Morpheus AI vs. Elastic Security
Beyond SIEM Investigation: Autonomous Investigation Layer
See Morpheus AI Complement Elastic Security

meet morpheus AI
Elastic Security detects threats. Morpheus AI investigates them. SIEMs generate 960–3,000+ daily alerts with 53% false positives; yet 67% go uninvestigated (SANS). Analysts spend 56 minutes before acting on an alert and 70 minutes investigating one alert. Morpheus AI closes this structural gap with autonomous L2 investigation, attack path discovery across 800+ tools in under 2 minutes, and contextual response playbook generation. Morpheus is not an Elastic Security alternative or replacement—it is an autonomous investigation layer that complements Elastic Security. The question is not Morpheus OR Elastic. It’s what happens to your alerts AFTER Elastic detects them.
Why SIEMs Like Elastic Security Cannot Close the Investigation Gap
Elastic Security is architecturally a detection and analytics platform. Detection alone doesn’t stop attacks. All SIEMs, including Elastic, face four structural challenges that autonomous investigation platforms are required to overcome:
| Structural Challenge | Details |
|---|---|
| Detection Without Autonomous Investigation | Elastic Security detects and alerts. Analysts take 56 minutes before acting on an alert, then 70 minutes to investigate one alert. With 960–3,000+ daily alerts, 40% go uninvestigated. Detection velocity alone does not reduce breach dwell time. Autonomous investigation velocity is required. |
| Single-Tool Correlation Cannot Trace Attacks | Elastic correlates alerts within Elastic-ingested data. Modern attacks traverse email, endpoints, identity, cloud, and network tools. SIEM-native correlation cannot follow attack paths across tool boundaries. 53% of all alerts are false positives. Without cross-tool correlation, teams cannot distinguish noise from genuine threats. |
| Static Playbooks, Not Contextual Response | Elastic has no native SOAR. Traditional hardcoded playbooks execute the same steps regardless of threat context. Gartner declared standalone SOAR “obsolete before plateau” (2024). Alert triage is not response. Response requires evidence-based decision logic and runtime playbook generation, not static templates. |
| Alert Fatigue Without Alert Reduction | 64% cite high false positive rates. 61% admit ignoring alerts that proved genuine. Elastic’s alert triage is not alert reduction. Only autonomous investigation at L2 depth can reduce actual alert volume and improve signal-to-noise ratio. |
What Autonomous Investigation Adds: Morpheus AI Capabilities Elastic Security Lacks
Morpheus AI is purpose-built to address each structural SIEM gap. Here’s what autonomous investigation at L2 depth delivers:
| Capability | Description |
|---|---|
| Autonomous L2 Investigation Every Alert | Morpheus AI investigates every alert at L2 depth without analyst intervention. Correlates evidence across 800+ tools, traces multi-hop attack paths in <2 minutes, determines context and severity, and generates natural language findings. 100% coverage. Elastic detects; Morpheus investigates. |
| N-South + East-West Attack Path Discovery | Morpheus AI traces both North-South (internet-to-asset) and East-West (asset-to-asset) attack paths regardless of tool boundaries. Elastic’s Alert Correlation stays within Elastic data. Morpheus discovers lateral movement, persistence, and multi-stage attacks that Elastic cannot trace across tool boundaries. |
| Self-Healing Integrations Autonomously | Morpheus AI maintains 800+ tool integrations autonomously. No manual API maintenance, no playbook updates when tools change. Elastic requires constant custom API integration engineering. Morpheus integrations self-heal based on runtime tool health and data freshness. |
| Contextual Playbook Generation at Runtime | Morpheus AI generates playbooks at runtime from evidence, not hardcoded templates. Each playbook is unique to the threat, evidence, and available remediation tools. Context-aware response automation. Elastic has no native playbook generation or orchestration capability. |
| Purpose-Built Cybersecurity LLM | Morpheus AI runs on a cybersecurity-specific large language model trained over 24 months by 60 specialists. Elastic’s AI Assistant uses general-purpose customer-selected LLMs. Cybersecurity reasoning requires domain-specific model training—general LLMs cannot reliably trace attack chains without hallucination. |
| Transparent Reasoning & Audit Trail | Morpheus AI explains investigation reasoning, adapts recommendations on evidence contradictions, and updates playbooks in real-time. 87% analyst-play rate (APR) on recommended actions. Every decision includes audit trail and rationale. Elastic provides detection; Morpheus provides defense accountability. |
Watch how autonomous investigation closes the detection-response gap. See N-South and East-West attack path discovery, contextual playbook generation, and self-healing integrations in real-world scenarios with live alerts.

