The human-centric SOC model has hit a wall.
Alert volumes scale exponentially, but human teams don’t. Many organizations outsource Tier 1 to an MSSP to bridge the gap, but without the right tools, this often results in simply “renting a bottleneck.”
Here’s the structural problem: You pay for detection. Your provider gets paid for speed. So they optimize for “time to close” instead of “time to analyze.” What you get is triage theater: a ten-minute glance at a hash instead of forensic investigation. They aren’t trying to ignore threats; they are simply battling a volume of noise that manual processes weren’t built to handle.
And the cost shows up as latency. Ransomware adversaries break out in 18 minutes. If your MSSP has a 30-minute SLA just to acknowledge the ticket, the response is already behind the curve.
You can’t fight code with a call center. Morpheus investigates the same alert, with more forensic depth at a fraction of the cost. The unit economics aren’t close.
What follows are the arguments for replacing a human-tier MSSP with Morpheus AI, our autonomous SOC platform.
The unit economics of alert triage
The traditional MSSP model scales by FTEs (Full-Time Equivalents). You pay per analyst per year in fully-loaded costs—salary, benefits, overhead, vendor margin. That analyst handles maybe 50-75 alerts per day if they’re moving fast. Do the math: you’re likely spending $2.25 to $3.00 per alert just for a initial human eyes-on.
For an enterprise generating 5,000 alerts daily, that’s roughly $15,000 burned every day on triage labor alone. Annually, you’re looking at $5.5 million in pure operational spend before you factor in turnover costs, training, or the degraded service quality that comes from analysts rushing through queues.
When alert volume spikes, and it will, you have two options: absorb the queue backlog or buy more headcount. Both scale linearly with cost. A 50% spike in alerts means a 50% spike in labor costs or a 50% degradation in triage quality.
Morpheus decouples cost from volume. It runs on elastic compute, not salaried shifts. The platform investigates alerts for approximately $0.27 each, a 10x reduction in operational cost. That price holds whether you’re processing 1,000 alerts or 100,000. Volume spikes don’t trigger emergency headcount requisitions. They trigger compute scaling.
The conservative model assumes you keep a small MSSP footprint for Tier 3 escalations and edge cases. The aggressive model, where Morpheus handles 90% of triage, pushes savings into millions of dollars annually.
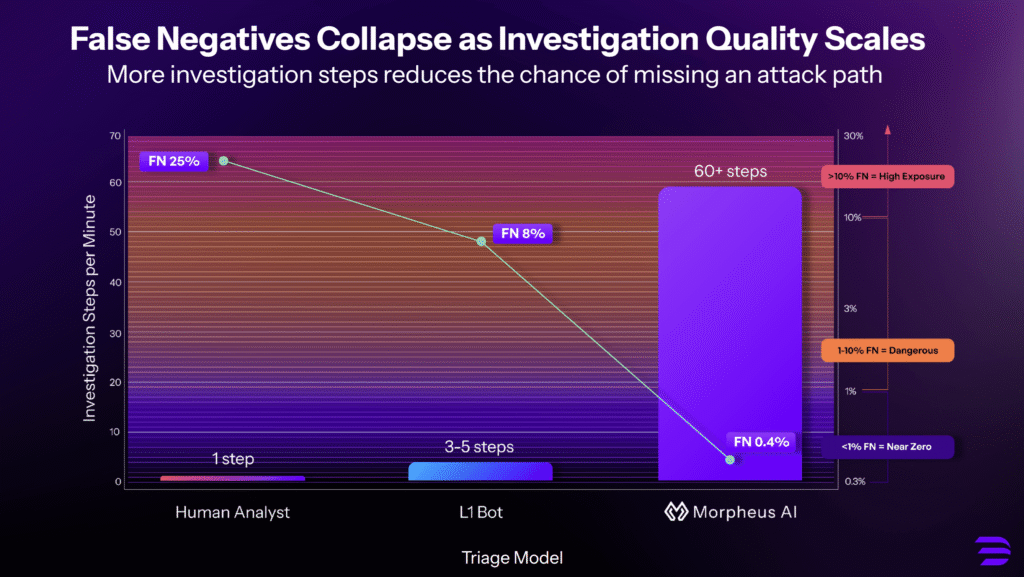
But the real ROI is cost reduction while simultaneously improving detection depth. Your MSSP analyst typically has 10-15 minutes to triage an alert before they blow an SLA. Morpheus executes 60+ investigation steps in under a minute. You’re getting more coverage for less spend.
A Note to the Modern MSSP
If you’re an MSSP reading this, the message is simple: Your customers are actively looking for AI-driven SOC solutions designed to handle L1 and L2 triage. The market is shifting away from “selling bodies” toward “selling outcomes.”
