Software to scale your Mssp
Automation Made for the MSSP Business
Optimize every aspect of your security services with Smart SOAR. Achieve interoperability with any product, minimize waste, and confidently execute detection and response across multi-platform customer environments. Easy to use and train on, and with a full spectrum of incident response, threat hunting and MITRE capabilities to deliver as a service, Smart SOAR is a unique MSSP SOAR solution that will help your business scale.
Scale Operations, Without Adding Headcount
99% Less Noise
Eliminate up to 99% of noise and increase incident fidelity with our Event Pipeline.
“We could absorb almost three times our client load right now without actually having to allocate more resources in our SOC.” – Senior Engineer, Large MSSP
5-Minute Onboarding
Launch new tenant environments, including playbooks and integrations, with an automated workflow.
“Our whole process for onboarding a client through D3 takes about 10 clicks. It’s made it easier to achieve our goal of doubling our global client base.” – Global SOC Director, MDR Provider
“We ran the top four or five automation tools through our lab and D3 came out on top.”
The Smart Soar Approach
Unlock Opportunities for Growth with the Leading MSSP SOAR Solution
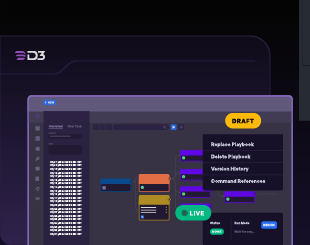
SOAR Automation
Streamline and enhance security operations and response with D3’s proven SOAR platform and architecture.
Proactive Threat Hunting
Support threat hunting and vulnerability management with Smart SOAR’s combination of MITRE ATT&CK, link analysis, and correlation capabilities.
SOC-as-a-Service
Centralize SecOps in Smart SOAR while using integrations and multitenancy to service customers who wish to retain their own tooling.
Resources for MSSP Leaders
Learn more about what makes Smart SOAR the preferred choice for MSSPs around the world:
-
MSSP Survey 2024
Exclusive insights from MSSP professionals reveal how automation drives growth and job satisfaction

-
Trifork Security’s Transformation: Streamlining SecOps with Smart SOAR
Learn how our platform revolutionized Trifork Security’s operations and how it can do the same for your business. Watch the video testimonial now.
-
Why High Wire Networks Chose Smart SOAR to Scale Its Security Operations
Learn how High Wire Networks, a master MSSP, achieved 99% noise reduction, shifted to a 70% proactive approach, and tripled its client capacity without added resources.
-
What Smart SOAR Means for Your MSSP
Download our guide to learn about Smart SOAR’s MSSP-focused design, client collaboration capabilities, profitability potential, and successful use cases.
-
The MSSP Client Portal: Differentiate Your Services with Streamlined Client Collaboration
The MSSP Client Portal addresses challenges in providing efficient communication, accurate reporting, and scaling security services.