See Morpheus AI Complement
Elastic Security
Methodology: How Morpheus AI Investigates
Morpheus AI follows a structured investigation methodology to ensure comprehensive, evidence-based threat analysis:
Step 1: Multi-Tool Evidence Correlation. Receives alert from Elastic Security or any SIEM. Queries 800+ integrated tools simultaneously for contextual data: email logs, endpoint telemetry, identity events, cloud activity, network records, and third-party threat feeds.
Step 2: Attack Path Discovery. Traces N-South (external-to-asset) and East-West (asset-to-asset) attack paths using correlations across tool boundaries. Identifies lateral movement, persistence mechanisms, and attack progression stages that SIEMs cannot detect alone.
Step 3: Evidence-Based Reasoning. Applies cybersecurity-domain LLM to synthesize evidence, determine attack severity and intent, identify indicators of compromise (IOCs) across the attack chain, and assess risk to business assets and data.
Step 4: Contextual Response Playbook Generation. Generates remediation playbooks tailored to the specific threat, available tools, and organization’s risk tolerance. Rank response actions by impact and confidence. Recommend or autonomously execute responses via integrated orchestration.
Step 5: Closed-Loop Feedback. Reports investigation findings back to Elastic Security for audit trail and alert closure. Learns from analyst feedback to refine future investigations. Maintains investigation history for trend analysis and retrospective threat hunting.
Detailed Comparison: Morpheus AI vs. Elastic Security
| Capability | Morpheus AI | Elastic Security |
|---|---|---|
| Core Function | Autonomous investigation + SOAR engine | Detection + analytics (SIEM) |
| Attack Path Discovery | N-South + East-West across 800+ tools in <2 min per alert | Alert correlation within Elastic-ingested data only |
| Self-Healing Integrations | 800+ tools with autonomous maintenance and health checks | API-first approach; manual engineering required |
| Playbook & Response | Contextual runtime generation from evidence | No native SOAR; basic actions in v8.4+ |
| AI Architecture | Purpose-built cybersecurity LLM (24 mo, 60 specialists) | AI Assistant using customer-chosen general LLM |
| Cross-Tool Investigation | Correlates across 800+ tools regardless of vendor | Correlates within Elastic data; cross-tool requires custom integration |
| Alert Coverage | 100% investigated at L2 depth autonomously | Detection only; investigation analyst-dependent |
| Alert Reduction | 144,000 alerts → 200 validated MSSP (99%+ reduction) | Detection volume; no autonomous reduction |
| MTTR Reduction | 80% vs. manual investigation baseline | Dependent on analyst response (56–70 min baseline) |
| Orchestration Engine | Full built-in SOAR with autonomous execution | No dedicated SOAR; third-party partnerships required |
| Investigation Transparency | Transparent reasoning, 87% APR, audit trail | Not applicable to detection platform |
| Pricing Model | Platform Subscription + User Licenses. No per-alert charges. No per-user fees. No token fees. No investigation caps. | Cloud from $99/mo; scales by usage and features. EASE adds variable costs. |
How Morpheus AI and Elastic Security Work Together
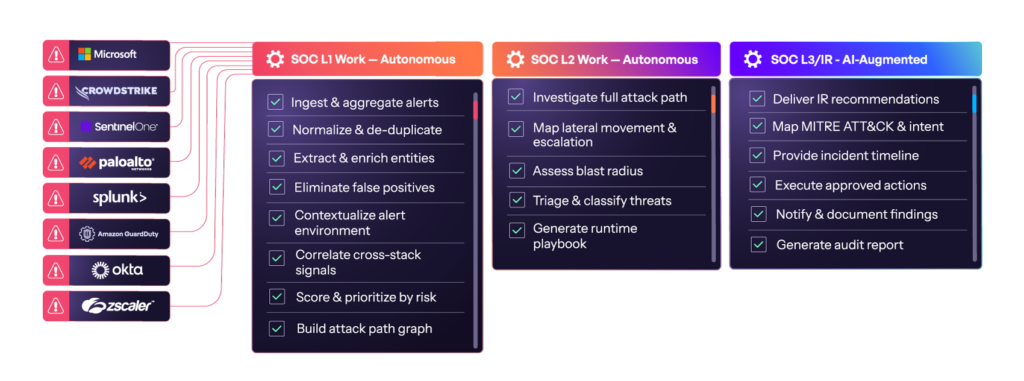
Morpheus AI is positioned alongside Elastic Security, not as a replacement. The architecture is “Beyond SIEM, Beside SIEM.” Here’s the complete SOC workflow:
| Step | Action |
|---|---|
| Elastic Security Detects | Detects threats via rules, baselines, and behavioral analytics. Generates alert payload. Sends to Morpheus AI. |
| Morpheus AI Investigates | Autonomously investigates every alert at L2 depth. Correlates evidence across 800+ tools. Traces attack paths. Generates findings and evidence-based recommendations. |
| Morpheus Response & Feedback | Recommends or executes response actions. Returns investigation findings to Elastic Security for audit trail, closed-loop feedback, and alert closure. |
Result: Detection velocity + Autonomous investigation velocity + Contextual response velocity = Complete autonomous SOC.
