Cortex XSOAR, originally known as Demisto before Palo Alto Networks acquired it in 2019, is the most widely deployed legacy SOAR platform in enterprise security operations. But a growing number of the world’s largest SOC teams are migrating from Palo Alto’s SOAR to D3 Security’s Morpheus, an autonomous SOC platform that replaces static playbook automation with AI-driven investigation, self-healing integrations, and contextual playbook generation. This guide examines why organizations are making the switch, compares the two architectures capability-by-capability, and provides a practical migration framework for SOC leaders evaluating an XSOAR alternative.
The Great Migration Has Already Begun
Across the UK, EU, and United States, SOC teams at some of the world’s most demanding organizations have migrated away from Palo Alto’s Cortex XSOAR (formerly Demisto) to D3 Security’s Morpheus autonomous SOC platform.
The organizations that have migrated from XSOAR to D3 Security include Big Four firms, firms on global stock exchanges, and even the stock exchange operators themselves, major financial data providers processing billions in daily transactions, global manufacturers, high-profile consumer brands, and MSSPs protecting hundreds of enterprise clients. Some operate global-scale SOCs across multiple continents and regulatory regimes. Others are smaller teams that simply reached the breaking point with XSOAR’s overhead. All reached the same conclusion: the economics of the autonomous SOC are now too compelling to ignore.
This is the definitive guide for SOC leaders, security architects, and CISOs evaluating a migration from Cortex XSOAR to an AI-native autonomous SOC platform. It covers the pain, the process, the economics, and the operational reality on the other side.
The Pain That Drives the Migration
Why are enterprise SOC teams leaving XSOAR? No security team migrates platforms for fun. The decision to rip out a deeply embedded legacy SOAR platform is expensive, disruptive, and politically fraught. The fact that so many elite organizations are doing it simultaneously tells you everything about the severity of the problems they’re leaving behind.
Broken Integrations and Silent Failures
What are the most common XSOAR problems? The most commonly cited pain point among XSOAR customers, including those who have used the platform since its Demisto days, is integration fragility. Palo Alto’s SOAR connectors to non-Palo Alto technologies—which, in any diverse enterprise environment, represent the majority of the security stack, can break and fail silently. When CrowdStrike updates its Falcon API, when Microsoft changes an Azure AD endpoint, when AWS modifies IAM policy structures, XSOAR integrations can stop working. The platform doesn’t always alert you. You may discover it when an automated response fails to fire during an active incident; the worst possible time to learn your automation is broken.
Gartner Peer Insights reviewers have consistently flagged this dynamic. One reviewer noted that “pre-built playbooks needed tons of work to use in a real environment,” adding that “professional services struggled to get anything beyond a basic playbook to work with Azure/O365.”

The Security Engineering Tax
XSOAR demands a level of ongoing engineering investment that many organizations did not anticipate. As one Gartner Peer Insight reviewer put it: “You need someone 100% dedicated to XSOAR in order to get results because the native playbooks need fine-tuning.” Another emphasized that “the main part of this tool is the coding side” and that Python scripting expertise is essential to unlock its potential.
This creates a compounding problem. Every playbook requires manual design, testing, deployment, and maintenance. When a vendor updates an API, those playbooks need to be rebuilt. When a new threat variant emerges, new logic must be authored from scratch. The result is a team of security engineers spending their time maintaining legacy SOAR automation infrastructure rather than investigating threats. D3 Security’s President Gordon Benoit calls this “the Achilles heel of SOAR”, and it is not a problem that better engineering can solve. It is an architectural limitation inherent to the static playbook model.
Poor Support and Eroding Confidence
Multiple organizations have reported frustration with Palo Alto’s support for XSOAR. Gartner Peer Insights reviewers have noted that “the documentation is out of date and lacking in many key areas.” Interface quality, search capabilities, and reporting have also drawn criticism.
