How D3 Morpheus ingests, triages, investigates, and escalates security alerts using AI-autonomous intelligence built for the regulatory demands and patient safety requirements of U.S. healthcare organizations.
EXECUTIVE SUMMARY
U.S. healthcare organizations face the most severe cybersecurity crisis of any industry, one measured in patient safety and clinical outcomes, not just dollars and regulatory penalties. D3 Morpheus is an AI-autonomous SOC built to address the converging pressures of record-breaking ransomware targeting, sweeping regulatory change, critical third-party dependencies, and persistent talent shortages. The following outcomes summarize what Morpheus delivers:
Protect Patient Safety by Identifying Attacks Before They Disrupt Clinical Systems
Ransomware attacks on hospitals follow recognizable patterns: credential compromise, privilege escalation, lateral movement, encryption. Each stage generates alerts across different security tools. Morpheus ingests those alerts from SIEM, EDR, firewalls, NDR, email security, DLP, and identity security. It then uses its attack path discovery framework to identify the kill chain in progress. By surfacing complete attack paths with recommended containment actions for analyst approval, Morpheus helps healthcare organizations stop ransomware before encryption disrupts EHR access or clinical operations.
Reduce Mean Time to Investigate from Hours to Minutes
Traditional SOC teams spend hours manually triaging and correlating alerts across siloed tools. Morpheus autonomously performs the investigation work: threat intelligence correlation, severity assessment based on ePHI exposure and patient safety impact, and attack path reconstruction, all in minutes. Analyst time shifts from repetitive triage to decision-making on validated, pre-investigated findings.
Meet HIPAA’s 60-Day Notification Deadline with Pre-Assembled Breach Documentation
When Morpheus determines an event constitutes a breach of unsecured PHI, it automatically generates the investigation documentation package: timeline from alert ingestion through determination, evidence chain, scope of ePHI involved, classification rationale, and remediation actions. Compliance teams receive pre-assembled documentation rather than spending weeks reconstructing events. This directly supports HIPAA’s 60-day breach notification requirement, state notification timelines, and the proposed 72-hour system restoration mandate.
Produce Audit-Ready Evidence for OCR Investigations and Compliance Certifications
Every action Morpheus takes is fully transparent and auditable: what alert data was analyzed, what reasoning was applied, what conclusions were drawn, and what actions were recommended. This structured audit trail satisfies OCR investigator expectations and supports HITECH Act “recognized security practices” as a mitigating factor. It also provides the documentation foundation for the annual audits the proposed HIPAA Security Rule update would require. When OCR asks how an incident was handled, the answer is documented from alert ingestion to resolution.
Detect Third-Party and Supply Chain Compromises Before They Become Your Breach
Over 80 percent of stolen healthcare records are compromised through third-party vendors, not hospitals directly. Morpheus ingests alerts from the firewalls, NDR, and DLP tools that monitor business associate connections. It identifies supply chain compromise patterns so organizations can contain vendor-originating threats before they escalate into covered entity breaches that trigger notification obligations and OCR scrutiny.
Scale SOC Capacity Without Proportional Headcount
Healthcare organizations invest only 4-7 percent of IT budgets in cybersecurity, versus 15 percent in financial services. Morpheus handles the high-volume work of alert triage, investigation, and correlation autonomously while keeping humans in control of remediation decisions, a patient safety requirement in environments where automated actions affect clinical systems. This allows organizations to handle significantly greater alert volumes without proportionally expanding SOC headcount.
The Healthcare Cybersecurity Crisis
Healthcare is the most targeted sector in the United States for cyberattacks, and the consequences extend far beyond data loss. When a hospital’s systems go down, surgeries are canceled, emergency departments divert ambulances, medication management reverts to error-prone manual processes, and patients die. A 2023 study published in the National Bureau of Economic Research estimated that ransomware-related delays in care may have contributed to the deaths of 42 to 67 Medicare patients between 2016 and 2021 alone. In 2024, 259 million Americans had their protected health information reported as compromised, a record driven by the catastrophic Change Healthcare ransomware attack that disrupted the majority of U.S. hospitals and providers.
