. You configure risk prioritization based on your HIPAA risk analysis. The platform generates contextual playbooks matched to your regulatory environment and clinical workflows. Over time, it incorporates your historical incident data and internal policies, learning the difference between a legitimate late-night EHR access by an on-call physician and an anomalous pattern that warrants investigation.
When your tools change (a SIEM migration, a new NDR deployment, an email security upgrade) Morpheus’s self-healing integrations adapt automatically. No coverage gaps.
Fully open and auditable
Every action Morpheus takes is fully transparent. For every alert ingested, every triage decision, every investigation, every correlation, every remediation recommendation, you get the complete logic chain. What was analyzed, what enrichment was applied, what reasoning was followed, what was recommended.
For healthcare, this matters enormously. OCR investigations don’t just examine the breach itself. They examine your entire security program. The proposed HIPAA Security Rule update would require annual audits of all safeguards. The HITECH Act gives you credit for “recognized security practices,” but only if you can demonstrate them.
When OCR asks “show me how your SOC handled this”, Morpheus gives you a timestamped, evidence-based answer for every alert, from ingestion through resolution.
Healthcare use cases
Ransomware kill chain identification: Each stage of a ransomware attack generates alerts in different tools. Morpheus ingests them all and uses attack path discovery to surface the full kill chain, often catching the attack in progress and recommending containment before encryption, with the documentation needed for HIPAA breach notification.
ePHI exfiltration scoping: When attackers steal patient data, Morpheus correlates DLP alerts, SIEM logs, identity events, and NDR traffic to determine the full scope of ePHI exposure. That enables accurate breach notifications with specific numbers of affected individuals and types of PHI compromised.
Business associate risk: Over 80% of stolen healthcare records come from third-party vendors, not hospitals. Morpheus ingests alerts from the firewalls, NDR, and DLP tools that monitor business associate connections and identifies supply chain compromise patterns before they become covered entity breaches.
Insider threat correlation: Individual EHR access alerts, DLP triggers, and identity anomalies often fall below escalation thresholds on their own. Morpheus’s attack path discovery framework correlates them to reveal systematic unauthorized ePHI access, the kind that leads to OCR investigations and class action lawsuits.
Medical device pivot detection: Connected medical devices on legacy operating systems are attractive pivot points for attackers. Morpheus ingests the network security alerts these devices generate and correlates them with broader attack indicators to identify when a compromised device is being used for lateral movement.
The regulatory moment
HIPAA’s regulatory framework is in the middle of its most significant overhaul in over a decade. The proposed Security Rule update would eliminate the flexibility that allowed some organizations to treat security controls as optional. Mandatory encryption, mandatory MFA, mandatory asset inventories, mandatory vulnerability scanning, mandatory annual audits, mandatory 72-hour system restoration. The word “mandatory” now applies to everything.
OCR’s compliance audits are underway. The HITECH Act rewards mature security practices and penalizes their absence. State attorneys general are pursuing enforcement. Bipartisan legislation in Congress is pushing for stricter standards.
An opaque AI system that produces outcomes without explaining itself creates compliance risk, not compliance assurance. Morpheus was built on the principle that speed and transparency coexist, and that keeping humans in the loop for remediation is the right way to operate in an industry where the consequences of automation are measured in patient outcomes.
Where this is heading
Healthcare’s cybersecurity crisis is accelerating. Ransomware attacks on hospitals held steady in 2025 as attacks on healthcare businesses surged. The regulatory requirements are increasing sharply. The talent gap isn’t closing. And the stakes (patient safety, patient privacy, organizational viability) are higher than in any other industry.
D3 Morpheus gives healthcare organizations what they actually need: an AI-autonomous platform that ingests alerts from across the existing security stack, applies a purpose-built cybersecurity threat LLM and attack path discovery framework to triage and investigate at machine speed, keeps humans in control of remediation decisions, and produces the auditable evidence trail that HIPAA, HITECH, and the next wave of regulation demand.
The autonomous SOC exists to make sure your analysts’ knowledge gets applied to validated, investigated findings. In healthcare, that’s how you keep patients safe.
For a deeper look at how autonomous alert intelligence addresses healthcare-specific threats, regulatory requirements, and SOC challenges, read the full whitepaper: The AI-Autonomous SOC for Healthcare.




