Platform Comparison
D3 Morpheus AI vs. Elastic Security
Why a SIEM with Assistive AI Isn’t Enough. Compare the AI SOC Platform (Morpheus) Against a SIEM-Anchored Suite. One engine. One trail. No fleet of agents.
See Morpheus AI Investigate Your Alerts
Executive Summary
Choose Morpheus if you need autonomous alert investigation and accountable response across every tool in the stack, not just inside one SIEM console. D3 Morpheus AI is an AI SOC Platform that delivers autonomous alert investigation and accountable response on one reasoning engine, with one audit trail across every tool in the stack. Elastic Security is Elastic’s SIEM and endpoint detection suite on the Elasticsearch data layer, with assistive AI features (Attack Discovery, AI Assistant) layered on top.
The critical difference: Morpheus triages up to 95% of alerts at L2+ depth in under 2 minutes, generates playbooks from live evidence, runs across 800+ integrated tools, and executes the four autonomy tiers under one audit trail. Elastic detects threats inside its own data layer and accelerates analyst review with an LLM assistant. Investigation, response orchestration, and accountable AI execution stay with the analyst.
Why a SIEM + Assistive AI Isn’t Enough
Detection inside a single data layer is necessary, but it isn’t an AI SOC. After Elastic Security generates an alert and Attack Discovery summarizes related signals, the analyst still owns every downstream decision. Critical gaps remain:
- Detection without autonomous investigation: Elastic alerts and summarizes; it does not autonomously investigate every alert at L2+ depth or generate response playbooks at runtime.
- SIEM-bound correlation: Attack Discovery operates inside the Elasticsearch cluster. Attack paths that traverse tools outside Elastic ingest are out of scope.
- No dedicated SOAR: Case management and built-in response actions ship with the product. Cross-tool orchestration and conditional playbook chains require a third-party SOAR or custom code against the Elastic API.
- Customer-selected general LLM: The AI Assistant routes to a customer-chosen general-purpose model. Cybersecurity reasoning, evidence trees, and explainability live in the customer’s external LLM contract, not in a purpose-built SecOps reasoning system.
- East-west blind spots: Lateral movement across email, endpoint, identity, and cloud boundaries cannot be traced from inside one SIEM’s ingest pipeline.
- Usage-coupled AI cost: Attack Discovery and the AI Assistant consume tokens and ingest at a rate that scales with alert volume and incident surges, exactly when SOC teams cannot afford to ration depth.
Morpheus solves all of this. Because investigation, orchestration, and accountable response are built into one platform with the Cybersecurity Triage Reasoning Graph at the core, alerts flow from detection to L2+ investigation to runtime playbook execution in under two minutes, beside Elastic or any SIEM, on one audit trail.
Morpheus AI Capabilities Elastic Cannot Match
The following six capabilities are core to Morpheus’s architecture. Elastic Security is not designed to deliver them.
Beside Any SIEM (No SIEM Lock-In)
Morpheus AI works beside Elastic Security, Splunk, Microsoft Sentinel, QRadar, Chronicle, or any SIEM. The customer’s existing data layer stays in place. Autonomous investigation is added across the stack on one audit trail. Elastic Security is itself the SIEM and compounds value only when more data is committed to the Elasticsearch data lake.
Attack Path Discovery (Across 800+ Tools)
Morpheus maps N-S (external-to-critical) and E-W (lateral) attack paths on every alert in real time, across 800+ integrated tools from any vendor, with MITRE ATT&CK references to adversary tactics and techniques. Elastic’s Attack Discovery correlates inside Elastic-ingested data and stops at the SIEM boundary.
Contextual Playbook Generation (Runtime)
Morpheus generates response playbooks at runtime from live evidence, specific to the attack, the customer’s environment, and available tools. Elastic ships case management and built-in response actions; complex orchestration is analyst-authored or requires third-party SOAR.
Autonomous Investigation (Not Assistive AI on SIEM Data)
Morpheus investigates up to 95% of alerts at L2+ depth in under two minutes, autonomously, before an analyst opens the case. Elastic’s AI Assistant and Attack Discovery accelerate analyst review inside the Elastic console but require the analyst to drive the investigation.