The threat picture in 2025 has not improved. Over 445 ransomware attacks targeted hospitals and direct care providers during the year, while attacks on healthcare businesses surged 25 percent. Healthcare data breaches now cost an average of $9.77 million per incident, the highest of any industry. The regulatory environment is undergoing its most significant shift since the HIPAA Omnibus Rule of 2013, with HHS proposing to make all Security Rule safeguards mandatory and OCR launching its third phase of compliance audits.
A Sector Where Cyberattacks Cost Lives
Unlike other industries where the primary impact of a cyberattack is financial, healthcare cyberattacks directly threaten patient safety. When ransomware disables a hospital’s electronic health record system, clinicians lose access to medication histories, allergy information, and laboratory data. Emergency departments are forced to divert patients. Surgical schedules are canceled. Pharmacies cannot verify prescriptions. The clinical impact cascades across the entire care delivery system.
| $9.77M | Average cost of a healthcare data breach in 2024, the highest of any industry |
| 445 | Ransomware attacks on hospitals and direct care providers recorded in 2025 |
| 259M | Americans whose protected health information was reported compromised in 2024 |
| 80%+ | Of stolen healthcare records traced to third-party vendors, not hospitals directly |
| 3.7 mo | Average time for U.S. healthcare organizations to report a breach after a ransomware attack |
Evolving Threat Vectors
Ransomware and Double Extortion
Healthcare remains the top target for ransomware, accounting for 17 percent of all ransomware attacks across industries. Attackers increasingly use double extortion, encrypting systems while simultaneously exfiltrating patient data and threatening to publish it. In 2025, ransomware strains including INC, Qilin, SafePay, Medusa, and RansomHub dominated attacks on healthcare providers, with average demands of $615,000 and some demands exceeding $100 million. The impact extends well beyond the ransom itself: hospitals have reported operating at half capacity for weeks following attacks while systems are restored.
Third-Party and Supply Chain Attacks
Over 80 percent of stolen healthcare records in recent years were not taken from hospitals directly. They were compromised through third-party vendors, business associates, medical billing providers, and healthcare technology firms. Attacks on healthcare businesses surged 25 percent in 2025. The Change Healthcare attack demonstrated the catastrophic potential of a single supply chain compromise, disrupting claims processing and pharmacy operations for the majority of U.S. healthcare providers for months.
Phishing and Credential Compromise
Phishing represents the most common access vector for healthcare data breaches, accounting for 16 percent of breaches as of September 2025. Healthcare is more vulnerable to phishing than any other major industry, with nearly 42 percent of organizations susceptible. Compromised credentials, often obtained through phishing or password-spraying attacks, provide attackers with initial access that leads to privilege escalation and ultimately data exfiltration or ransomware deployment.
AI-Powered Threats
Over a third of healthcare organizations report that AI-driven threats are forcing them to develop stronger defenses. Attackers are using generative AI to build more convincing phishing campaigns, automate social engineering at scale, and develop malware that adapts to evade detection. These AI-powered attacks generate alerts across email security, identity platforms, and endpoint detection tools that must be triaged and correlated faster than manual processes allow.
The Regulatory Environment
Healthcare cybersecurity in the United States is governed by a regulatory framework centered on HIPAA but extending across multiple federal and state requirements. This framework is undergoing rapid change, with proposed rules that would significantly increase enforcement and prescriptiveness.
HIPAA Security Rule
The HIPAA Security Rule establishes administrative, physical, and technical safeguards for electronic protected health information (ePHI). Covered entities (healthcare providers, health plans, and healthcare clearinghouses) and their business associates are required to implement security programs that protect the confidentiality, integrity, and availability of ePHI. The proposed January 2025 overhaul represents the most significant revision since 2013 and would, if finalized:
- Eliminate the distinction between “required” and “addressable” implementation specifications, making all safeguards mandatory
- Require mandatory encryption of ePHI at rest and in transit
- Mandate multi-factor authentication for all access to ePHI
- Require technology asset inventories and network maps updated at least annually
- Require vulnerability scanning every six months and annual penetration testing
- Require written security incident response plans with 72-hour system restoration procedures
- Require annual audits of administrative, technical, and physical safeguards
- Require written verification of business associate security compliance at least annually
- Require notification within 24 hours when workforce member access to ePHI is changed or terminated
HIPAA Breach Notification Rule
The Breach Notification Rule requires covered entities to notify affected individuals, HHS’s Office for Civil Rights (OCR), and in some cases the media, following a breach of unsecured PHI. Notifications must be provided without unreasonable delay and no later than 60 days following discovery. Breaches affecting 500 or more individuals must be reported to OCR within 60 days and are publicly listed on the HHS breach portal. Business associates must notify covered entities within 60 days of discovering a breach. OCR enforces the rule through investigations, resolution agreements, and civil monetary penalties.
HITECH Act
The Health Information Technology for Economic and Clinical Health Act strengthened HIPAA enforcement by establishing tiered penalty structures and making business associates directly liable for HIPAA compliance. The 2021 amendment requires HHS to consider “recognized security practices”, including NIST Cybersecurity Framework adoption, when making enforcement determinations. This gives organizations that can demonstrate mature, well-documented security programs a potential mitigating factor.
HHS Healthcare Sector Cybersecurity Strategy
In 2023, HHS released its Healthcare Sector Cybersecurity concept paper establishing Cybersecurity Performance Goals (CPGs) for healthcare organizations. While initially voluntary, HHS signaled its intent to fold CPGs into enforceable regulatory requirements. The proposed HIPAA Security Rule update implements this directive, and CISA has developed sector-specific Cybersecurity Performance Goals for healthcare to complement the broader framework.
OCR Compliance Audits
OCR confirmed in March 2025 that its third phase of HIPAA compliance audits is underway, initially targeting 50 covered entities and business associates. The audits focus on risk analysis and risk management requirements of the Security Rule. Previous OIG reviews found that the audit program lacked enforcement teeth; OCR has signaled that this phase will include more rigorous follow-up and potential enforcement actions.
State-Level Requirements
Multiple states have enacted or are developing cybersecurity requirements for healthcare that exceed federal minimums. New York’s NYDFS Part 500 applies to health insurers and other financial services entities in the healthcare system. State attorneys general have increasingly pursued enforcement actions following healthcare breaches, and state breach notification laws often impose shorter timelines than HIPAA’s 60-day maximum.
Regulatory Reality: A single healthcare breach can trigger simultaneous obligations under HIPAA’s Breach Notification Rule (60 days), the proposed Security Rule’s incident response requirements (72-hour system restoration), applicable state breach notification laws (often 30-45 days), and CMS Conditions of Participation. An organization’s SOC must produce the investigation documentation required for all of these timelines simultaneously.
Why Traditional SOC Models Fail Healthcare
Alert Volume Across Complex Clinical Environments
Healthcare organizations operate some of the most complex IT environments of any industry. A typical hospital’s security stack generates alerts from SIEMs, EDR on clinical workstations and servers, network firewalls protecting segmented clinical networks, NDR monitoring east-west traffic, email security filtering threats to clinical and administrative staff, DLP watching for ePHI exfiltration, and identity security managing access for clinicians and administrators, many of whom rotate through multiple facilities and systems. The alert volume from these tools overwhelms SOC teams that are already stretched thin by the healthcare cybersecurity talent shortage.
Static Playbooks Cannot Address Clinical Complexity
Traditional SOAR playbooks are built for standardized environments with predictable workflows. Healthcare is anything but standardized. A suspicious login alert on a clinical workstation in an ICU demands a different investigation context than the same alert on an administrative workstation in billing. An anomalous data transfer from a radiology PACS system has different implications than one from a scheduling application. Static playbooks cannot account for this clinical context, leading to either over-escalation that fatigues clinical operations or under-escalation that misses genuine threats to ePHI and patient safety.
Third-Party Blind Spots
Healthcare organizations depend on extensive networks of business associates, cloud service providers, and medical device manufacturers. Each of these connections generates alerts across firewalls, NDR, and DLP that must be correlated to identify when a trusted partner has been compromised. The Change Healthcare attack demonstrated that a single third-party failure can cascade across the entire healthcare system. Traditional SOC models lack the correlation capability to rapidly connect anomalous third-party alerts into a coherent supply chain compromise narrative.
Documentation Gaps Under Regulatory Scrutiny
OCR investigations following a breach examine not just the breach itself but the organization’s entire security program, including risk analyses, security incident response procedures, and evidence of workforce training and access management. Traditional SOC workflows often lack the structured, timestamped audit trails that satisfy OCR investigators. With HIPAA audits now underway and the proposed Security Rule demanding annual documented audits of all safeguards, the documentation bar is rising sharply.
