What an Autonomous SOC Platform Actually Is, and Why Static Playbooks Are Hitting Their Ceiling
The numbers tell the story before any argument does.
The average enterprise SOC receives 4,484 security alerts per day from 28+ tools. Analysts spend 70 minutes investigating a single alert. Fifty-six minutes pass before anyone even looks at it. According to Devo’s 2024 SOC Performance Report, 53% of those alerts are false positives. And nearly half of all alerts? They’re never investigated at all.
This isn’t a process failure. It’s a capacity failure. And it’s getting worse.
ISC2’s 2025 Cybersecurity Workforce Study counts 4.8 million unfilled cybersecurity positions globally. Among the analysts who are working, 71% report burnout and one-third are considering leaving. Annual SOC analyst turnover runs 15–25%.
SOAR platforms were supposed to fix this. They didn’t.
Where SOAR Hit Its Ceiling
Security Orchestration, Automation and Response (SOAR) platforms introduced playbook-driven automation starting around 2015. The idea was sound: connect security tools through APIs, define response workflows, and reduce manual investigation time.
The reality proved more complicated. Playbooks required constant maintenance. Integrations broke every time a vendor updated its API. The engineering overhead to build and maintain playbooks often exceeded what security teams could sustain. Both Gartner and Forrester retired their dedicated SOAR evaluations by 2025, a clear signal that the standalone SOAR category reached its ceiling.
AI-augmented copilots improved things incrementally starting around 2022. Analysts could query security data in natural language, get enrichment suggestions, and receive summarized incident reports. But the human still initiated every investigation and made every decision. The bottleneck remained.
Enter the Autonomous SOC
An autonomous SOC platform replaces the static playbook model with agentic AI that reasons through investigations independently. When a phishing alert arrives, the system doesn’t follow a pre-built decision tree. It analyzes email headers, checks sender reputation, inspects URLs and attachments, correlates with endpoint telemetry, traces lateral movement, and produces a structured investigation report. Minutes, not hours.
Five capabilities define a genuine Autonomous SOC platform:
Agentic investigation. The platform reasons dynamically through each alert, adapting its approach based on evidence discovered, not pre-defined playbook steps.
Cross-stack correlation. Threats traverse email, endpoints, identity, cloud, and network. The platform correlates horizontally across the entire security stack, including tools beyond the one that generated the alert.
Contextual response generation. Playbooks are generated at runtime based on the specific incident, the customer’s tool stack, and organizational policies. No authoring. No versioning.
Self-maintaining integrations. When vendor APIs change, the platform detects the drift and generates corrective code autonomously, eliminating SOAR’s most persistent failure mode.
Human-in-the-loop governance. Every AI decision is explainable, auditable, and overridable. Analysts review reasoning, approve actions, and provide feedback that improves future performance.
What D3 Morpheus AI Brings to This
D3 Security’s Morpheus AI is built on a purpose-built cybersecurity LLM developed over 24 months by 60 specialists — red teamers, data scientists, AI engineers, and SOC analysts. Unlike general-purpose LLMs adapted for security, this model understands how attacks propagate across tools and time at a foundational level.
On every alert, Morpheus AI performs multi-dimensional correlation: vertical deep inspection into the origin tool and horizontal correlation across the full security stack. It maps telemetry to D3’s proprietary attack path discovery graph, producing structured investigation reports in minutes.
Morpheus AI generates bespoke playbooks at runtime, heals its own integrations across 800+ tools when APIs drift, includes a full built-in SOAR engine for teams that want to run static and autonomous models simultaneously, and offers flat-rate pricing with no token fees.
The Honest Caveats
No Autonomous SOC eliminates the need for human analysts. “Autonomous” describes the investigation model, not the governance model. LLMs can hallucinate. Over-reliance on automation risks skill erosion over time. Gartner’s 2025 research explicitly recommends treating AI SOC agents as augmentation tools with human oversight, and that’s the right framing.
The question isn’t whether to adopt an Autonomous SOC platform. It’s whether your current model can keep pace with 4,484 alerts per day when half your team is burned out and your playbooks were written for last quarter’s threat landscape.
