Executive Summary
Anthropic’s Mythos is about to change the economics of vulnerability discovery permanently. In its preview release through Project Glasswing, Mythos identified thousands of previously unknown zero-day vulnerabilities across every major operating system, browser, and enterprise application. Over 99% remain unpatched. When Mythos reaches general availability, SOC teams will face a volume and complexity of vulnerability findings that no existing manual process can absorb.
Mythos is only the first wave. The same AI capabilities that make Mythos effective are available to every major AI lab, security vendor, and research team. Within 12 to 24 months, multiple LLMs will be producing vulnerability reports at machine speed. The industry is entering an era where vulnerability discovery permanently outpaces human triage capacity.
This paper examines the Mythos problem from three angles: the immediate operational burden on SOC teams, the compounding effect as more AI models follow Mythos into vulnerability discovery, and the autonomous triage architecture required to process Mythos-scale findings without burning out the analysts who are already at capacity.
D3 Security’s Morpheus AI, the AI-driven autonomous SOC platform, already processes vulnerability reports through its attack path discovery framework, correlating findings by CVE and device across 800+ integrated security tools. When Mythos reaches general availability, Morpheus AI will be fully prepared to ingest, investigate, and prioritize Mythos vulnerability findings using the same customizable LLM framework that today handles 100% of security alerts at L2+ analyst depth.
Pre-release advisory
Mythos has not yet reached general availability. Morpheus AI currently processes vulnerability reports from scanners including InsightVM and Qualys through its attack path discovery framework. The capabilities described in this paper reflect Morpheus AI’s existing architecture applied to the data structures Mythos is expected to produce. Deep Mythos integration is on D3 Security’s product roadmap. The operational constraints Mythos will impose are foreseeable, quantifiable, and plannable. Organizations that build autonomous Mythos triage capacity before launch will absorb the impact. Those that wait will face a backlog they cannot clear.
Table of Contents
- What Mythos Means for Vulnerability Management
- The Time Burden: Quantifying the Mythos SOC Impact
- The Multi-LLM Vulnerability Landscape
- Why Static Triage Fails at Mythos Scale
- The Autonomous SOC: Matching Mythos Discovery Speed
- How Morpheus AI Processes Mythos Vulnerability Findings
- Bespoke Mythos Triage: Every Organization Is Different
- A Readiness Framework for the Post-Mythos Landscape
- Questions for Your Evaluation
What Mythos Means for Vulnerability Management
For decades, vulnerability discovery has been bottlenecked by human effort. A researcher spends weeks analyzing a single codebase, files a CVE, and vendors patch it over a coordinated timeline. The entire industry, staffing models, triage workflows, patch schedules, is built around the assumption that new vulnerabilities arrive at a pace humans can process. Mythos ends that assumption.
Anthropic’s Project Glasswing demonstrated that a purpose-trained AI model can scan major software stacks and surface thousands of high-severity zero-days in a timeframe that would take human researchers decades to match. Each Mythos finding arrives with structured, detailed triage data far richer than a standard CVE advisory.
Mythos Triage Reports vs. Traditional CVE Advisories
| Data Element | Traditional CVE Advisory | Mythos Triage Report |
|---|---|---|
| Vulnerability detail | Description, affected versions, CVSS score | Code-level analysis pinpointing the vulnerable function and execution context |
| Exploitation data | Proof-of-concept (if public) | Ordered exploitation steps for tested applications |
| Priority assessment | CVSS score only | AI-assessed severity accounting for real-world exploitability |
| Verification | Vendor confirmation (often delayed) | Automated verification agent results confirming exploitability |
| Validation | Community peer review | Human expert validation loop before disclosure |
| Arrival pattern | Trickle: 50–200 relevant findings/month | Flood: thousands at disclosure + ongoing daily stream |
The Richness Problem: Why Better Data Makes Triage Harder
Counterintuitively, the quality of Mythos findings compounds the SOC time burden. A bare CVE advisory takes an analyst 15 to 30 minutes to triage. A Mythos report, with exploitation steps, code-level context, and verification results, demands 45 to 90 minutes of deeper analysis. Each finding contains the detail that would normally justify a full investigation. Multiply that across thousands of Mythos findings and the analyst workload becomes physically impossible without automation.
The Mythos paradox
Mythos produces the best vulnerability data the industry has ever seen. That same richness makes manual triage slower per finding, at exactly the moment volume makes it faster per finding or nothing. Organizations that can process this data automatically gain a decisive security advantage. Those that cannot will drown in it.