This erosion of confidence has been compounded by Palo Alto’s strategic direction. In October 2025, Palo Alto announced Cortex AgentiX as the successor to XSOAR, with professional services SKUs for XSOAR entering end-of-sale. For current XSOAR customers, the message is clear: even Palo Alto is moving on from XSOAR. The question is whether you migrate to another Palo Alto product, or to an autonomous SOC platform that solves the problems XSOAR never could.
Slowness, Instability, and Alert Ingestion Issues
At enterprise scale, XSOAR performance issues can become acute. Organizations have reported platform slowness, instability during high-volume alert surges, and alert ingestion failures that leave gaps in coverage. For a SOC that needs to process thousands of alerts per hour, a platform that struggles to keep up is a liability.
The alert ingestion problem is particularly insidious. When alerts fail to ingest properly, the SOC doesn’t know what it doesn’t know. Threats pass through uninvestigated, and the team has no visibility into the gap until something goes wrong.
The Palo Alto Ecosystem Lock-in
A structural reality of XSOAR is that it works best as part of the broader Palo Alto Cortex ecosystem. Integrations with Cortex XDR, Cortex XSIAM, and other Palo Alto products are naturally prioritized. For organizations running diverse, multi-vendor security stacks—which is virtually every large enterprise—this creates a persistent bias in integration quality. Third-party connectors are second-class citizens, and the experience degrades accordingly.
This is not a conspiracy. It is an inevitable consequence of a vendor building orchestration tooling primarily to support its own detection platform. For organizations that have standardized on Palo Alto across their entire stack, XSOAR may work acceptably. For everyone else, the non-Palo Alto integration experience is a constant source of friction.
The Market Has Spoken
Industry analysts have increasingly questioned whether legacy SOAR as a category can deliver on its original promise. The critiques are consistent: the development resources required to maintain SOAR are prohibitive, the vendor landscape has consolidated through acquisitions leaving fewer independent options, and the expense is difficult for many buyers to justify relative to the outcomes delivered.
The consensus is shifting toward AI-driven security automation as the SOAR replacement model. An autonomous SOC platform replaces static playbook automation with AI-driven investigation that reasons about threats in real time, generates contextual playbooks dynamically, and maintains its own integrations without human intervention. The future belongs to platforms built on this architecture.
Even Palo Alto’s own actions confirm this trajectory. The launch of AgentiX as XSOAR’s replacement is an implicit acknowledgment that Palo Alto’s SOAR model is insufficient. But for organizations that have already been burned by XSOAR’s limitations, the question is whether to bet on another Palo Alto product that’s still finding its footing, or move to a proven XSOAR alternative that’s been purpose-built for the autonomous SOC from day one.
The Economics That Make Migration Inevitable
How much does XSOAR really cost? Here is the fact that surprises many CISOs: even when XSOAR is offered at a steep discount or effectively bundled at no additional cost, organizations still choose to migrate to D3 Morpheus. The reason is that the licensing cost of Palo Alto’s SOAR was never the primary expense. The real costs are operational.
The True Cost of XSOAR Ownership
The total cost of operating XSOAR includes platform licensing, two to three dedicated SOAR engineers to build and maintain playbooks (large enterprises frequently require more), a separate case management solution (or the toleration of XSOAR’s limited built-in capabilities), integration maintenance labor when connectors break, professional services engagements to handle complex implementations, analyst productivity losses from context-switching between tools, and the invisible cost of threats that could slip through when automation fails silently.
When organizations run this full TCO calculation, the math changes dramatically. A “free” XSOAR license that requires two to three dedicated engineers, a separate case management platform, and quarterly professional services engagements is far more expensive than a unified autonomous SOC platform that eliminates most of those costs.
The Morpheus Economic Advantage
D3 Morpheus restructures the economics of SOC operations through three mechanisms. First, autonomous triage eliminates the manual investigation burden. Morpheus’s Attack Path Discovery performs L2-level investigation on every alert, delivering structured investigation reports in under two minutes. Based on production deployment data, customers report dramatic alert noise reduction—one enterprise customer processing 145,000 XDR alerts per two-week period saw that number reduced to 1,000 alerts requiring human attention, and eventually to just 200 after further tuning.
