Response & Orchestration
Autonomous Investigation. Governed Response. One Platform.
Morpheus handles the investigation. Generates the response plan. Executes through trusted integrations. Your analyst approves every action. Nothing handed off. Nothing left open.
From Alert to Closed Case. Without a Second Tool.
800+ trusted integrations for investigation, triage, and IR orchestration — no SOAR required.






An AI SOC That Can Actually Replace Your SOAR
Every Other AI SOC Tool Still Needs a SOAR. Morpheus Doesn’t.
AI SOC tools do triage. Then they stop. The investigation is handed back to your analysts, and the response still needs a SOAR underneath to execute. You haven’t replaced anything — you’ve added a layer.
Morpheus is different. It autonomously investigates and triages every alert, then generates a complete IR response plan — tailored to the specific incident, your environment, and your tool stack — ready for analyst approval and one-click execution. One platform. Alert to closed case. No SOAR required.
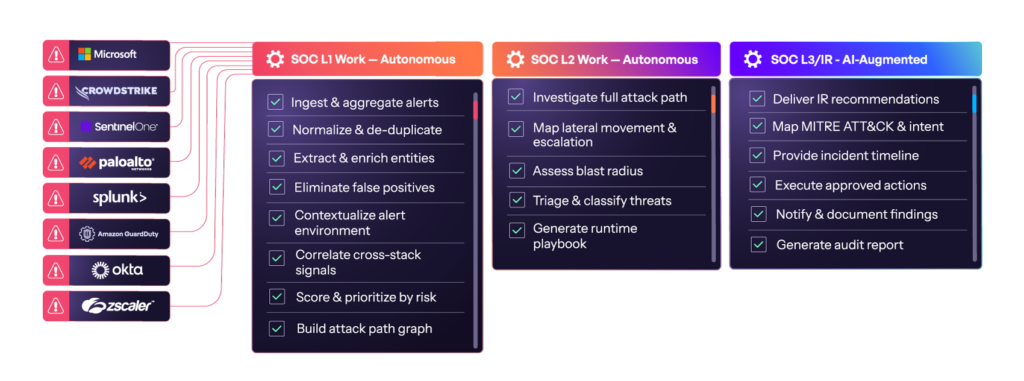
How Morpheus Works
From Alert to Closed Case — In One Platform
