Cybersecurity Triage LLM
Spend Your Time on Confirmed Threats.
The Morpheus SecOps LLM separates real threats from noise — autonomously, at L2+ depth, across your entire security stack. Purpose-built for security. Trained on attack paths, TTPs, kill chains, and IR. Not a generic AI model with a security prompt.
95% of Alerts Triaged in Under 2 Minutes. Without Static Playbooks.
Autonomous SOC triage across every tool in your stack — from alert to high-fidelity decision in seconds, not hours.






The Morpheus SecOps LLM
Every Other AI SOC Triage Tool Wrapped a Generic Model. We Didn’t.
Most AI-powered security tools are general-purpose LLMs with a security prompt attached. They know security vocabulary. They don’t know how attacks work. The Morpheus SecOps LLM was developed over 24 months by 60 specialists — red teamers, SOC analysts, data scientists, and AI engineers. Trained on attack paths, adversary TTPs, kill chains, and real IR case data, it understands attack behavior, not just attack names. That’s the difference between AI that describes a Kerberoasting attempt and AI that knows what comes next.
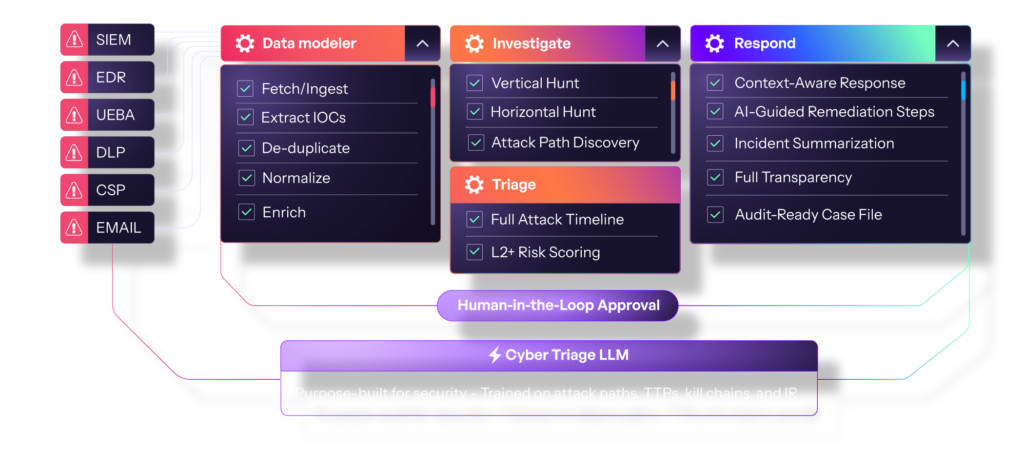
And it learns. Custom EDR detections, regulated workflows, industry-specific threat profiles, unique asset sensitivities — the Morpheus SecOps LLM absorbs them all, continuously sharpening its analysis against your specific environment.
Cyber Alert Triage
High-Fidelity, High-Confidence Incidents. Nothing Else Gets Through.
The Morpheus SOC LLM merges low-quality alerts into robust, contextual incidents — eliminating false positives and benign noise before they reach your analysts. 145,000 alerts became 200 requiring human review for one MSSP customer. That’s not a filter. That’s intelligence.
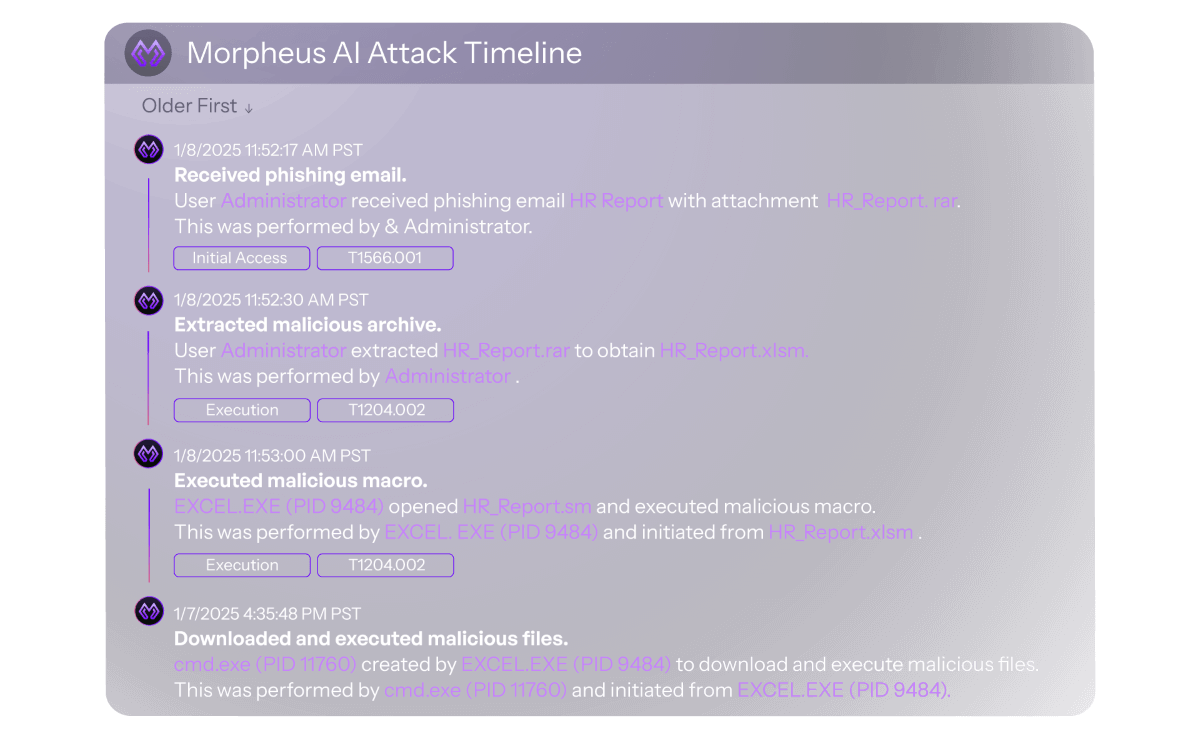
Full Attack Timeline
The Complete Attack Story. Stitched Together Automatically.
Morpheus compiles every alert, IOC, file, and entity into a chronological attack timeline — visualizing the full investigation sequence from initial access to current state. No manual reconstruction. No pivoting between tools. Your analyst sees the complete picture at a glance, with every data point sourced and auditable.

