MORPHEUS AI SOC
Every Alert Investigated. Autonomously.
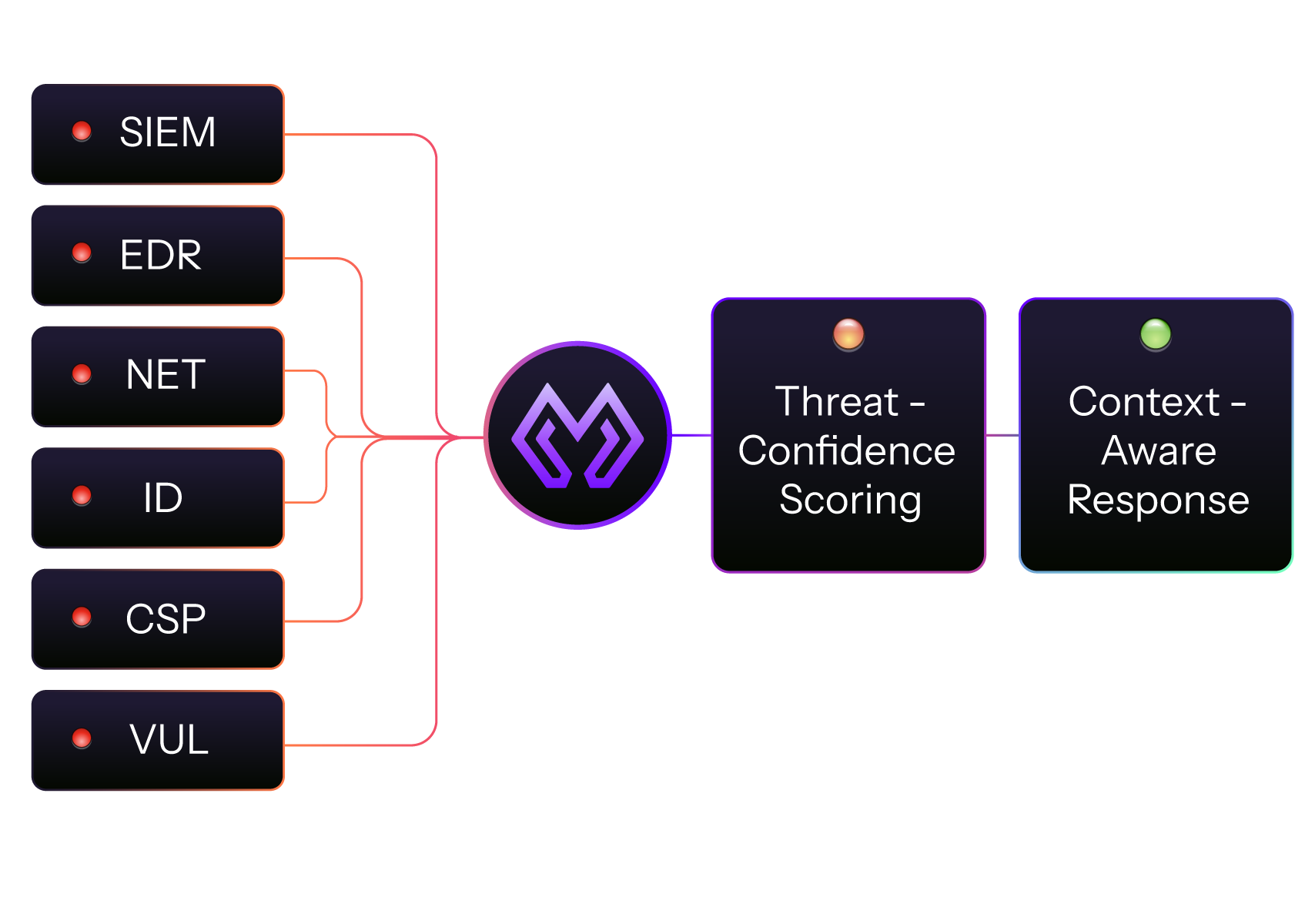
Morpheus is the AI SOC platform that traces every alert to its source — autonomously delivering L2+ investigation depth on every alert, sharpening every response decision, across your entire security stack.
100% Alert Coverage.
95% Triaged in Under 2 Minutes.
Morpheus investigates every alert like a world-class analyst — across every product in your stack.






Give Morpheus Your Alerts. Get Back Closed Cases.
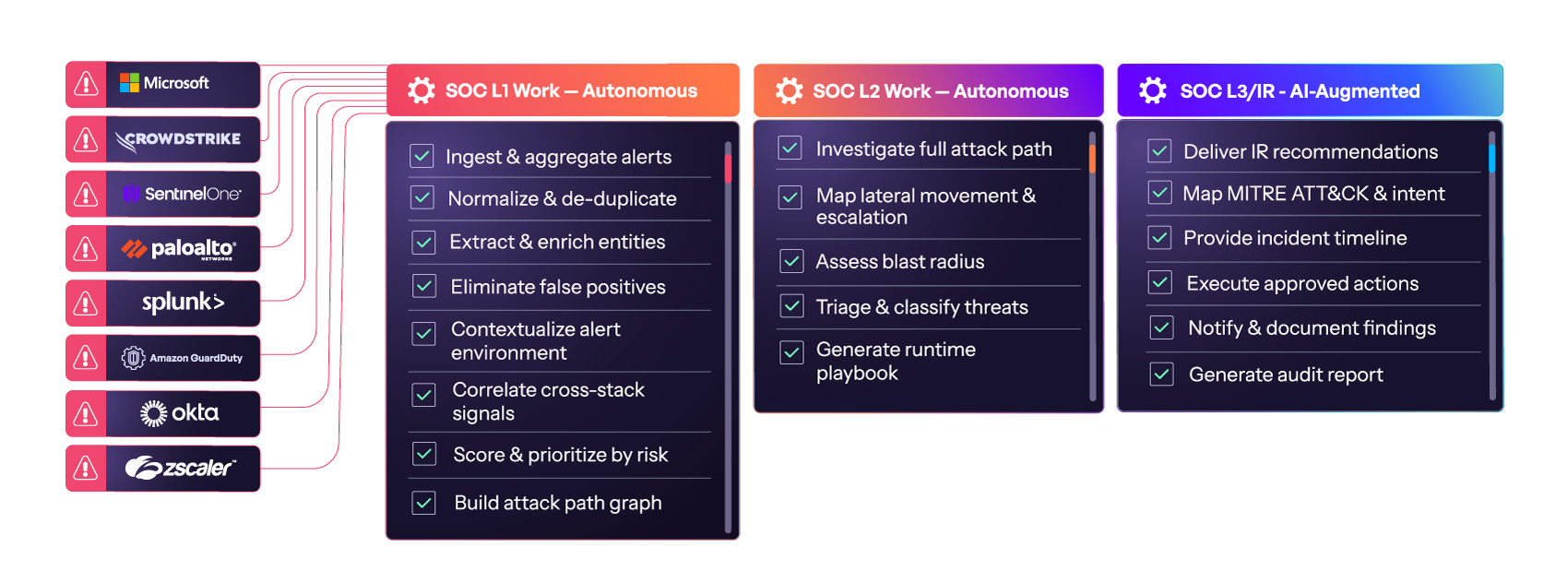
Morpheus AI SOC provides an autonomous, human-supervised security operations workflow — fully investigating every alert, generating response playbooks at runtime, and delivering structured case files ready for analyst review and approval.
A Different Approach to Security Automation.
| Dimension | Morpheus AI | Legacy Approach |
|---|---|---|
| AI Foundation | Purpose-built cybersecurity LLM trained on attacker TTPs and real IR data | Generic models or rule-based logic |
| Investigation Depth | L2+ investigation depth on every alert | Sample-based or manual analyst review |
| Stack Coverage | Traces context across your entire stack and back through time | Siloed tools, manual correlation |
| Integration Maintenance | Self-healing integrations, zero engineering maintenance burden | Dedicated engineering effort for break/fix |
| Investigation Output | Attack path, risk score, MITRE mapping, and IR recommendations | Raw alerts, minimal context |
| Playbooks | Autonomously generated at runtime per incident | Static, hand-coded, require ongoing maintenance |