Second, self-healing integrations eliminate the integration maintenance tax. When vendor APIs change, detection formats drift, or authentication rotates, Morpheus autonomously detects and adapts, recapturing the operational time that SOC teams typically spend keeping integrations alive.
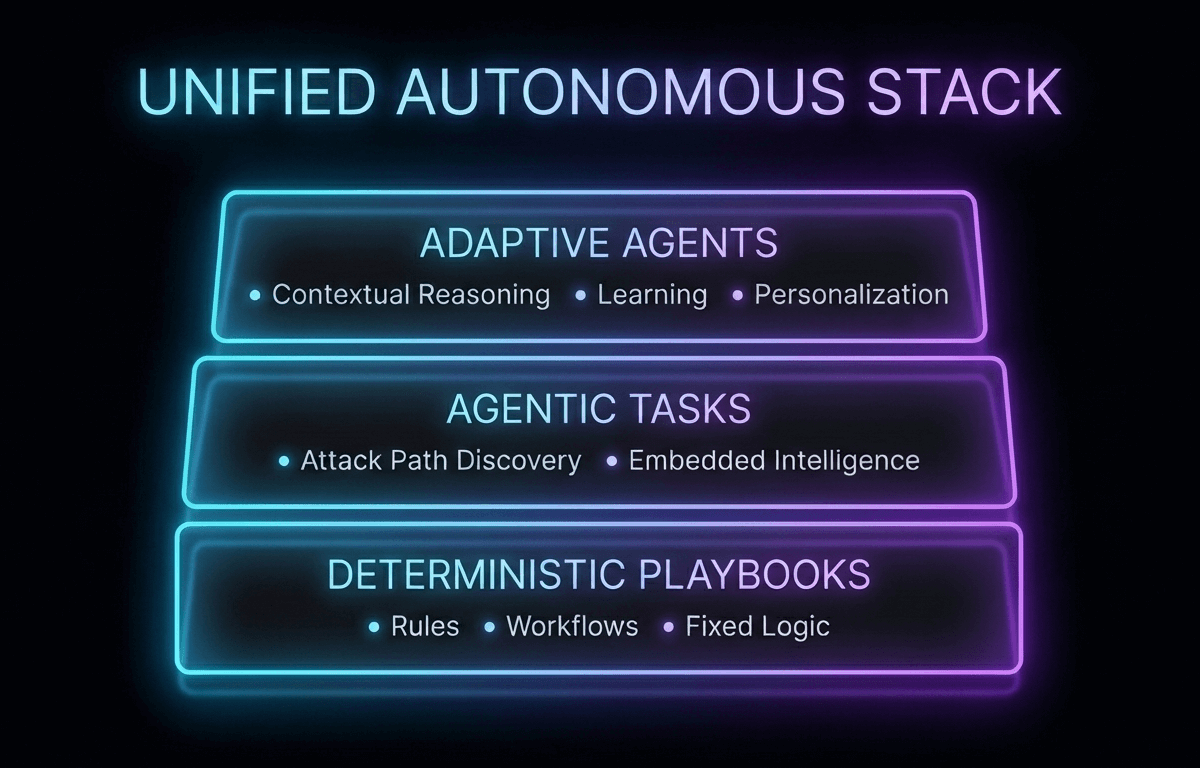
Third, AI-generated contextual playbooks eliminate the playbook engineering lifecycle entirely. No authoring, no versioning, no playbook maintenance when a new attack variant appears. Morpheus generates a bespoke playbook for each incident at runtime based on the alert context, the organization’s tool stack, and its SOC preferences.