Alert Prioritization
Every Incident Ranked. Nothing Critical Missed.
IRPS considers impact, confidence, context and mitigation. It’s how Morpheus weighs attack severity, threat likelihood, and existing containment to rank each incident’s urgency, boiling everything down for at-a-glance alert priority. The fastest path from alert queue to right action.
Environment-Aware Analysis
The LLM That Knows Your Environment, Industry and Unique SOPs.
Generic AI reasons about threats in the abstract. The Morpheus SecOps LLM reasons about threats in your environment — absorbing your asset hierarchy, custom detections, SOPs, and IR procedures over time. The longer it runs in your security operations, the sharper the convictions.
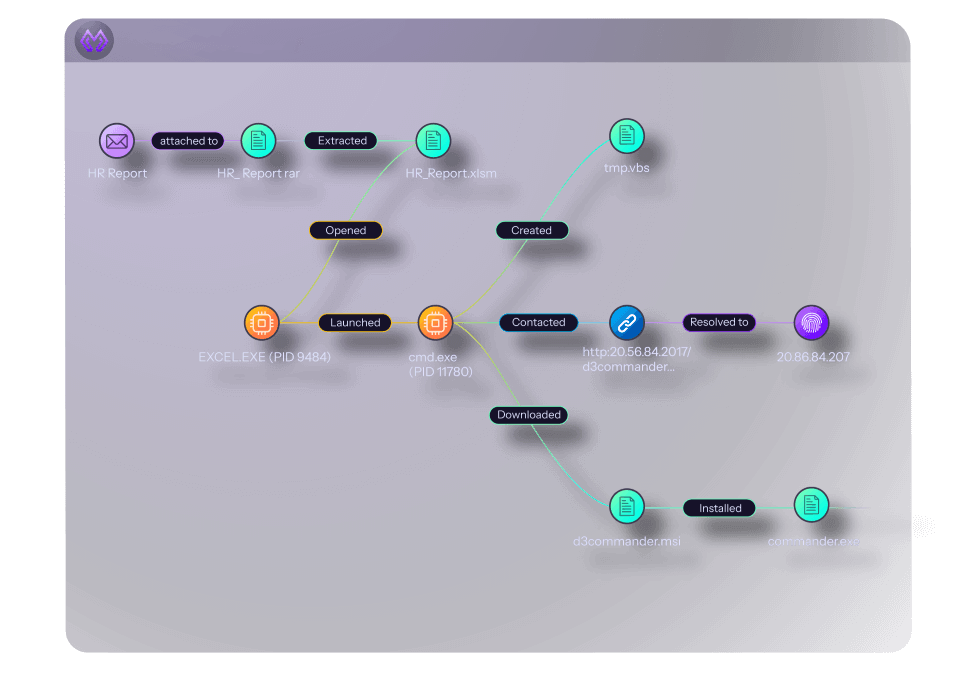
Dynamic Link Analysis
See Every Connection. Understand Every Relationship.
Morpheus maps every alert, user, IP, and artifact into a dynamic relationship graph — revealing how an incident unfolds across users, hosts, and systems. Hidden connections surface automatically. The graph updates in real time as new data arrives, sharpening the investigation and response picture continuously.
Instant Cross-Stack Alert Prioritization
Every Threat Ranked. Across Every Tool. In Real Time.
Morpheus auto-grades every incident based on severity, context, and full-stack telemetry — not just what one tool saw. Real threats rise to the top. Noise disappears. Analysts always know exactly where to focus.