One Platform. Alert to Closed Case.
Morpheus unifies autonomous investigation, AI triage, and governed response orchestration in a single platform — replacing legacy SOAR, eliminating playbook maintenance, and delivering L2+ investigation depth on every alert.
Morpheus AI Investigation
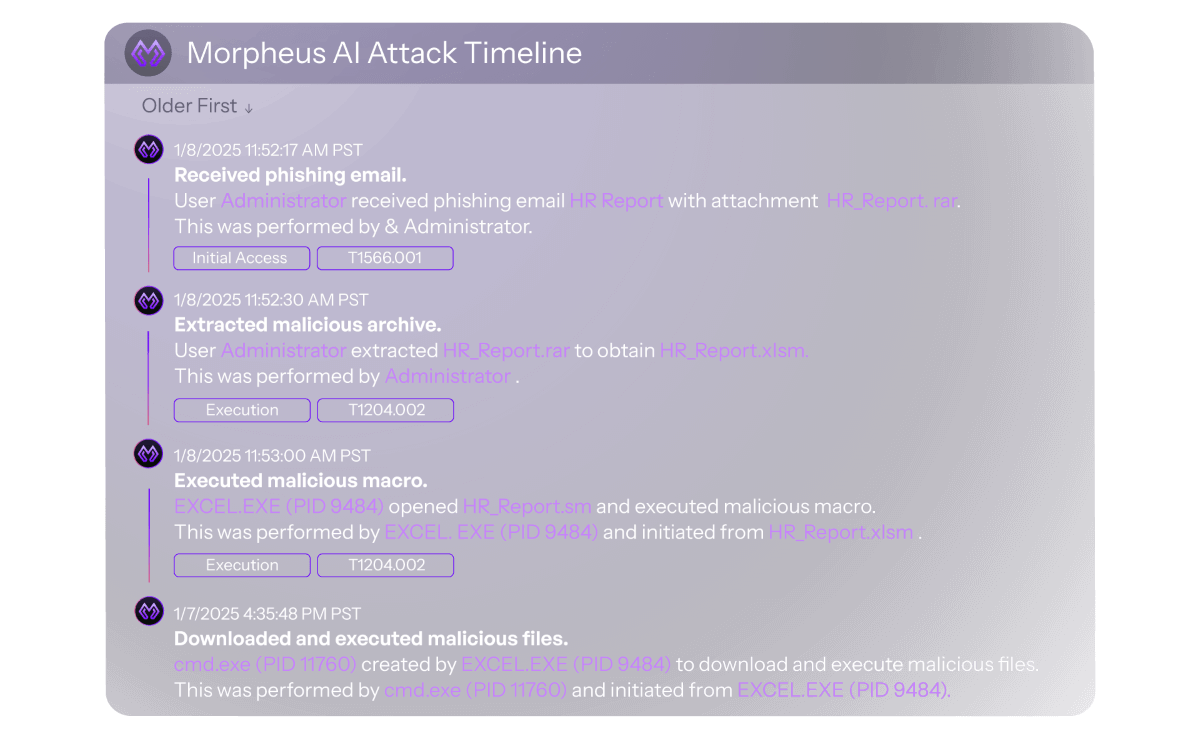
Attack Path Discovery traces every alert horizontally across your existing security stack and vertically through time — mapping lateral movement, privilege escalation, and blast radius before your analyst opens the case.
Morpheus AI Triage
A purpose-built cybersecurity LLM — trained over 24 months by 60 specialists — separates real threats from noise, generates full-stack risk scores, and adapts to your environment the longer it runs.
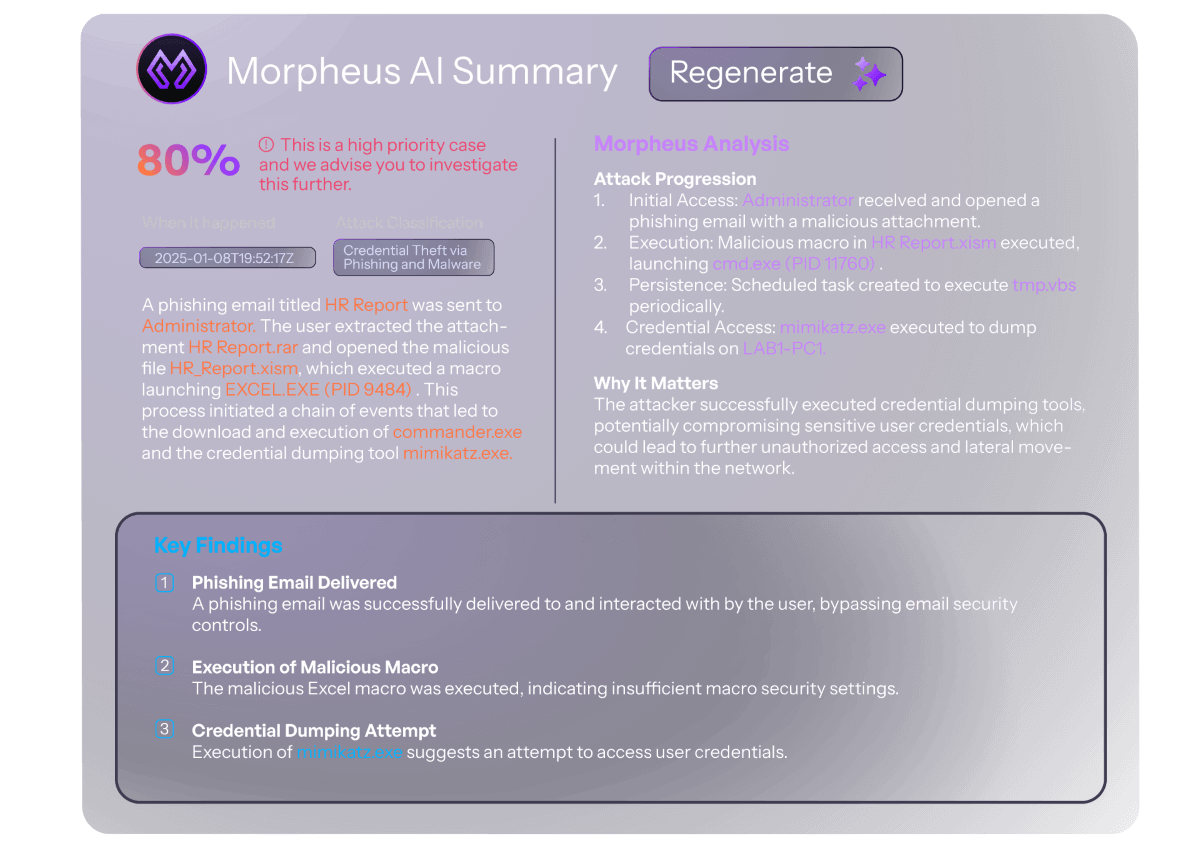
Morpheus AI Response
Contextual playbooks generated at runtime. Your team approves. Morpheus executes — with full audit trail, rollback capability, and human-in-the-loop governance at every step.
AI YOUR SOC ✨
Every alert. Fully investigated. In under 2 minutes.
Everything You Need for Autonomous Investigation, Triage and Response.