XSOAR vs. D3 Morpheus: Architecture Comparison
How does XSOAR compare to D3 Morpheus? The differences are not incremental improvements. They represent a generational shift from legacy SOAR to an autonomous SOC platform. The following table provides a capability-by-capability comparison between Cortex XSOAR (formerly Demisto) and D3 Morpheus across the dimensions that matter most to enterprise SOC teams and MSSPs.
| Capability | Cortex XSOAR (Demisto) | D3 Morpheus |
|---|---|---|
| Foundation | Playbook engine with static workflows | Purpose-built cybersecurity threat LLM |
| Threat Understanding | Rule-based pattern matching | Native LLM-based attack path reasoning |
| Investigation Depth | L1 enrichment and triage | L2-level autonomous investigation on every alert |
| Playbook Model | Static; manually built and maintained | AI-generated contextually at runtime |
| Integration Maintenance | Manual; breaks require engineer intervention | Self-healing; autonomous API drift detection and repair |
| Integration Count | 1,000+ (Palo Alto ecosystem preferred) | 800+ vendor-agnostic, bidirectional |
| Case Management | Basic built-in; often supplemented externally | Full lifecycle: evidence, RBAC, SLA tracking, audit trails |
| Attack Path Discovery | Not available | Native on every alert—vertical and horizontal correlation |
| MITRE ATT&CK Mapping | Manual mapping required | Native / automated TTP analysis |
| Deterministic Playbooks | Yes (primary model) | Yes (alongside autonomous AI; dual mode) |