D3 Morpheus: The AI-Autonomous SOC
D3 Morpheus is not a detection engine and does not proactively scan a healthcare organization’s environment. Instead, it sits at the center of the existing security architecture, ingesting alerts from the detection tools already deployed, and applies AI-autonomous intelligence to turn raw alert volume into triaged, investigated, and actionable outcomes.
How Morpheus Works: Morpheus ingests alerts from a healthcare organization’s SIEM, EDR, network firewalls, NDR, email security, DLP, and identity security tools. It autonomously triages and investigates those alerts, uses its attack path discovery framework to correlate related events and identify attacker behaviors across systems, and surfaces prioritized findings with recommended remediation actions for human analyst approval.
Purpose-Built Cybersecurity Threat LLM
Morpheus’s cybersecurity-specific threat LLM was trained on threat intelligence, attack methodologies, and defensive techniques, not adapted from a general-purpose AI model. For healthcare, this means:
- Interpreting alerts from healthcare-specific systems (EHR access logs, medical device network alerts, PACS and imaging system security events, health information exchange traffic) in context, understanding their clinical and security significance
- Adding threat intelligence to ingested alerts to assess whether indicators of compromise are associated with known healthcare-targeting ransomware groups such as INC, Qilin, or Medusa
- Assessing alert severity in the context of ePHI exposure risk and patient safety impact, not just generic severity scores
- Generating investigation narratives using accurate cybersecurity and healthcare terminology that match the documentation standards OCR expects during breach investigations
Attack Path Discovery Framework
Morpheus’s attack path discovery framework correlates alerts across sources and time windows to reconstruct the sequence of behaviors, actions, and functions performed by an attacker. It does not scan the environment for anomalies. It takes the alerts already being generated by detection tools and identifies the attack paths hidden within them.
In healthcare, this capability is essential for identifying:
- Ransomware kill chains where a phishing email (flagged by email security) leads to credential compromise (flagged by identity security), privilege escalation on a clinical workstation (flagged by EDR), lateral movement across clinical network segments (flagged by NDR and firewalls), and pre-encryption reconnaissance of EHR databases (flagged by the SIEM), a sequence only visible as a coordinated attack when the alerts are correlated
- Supply chain compromise patterns where anomalous traffic from a business associate connection (flagged by NDR and firewalls) correlates with unusual ePHI access patterns (flagged by DLP) to reveal that a vendor’s systems have been compromised and are being used to exfiltrate patient data
- Credential-based ePHI access chains where compromised credentials are used to access EHR systems across multiple facilities, with identity security alerts, SIEM logs, and DLP flags combining to reveal systematic unauthorized access to patient records
- Insider threat progressions where a pattern of after-hours EHR access (identity security), bulk patient record queries (SIEM), and data transfers to external destinations (DLP) collectively indicate unauthorized access to ePHI that no individual alert would escalate
Institution-Customizable AI
Healthcare organizations vary enormously in size, complexity, and regulatory exposure. A rural critical access hospital has different risk priorities and technology stacks than a large delivery network or a specialty pharmacy. Morpheus adapts through deep customization:
Custom Risk Prioritization
Organizations can configure Morpheus to weight alert severity based on their specific risk assessment, prioritizing alerts that involve ePHI exposure, clinical system access, or patient safety impact in line with the organization’s HIPAA risk analysis.
Organization-Specific Playbook Generation
Morpheus autonomously generates contextual response playbooks built for each organization’s technology stack and regulatory requirements. An organization operating under NYDFS Part 500 as a health insurer will receive workflows that reflect Part 500’s requirements alongside HIPAA obligations; a provider organization will see workflows matched to OCR expectations and CMS Conditions of Participation.
Custom Training on Organizational Data
Morpheus incorporates organization-specific threat intelligence, historical incident data, and internal security policies to refine its models. The platform becomes more accurate over time, learning the distinction between a clinician’s legitimate late-night EHR access and an anomalous pattern that warrants investigation.
Self-Healing Integrations
Morpheus’s self-healing integration framework automatically adapts when the organization’s security tools change. When a hospital migrates to a new SIEM, adds an NDR solution, or upgrades its email security gateway, Morpheus adapts its alert ingestion without requiring manual reconfiguration. No gaps in coverage during the transition.