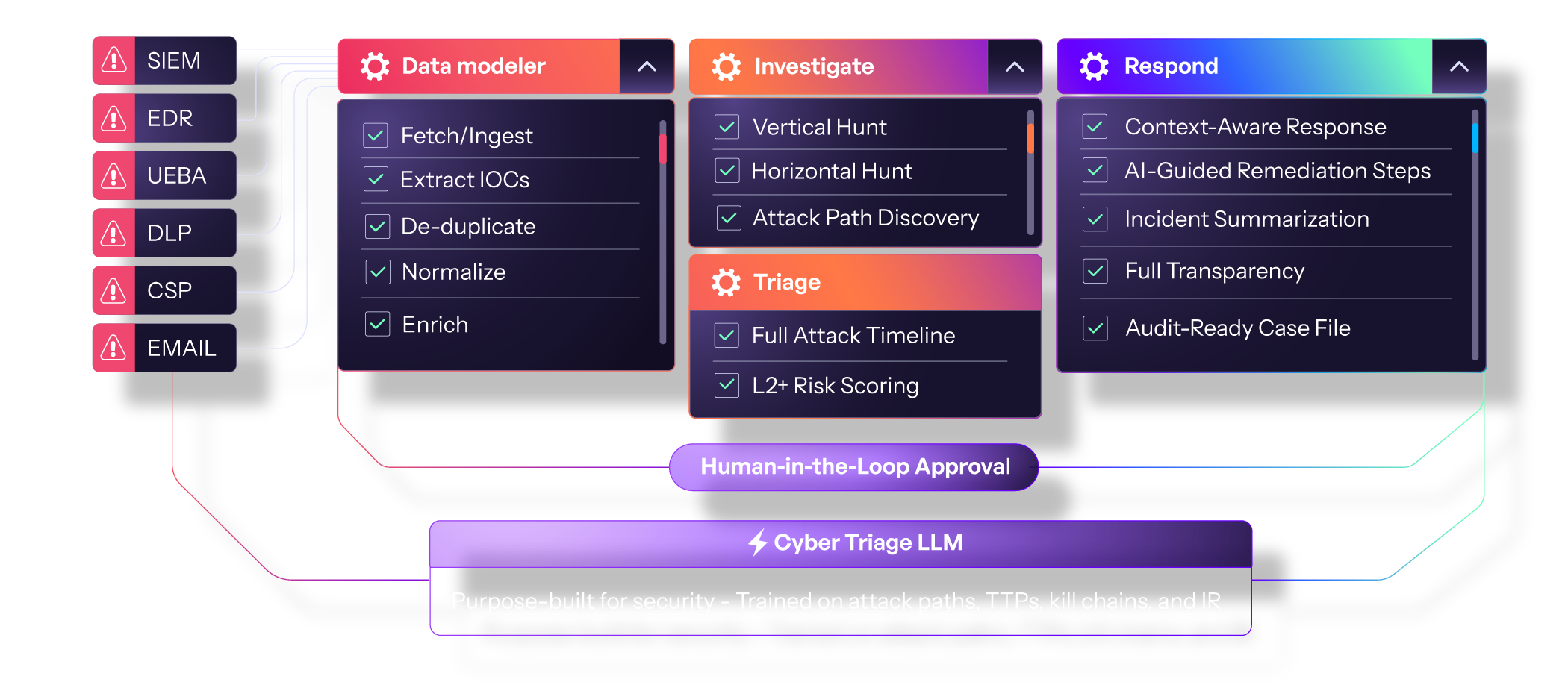
Morpheus connects to your existing security stack and autonomously handles the entire alert lifecycle — from ingestion to response. Its purpose-built Cyber Triage LLM normalizes data, maps full attack paths, and delivers L2-level triage in under two minutes. Human-in-the-loop approval gates keep high-impact actions under analyst control.
Deep Thinking Features for Every Stage of the Alert Lifecycle
| Phase | Key Capabilities | Outcome |
|---|---|---|
| Alert Ingestion | Centralizes alerts from SIEM, EDR, IAM, cloud, email, NDR, DLP | Every alert vetted, normalized, and queued — none left behind |
| Attack Path Discovery | Hunts horizontally across your stack and vertically through time | Complete attack path reconstructed from initial access to objective |
| Autonomous Triage | Purpose-built cybersecurity LLM analyzes every alert in full context | L2+ investigation depth, genuine threats separated from noise |
| Runtime Playbook Generation | Generates tailored response playbooks per incident at runtime | No playbooks to build or maintain |