Frequently Asked Questions About Morpheus AI and Elastic Security
Can Morpheus AI work with Elastic Security?
Yes. Morpheus AI integrates directly with Elastic Security via alert API and webhook. Elastic Security detects threats and generates alerts; Morpheus AI investigates every alert autonomously at L2 depth, traces attack paths across 800+ integrated tools, and generates contextual response playbooks. Morpheus complements Elastic without replacing it. The integration is bidirectional: Elastic sends alerts; Morpheus returns investigation findings, evidence correlations, and recommended actions. This is the “Beyond SIEM, Beside SIEM” architecture—detection platform + autonomous investigation platform = complete SOC.
What does Morpheus AI do that Elastic Security’s AI Assistant cannot?
Elastic’s AI Assistant accelerates natural language queries within Elastic-ingested data only. Morpheus AI autonomously investigates every alert without analyst prompting, correlates evidence across 800+ tools (many outside Elastic ingestion), traces multi-hop attack paths in under 2 minutes, generates contextual response playbooks at runtime from evidence, and maintains 800+ tool integrations autonomously with self-healing APIs. Elastic’s AI Assistant makes detection faster; Morpheus autonomous investigation requires cybersecurity-domain LLM training, multi-tool correlation logic, and evidence-based reasoning that general AI assistants cannot provide reliably.
Does Morpheus AI replace Elastic Security?
No. Morpheus AI is explicitly positioned to complement Elastic Security. Elastic Security is a detection and analytics platform; Morpheus AI is an autonomous investigation platform. Elastic detects and alerts; Morpheus investigates and responds. The positioning is “Beyond SIEM, Beside SIEM”—Morpheus fills the structural investigation gap that no SIEM architecture can close alone. Together, Morpheus + Elastic Security create a complete autonomous SOC capable of detecting, investigating, and responding to every alert without manual analyst handoff.
How does Morpheus attack path discovery go beyond Elastic Security’s Attack Discovery?
Elastic’s Attack Discovery feature correlates alerts within Elastic-ingested data to identify attack chains from detection signals alone. Morpheus AI traces attack paths across 800+ integrated tools—email, endpoints, identity, cloud, network, and third-party solutions—in under 2 minutes per alert, regardless of vendor or data ingestion. Modern multi-stage attacks traverse email → endpoint → identity → cloud boundaries. SIEM-native correlation cannot follow paths outside SIEM data. Morpheus AI provides N-South (internet-to-asset) and East-West (asset-to-asset) attack path discovery that Elastic Security cannot deliver.
What is the investigation gap in SIEM platforms like Elastic Security?
The investigation gap is a structural limitation all SIEMs share: they detect and alert but do not autonomously investigate. Analysts take 56 minutes before acting on an alert and 70 minutes to investigate one alert. With 960–3,000+ daily alerts, 53% of which are false positives, 67% of all alerts go uninvestigated. SIEMs cannot trace attack paths across tool boundaries, generate context-aware response without manual playbook authoring, or reduce alert fatigue autonomously. This gap exists in Elastic Security and all SIEM platforms. Autonomous investigation platforms like Morpheus AI are required to close this gap and achieve true SOC automation.
How does Morpheus AI pricing compare to Elastic Security?
Morpheus AI: Platform Subscription + User Licenses model. No per-alert charges, no per-user fees, no token fees, no investigation caps. D3 Security absorbs all AI token costs; investigation volume does not drive incremental costs. One flat subscription covers unlimited autonomous investigations across your entire SOC. Elastic Security: Cloud pricing starts at $99 per month and scales based on data ingestion volume, features, and storage. Elastic’s serverless EASE (AI SOC Engine) for alert triage adds additional usage-based variable costs; each GB of ingestion increases cost. For organizations with 960–3,000+ daily alerts, Morpheus AI’s flat-subscription model provides cost predictability and full L2 autonomous investigation coverage at no per-alert charge. Elastic’s usage-based model scales with data volume but does not include autonomous investigation—additional SOAR tools or services are required to add investigation and response capabilities. See d3security.com/morpheus/pricing/ for Morpheus AI details.
D3 Security is not affiliated with Elastic or Elastic Security. All trademarks are the property of their respective owners. This comparison reflects publicly available information and our team’s evaluation as of March 2026.
Explore Autonomous Investigation Resources
Go deeper into autonomous investigation, attack path discovery, and autonomous SOAR orchestration: