MITRE Corp’s recently published book, 11 Strategies of a World-Class Cybersecurity Operations Center, is a must-read for security operations center (SOC) teams and just about anyone interested in infosec. The book is written for professionals who work in a SOC, but applies to any security operations team, whether they go by CSIRT, CIRT, CIRC, CSOC, CERT, or another name. The book is written for SOC managers, engineers, and analysts who are looking for insights on how to improve their SOC operations or are looking to build one from scratch. Best of all, the book is available as a free download in PDF format.
What’s New in the Second Edition
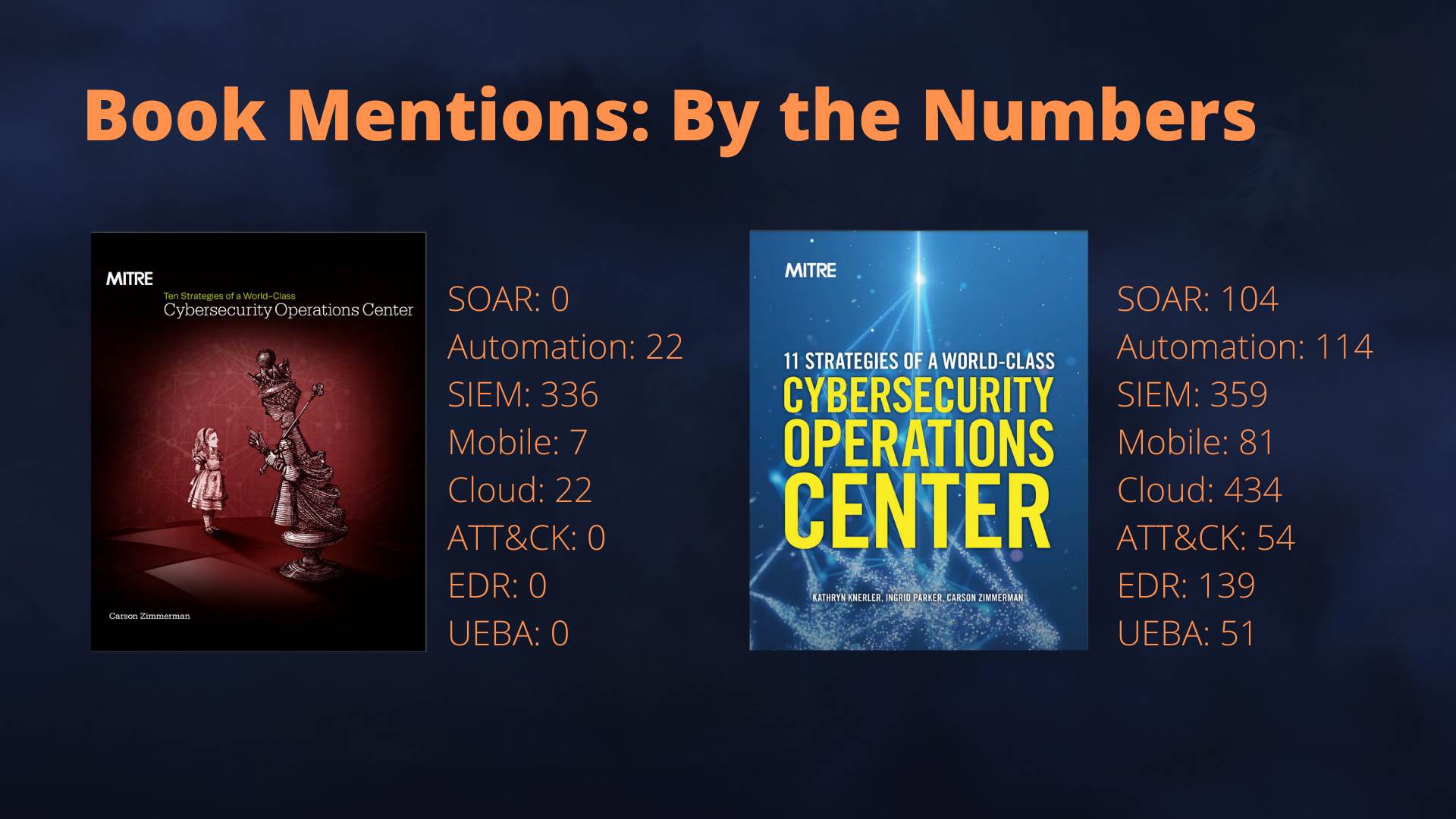
This 432-page book, now in its second edition, is an update to the 2014 release, which had covered 10 strategies. It might sound like an incremental update, but it’s quite the opposite. The 11 strategies are mostly rewritten save for a couple, and there’s a lot of new and expanded material. The cybersecurity landscape has changed tremendously since 2014: there was nothing called SOAR for starters, and ATT&CK, MITRE’s threat intelligence framework was not released publicly until a year later.