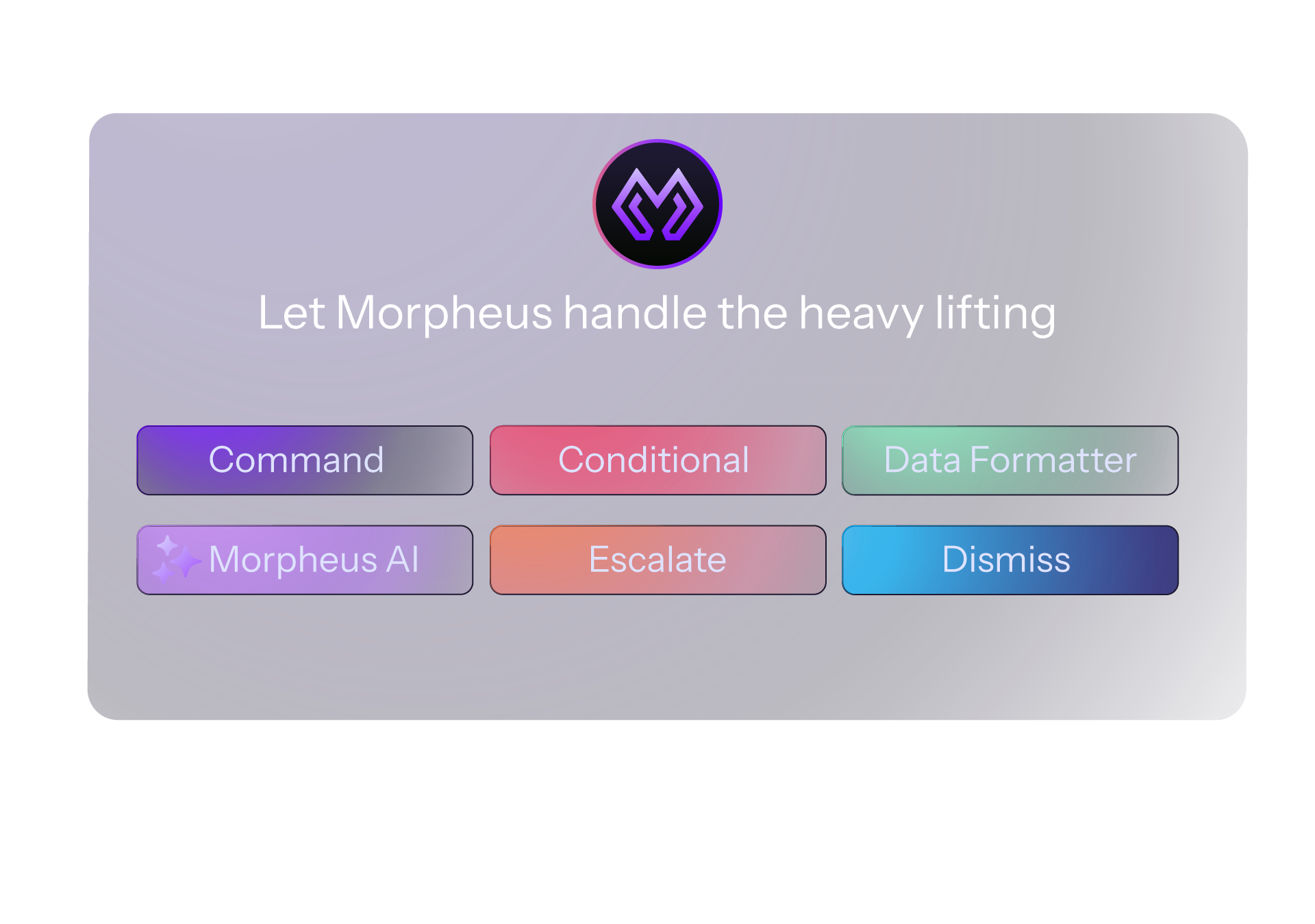
Autonomous Playbook Generation
No Playbooks to Build. No Playbooks to Maintain.
Legacy SOAR requires your engineers to build, test, and maintain every playbook in advance — then scramble to update them when threats evolve or APIs break. Morpheus eliminates that lifecycle entirely. The Morpheus SecOps LLM generates a tailored IR playbook for every incident at runtime — based on live alert context, your tool stack, and your SOC’s operational preferences. No authoring. No versioning. No 2 AM emergency updates.
Human-in-the-Loop IR
AI Does the Work. Your Analyst Makes the Call.
High-severity IR actions — isolating endpoints, suspending accounts, blocking IPs — are never executed autonomously. Morpheus stages the complete response workflow and presents it to your analyst: full investigation context, IR recommendations, and pre-built execution steps. One-click approval. Morpheus executes through trusted integrations. Every action logged, auditable, and reversible.
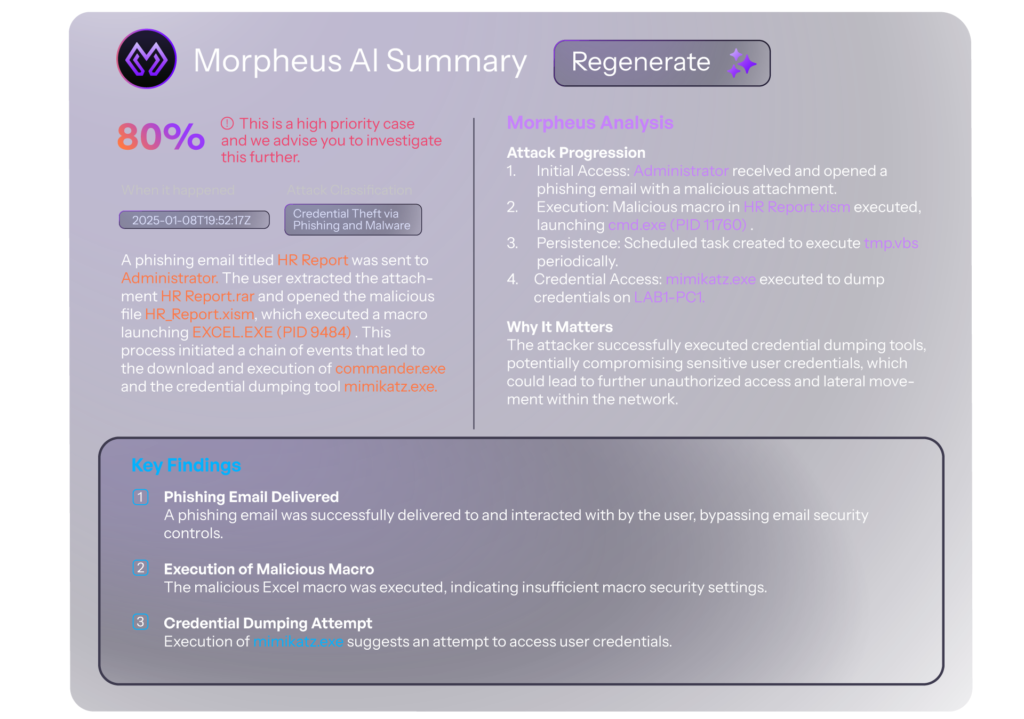
AI Incident Summaries
Every Incident Summarized. Before Your Analyst Opens It.