Morpheus AI SOC delivers autonomous investigation and response at machine speed — with full transparency and human approval on every action.
Instant Event Timelines
Every security alert automatically compiled into a chronological visual timeline — clear, real-time insight into incident progression across your entire stack.
Alert Prioritization Without Blinders
IR Priority Score uses data from every connected security tool and threat intel source — delivering accurate alert priority with no visibility gaps.
Dynamic Link Analysis
IOCs, incidents, and attack timelines visualized in an AI-powered relationship graph — uncovering hidden connections and threat patterns that manual analysis would miss.
Don’t Take Our Word for It. Take Theirs.
“We completely elevated our SecOps and incident response.”
David, CISO
“Ingesting it all into D3 and getting that level of automation is amazing.”
Evan, CISO
“An indispensable asset in our SecOps arsenal, delivering immediate value.”
Arif, VP Cyber
AI YOUR SOC ✨
Every alert. Fully investigated. In under 2 minutes.
Learn More About AI SOC Triage
Check out these resources on the Morpheus SecOps LLM and autonomous SOC investigation methodology.
-
6 Minutes and a Prayer: The Math That Proves Your SOC Is Gambling with Every Alert
This whitepaper presents a math-driven analysis that exposes an inconvenient truth hiding in plain sight across the cybersecurity industry.
-
Autonomous Investigation Compared: D3 Morpheus AI vs. Microsoft Security Copilot
We tested D3 Morpheus AI against Microsoft Security Copilot across three real attack scenarios. Morpheus found root cause in all three. Copilot found it in none. Read the full results.

-
Blending Deterministic Workflows with AI: Architecting the Enterprise and MSSP SOC of the Future
A blueprint for autonomy you can control. Learn how to blend deterministic precision with cognitive scale to autonomously triage 95% of alerts.

Common Questions
AI SOC Triage and the Morpheus SecOps LLM — Explained.
What is autonomous SOC triage?
Autonomous SOC triage is the AI-powered classification, prioritization, and investigation of security alerts without manual analyst intervention. D3 Morpheus delivers autonomous SOC triage at L2+ depth using a purpose-built cybersecurity triage LLM — covering 100% of alerts, 95% in under 2 minutes.
What is the Morpheus SecOps LLM?
A SecOps LLM purpose-built for security — developed over 24 months by 60 specialists and trained on attack paths, adversary TTPs, kill chains, and real IR case data. Unlike general-purpose AI, it understands how attacks propagate and investigates across your entire environment, not just individual alerts.
How is AI-powered SOC triage different from traditional alert handling?
Traditional alert handling requires analysts to manually review, enrich, and rank each alert — 20–40 minutes at L2 depth. AI-powered SOC triage performs that work autonomously, applying the Morpheus SecOps LLM to every alert simultaneously. Same depth. A fraction of the time.
What is alert prioritization in Morpheus?
Morpheus uses its IR Priority Score (IRPS) for alert prioritization — weighing attack severity, threat confidence, environmental context, and existing containment to rank every incident by urgency. Instant at-a-glance alert priority. No manual review required.
How does Morpheus reduce alert noise?
The Morpheus SecOps LLM merges low-quality alerts into consolidated, high-confidence incidents — eliminating false positives before they reach analysts. One MSSP customer reduced 145,000 alerts every two weeks to 200 requiring human review. A 99%+ reduction.
What makes the Morpheus SecOps LLM different from a generic model for cyber alert triage?
Generic models know security vocabulary. The Morpheus SecOps LLM knows security behavior — reasoning about attack sequences, lateral movement, and threat propagation across your specific environment. It also learns your SOPs, asset hierarchy, and historical incidents, improving cyber alert triage accuracy continuously.
Does Morpheus work across my entire security stack?
Yes. Morpheus connects to 800+ security tools across SIEM, EDR, IAM, cloud, email, NDR, and DLP via self-healing integrations — performing autonomous analysis across every alert source simultaneously, with investigation and response workflows that execute across your existing stack.
Your Analysts Deserve Better Than an Alert Queue.
Give them confirmed threats. Give them context. Give them convictions.
Your data. Your stack. Your results. No slideshow.