-
Advancing SOAR Technology: Key 2023 Updates in Incident Response Automation
In 2023, we’ve achieved a remarkable milestone in the cybersecurity landscape by securing 70% of our new business from security teams eager to upgrade from…
-

Navigating the Trade-Offs Between Security Vendor Consolidation and Best-Of-Breed Solutions
Vendor consolidation, a strategy where organizations reduce the number of vendors they use, has become one of the key trends witnessing significant growth in recent…
-

Unpacking the Financial and Security Implications of Vendor Lock-In
The concept of ‘platformization’ – where leading vendors like Cisco or Palo Alto offer extensive, integrated security platforms – is becoming increasingly common. However, this…
-

Integration Spotlight: Stellar Cyber Open XDR
By integrating D3 Smart SOAR (Security Orchestration, Automation, and Response) with Stellar Cyber Open XDR, organizations can create a seamless incident response workflow that minimizes…
-
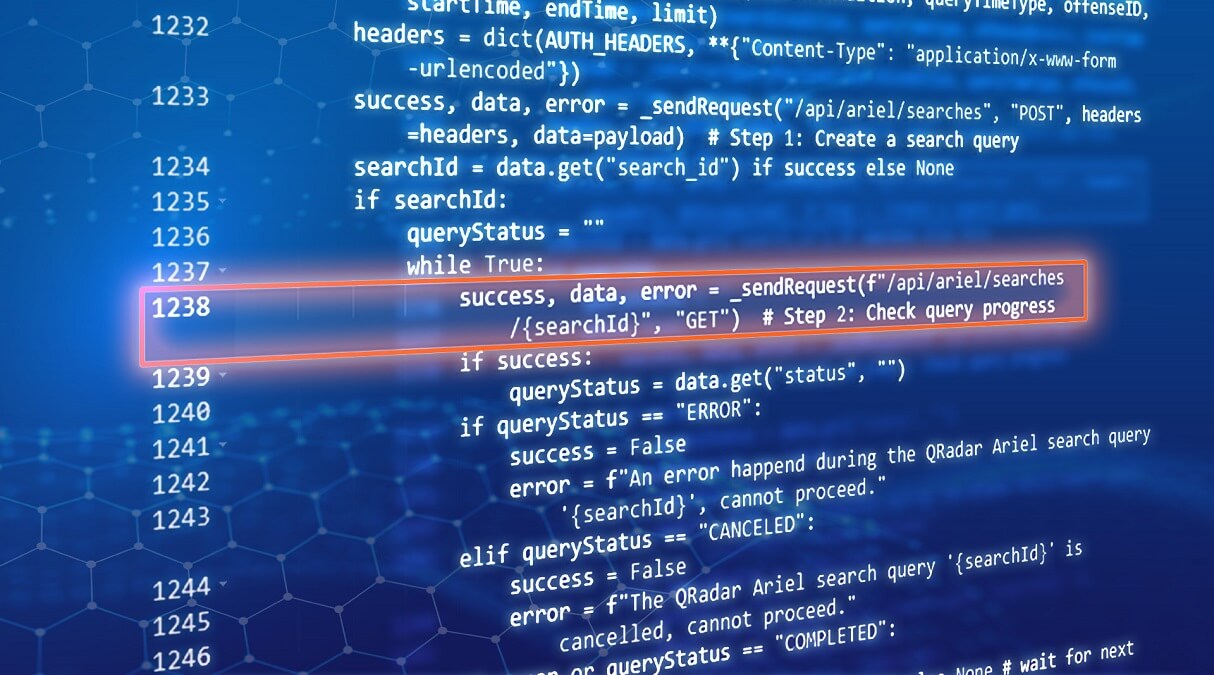
How Smart SOAR Integrations are Built
One of the most common reasons that SOAR users leave their existing solution and work with D3 is because of integration maintenance. In other SOAR…
-

Automated Incident Response with ServiceNow and Smart SOAR
Effective IT service management is often determined by the speed and efficiency of response mechanisms. This article delves into how Smart SOAR’s integration with ServiceNow…
-

Why Smart SOAR is the Best SOAR for Slack
Effective communication is a critical component in incident response, often making the difference between rapid resolution and prolonged impact. This article explores how the integration…
-
Bi-Directional Sync with Microsoft Sentinel and Smart SOAR
Managed security service providers (MSSPs) and organizations that oversee multiple security teams will often have to manage multiple tenants of Microsoft Sentinel. In this situation,…
-

Why Smart SOAR is the Best SOAR for Darktrace
The need for integrated cybersecurity solutions has never been more pressing. With the growing complexity of cyber threats, having siloed security tools is no longer…
Pierre Noujeim
Select a term…