| Time to Value | 3–6 months typical | Days to weeks |
| SOAR Architect Required | Yes—2–3+ dedicated FTEs typical at scale | Single engineer to deploy and maintain |
| Deployment Options | Cloud, on-prem | Cloud, on-prem, hybrid |
| Multi-Tenant / MSSP | Limited multi-tenancy | Purpose-built multi-tenant with per-tenant AI control |
| Alert Throughput | Enterprise scale | 100M+ alerts/day; stress-tested for 10x surge volumes |
| Vendor Lock-in | Palo Alto ecosystem favored | Fully vendor-agnostic |
What XSOAR Teams Gain with D3 Morpheus
What Is an Autonomous SOC and How Does It Replace XSOAR?
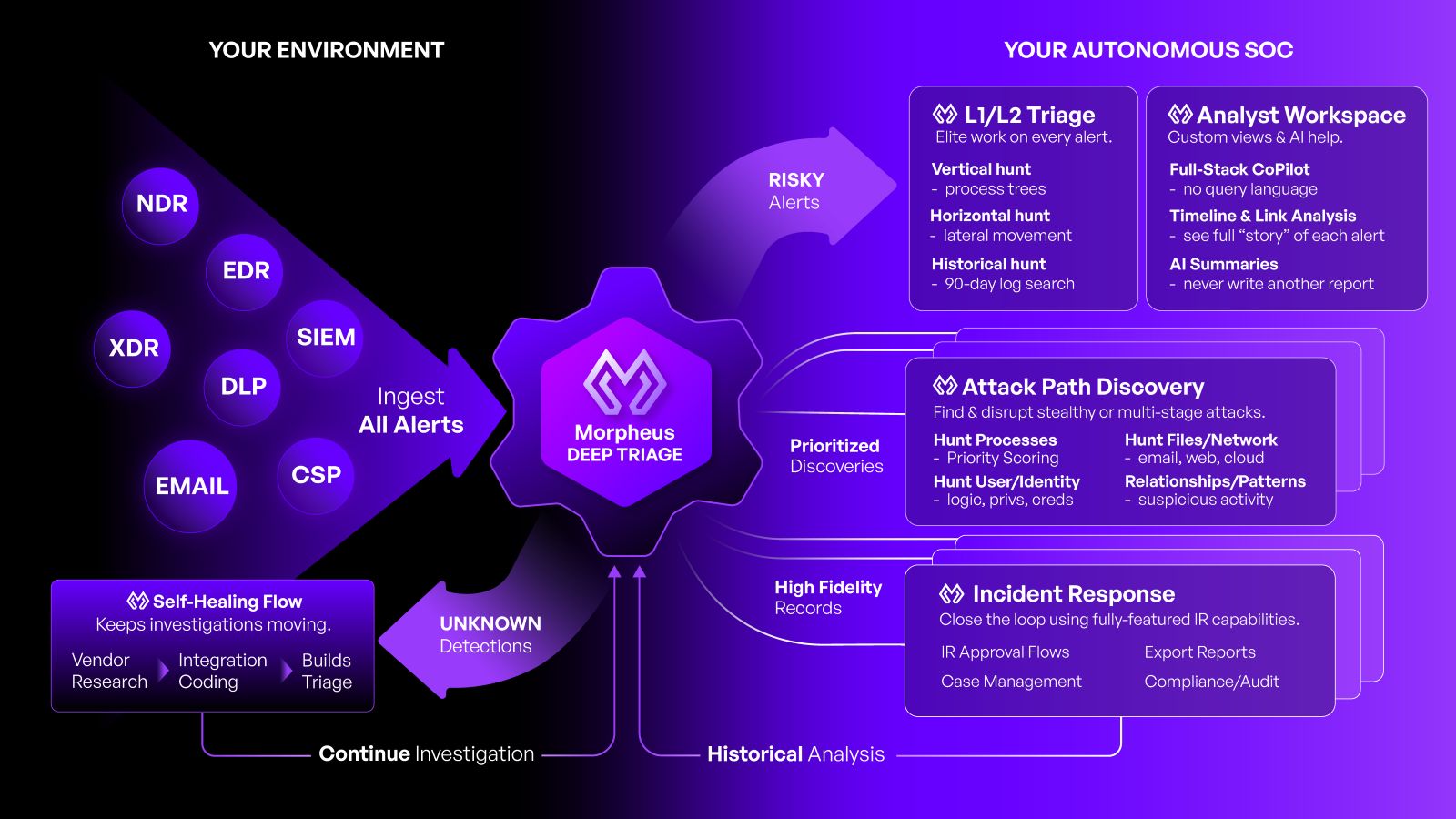
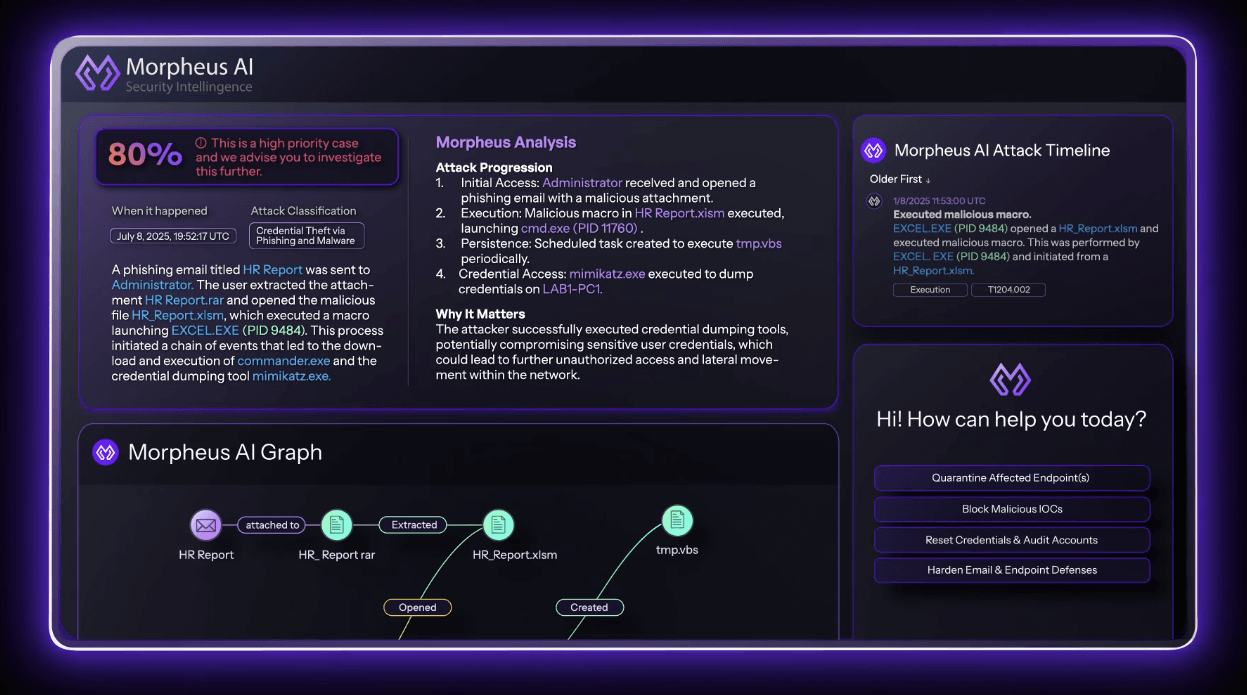
The primary driver for migration is the shift from manual-plus-automation to genuine autonomy. An autonomous SOC platform like D3 Morpheus does not simply orchestrate predefined steps—it investigates threats the way an experienced analyst would, using AI to reason across the entire security stack. Morpheus’s Attack Path Discovery doesn’t just enrich alerts—it investigates them. On every incoming alert, the platform performs multi-dimensional correlation: vertical (north-south) deep inspection into the alert’s originating tool and horizontal (east-west) correlation across the full security stack. The output is a structured investigation report with step-by-step reasoning, evidence chains, entity timelines, and a clear disposition. Ninety-five percent of alerts are triaged in under two minutes.