Morpheus condenses every investigation into a clear, structured incident summary — attack narrative, key findings, entity relationships, and recommended next steps — ready before your analyst touches the case. No manual write-ups. No context-switching. Everything needed to make a decision, in one place.
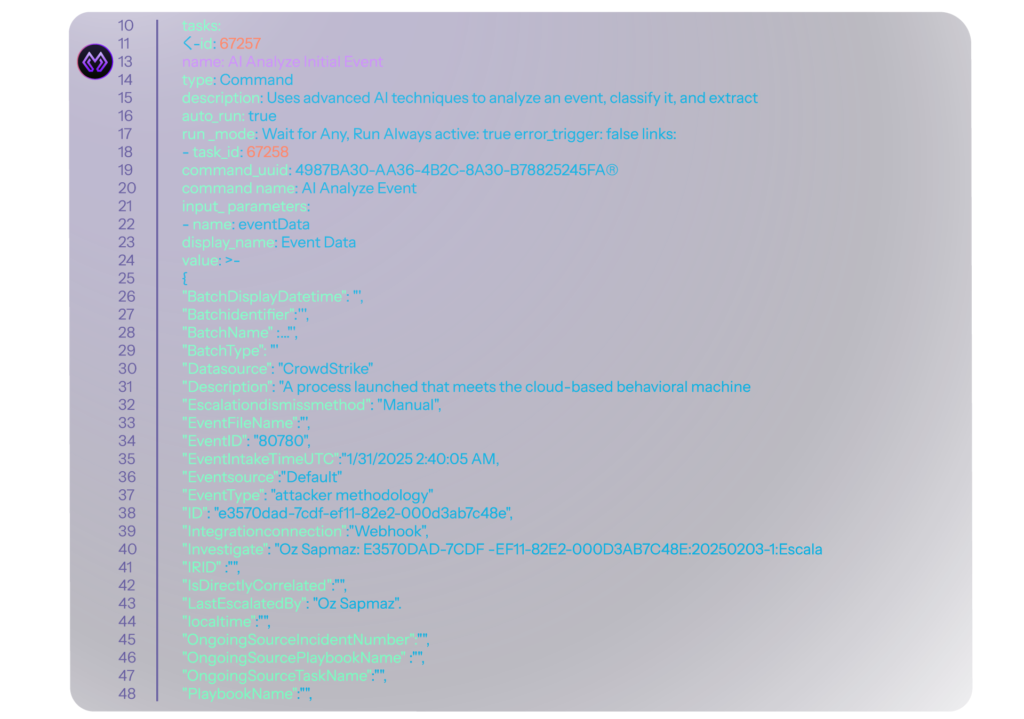
Full Transparency & Governance
Open Playbooks. No Black Boxes. Complete Audit Trail.
Every IR action Morpheus takes is visible, editable, and auditable. Playbooks are generated in open YAML — readable by your team, version-controlled via GitHub, and modifiable at any point. Every decision, recommendation, and execution step is logged from alert ingestion to case closure. Ready for your analyst, your CISO, your auditor, or your regulator.
Response in the Full Morpheus Workflow
Investigation. Triage. Response. One Platform.
Morpheus unifies the complete security operations workflow — from autonomous investigation through AI triage, runtime playbook generation, and human-approved response orchestration. Every step connected. Every action transparent. No SOAR required.
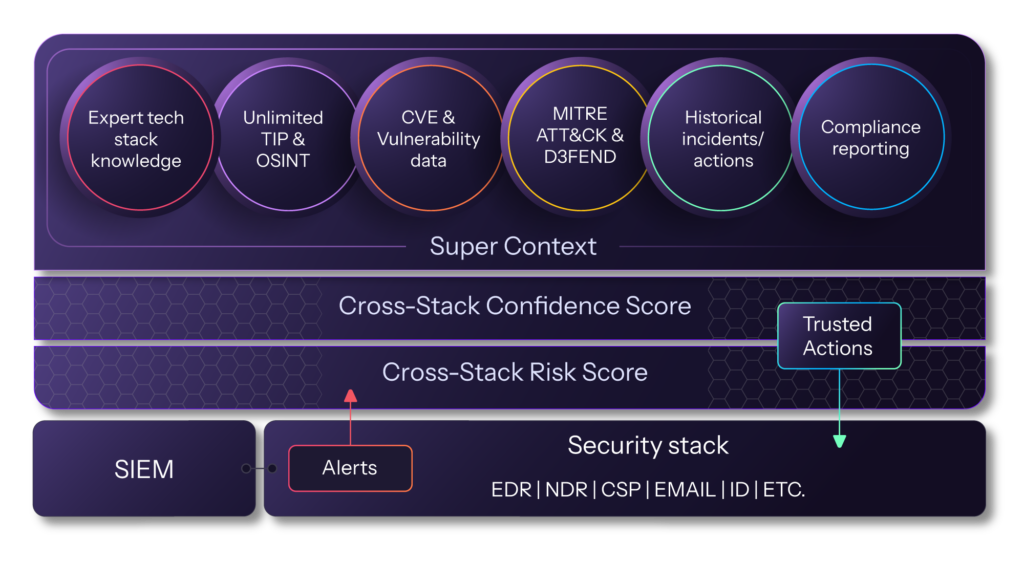
Morpheus ASOC provides an AI-driven, end-to-end security operations workflow that executes autonomous responses with optional human oversight.