The Time Burden: Quantifying the Mythos SOC Impact
The figures below are conservative estimates based on current analyst triage speeds and the known characteristics of Mythos preview findings.
Phase 1: The Mythos Initial Disclosure Wave
Assume Mythos discloses 3,000 verified vulnerabilities at GA through Glasswing’s coordinated disclosure. An enterprise running Windows, macOS, Chrome, and standard enterprise applications could face 400 to 800 relevant findings. At 60 minutes manual triage per finding, that is 400 to 800 analyst hours, or 10 to 20 full-time work weeks.
Phase 2: The Mythos Ongoing Daily Stream
The Mythos initial disclosure is not a one-time event. As the model continues analyzing new software releases, patches, and libraries, it will produce a steady stream of new vulnerability findings. Conservatively, 20 to 50 new Mythos findings per week will require organizational triage, adding 20 to 50 analyst hours weekly to existing workloads, permanently.
The Mythos Compound Burden: Two Phases Stacked
| Scenario | Weekly Analyst Hours (Vulnerability Triage Only) | % of 8-Analyst Team Capacity (320 hrs/week) |
|---|---|---|
| Pre-Mythos baseline | 20–40 hrs | 6–12% |
| Mythos initial wave (backlog clearance) | 80–120 hrs | 25–38% |
| Mythos ongoing stream (steady state) | 40–90 hrs | 12–28% |
| Mythos + 2 additional LLMs (12–24 months) | 100–250 hrs | 31–78% |
When vulnerability triage consumes 30 to 80% of analyst capacity, incident response and threat hunting collapse. This is a staffing crisis with real consequences for organizational risk.
The Multi-LLM Vulnerability Landscape
Mythos is the first AI model built for vulnerability discovery. It will not be the last. The capabilities that make Mythos effective, large-scale code analysis, pattern recognition across software stacks, automated exploitation testing, emerge from large language models that any well-resourced AI lab can replicate.
Why More LLMs Will Follow Mythos
1. Economic Incentives
Bug bounty programs pay $10K to $1M+ per high-severity zero-day. An LLM discovering 100 vulnerabilities per week generates tens of millions in bounty value annually.
2. Security Vendor Competition
Security vendors already integrate LLMs for threat detection and log analysis. Expect major vendors to ship Mythos-like capabilities within 12 to 18 months.
3. Open-Source Replication
Open-source models for vulnerability discovery will emerge from university labs and security teams, multiplying AI-generated findings.
4. Nation-State Programs
Governments will develop their own discovery models. Some findings will enter coordinated disclosure; others may not. Prepare for both.
The Mythos Multiplier Effect
| Timeline | Active AI Discovery Models | Estimated Weekly Findings (Per Enterprise) | Weekly Analyst Hours (Manual Triage) |
|---|---|---|---|
| Today | Mythos preview only | 0 (pre-release) | 0 |
| Mythos GA (2026) | 1 (Mythos) | 20–50 | 20–50 |
| GA + 12 months | 2–3 models | 50–120 | 50–120 |
| GA + 24 months | 5+ models | 100–300 | 100–300 |
Format Fragmentation Across Mythos and Successors
That timeline has already accelerated. In March 2026, OpenAI launched Codex Security, which scanned 1.2 million commits in 30 days and surfaced over 10,000 high-severity findings. It targets active development workflows — a different layer than Mythos, but together they eliminate quiet periods for SOC teams.
Mythos produces highly structured triage reports. Other LLMs may not. SOC teams will face a mix of richly documented Mythos findings, bare CVE-style advisories, and everything in between. Any triage platform must normalize, correlate, and prioritize across formats without manual adaptation per source.
Strategy note
Preparing only for Mythos is preparing for yesterday’s problem. The sustainable strategy accounts for a future where AI-driven vulnerability discovery is the norm, where multiple models produce findings continuously, each with different formats, severity models, and verification rigor.
Why Static Triage Fails at Mythos Scale
Most SOC teams triage vulnerability findings through scanner dashboards, spreadsheet tracking, CVSS score filtering, and manual analyst review. These methods work at human-speed discovery. They fail at Mythos-speed discovery for five structural reasons.