What to Do Next
Measure your current alert-to-investigation ratio, MTTR, and false positive rate. Map which tools generate the most alerts. Then evaluate an Autonomous SOC platform against your actual data, because the value is measurable.
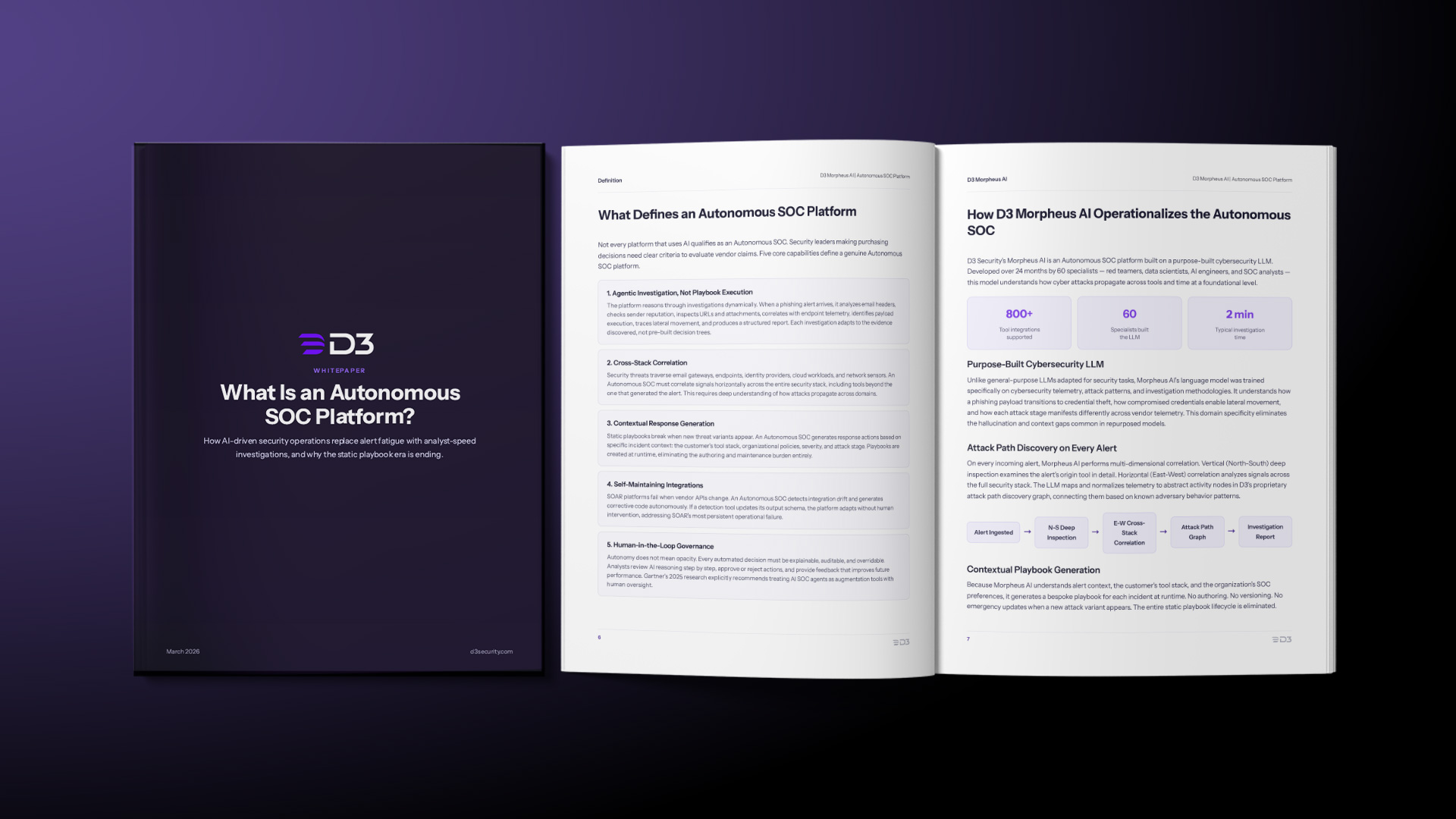
For a deeper dive into the research, competitive landscape, and evaluation framework, read the full whitepaper: What Is an Autonomous SOC Platform?