Human-in-the-Loop Remediation
While Morpheus autonomously triages, investigates, and correlates alerts at machine speed, remediation actions are routed to human analysts for review and approval. In healthcare, where a wrong automated action could disrupt clinical systems, disable a medical device network, or interrupt EHR access during patient care, human oversight of remediation is not just a regulatory expectation. It is a patient safety requirement.
Morpheus can proactively execute remediation when configured to do so, but in most healthcare deployments, the platform surfaces recommended response actions with full supporting evidence for a human analyst to approve, modify, or reject. Organizations retain full control over which categories of actions can be automated and which require human sign-off.
Full Transparency and Auditability
Every action Morpheus takes is fully visible. For every alert ingested, every triage decision, every investigation conducted, and every remediation recommendation generated, Morpheus provides the complete logic chain: what alert data was analyzed, what reasoning led to the conclusion, and what actions were recommended.
This transparency directly addresses the regulatory documentation requirements healthcare organizations face:
- OCR breach investigations can be supported by Morpheus’s structured, timestamped audit trails showing exactly how the organization’s SOC detected, investigated, and responded to the incident
- HIPAA Security Rule risk analysis and risk management documentation is reinforced by Morpheus’s continuous evidence of how alerts are handled and threats are prioritized
- The proposed annual audit requirement under the HIPAA Security Rule update can be supported by Morpheus’s logs demonstrating the ongoing effectiveness of security safeguards
- HITECH Act “recognized security practices” mitigating factors can be demonstrated through Morpheus’s evidence of mature and well-documented security operations
- Business associate security verification can use Morpheus’s audit data showing how third-party-related alerts are monitored, investigated, and escalated
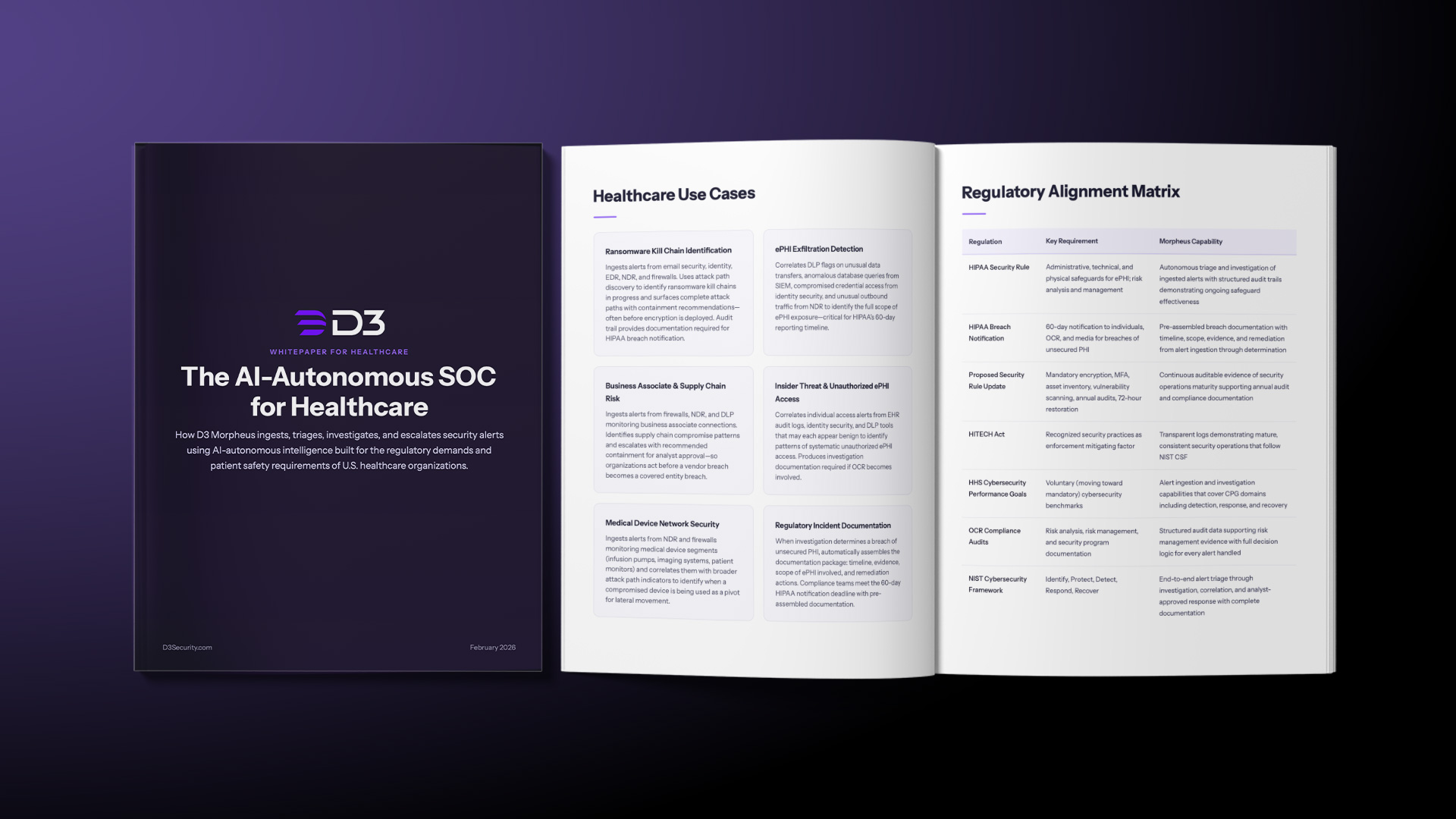
Healthcare Use Cases
Ransomware Kill Chain Identification
Ransomware attacks on healthcare follow recognizable patterns: credential compromise, privilege escalation, lateral movement across clinical network segments, and encryption deployment. Each stage generates alerts across different security tools. Morpheus ingests those alerts and uses its attack path discovery framework to identify the kill chain in progress, surfacing the complete attack path and recommended containment actions for analyst approval, often before encryption is deployed. When analysts approve containment, Morpheus can execute actions such as isolating affected endpoints and blocking lateral movement paths. For incidents that progress to encryption, Morpheus’s audit trail provides the documentation required for HIPAA breach notification.
