67% of SIEM alerts go uninvestigated every day. Tuning your rules trades visibility for quiet. AI alert triage offers a third option: investigate everything, escalate only what matters.
uninvestigated
triaged at all
tenure (burnout)
The Math That Breaks Every SOC
Enterprise SIEMs generate over 100,000 alerts per day. The average SOC has 5 to 10 analysts. At 40 alerts per hour, a single analyst investigates about 320 alerts in an 8-hour shift. To cover 100,000 alerts manually would require 312 analysts working non-stop.
No one has 312 analysts. So most organizations do the next best thing: they tune.
They raise severity thresholds. They suppress alert categories. They add exclusion lists. The queue shrinks. The dashboard looks calmer. But every suppressed alert is a detection you paid to build and then chose to ignore.
How Do I Reduce False Positives Without Replacing My SIEM?
This is the most common question security leaders ask when evaluating their SIEM strategy. The answer is not better rules. It is a different layer entirely.
D3 Security’s Morpheus AI is an AI Autonomous SOC platform that sits beside your SIEM—not on top of it, not instead of it. It queries your SIEM through native APIs, collects context from your EDR, identity provider, cloud security tools, and other sources, then investigates every alert autonomously.
The result: alert volume drops 70–90%. Not because alerts are suppressed, but because Morpheus AI resolves them. It delivers a verdict—true positive, false positive, or needs human review—with the investigation evidence to back it up. Analysts receive confirmed threats, not noise.
What Changes With AI Alert Triage
| Metric | Before Morpheus AI | After Morpheus AI |
|---|---|---|
| Alerts investigated | ~33% (manual) | 100% (autonomous) |
| Triage time per alert | 15–30 minutes | <2 minutes |
| Alerts escalated to analysts | All surviving alerts | ~5–10% (confirmed threats) |
| Analyst time on Tier-1 triage | 60–70% of shift | 5–10% of shift |
| Threat hunting time | 5–10% of shift | 25–30% of shift |
| MTTR | 4–24 hours | Under 20 minutes |
| SIEM replacement required | — | No |
Why SIEM Tuning Alone Makes the Problem Worse