Cybersecurity Triage Reasoning Graph
Morpheus runs on D3’s purpose-built SecOps reasoning system: 24 months and 60 specialists in the build. The graph is the moat; the LLM underneath is interchangeable. Elastic’s AI Assistant routes natural-language queries to a customer-selected general-purpose LLM.
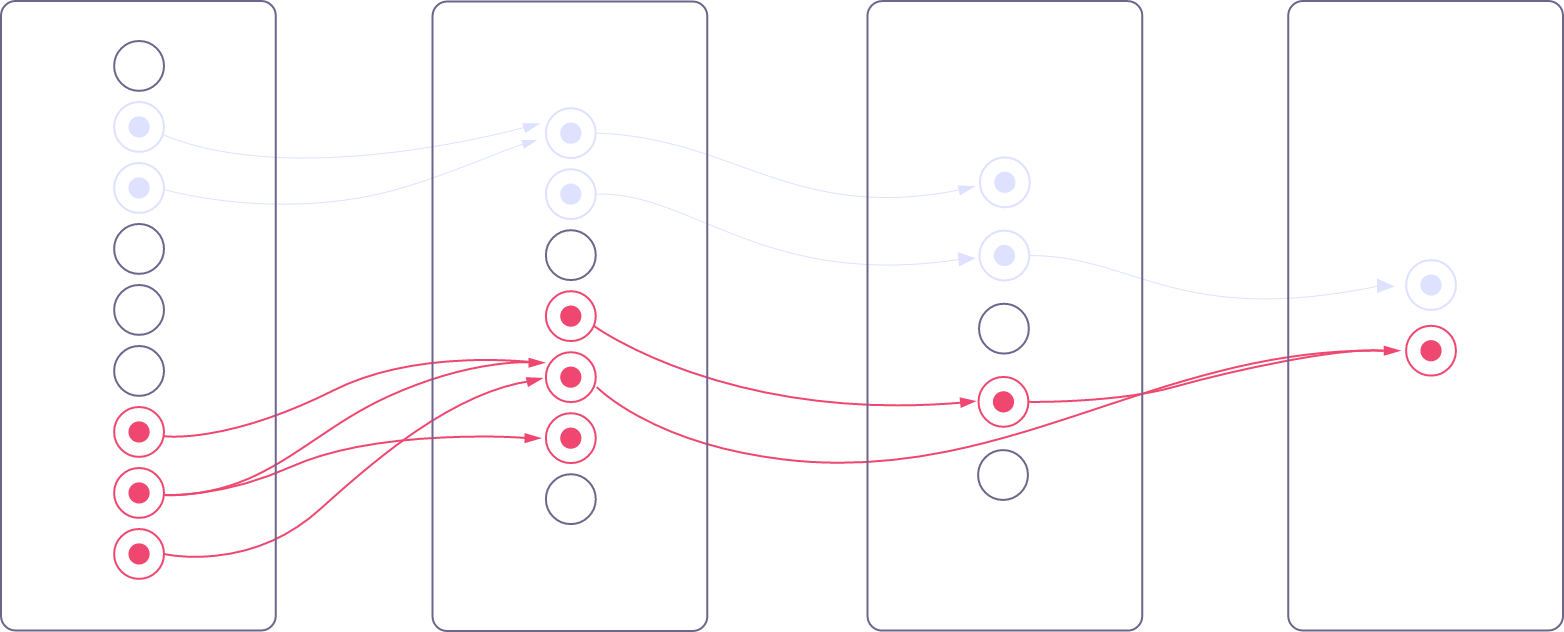
Four Autonomy Tiers (One Engine, One Audit Trail)
Morpheus operates across four tiers on one engine: Tier 1 Deterministic, Tier 2 AI-Assisted, Tier 3 AI-Led, Tier 4 Autonomous. Each tier produces evidence trees, logic chains, and confidence scores on one audit trail. See d3security.com/morpheus/autonomy-modes/.