From Alert to Closed Case: Morpheus vs. Legacy SOAR
| Stage | What Happens | Time (Manual) | Time (Morpheus AI) |
|---|---|---|---|
| Alert Triage | Classify severity and type | 15–30 min | Seconds |
| Investigation | Correlate signals across stack, reconstruct attack path | 1–4 hours | Under 5 min |
| Playbook Generation | Build response plan for the specific incident | Weeks to author and test | Generated at runtime |
| Analyst Review | Approve response actions with full context | 30–60 min (context-switching between tools) | One-click approval, pre-staged |
| Response Execution | Isolate, block, contain, remediate | 1–4 hours across fragmented tooling | Immediate via 800+ trusted integrations |
| Incident Summary | Document findings, actions, and audit trail | 30–90 min manual write-up | Auto-generated before analyst opens case |
AI YOUR SOC ✨
Alert to closed case. No second tool. No playbooks to build.
Learn More About AI Incident Response
Check out these resources on automated incident response and security orchestration.
-
6 Minutes and a Prayer: The Math That Proves Your SOC Is Gambling with Every Alert
This whitepaper presents a math-driven analysis that exposes an inconvenient truth hiding in plain sight across the cybersecurity industry.
-
Autonomous Investigation Compared: D3 Morpheus AI vs. Microsoft Security Copilot
We tested D3 Morpheus AI against Microsoft Security Copilot across three real attack scenarios. Morpheus found root cause in all three. Copilot found it in none. Read the full results.

-
Blending Deterministic Workflows with AI: Architecting the Enterprise and MSSP SOC of the Future
A blueprint for autonomy you can control. Learn how to blend deterministic precision with cognitive scale to autonomously triage 95% of alerts.

Common Questions
AI Incident Response and Security Orchestration — Explained.
Can Morpheus replace our existing SOAR platform?
Yes — and that’s the point. Morpheus includes built-in IR orchestration, runtime playbook generation, case management, and 800+ trusted integrations. Organizations migrating from Cortex XSOAR, Splunk SOAR, Tines, or Torq get autonomous investigation and AI triage on top of the orchestration capabilities they already depend on. One platform. No second tool required.
How is Morpheus different from AI SOC tools that still require SOAR?
Most AI SOC tools perform triage — then stop. The response still requires a SOAR underneath to execute. Morpheus autonomously investigates, triages, and generates the IR response plan, then executes it through trusted integrations with analyst approval. The entire workflow lives in one platform.
Does Morpheus autonomously execute high-severity IR actions?
No — and that’s deliberate. Morpheus autonomously handles investigation and triage. High-severity response actions — isolating endpoints, suspending accounts, blocking IPs — require explicit analyst approval. Every action is staged, reviewable, and executed through trusted integrations only after a human authorizes it.
What is runtime playbook generation?
Runtime playbook generation means Morpheus creates a tailored IR response playbook for each specific incident at the moment it occurs — based on live alert context, your tool stack, and your SOC’s preferences. No pre-built playbooks required. No maintenance burden. The response plan is always current, always relevant, and always generated fresh for each case.
How does Morpheus handle incident response for compliance-regulated environments?
Morpheus generates a complete audit trail for every incident — from alert ingestion through investigation, triage, response actions, and case closure. Every AI decision, analyst approval, and executed action is logged and timestamped. The structured case file is ready for your auditor, your regulator, or your legal team without additional documentation effort.
What integrations does Morpheus use for response execution?
Morpheus executes response actions through 800+ trusted integrations across SIEM, EDR, IAM, cloud, email, NDR, and DLP — including Microsoft Sentinel, CrowdStrike, SentinelOne, Okta, Palo Alto, and more. Self-healing integrations ensure connectors remain operational when vendors push API updates, so response execution never has a silent gap.
One Platform. Alert to Closed Case. No SOAR Required.
Autonomous investigation. AI triage. Human-approved response. Everything your SOC needs — nothing it doesn’t.
Your data. Your stack. Your results. No slideshow.