| Full-Stack Timeline | Compiles chronological timeline of the complete attack lifecycle | Analyst-ready timeline with no manual reconstruction |
| Risk Score Prioritization | Scores alerts on impact, threat confidence, contextual weight, mitigation status | Analysts always know which cases need immediate attention |
| Incident Summarization | Produces structured case file with MITRE mapping and evidence chain | Written for analyst, CISO, or auditor — ready on delivery |
| Guided IR Recommendations | Delivers actionable IR recommendations tailored to each incident | Analyst reviews, approves, and executes in one click |
| Self-Healing Integrations | Monitors 800+ connections, detects API drift and generates corrective code | No ticket, no engineer, no coverage gap |
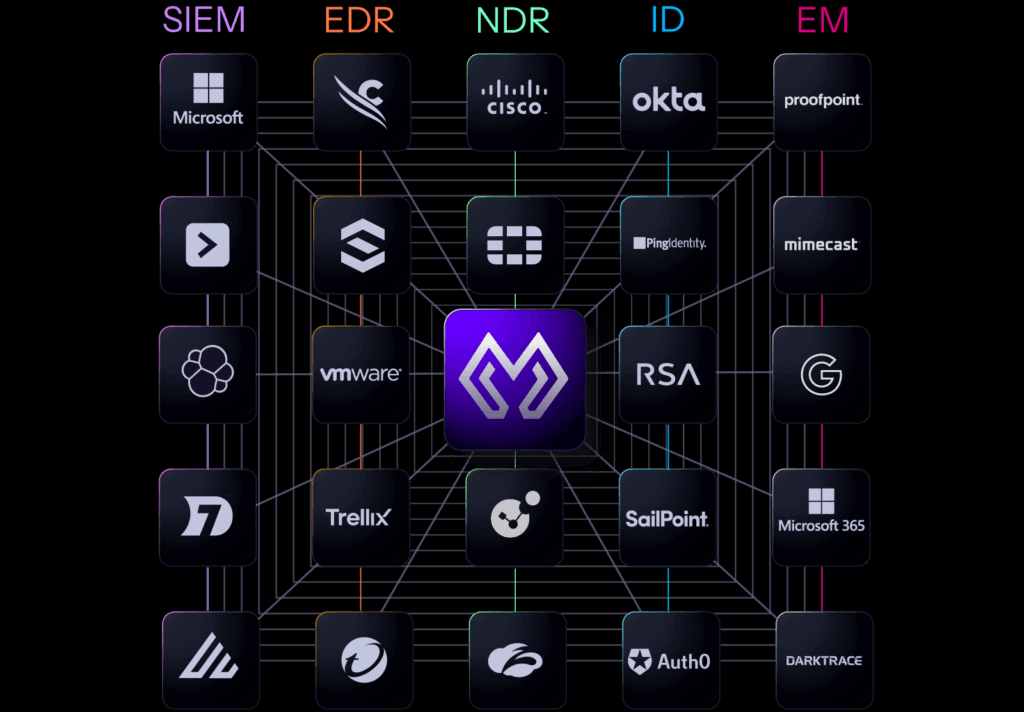
Works With Your Existing Security Stack. Doesn’t Replace It.
Morpheus sits on top of your existing security infrastructure — vendor agnostic, no rip-and-replace. 800+ integrations across SIEM, EDR, IAM, cloud, email, NDR, and DLP, with self-healing connectors that adapt automatically when your vendors push updates.