You have a choice: watch your customers buy this functionality directly from vendors like D3, or deliver it to them. By adopting Morpheus, you can evolve your service from a manual labor provider to an automated powerhouse, increasing your margins while providing the sub-minute triage your customers now demand.
Why manual triage misses the breach (and burns budget)
Manual triage is a linear process. An analyst pulls a ticket, runs a static query, and makes a binary decision. If a credential stuffing campaign hits, the queue explodes. To maintain margins, manual teams are often forced to choose between speed and depth.
Morpheus flips the model. It executes deep forensic checks that a human would need 45 minutes to complete, including:
- Vertical Hunt: It pulls the process tree, dumps browser history, and analyzes the MFT.
- Horizontal Hunt: It correlates the user’s identity across Okta, email, and cloud logs to find lateral movement.
Morpheus drives that risk down to near zero. By running comprehensive checks on every alert, it uncovers threats that human teams simply do not have the time to find. You stop relying on luck. You start relying on total coverage.
Infinite elasticity: The end of throttling
Manual SOCs have physical limits. When a surge hits, providers may be forced to “throttle” data or cap intake to keep the queue manageable. Morpheus is built for spikes. It processes 10 events as thoroughly as 10,000, ensuring your visibility isn’t dictated by your provider’s staffing levels.
Visibility: Escaping the “SLA police”
Most traditional services operate behind a curtain. They sell you peace of mind in the form of a monthly PDF. But as industry analysts like Rafal Kitab have noted, these reports give a skewed picture. They measure “Time to Acknowledge” instead of “Time to Resolve.” Worse, they often suppress noisy alerts that might indicate a subtle breach to protect their margins and meet their quotas.
Morpheus treats security logic as code, producing an audit trail for every decision, API call, variable check, branching path, recorded in a structured, readable log. You get a verdict with the evidence package. You see the specific registry key that triggered the escalation.
Most importantly, you control the logic. Every environment faces unique threats. You need a model that adapts to your reality. Try getting a global MSSP to sing off your sheet music. They run a rigid, one-size-fits-all playbook. They cannot deviate without breaking their model for everyone else.
With Morpheus, you refine the model instantly. You spot a logic gap. You update the variable. The change propagates to 100% of alerts immediately. You do not wait for a “Change Request” ticket. You own the tune.
End to end SOC triage and IR
For many, the goal isn’t to eliminate external support, but to optimize it.
Morpheus serves as the perfect bridge for the multi-tier internal SOC. It acts as an automated Tier 1 and Tier 2 analyst that sits inside your network and flips the leverage. It investigates 100% of alerts, filtering out the noise. It prepares response actions for your internal team to approve.
Organizations that deploy Morpheus to handle 85% of triage while retaining a small MSSP footprint for escalations see their billed FTEs drop from 15 to 3. That’s $2 million in annual savings while maintaining access to expert-level incident response for genuinely complex threats.
The unit economics of AI SOC triage
Because Morpheus runs on elastic compute rather than salaried shifts, it decouples cost from volume. Morpheus investigates that same alert, with deeper context and multi-step investigations for approximately $0.27. This is a 10x reduction in operational cost.
Comparative Cost Analysis (5,000 Alerts/Day)
| Component | MSSP (Human Tier) | Autonomous SOC (Morpheus) |
| Primary Resource | Human Labor (Linear) | GPU/CPU (Elastic) |
| Cost Per Alert | $2.25 – $3.00 | $0.27 |
| Triage Depth | ~5 Checks/Alert | ~60 Checks/Alert |
| Investigation Time | 10-15 minutes | <1 minute |
| Scalability | Capped by Headcount | Infinite |
| Alert Throughput | 50-75 alerts/analyst/day | Unlimited |
| Queue During Spikes | Explodes | Absorbs |
| SLA Acknowledgment | 30 minutes (average) | Immediate |
| Annual Turnover Impact | $84K (30% industry avg) | $0 |
| False Negative Rate | ~25% (rushed triage) | <1% |
| Coverage Consistency | Degrades with volume | Constant at any scale |
| Visibility Control | Vendor-controlled | Customer-controlled |
| SAVINGS | — | >70% |
The math is clear
The traditional model was built for a world where alerts were manageable and adversaries moved slowly. That world is gone.
You’re now facing ransomware crews that operate in minutes, drowning in telemetry that human teams physically cannot analyze at scale. And you’re paying premium rates for a service that optimizes for metrics instead of outcomes.
The autonomous SOC can help take back control of your detection logic, eliminating the structural conflicts that come with outsourced triage, and building a system that scales with the threat.
The numbers are stark: 70% cost reduction, 12x deeper investigation, zero queue backlog. Organizations running Morpheus in aggressive deployment models are seeing effective cost per alert drop 10x, while simultaneously improving alert coverage.
Bring the stack home. Control the logic. Own the data.