ePHI Exfiltration Detection
When attackers exfiltrate electronic protected health information, the activity generates alerts across multiple systems: DLP flags unusual data transfers, the SIEM captures anomalous database queries, identity security logs access from compromised credentials, and NDR detects unusual outbound traffic. Morpheus correlates these alerts to identify the full scope of ePHI exposure. This allows the organization to accurately determine the number of affected individuals and the types of PHI compromised, critical information for the HIPAA Breach Notification Rule’s 60-day reporting timeline.
Business Associate and Supply Chain Risk
Healthcare organizations depend on extensive networks of business associates, and the regulatory framework makes covered entities responsible for the security of ePHI shared with those partners. Morpheus ingests alerts from firewalls, NDR, and DLP that monitor business associate connections. When those alerts correlate in patterns consistent with a supply chain compromise, Morpheus identifies the pattern and escalates with recommended containment for analyst approval. Organizations can then act before a vendor breach becomes a covered entity breach.
Insider Threat and Unauthorized ePHI Access
Unauthorized access to patient records (whether by curious employees, departing staff, or malicious insiders) is a persistent compliance and legal risk. Individual access alerts from EHR audit logs, identity security, and DLP tools may each appear benign. Morpheus’s attack path discovery framework correlates these alerts to identify patterns of systematic unauthorized ePHI access. Organizations can then intervene before the exposure escalates and produce the investigation documentation required if OCR becomes involved.
Medical Device Network Security
Connected medical devices (infusion pumps, imaging systems, patient monitors) expand the healthcare attack surface and generate alerts across NDR and network firewalls. These devices often run legacy operating systems that cannot be patched and communicate on clinical networks that must remain available for patient care. Morpheus ingests alerts from the network security tools that monitor medical device segments and correlates them with broader attack path indicators to identify when a compromised device is being used as a pivot point for lateral movement into clinical or administrative systems.
Regulatory Incident Documentation
When Morpheus’s investigation determines that a security event constitutes a breach of unsecured PHI, it automatically assembles the documentation package required for notification: the timeline from initial alert ingestion through investigation and determination, the evidence supporting the breach classification, the scope of ePHI involved, and the remediation actions taken or recommended. Compliance teams can then meet the 60-day HIPAA notification deadline with pre-assembled, investigation-quality documentation.