This is the work that a skilled L2 analyst would perform, executed consistently, at machine speed, on every single alert, 24 hours a day.
Mature Case Management and Incident Response
XSOAR customers frequently cite case management as a pain point. The platform’s built-in case management capabilities have been described in peer reviews as limited and “underwhelming.” Many organizations supplement XSOAR with a separate case management tool, adding cost and context-switching.
D3 Morpheus includes a full-lifecycle case management system built directly into the AI SOC platform—a capability that reflects D3’s 20+ years of heritage in incident response and case management. This includes complete evidence tracking and chain of custody, role-based access control (RBAC), SLA tracking and governance workflows, executive dashboards and reporting, AI-generated investigation summaries with dynamic attack timelines, entity graphs and IOC panels, and configurable approval gates for high-impact response actions.
When an investigation escalates, all relevant context—the AI’s findings, automated response actions, evidence timeline, and full audit trail—travels with the case automatically. No context-switching. No re-keying data into a separate system.

Self-Healing Integrations: The End of SOAR Maintenance
If brittle integrations are XSOAR’s Achilles heel, self-healing integrations are Morpheus’s decisive advantage. Self-healing integrations are a capability in which the platform continuously monitors the health and behavior of every API integration across the security stack and, when a change is detected—schema changes, new alert types, API endpoint modifications, authentication rotation—generates corrective code autonomously, without human intervention.
The result: new vendor detections flow into the SOC in near-real-time instead of waiting days or weeks for manual fixes. No more visibility gaps. No more Saturdays ruined when an integration breaks during an active incident.
What Happens to Existing XSOAR Playbooks During Migration?
A critical concern for any migration is preserving existing investments. Morpheus includes a full built-in SOAR engine alongside its autonomous AI capabilities. Organizations can run both models simultaneously: deterministic playbooks for alert categories where strict, predictable behavior is required, and autonomous AI triage for categories where AI-driven investigation adds value.
This dual-mode architecture means teams can recreate any functionality they built in XSOAR or Demisto while simultaneously gaining autonomous capabilities. D3 has deep expertise in XSOAR-to-Morpheus migrations and can rebuild existing workflows within the Morpheus deterministic SOAR engine. The transition is on the customer’s timeline—not a forced rip-and-replace.
MSSP-Specific Benefits
For managed security service providers, the migration calculus is even more compelling. MSSPs face a structural challenge: their client portfolios contain fundamentally conflicting risk profiles. Some clients demand AI-driven automation. Others—particularly in finance, healthcare, and government—enforce strict policies prohibiting AI involvement in security decision-making.
XSOAR’s architecture—like most legacy SOAR platforms, including those from Palo Alto, Splunk, and IBM—creates a hard ceiling on MSSP scalability. It lacks autonomous integration maintenance, so as tenant count grows, the engineering hours required to patch broken API connectors grow linearly. The marginal cost of adding a new client remains static rather than decreasing over time.