Don’t Take Our Word for It.
Take Theirs.
“We completely elevated our security operations capabilities with D3. It’s our primary platform for cyber security investigations, incident response and case management.”

“It solved our problems right out of the box. We are reducing our workload by having intelligent, dynamic playbooks and commands. Of course, this has saved us a ton of time.”
“We have a complete picture of alerts, and which ones represent the most danger. We’re doing a lot of proactive automated threat hunting to make sure we’re keeping our risk low.”
“Our SOC data is exponential. So being able to ingest it all into D3 and get that level of automation is amazing.”

“Automating response has drastically reduced IR times and freed our team to focus on proactive threat hunting and strategy. It’s an indispensable asset in our SecOps arsenal, delivering both immediate and long-term value.”

“We ingest very quickly and filter out the false from the true positives. D3 really helped the team get rid of alert fatigue, with super actionable alerts.”

“It allows us to build and run agnostic, dynamic playbooks. We can integrate easily with any vendor to perform tasks and control what/when actions can be taken.”
“A game changer for our org with automation. We’ve streamlined response, reducing manual efforts and improving efficiency. The interface makes it easy to prioritize incidents.”

“The noise reduction within the SOC has been incredible. We saw 145,000 alerts within our XDR platform reducing down to only 200 alerts that required analyst actioning, for an entire month. That’s a 99% reduction.”