1. CVSS-Only Prioritization Misses Mythos Chain Risk
Mythos exposed that individually “medium” vulnerabilities chain into critical exploit paths. A CVSS 5.3 information leak plus a CVSS 6.1 privilege escalation plus a CVSS 4.8 sandbox escape individually pass below thresholds, but together form full remote code execution. Static CVSS filtering cannot detect chainability across Mythos findings.
2. Manual Correlation Collapses at Mythos Volume
Experienced analysts correlate vulnerabilities by memory: “I saw a similar library issue last month.” This works for 50 findings. At 500 Mythos findings with rich exploitation data, the correlation relationships exceed what any team can hold in working memory, regardless of skill level.
3. Static Playbooks Cannot Handle Mythos Zero-Days
Pre-built playbooks assume known vulnerability types. Mythos discoveries are, by definition, previously unknown. A static playbook for “browser vulnerability” cannot incorporate the specific exploitation chain, environmental context, or chainability data that a Mythos triage report provides.
4. Staffing Models Assume Pre-Mythos Volumes
SOC staffing is calibrated to historical vulnerability rates. Mythos is not a gradual increase. It is a step function. Organizations cannot hire and train enough vulnerability analysts in the Mythos disclosure timeline. Experienced analysts take 12 to 18 months to develop.
5. Multi-LLM Normalization Is Manual Today
When Mythos and future LLMs produce findings in different formats, with different severity models and different verification standards, someone must normalize before triage begins. That manual normalization adds 10 to 20 minutes per finding before actual Mythos triage even starts.
The fundamental Mythos mismatch
AI discovers vulnerabilities at machine speed. Human triage processes operate at human speed. No amount of process optimization, staffing increase, or CVSS filtering closes that gap. The triage process itself must become AI-driven: autonomous, adaptive, and tailored to each organization’s environment.
The Autonomous SOC: Matching Mythos Discovery Speed
D3 Security has published extensively on the evolving role of the SOC analyst in the age of AI-driven autonomous security operations. The core argument: analysts spending 3+ hours daily on repetitive L1/L2 triage are misallocated. That work should be handled autonomously, freeing analysts for threat hunts, AI decision validation, and detection engineering. The result is better-deployed analysts: strategic security advisors who shape detection engineering, threat hunting, and AI decision validation.
This model, already proven for alert triage, maps directly to the Mythos vulnerability challenge. The operational structure is identical: a flood of incoming data requires initial processing, contextual enrichment, risk prioritization, and human judgment for final remediation decisions. If autonomous processing can handle security alerts at L2+ depth, it can handle Mythos vulnerability findings using the same framework.
Alert Triage vs. Mythos Vulnerability Triage: A Direct Comparison
| Dimension | Alert Triage (Today) | Mythos Vulnerability Triage |
|---|---|---|
| Input volume | Thousands of alerts/day from SIEM, EDR, firewall | Hundreds of Mythos findings/week + future LLM sources |
| Data richness | Log data, IOCs, behavioral signals | Mythos code analysis, exploitation steps, verification results |
| Correlation | Cross-alert, cross-source linking | Cross-vulnerability chainability from Mythos exploitation data |
| Prioritization | Severity, confidence, business impact | Chainability, environmental exposure, Mythos severity + CVSS |
| Human role | Validate findings, approve response | Validate Mythos prioritization, approve remediation plans |
Why the Autonomous SOC Model Solves the Mythos Problem
When autonomous processing absorbs L1/L2 Mythos vulnerability triage, the analyst role elevates. Analysts review the 15 to 20 findings the autonomous system flagged as critical, complete with environmental context, chainability analysis, and recommended remediation steps. They apply the organizational judgment that AI should not make unilaterally: “This Mythos finding affects our payment environment during a code freeze; escalate to the change advisory board.”
Reference
For a deeper exploration of the analyst role transformation, see D3 Security’s The Evolving Role of the SOC Analyst in the Age of AI-Driven Autonomous Security Operations. The principles outlined there, autonomous triage absorbing L1/L2 workload, analyst elevation to strategic roles, burnout reduction, apply directly to the Mythos challenge.
How Morpheus AI Processes Mythos Vulnerability Findings
Morpheus AI already processes vulnerability reports through its attack path discovery framework, correlating alerts by CVE and device across scanners like InsightVM and Qualys. When Mythos reaches GA, Morpheus AI will handle its findings using the same architecture.