Every tuning approach carries a hidden cost that accumulates over time:
| Tuning Approach | Hidden Cost |
|---|---|
| Raise severity thresholds | Low-severity alerts indicating early reconnaissance become invisible; kill-chain blind spots emerge |
| Add exclusion lists | Lists go stale; compromised assets remain trusted while attackers pivot through them |
| Suppress alert categories | Entire detection investments abandoned; reactivation after a breach is slow and costly |
| Widen correlation windows | Slow-and-low attacks deliberately space activity to avoid time-based detection |
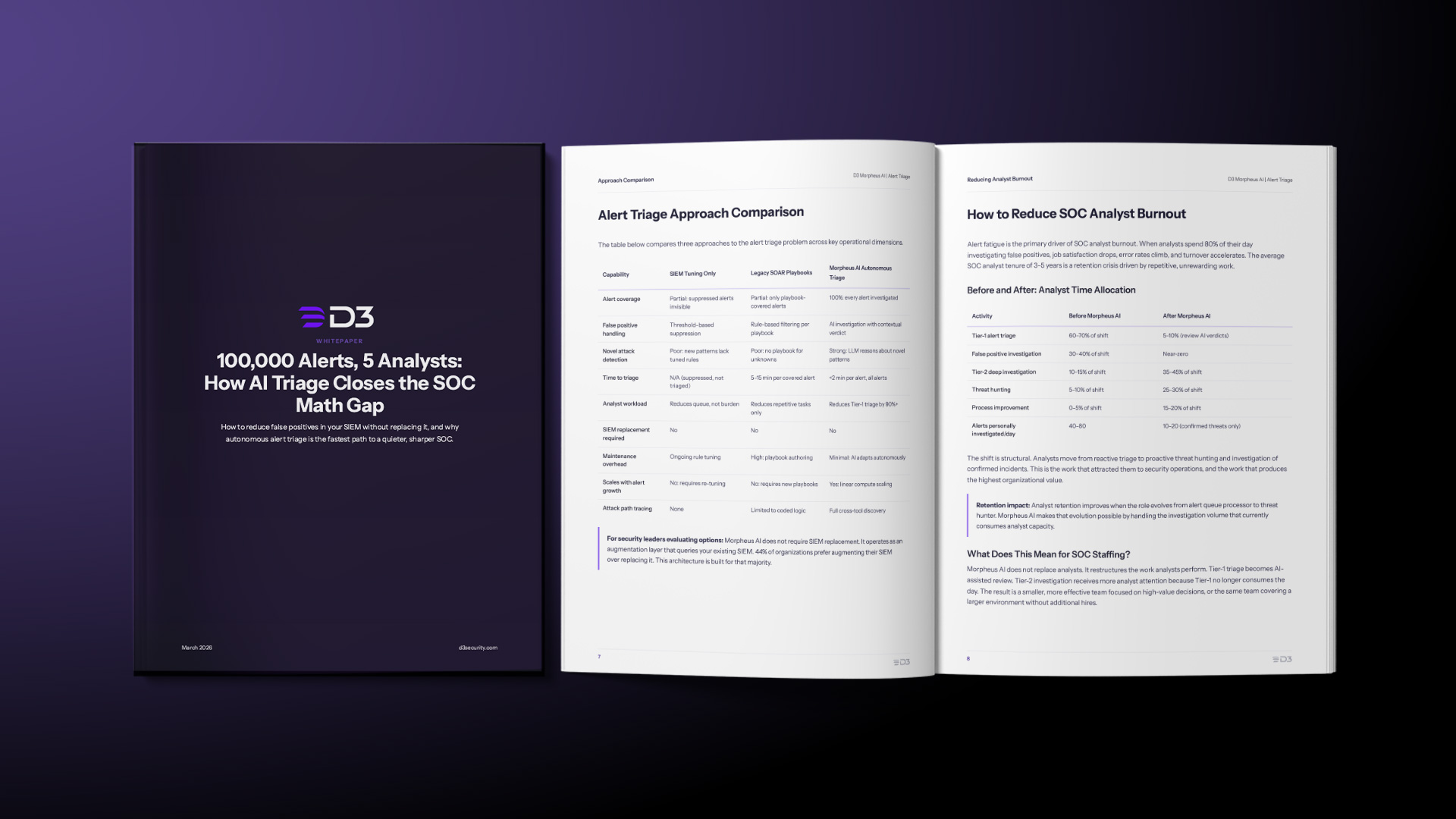
SIEM Tuning vs. Legacy SOAR vs. AI Autonomous Triage
| Capability | SIEM Tuning | Legacy SOAR | Morpheus AI |
|---|---|---|---|
| Alert coverage | Partial | Partial | 100% |
| Novel attack handling | Poor | Poor | Strong (LLM reasoning) |
| Maintenance | Ongoing tuning | High (playbooks) | Minimal (AI adapts) |
| Scales with growth | No | No | Yes |
| Attack path tracing | None | Limited | Full cross-tool |
| SIEM replacement | No | No | No |
What Deployment Looks Like
Morpheus AI connects to your SIEM via native APIs. No log migration, no detection rule rewrite, no disruption to existing workflows.
| Phase | Duration | What Happens |
|---|---|---|
| Connect | 1–2 days | API integration with SIEM and security stack |
| Baseline | 5–7 days | Pattern observation and confidence calibration |
| Shadow Mode | 7–14 days | Parallel triage with accuracy validation |
| Production | Day 14+ | Full autonomous triage with analyst review |
Total time to value: 2–4 weeks. Works with Splunk, Microsoft Sentinel, IBM QRadar, Elastic SIEM, Google Chronicle, and others.
The Bottom Line
You do not need to replace your SIEM to solve the false positive problem. 44% of organizations prefer augmenting their SIEM over replacing it. Morpheus AI is built for exactly that: it queries your SIEM, investigates every alert autonomously, and delivers confirmed threats to your analysts instead of noise.
The SOC math problem is real. Tuning cannot solve it. Hiring cannot solve it. Autonomous AI investigation can.
Read The Whitepaper: 100,000 Alerts, 5 Analysts: How AI Triage Closes the SOC Math Gap