The new book also covers other megatrends that have shaped the IT industry in the past decade: the rise of cloud, mobile, and IoT, to name a few. The book covers several new technologies employed by the SOC, ranging from threat intelligence platforms, endpoint detection and response, user entity behavior analytics (UEBA), and security orchestration, automation, and response (SOAR).
Shifting SOC Strategies
In light of all the changes that have taken place since 2014, the strategies covered in the new book have very little in common with the ones in the previous edition. Here are the 10 strategies from the first edition.
- Consolidate CND under one organization.
- Achieve balance between size and agility.
- Give the SOC the authority to do its job.
- Do a few things well.
- Favor staff quality over quantity.
- Maximize the value of technology purchases.
- Exercise discrimination in the data you gather.
- Protect the SOC mission
- Be a sophisticated consumer and producer of cyber threat intelligence
- Stop. think. respond… calmly.
The new book only inherits one strategy verbatim from the first edition: Strategy #3. And if you look closely, a couple of points, though rewritten, are somewhat similar. There’s an emphasis on hiring quality staff (strategy #5, now strategy #4), and leveraging cyber threat intelligence (strategy #9, now strategy #6).
- Know what you are protecting and why.
- Give the SOC the authority to do its job.
- Build a SOC structure to match your organizational needs.
- Hire and grow quality staff.
- Prioritize incident response.
- Illuminate adversaries with cyber threat intelligence.
- Select and collect the right data.
- Leverage tools to support analyst workflow.
- Communicate clearly, collaborate often, and share generously.
- Measure performance to improve performance.
- Turn up the volume by expanding SOC functionality.
The new strategies reflect how SOC teams have evolved in their thinking and working. There’s a section dedicated to different SOC models, as organizations increasingly outsource SOC functions, wholly or partly to managed security service providers (MSSPs). There’s also an added emphasis on the importance of communication and collaboration, and in using threat intelligence frameworks. The book also has a new section dedicated to measuring SOC performance through metrics like ATT&CK framework coverage, dwell time, and response time, to name a few.
What the Book Says About SOAR
SOAR gets mentioned over a hundred times throughout the book, highlighting how it has revolutionized cybersecurity operations. The book calls SOAR an “indispensable capability” for the modern SOC. It’s something that we’ve said before, but it’s validating to hear from a trusted player in the cybersecurity community. SOAR solves a lot of problems that are exacerbated by a combination of a persistent talent gap in the industry, rising cyber threats, an ever-increasing number of security tools, and alert fatigue and the burnout it causes to SOC teams. Through playbooks and automation, SOC investigations, alert triage, and enrichment take a fraction of the time they used to. SOAR eliminates unfulfilling and repetitive work, enabling SOC teams to focus on intellectually rewarding work.
Section 8.5 in the book talks about SOAR exclusively for four pages, under strategy #8, titled Leverage Tools to Support Analyst Workflow. The section explores the following points in detail:
- Key use-cases and reasons for SOCs to harness SOAR
- When SOCs should consider SOAR
- Differences between SIEM and SOAR
There’s also a section dedicated to how SOCs can achieve some of the outcomes of SOAR through other tools or in-house programmers. It comes with this caveat: “While this may be cheaper than buying a SOAR for some SOCs, it runs into challenges with staff turnover and scaling “up” with analysts who are not strong scripters and coders”.
SOAR is an indispensable capability for the modern SOC. Like any other tool, the SOC will generally get out what it puts into SOAR.
Read: How SOAR Can Help You Attract and Retain Cybersecurity Talent
The Next Generation SOAR platform with MITRE ATT&CK
As one of the pioneers of SOAR, a category that didn’t exist five years ago, D3 Security has had many industry firsts and incorporated several innovative features into its platform. It was the first to operationalize the MITRE ATT&CK framework, empowering SOC teams with the ability to query and validate security alerts with ATT&CK TTPs and trigger swift remediations through response playbooks. NextGen SOAR also includes MITRE ATT&CK dashboard that provides a global view of attack trends. Speak to a specialist to find out how your SOC team can catch threats faster.