Regulatory Mapping
The following matrix maps D3 Morpheus’s capabilities to the regulatory requirements most relevant to U.S. healthcare organizations:
| Regulation | Requirement | Morpheus Capability |
|---|---|---|
| HIPAA Security Rule | Administrative, technical, and physical safeguards for ePHI; risk analysis and management | Autonomous triage and investigation of ingested alerts with structured audit trails demonstrating ongoing safeguard effectiveness |
| HIPAA Breach Notification | 60-day notification to individuals, OCR, and media for breaches of unsecured PHI | Pre-assembled breach documentation with timeline, scope, evidence, and remediation from alert ingestion through determination |
| Proposed Security Rule Update | Mandatory encryption, MFA, asset inventory, vulnerability scanning, annual audits, 72-hour restoration | Continuous auditable evidence of security operations maturity supporting annual audit and compliance documentation |
| HITECH Act | Recognized security practices as enforcement mitigating factor | Transparent logs demonstrating mature, consistent security operations that follow NIST CSF |
| HHS Cybersecurity Performance Goals | Voluntary (moving toward mandatory) cybersecurity benchmarks | Alert ingestion and investigation capabilities that cover CPG domains including detection, response, and recovery |
| OCR Compliance Audits | Risk analysis, risk management, and security program documentation | Structured audit data supporting risk management evidence with full decision logic for every alert handled |
| NIST Cybersecurity Framework | Identify, Protect, Detect, Respond, Recover | End-to-end alert triage through investigation, correlation, and analyst-approved response with complete documentation |
Implementation and Deployment
Deployment Model
Morpheus supports on-premises, private cloud, and hybrid deployment models that meet ePHI data residency requirements and organizational architectural standards. The platform integrates with an organization’s existing security architecture, ingesting alerts from tools already deployed, rather than requiring wholesale replacement.
Alert Ingestion Architecture
Morpheus connects to the alert sources common in healthcare environments: enterprise SIEMs, EDR on clinical and administrative endpoints, network firewalls segmenting clinical and medical device networks, NDR monitoring lateral traffic, email security gateways, DLP systems monitoring ePHI movement, and identity security platforms managing clinician and staff access. Self-healing integrations adapt automatically when tool configurations change.
Time to Value
Morpheus begins autonomous triage and investigation immediately upon connecting to alert sources. The cybersecurity threat LLM and contextual playbook generation eliminate the need for months of manual playbook development, delivering operational value from day one.
Human Oversight Model
Morpheus autonomously handles alert triage, investigation, and correlation. Remediation recommendations are surfaced with full supporting evidence for human analyst approval. Organizations configure which response actions Morpheus may execute proactively and which require explicit approval. Actions affecting clinical systems, EHR availability, or medical device networks require human sign-off.
The Case for Autonomous Alert Intelligence in Healthcare
Healthcare’s cybersecurity challenges span IT, patient safety and regulatory compliance. The convergence of escalating ransomware targeting, expanding regulatory requirements, critical third-party dependencies, and a persistent cybersecurity talent shortage creates an urgent need for AI-autonomous security operations.
D3 Morpheus provides U.S. healthcare organizations with an AI-autonomous SOC platform that:
- Ingests alerts from across the organization’s existing security stack (SIEM, EDR, firewalls, NDR, email security, DLP, and identity security) and triages them at machine speed
- Investigates with the depth and rigor that OCR expects, producing structured audit trails for every decision
- Discovers complex attack paths hidden within alert data that static playbooks and manual correlation miss, including ransomware kill chains, supply chain compromises, and insider threats
- Adapts to each organization’s specific clinical environment, technology stack, and regulatory obligations through customizable AI
- Produces the transparent, auditable evidence trail that HIPAA, HITECH, and proposed regulatory updates require
- Keeps human analysts in control of remediation decisions, a patient safety requirement in environments where automated actions can affect clinical systems
- Scales to handle the alert volumes that overwhelm human-only SOC models without sacrificing investigation quality
In healthcare, security teams are buried in alerts while trying to meet HIPAA standards. An autonomous SOC is just a way to stop wasting human talent on event monitoring and data entry and start using it for high-stakes threat response.
Powering the World’s Best SecOps Teams
From bespoke MDR firms to the world’s largest brands and companies.

Ready to see Morpheus?
Morpheus is ready to transform your SOC—intelligent, AI-driven security that adapts to you. See it in action. 🚀