Feature Comparison: Morpheus vs. Elastic Security
Morpheus AI is an AI SOC Platform for autonomous investigation and accountable response across every tool in the stack. Elastic Security is a SIEM and endpoint detection suite with assistive AI features. The table below shows what each delivers.
| Capability | D3 Morpheus AI | Elastic Security |
|---|---|---|
| Alert Investigation | Up to 95% in <2 min (L2+ quality) | Detection inside Elasticsearch; investigation analyst-driven with AI assist |
| Attack Path Discovery (N-S + E-W) | Every alert | Attack Discovery correlation within Elastic-ingested data only |
| Contextual Playbook Generation | Runtime from live evidence | Case management + built-in response actions; no native playbook generation |
| Orchestration & Remediation Engine | Built-in (800+ tools) | No dedicated SOAR; third-party SOAR or webhook required |
| Triage component | Cybersecurity Triage Reasoning Graph (24 months / 60 specialists) | AI Assistant + Attack Discovery using customer-selected general LLM |
| Autonomous Self-Healing | Verify & retry | Not available |
| Integrated Tool Ecosystem | 800+ self-healing integrations, any vendor | Broad log-source coverage; cross-tool action via webhook or third-party |
| Autonomy Spectrum | Four tiers, one engine, one audit trail | Analyst-driven workflow with AI assistance |
| Governance & Explainability | Evidence trees, logic chains, confidence scores — supports GDPR, EU AI Act, NIS2, SEC, CISA | Elastic audit logging; AI reasoning chain depends on customer-selected LLM |
| MTTR (Mean Time to Remediation) | 80% reduction | Dependent on analyst response and third-party SOAR |
| Single-Vendor Solution | Investigation + Orchestration + Remediation | Detection + analytics; SOAR partner required for response |
| Pricing Model | Platform Subscription + User Licenses | Resource-based cloud or tiered subscription; AI features add usage-based variable cost |

Request your free Elastic cost comparison
WHY MORPHEUS
Why SOC Teams Choose Morpheus AI

Complete Platform, No Fragmentation
One vendor, one API, one training program, one audit trail. Investigation feeds into orchestration feeds into accountable response. Morpheus AI sits above Elastic Security and the rest of the security stack, not inside any one SIEM console. No integration glue, no vendor finger-pointing when something breaks.
80% Faster Remediation
Attacks are stopped in minutes, not hours. Playbooks are generated from live evidence and executed through 800+ integrated tools without manual handoffs. East-west lateral movement that an Elasticsearch-bound correlation cannot reach gets traced and contained on the same audit trail.

7,800 Analyst Hours Saved Annually
Per 1,000 alerts, Morpheus eliminates the busywork of triage, playbook authoring, orchestration planning, and post-incident forensics. Analysts focus on strategic threats, not alert fatigue inside the Elastic console.

99% False Positive Elimination
Morpheus’s contextual investigation cuts false positives to roughly 1%. No more investigating non-threats. Analysts work actual attacks and escalate with evidence trees and confidence scores, not hunches drawn from an LLM summary inside one SIEM.
Lower Total Cost of Ownership
Morpheus uses a subscription pricing model. The customer pays a Platform Subscription plus User Licenses that together form the Expected Cost of running an AI SOC. The model is designed to absorb the operational cost of token consumption and AI compute internally rather than passing it through as a usage meter. By contrast, Elastic Security’s ingest- and resource-based cloud pricing scales with data volume, retention, and features, and the AI Assistant and Attack Discovery introduce additional usage-based variable costs through a customer-selected LLM contract. One platform, one budget line. Visit d3security.com/morpheus/pricing/ for details.
Bounded Reasoning, Customer-Extensible
The Cybersecurity Triage Reasoning Graph encodes attack patterns, evidence-tree logic, and confidence scoring as a purpose-built SecOps reasoning system. The graph is the moat; the reasoning model underneath is interchangeable. Customers can extend the graph with their own playbooks, SOPs, and tool stack, without rebuilding the reasoning system or coupling to a single SIEM data layer.
Morpheus Performance Metrics at a Glance
Real-world data from live Morpheus deployments:
Frequently Asked Questions
Can Elastic Security be paired with a SOAR platform to match Morpheus?