“The problem is that there’s too much information. D3 gives us greater correlation, context, and more effective AI, so we can find things faster, remediate faster.”

“In the journey to scale, our existing team has turned from fully reactive to about 70 percent proactive at this point because of the automations we’ve built with D3.”

“Having D3 allows us to get the noise out of the way, automate level I and II analysis, and focus on what is important.”

Learn More About Morpheus
Check out these resources to answer your questions about our other cutting-edge capabilities.
-
6 Minutes and a Prayer: The Math That Proves Your SOC Is Gambling with Every Alert
This whitepaper presents a math-driven analysis that exposes an inconvenient truth hiding in plain sight across the cybersecurity industry.
-
Autonomous Investigation Compared: D3 Morpheus AI vs. Microsoft Security Copilot
We tested D3 Morpheus AI against Microsoft Security Copilot across three real attack scenarios. Morpheus found root cause in all three. Copilot found it in none. Read the full results.

-
Blending Deterministic Workflows with AI: Architecting the Enterprise and MSSP SOC of the Future
A blueprint for autonomy you can control. Learn how to blend deterministic precision with cognitive scale to autonomously triage 95% of alerts.

faqs
Common Questions
Everything buyers ask before an Autonomous AI SOC demo. If you don’t see your question here, we’ll answer it live.
What is an AI SOC platform?
An AI SOC platform uses artificial intelligence to autonomously investigate, triage, and respond to security alerts across an organization’s entire tool stack. Unlike legacy SOAR platforms that depend on static playbooks, AI SOC platforms apply specialized LLMs to analyze alerts in context, correlate signals across tools and time, and deliver complete investigation findings with minimal human intervention. D3 Morpheus delivers L2+ investigation depth on every alert using Attack Path Discovery and a purpose-built cybersecurity triage LLM.
What is the difference between SOAR and an AI SOC?
SOAR platforms are workflow engines — they execute predefined playbooks that must be manually built, tested, and maintained. When integrations break or threats evolve, the playbooks fail. An AI SOC platform like D3 Morpheus eliminates the playbook dependency. Morpheus generates contextual playbooks at runtime, adapts to new threat patterns without human scripting, and uses self-healing integrations to maintain connectivity automatically.
What is Attack Path Discovery?
Attack Path Discovery is an AI-driven investigation methodology developed by D3 Security that traces the full sequence of an attack across an organization’s environment. Rather than examining each alert in isolation, it follows threats horizontally across tools (lateral movement) and vertically through time (privilege escalation, persistence), reconstructing the complete attack path from initial access through objective completion.
What are self-healing integrations?
Self-healing integrations continuously monitor every connection between Morpheus and an organization’s security tools. When a vendor pushes an API update, changes a schema, or rotates credentials, self-healing integrations detect the drift and generate corrective code without human intervention — eliminating the integration maintenance burden that makes traditional SOAR so expensive to operate.
Can D3 Morpheus replace our SOAR?
Yes. Morpheus includes built-in orchestration, case management, playbook generation, and response execution in a single platform. Organizations migrating from Cortex XSOAR, Splunk SOAR, Tines, or Torq can deploy Morpheus on top of their existing detection stack with 800+ out-of-the-box integrations.
Is D3 Morpheus suitable for MSSPs?
Morpheus is built for MSSP-scale operations with native multi-tenancy, complete data isolation, segregated client views, and client-specific configurations. MSSPs of all sizes and stripes, in many regions across the world, rely on D3.
What tools does Morpheus integrate with?
Morpheus integrates with over 800 security tools across SIEM, EDR, IAM, cloud, email, NDR, and DLP — including Microsoft Sentinel and Defender, Splunk, CrowdStrike, SentinelOne, Palo Alto, Okta, Fortinet, and Elastic. No rip-and-replace. Morpheus sits on top of your existing stack. For Microsoft environments, Morpheus ships on Azure and is purchasable with Azure Marketplace credits.
Threats Don’t Wait. Neither Should You.
Every hour spent maintaining playbooks, babysitting integrations, and rubber-stamping alerts is an hour an attacker uses to move deeper into your environment.
Your data. Your stack. Your results. No slideshow.