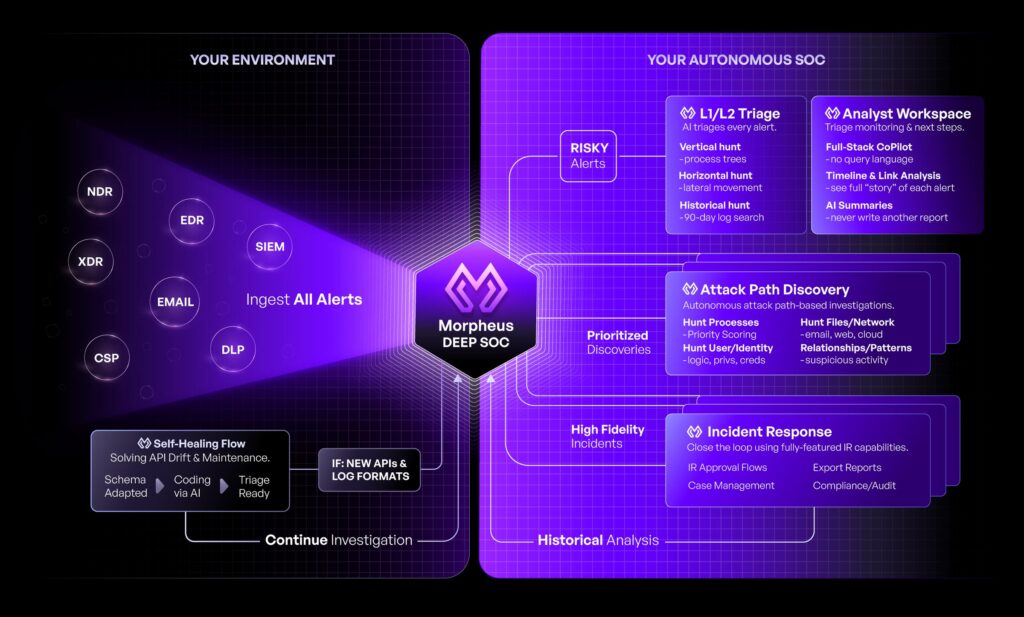
Why Mythos Findings Are Uniquely Valuable to Morpheus AI
Mythos triage reports contain significantly richer information than traditional CVE advisories. The exploitation steps for tested applications let Morpheus AI correlate adversary activities that would otherwise go undetected. No other source provides this level of application-level exploit detail.
Mythos exploitation data is scoped to tested applications, a bounded slice of the attack surface. Morpheus AI maps the rest through 800+ integrations: network topology, user behavior, lateral movement, full-stack telemetry. Mythos discovers; Morpheus AI investigates, correlates, and remediates.
Morpheus AI Capabilities Applied to Mythos Triage
| Capability | How It Applies to Mythos Findings |
|---|---|
| Attack Path Discovery | Correlates Mythos exploitation steps with vulnerability data across the environment, identifying chainable exploit paths that CVSS scoring alone misses |
| Contextual Playbooks | Generates Mythos-specific response playbooks at runtime from actual evidence. No pre-built templates needed for novel zero-days |
| Adaptive Tasking | Investigates Mythos findings using vulnerability data from InsightVM, Qualys, and 800+ tools, driven by LLM reasoning, SOPs, or analyst prompts |
| Self-Healing Integrations | Auto-repairs API drift during mass Mythos remediation events in 45 min–2 hrs vs. 7–14 days manually |
| AI SOPs | Natural language operating procedures define Mythos response logic: escalation paths, change windows, regulatory triggers |
| Customer-Expandable LLM | Organizations extend Morpheus AI with their own Mythos triage priorities, asset criticality data, and remediation policies |
Roadmap
Deep Mythos integration is on D3 Security’s roadmap. The alignment described here reflects Morpheus AI’s current vulnerability processing, applied to the data structures Mythos will produce. With Mythos filling the gap in application-level exploitation insight, attack path discovery gains its final missing piece.
Bespoke Mythos Triage: Every Organization Is Different
A Mythos vulnerability on a hospital’s patient records system demands a fundamentally different response than the same Mythos vulnerability on a media company’s content delivery network. CVSS score is identical. Business impact, remediation urgency, change window constraints, and regulatory notification requirements differ completely. This is why bespoke Mythos triage is essential.
How Morpheus AI Delivers Bespoke Mythos Processing
800+ Security Tool Integrations
Morpheus AI connects to every layer of the stack: vulnerability scanners, EDR, SIEM, patch management, asset inventory, and ticketing. Mythos findings are automatically enriched with environmental data from every connected source. No manual lookup or context-switching required.