D3 Morpheus resolves this through three capabilities. Native multi-tenancy provides granular isolation with per-tenant configurations. Hybrid workflow execution allows autonomous AI triage and deterministic, rule-based playbooks to run within the same instance, with AI configuration controlled at the individual tenant and playbook level. Self-healing integrations decouple engineering costs from client volume, recapturing operational time currently consumed by integration maintenance.
This architecture allows MSSPs to standardize on a single AI SOC platform while delivering tiered, compliance-aligned service levels to any client profile—from full AI-autonomous triage for technology clients to strictly deterministic workflows for regulated financial institutions, all from the same instance.
The Migration Path
How do you migrate from XSOAR to an autonomous SOC? D3 Security has developed a three-phase accelerated migration methodology refined through engagements with the world’s largest SOC teams. The process is designed to minimize disruption while maximizing time-to-value, whether an organization is migrating from Cortex XSOAR, the original Demisto deployment, or another legacy SOAR platform.
Phase 1: Assessment and Architecture (Week 1–2)
D3 learns your playbook, integration, case management workflow, and reporting requirements. This produces a migration architecture that identifies which XSOAR workflows will be replicated in Morpheus’s deterministic SOAR engine and which alert categories will be transitioned to autonomous AI triage.
Phase 2: Workflow Recreation and Transition (Week 2–6)
Existing XSOAR playbooks that need to be preserved are recreated in Morpheus’s SOAR engine. Alert categories that benefit from autonomous investigation are transitioned to Attack Path Discovery. Case management workflows, reporting, and governance structures are configured.
Phase 3: Full Cutover and Optimization (Week 6–9)
XSOAR is decommissioned. The team enters an optimization phase where Morpheus’s customer-expandable LLM is fine-tuned to the organization’s specific environment, threat landscape, and SOC procedures. Ongoing support ensures the platform evolves with the team’s needs.
Total migration timeline for most organizations is 6–9 weeks from kickoff to full production—compared to the up to 12 months some organizations have spent getting XSOAR to a functional state.
Why the Window Is Now
Three converging forces make this the optimal moment for migration.
XSOAR’s uncertain future. Palo Alto has signaled that AgentiX will replace XSOAR. Professional services SKUs for XSOAR are entering end-of-sale. Organizations that delay migration may find themselves forced onto AgentiX—a platform that is still in early availability and lacks the production maturity of Morpheus. For teams evaluating Cortex AgentiX vs. D3 Morpheus, the question is whether to trust an unproven successor to a platform that already failed to deliver, or to move to a purpose-built autonomous SOC that is already in production at global scale.
The threat landscape is accelerating. Modern adversaries operate dynamically, using AI to launch attacks at record speeds. A SOC built on static playbooks that can only respond to scenarios it was explicitly programmed for is structurally incapable of keeping pace. With the average cost of a data breach in the United States reaching $10.22 million, the cost of maintaining a defense model designed for the previous generation of threats is no longer justifiable.
The autonomous SOC is production-ready. Morpheus is not a concept or a roadmap. It is in production at some of the world’s most demanding SOC environments—processing millions of alerts, delivering L2-level investigation on every one, and adapting autonomously when the environment changes. The technology risk of migration has been resolved by the organizations that went first.
The Question Is Not Whether, But When
The migration itself is not the hard part. D3 has run enough of these—from Demisto-era deployments to fully scaled XSOAR environments—that the process is predictable: six to nine weeks, phased cutover, existing workflows preserved in Morpheus’s deterministic engine while autonomous triage takes over the alert categories where it adds the most value.
The hard part is the decision. But the organizations profiled in this guide already took that bet. They did it because the cost of staying was worse than the cost of switching, and because the gap between the two architectures is no longer close enough to justify waiting.
Palo Alto ended the sale of XSOAR professional services SKUs on February 1, 2026. The successor product is still in early availability. The window to migrate on your own terms is open now, but it won’t stay open indefinitely.
Schedule a migration assessment—D3’s team will scope your environment, map your existing playbooks, and show you what the transition looks like for your SOC.