D3 Security’s Smart SOAR (security orchestration, automation, and response) is a powerful platform designed to unify disparate security tools and streamline incident response workflows. One of the most widely used tools in the cybersecurity ecosystem is Microsoft’s Active Directory (AD), a centralized directory service that manages user authentication, authorization, and other critical network functions. In this article, we’ll explore how integrating Active Directory with Smart SOAR enables use-cases beyond traditional security automation.
The Benefits of Active Directory Integration in Smart SOAR:
Streamlined User Management
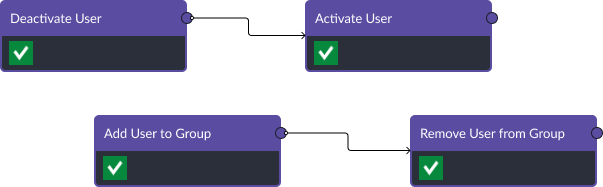
By integrating Active Directory with Smart SOAR, security teams can streamline user management and access control. This allows for faster and more efficient user provisioning, deprovisioning, and password resets. Additionally, it ensures that user accounts are consistently managed across all integrated security tools, reducing the risk of unauthorized access and data breaches.
Automated Incident Response
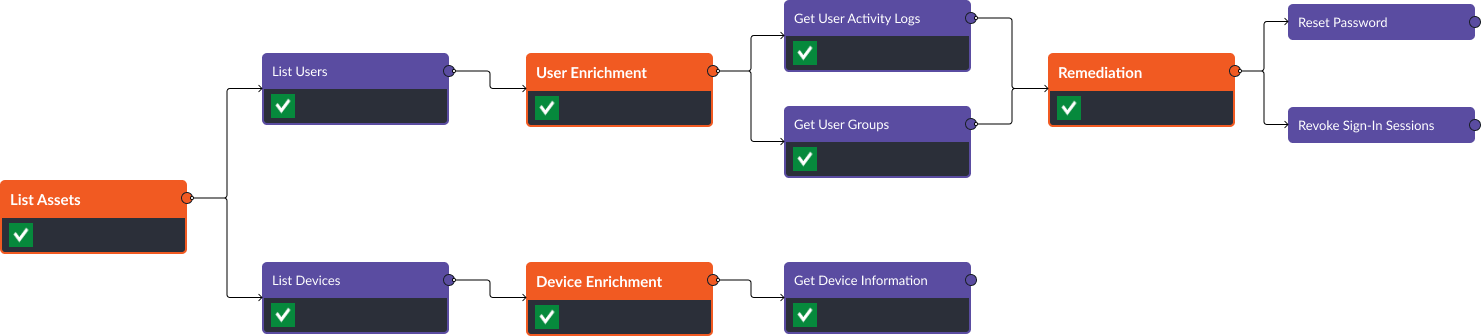
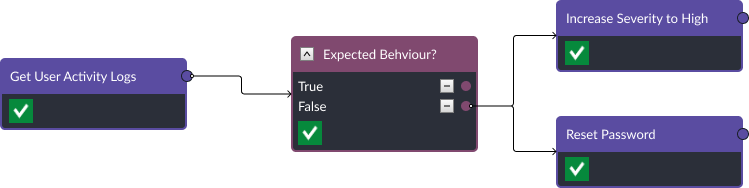
When an incident is detected, Smart SOAR can leverage Active Directory to automatically gather relevant user information and perform actions such as disabling accounts, resetting passwords, or revoking access to sensitive resources. This not only reduces the time to respond to security incidents but also minimizes the risk of human error in critical situations.
Enhanced Visibility
Integrating Active Directory with Smart SOAR provides security teams with enhanced visibility into user activities and potential security risks. By correlating user data from Active Directory with other security tools, analysts can quickly identify suspicious behavior, detect potential insider threats, and proactively respond to security incidents.
Conclusion
Smart SOAR’s integration with Active Directory is a powerful way to enhance your organization’s security posture, streamline operations, and ensure the consistent application of security policies across all integrated tools. By automating incident response workflows, simplifying user management, and providing enhanced visibility into user activities, organizations can turn siloed tools into a unified ecosystem that works together to minimize the impact of individual security incidents.