Customizable LLM Framework
Organizations extend Morpheus AI’s purpose-built cybersecurity LLM with environment-specific data: asset criticality, custom severity weighting, proprietary threat intelligence, and Mythos remediation policies. The platform becomes a proprietary triage asset that improves with every Mythos investigation.
Natural Language Mythos Response Procedures
SOC teams define Mythos response processes as AI SOPs in natural language. An analyst can write: “For critical Mythos findings affecting production web servers, check the change advisory board schedule before recommending patching.” Morpheus AI executes that logic automatically.
Self-Healing During Mythos Remediation Events
Mass Mythos patching triggers vendor API updates that break traditional automation. Morpheus AI’s self-healing integrations detect drift and auto-repair connectors in 45 min–2 hrs, compared to 7–14 days for manual repair. The SOC never loses connectivity during the critical Mythos response window.
The Mythos complement
Mythos discovers application-level exploitation paths that no other security vendor can provide. Morpheus AI maps the rest: network topology, user behavior, lateral movement, full-stack telemetry. Together, they produce a complete picture: Mythos provides the vulnerability insight; Morpheus AI provides the investigation, prioritization, and remediation.
A Readiness Framework for the Post-Mythos Landscape
Regardless of which autonomous platform an organization selects, the following framework provides a structured approach to preparing for Mythos and the AI-driven vulnerability discovery models that will follow.
Phase 1: Assess Mythos Readiness (Now)
- Audit current triage throughput: How many vulnerability findings can your team process per week? What is the average time per finding? What is the current backlog?
- Map your Mythos exposure: Which OSes, browsers, libraries, and applications does your organization run? Estimate how many Mythos findings will be relevant.
- Measure analyst allocation: What percentage of analyst time goes to vulnerability triage today? What happens to incident response and threat hunting when that percentage doubles?
Phase 2: Build Autonomous Mythos Triage Capacity (Before GA)
- Deploy an autonomous triage platform capable of ingesting Mythos triage reports and normalizing findings from multiple AI sources.
- Integrate vulnerability scanners and asset inventories so the platform has environmental context for Mythos prioritization.
- Define Mythos response SOPs: Escalation paths, change window constraints, regulatory notification triggers, in a format the autonomous system executes.
- Train the system on your environment: Asset criticality, network topology, business-specific risk definitions. Generic prioritization is not sufficient for Mythos-scale decisions.
Phase 3: Validate and Refine (First 30 Days Post-Mythos)
- Monitor autonomous Mythos triage accuracy against analyst spot-checks. The goal: confidence that the system surfaces the right 15–20 critical Mythos findings from a larger pool.
- Measure time-to-remediation for autonomous-triaged Mythos findings vs. manually triaged. Track the improvement.
- Iterate on SOPs: Real Mythos findings will reveal gaps. The autonomous system should adapt to new Mythos finding types without manual reconfiguration.
Questions for Your Evaluation
Mythos Capacity
If 600 verified, high-detail Mythos vulnerability findings arrived tomorrow, how long would your team take to triage all of them? What would you stop doing to make room?
Mythos Chain Detection
Can your current process detect chainable exploit paths across multiple Mythos findings, or does it evaluate each Mythos vulnerability in isolation by CVSS?
Multi-LLM Readiness
If three AI models were producing vulnerability findings simultaneously (Mythos and two successors, each with different formats), could your platform correlate across all three?
Mythos Environmental Context
Does your triage process incorporate asset criticality, network topology, and change windows when prioritizing Mythos findings, or does it treat every instance identically?
Analyst Allocation Post-Mythos
What percentage of L2/L3 time is consumed by automatable tasks today? When Mythos doubles the vulnerability triage volume, which strategic activities get cut?
Next Steps
Morpheus AI currently processes vulnerability reports through its attack path discovery framework and will be fully prepared to handle Mythos vulnerability findings at launch. To evaluate how Morpheus AI’s customizable LLM framework, 800+ integrations, and autonomous triage capabilities apply to your Mythos readiness, schedule a demonstration.
About D3 Security
D3 Security is the force behind Morpheus AI, the AI-driven autonomous SOC platform that investigates 100% of alerts at L2+ analyst depth. Purpose-built by 60 cybersecurity specialists over 24 months, Morpheus AI delivers bespoke vulnerability triage processing through a customizable LLM framework, 800+ self-healing integrations, and natural language operating procedures, ready for the post-Mythos world.