Technically yes, but it creates significant overhead. You would license Elastic Security, license a separate SOAR platform (Splunk SOAR, Cortex XSOAR, Tines, or similar), build custom integrations between them, train your team on both, and maintain two consoles with two audit logs. Even then, Elastic’s detection and the SOAR’s response remain separate systems with separate interfaces. Morpheus AI unifies investigation, orchestration, and remediation on one reasoning engine and one audit trail, beside Elastic or any SIEM. The result: faster remediation, predictable subscription pricing, and fewer integration breakpoints.
What makes the Cybersecurity Triage Reasoning Graph different from Elastic’s AI Assistant?
Elastic’s AI Assistant routes natural-language queries to a customer-selected general-purpose LLM and operates against data inside Elasticsearch. The Cybersecurity Triage Reasoning Graph is D3’s purpose-built SecOps reasoning system, built over 24 months with 60 specialists. It encodes attack patterns, tool integration syntax, evidence-tree logic, and confidence scoring for the full SOC lifecycle: discovery, investigation, orchestration, response, and verification. The graph is the moat; the LLM underneath is interchangeable. The result is better accuracy, explainability, and autonomy than a general-purpose assistant on a single SIEM’s data layer.
What is contextual playbook generation, and does Elastic Security have it?
No. Elastic Security ships case management, alert routing, and a set of built-in response actions in the Elastic Defend agent. Cross-tool orchestration and complex playbook chains require third-party SOAR or custom code against the Elastic API. Morpheus AI generates response playbooks at runtime from live evidence, tailored to the specific threat, target asset, organizational SOPs, and available tool stack. Novel threats receive a purpose-built workflow on first encounter, with no static library to maintain and no coverage ceiling.
How does Morpheus discover east-west attacks Elastic cannot trace?
Elastic’s Attack Discovery correlates alerts within Elasticsearch-ingested data. Morpheus Attack Path Discovery performs simultaneous two-axis investigation on every alert: vertical (North-South) deep inspection through up to 90 days of historical telemetry, and horizontal (East-West) cross-stack correlation across 800+ integrated tools from any vendor, including tools that do not feed Elastic. Lateral movement, persistence mechanisms, and multi-stage attacks that traverse email, endpoint, identity, and cloud boundaries are reconstructed at L2+ depth in under two minutes, before an analyst opens the case.
How does Morpheus AI pricing compare to Elastic Security pricing?
Morpheus AI uses a subscription pricing model. The customer pays a Platform Subscription plus User Licenses that together form the customer’s Expected Cost of running an AI SOC. The model is designed to absorb the operational cost of token consumption and AI compute internally rather than passing it through as a usage meter. Elastic Security uses an ingest-based and resource-based cloud pricing model that scales with data volume, retention, and features. AI features such as Attack Discovery and the AI Assistant introduce additional usage-based variable costs through a customer-selected LLM contract. See d3security.com/morpheus/pricing/ for details.
What compliance and governance capabilities does Morpheus AI provide alongside Elastic Security?
Morpheus AI produces documentation for every autonomous decision: evidence trees, logic chains, and confidence scores. The artifacts support audit and reporting requirements under GDPR, EU AI Act, NIS2, SEC, and CISA. Every AI action is traceable and every decision is explainable on one audit trail across the full security stack, beside Elastic Security or any SIEM. D3 Security is SOC 2 Type II certified and ISO 27001 certified.
Ready to See Morpheus in Action?
Elastic Security is an excellent SIEM and endpoint detection suite. But a SIEM with assistive AI inside its own console isn’t enough to autonomously investigate and respond to modern attacks. See how Morpheus delivers autonomous alert investigation and accountable response on one engine and one audit trail, beside Elastic or any SIEM.
About D3 Security
D3 Security is the maker of Morpheus AI, the AI SOC Platform that combines autonomous investigation, orchestration, and remediation on one reasoning engine across every tool in the stack. Founded in 2015, D3 is trusted by Fortune 500 enterprises, government agencies, and leading financial institutions.
Learn more: www.d3security.com
D3 Security is not affiliated with Elastic or Elastic Security. All trademarks are the property of their respective owners. This comparison reflects publicly available information and our team’s evaluation as of May 2026.